Over 80 percent of american organizations have adopted artificial intelligence for network security, yet many professionals still misunderstand its true capabilities and risks. As cyber threats grow smarter and more relentless, relying solely on traditional defenses is no longer enough. This article sheds light on the key fundamentals of AI network security and uncovers the most common misconceptions, helping readers gain a clear, realistic understanding of this evolving field.
Table of Contents
- AI Network Security Fundamentals and Misconceptions
- Types of AI-Powered Network Security Solutions
- How AI Enhances Network Threat Detection
- Real-World Use Cases in B2B Environments
- Risks, Limitations, and Compliance Challenges
- Best Practices for Implementing AI Security
Key Takeaways
| Point | Details |
|---|---|
| AI Enhances Security | AI technology significantly improves threat detection and defense by utilizing advanced algorithms and continuous learning. |
| Awareness of Limitations | Organizations must recognize that AI is a tool with limitations and vulnerabilities, requiring human oversight and regular assessments. |
| Diverse Solutions Available | A range of AI-powered solutions, such as predictive threat intelligence and automated incident response, can enhance cybersecurity strategies. |
| Compliance is Key | Navigating the regulatory landscape is essential, as compliance and accountability frameworks are critical for successful AI security implementation. |
AI Network Security Fundamentals and Misconceptions
AI network security represents a sophisticated technological frontier where machine learning and cybersecurity converge to defend digital infrastructures against increasingly complex threats. As organizations increasingly rely on artificial intelligence to protect their networks, understanding the core principles and dispelling common misconceptions becomes paramount.
According to research from arxiv.org, AI-based cyber threat detection has emerged as a critical strategy for protecting modern digital ecosystems. The study highlights several key insights about machine learning classifiers in network security:
- Machine Learning Classifiers: Advanced algorithms capable of identifying network anomalies and potential malware intrusions
- Anomaly Detection: Sophisticated techniques that go beyond traditional signature-based security methods
- Predictive Capabilities: AI systems can proactively recognize potential security threats before they fully manifest
However, adversarial attacks present a significant challenge to AI network security. arxiv.org reveals that cybercriminals can potentially manipulate AI applications through advanced techniques designed to exploit system vulnerabilities. These attacks demonstrate that while AI offers powerful defense mechanisms, it is not inherently infallible.
Key misconceptions about AI network security often stem from overestimating its capabilities or underestimating its limitations. Professionals must recognize that AI is a sophisticated tool, not a magical solution. Successful implementation requires:
- Continuous model training
- Regular vulnerability assessments
- Human oversight and intervention
- Adaptive security frameworks
Effective AI network security demands a holistic approach that combines cutting-edge technology with human expertise. Organizations must invest not just in advanced algorithms, but in comprehensive strategies that integrate AI capabilities with robust cybersecurity practices. The future of network defense lies in understanding AI as a powerful ally, not an autonomous guardian.
Types of AI-Powered Network Security Solutions
AI-powered network security solutions represent a sophisticated technological approach to defending digital infrastructures against increasingly complex cyber threats. As organizations seek more advanced protection mechanisms, understanding the diverse types of AI-driven security solutions becomes crucial for comprehensive digital defense strategies.
According to research from uir.ac.id, AI techniques are transforming cybersecurity through multiple innovative approaches. The study highlights several key AI-powered network security solutions:
- Machine Learning Classifiers: Advanced algorithms that analyze network traffic patterns to detect potential security breaches
- Natural Language Processing (NLP): Systems that can interpret and analyze communication channels for potential security risks
- Anomaly Detection Systems: Intelligent frameworks that identify unusual network behaviors indicating potential cyber threats
Research from researchcorridor.org further demonstrates the powerful capabilities of AI in network security, emphasizing its ability to automate and enhance threat detection processes. The primary types of AI-powered network security solutions can be categorized into the following comprehensive approaches:
-
Predictive Threat Intelligence
- Real-time threat detection
- Proactive risk assessment
- Continuous learning and adaptation
-
Behavioral Analysis Systems
- User and entity behavior tracking
- Identifying potential insider threats
- Anomaly pattern recognition
-
Automated Incident Response
- Immediate threat mitigation
- Automated containment strategies
- Rapid vulnerability patching
The effectiveness of these AI-powered solutions lies not just in their technological sophistication, but in their ability to adapt and learn from emerging cyber threats. Unlike traditional security approaches, AI-driven systems can continuously evolve, providing organizations with dynamic and intelligent defense mechanisms that stay ahead of increasingly complex cybersecurity challenges.

How AI Enhances Network Threat Detection
Network threat detection has undergone a revolutionary transformation with the integration of artificial intelligence, shifting from reactive to proactive security strategies. Modern organizations now leverage advanced AI technologies to identify, analyze, and neutralize potential cybersecurity risks before they can cause significant damage.
Research from arxiv.org highlights a groundbreaking approach to intrusion detection, particularly in software-defined IoT networks. The study reveals how AI-powered systems can dramatically improve threat detection through intelligent feature selection and advanced flow classification techniques:
- Intelligent Feature Selection: AI algorithms can automatically identify the most critical network indicators
- Dynamic Pattern Recognition: Machine learning models continuously adapt to emerging threat landscapes
- Real-Time Threat Mapping: Instantaneous identification of potential security vulnerabilities
The core mechanisms of AI-enhanced network threat detection involve several sophisticated strategies:
-
Behavioral Baseline Establishment
- Creating comprehensive network behavior profiles
- Detecting deviations from normal operational patterns
- Identifying potential security anomalies
-
Predictive Threat Modeling
- Analyzing historical attack data
- Generating probabilistic threat scenarios
- Anticipating potential future security risks
-
Automated Response Protocols
- Instantaneous threat isolation
- Automatic system reconfiguration
- Rapid incident mitigation
By combining advanced machine learning algorithms with comprehensive data analysis, AI transforms network threat detection from a manual, time-consuming process into a dynamic, intelligent defense mechanism. Organizations can now leverage AI to create self-learning security ecosystems that evolve in real-time, providing unprecedented protection against sophisticated cyber threats.
Real-World Use Cases in B2B Environments
AI-powered network security solutions have transformed how businesses approach cybersecurity, moving beyond traditional defensive strategies to proactive, intelligent threat management. B2B environments increasingly rely on sophisticated AI technologies to protect complex digital infrastructures and sensitive corporate networks.
Research from francis-press.com highlights several critical AI-driven cybersecurity applications in enterprise contexts:
- Threat Detection and Prevention: AI systems that continuously monitor network activities
- Anomalous Behavior Recognition: Intelligent algorithms identifying potential security risks
- Authentication Control: Advanced access management using AI-powered verification techniques
According to research from admin.mantechpublications.com, real-world AI network security solutions demonstrate remarkable capabilities across multiple domains:
-
AI-Enhanced Firewall Systems
- Dynamic threat filtering
- Intelligent traffic pattern analysis
- Real-time malicious activity blocking
-
Intelligent Intrusion Detection
- Continuous network monitoring
- Predictive threat identification
- Automated response mechanisms
-
Endpoint Security Management
- Device-level threat assessment
- Behavioral anomaly tracking
- Proactive vulnerability mitigation
These AI-driven approaches represent a paradigm shift in network security, enabling organizations to transform reactive defense mechanisms into intelligent, predictive protection systems. By leveraging machine learning and advanced analytics, businesses can now anticipate, identify, and neutralize potential security threats with unprecedented speed and accuracy.
Risks, Limitations, and Compliance Challenges
AI network security represents a powerful technological advancement, but it is not without significant challenges that organizations must carefully navigate. Understanding the inherent risks, limitations, and compliance complexities is crucial for implementing effective and responsible AI-driven security strategies.
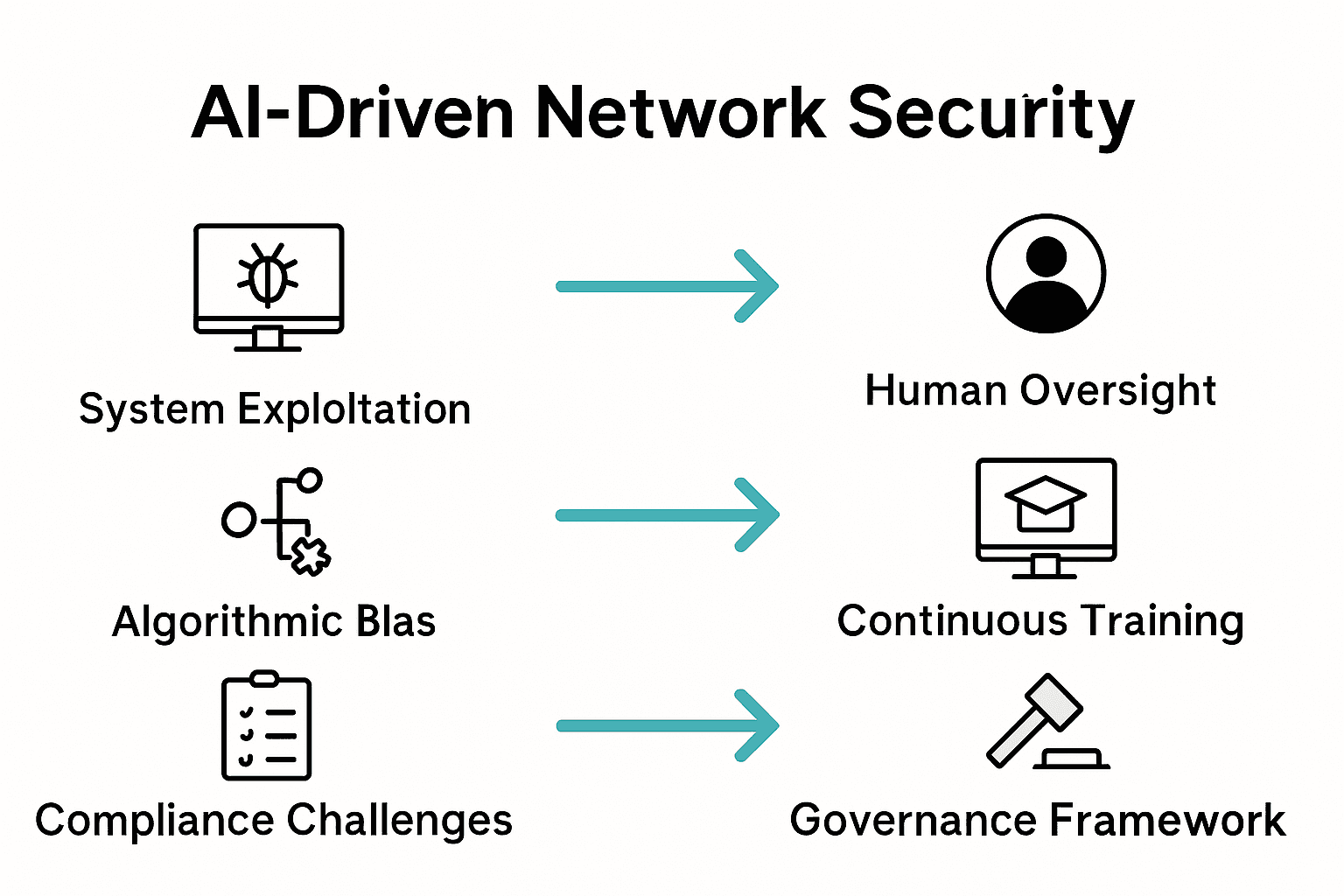
Research from ojs.acad-pub.com systematically investigates the critical vulnerabilities surrounding AI in cybersecurity, highlighting several key concerns:
- System Exploitation: Potential for malicious actors to manipulate AI algorithms
- Algorithmic Bias: Inherent limitations in machine learning decision-making processes
- Unpredictable Behavior: Challenges in creating fully reliable AI security systems
According to arxiv.org, adversarial attacks represent a significant threat to AI network security, demonstrating multiple critical vulnerabilities:
-
Adversarial Knowledge Risks
- Potential for attackers to understand and exploit AI system weaknesses
- Sophisticated methods of generating deceptive input examples
- Capabilities to manipulate AI decision-making processes
-
Compliance and Regulatory Challenges
- Complex legal frameworks governing AI technology
- Evolving standards for AI security and data protection
- Requirement for transparent and explainable AI systems
-
Technical Limitations
- Difficulty in achieving 100% accurate threat detection
- Potential for false positives and negatives
- Challenges in maintaining system adaptability
With understanding the GRC framework, organizations can develop more robust strategies to mitigate these risks. The future of AI network security lies not in eliminating all vulnerabilities, but in creating adaptive, resilient systems that can anticipate and respond to emerging threats with increasing sophistication and precision.
Best Practices for Implementing AI Security
Implementing AI security requires a strategic, comprehensive approach that goes beyond traditional cybersecurity methodologies. Organizations must develop robust frameworks that leverage advanced technologies while maintaining rigorous standards of protection and operational integrity.
Research from arxiv.org provides critical insights into deploying AI-enabled cybersecurity solutions, highlighting key considerations for effective implementation:
- Machine Learning Classifier Selection: Choosing sophisticated algorithms tailored to specific network environments
- Anomaly Detection Techniques: Developing nuanced approaches for identifying potential security threats
- Continuous Model Training: Ensuring AI systems remain adaptive and responsive to emerging risks
Effective AI security implementation demands a multifaceted strategy:
-
Comprehensive Risk Assessment
- Detailed infrastructure vulnerability mapping
- Identification of potential attack vectors
- Prioritization of critical security domains
-
Advanced Threat Modeling
- Predictive threat landscape analysis
- Scenario-based security simulations
- Dynamic risk mitigation planning
-
Governance and Compliance Framework
- Establishing clear AI security protocols
- Implementing robust monitoring mechanisms
- Ensuring transparency and accountability
With essential steps for a security compliance checklist, organizations can systematically enhance their AI security posture. Success requires a holistic approach that balances technological innovation with strategic risk management, recognizing that AI is a powerful tool that demands careful, intelligent deployment.
Strengthen Your AI Network Security with Streamlined Compliance Automation
AI network security requires more than advanced algorithms to defend against evolving cyber threats. The article highlights challenges like continuous model training, vulnerability assessments, and the need for human oversight to maintain resilient defenses. These demands often translate into complex and time-consuming security questionnaires that many organizations face, especially in tech and finance sectors where proving compliance and security posture is critical.
Skypher’s AI Questionnaire Automation Tool addresses these exact pain points by empowering organizations to accelerate and simplify their security review process. With features such as reliable AI-powered parsing for every format, integration with over 40 third-party risk management platforms like ServiceNow and Slack, and instant answering of hundreds of security questions, Skypher helps teams maintain compliance effortlessly while focusing on real threat management. This connection between AI network security concepts and practical compliance automation ensures your defenses stay adaptive and trustworthy.
Ready to transform your security questionnaire workflow and bolster your AI-driven network defenses?

Explore how Skypher can accelerate your cybersecurity operations and reduce risk today by visiting our main website. Discover the power of our AI Questionnaire Automation Tool and strengthen your security posture with seamless collaboration and real-time integrations. Take the next step toward smarter, faster network security compliance now.
Frequently Asked Questions
What is AI network security?
AI network security refers to the integration of artificial intelligence and machine learning technologies to protect digital infrastructures from cyber threats. It enhances threat detection, prevention, and response capabilities by analyzing network data in real-time.
How do AI-powered solutions improve threat detection?
AI-powered solutions use advanced algorithms to identify patterns in network traffic, detect anomalies, and predict potential threats before they can cause harm. This proactive approach allows organizations to respond to security risks more effectively than traditional methods.
What are the common misconceptions about AI in network security?
Common misconceptions include the belief that AI systems can operate autonomously without human oversight or that they eliminate all security risks. In reality, AI tools require continuous training, regular assessments, and human intervention to be effective.
What are some best practices for implementing AI security in organizations?
Best practices include conducting a comprehensive risk assessment, selecting appropriate machine learning classifiers, ensuring ongoing model training, and establishing a governance framework that addresses compliance and accountability.
Recommended
- ISO 27001 Consulting: Complete Guide for Businesses
- Smart Security Knowledge Base | Security Questionnaire Automation | Skypher
- Understanding GRC Cyber Security: Concepts and Importance
- Understanding SOC 2 AICPA: Your Guide to Compliance
- Securing the Defense Industry: Tackling Cybersecurity in an Interconnected World
