AI is taking over network security faster than anyone predicted and now intelligent systems can spot threats with over 92 percent accuracy before attackers even get through the door. Most people picture hackers racing ahead, outsmarting digital defenses with ease. Actually, AI is flipping the script and catching cybercriminals off guard, shutting down attacks before they even start.
Table of Contents
- How Ai Transforms Modern Network Security
- Top Use Cases For Ai In Network Protection
- Risks, Challenges, And Ethical Considerations
- Best Practices For Adopting Ai Solutions
Quick Summary
| Takeaway | Explanation |
|---|---|
| AI enhances predictive threat intelligence | AI systems can identify potential vulnerabilities with over 92% accuracy, allowing for proactive security measures. |
| Real-time adaptive responses mitigate threats | AI can instantly neutralize threats by adjusting network defenses without human intervention, speeding up response times. |
| Automated threat hunting improves efficiency | AI can autonomously investigate and remediate security incidents rapidly, reducing reliance on manual processes. |
| Establish robust AI governance frameworks | Organizations must create clear guidelines for ethical AI deployment, ensuring transparency, accountability, and compliance. |
| Train staff for effective AI utilization | Continuous training is essential for employees to understand AI's capabilities and manage security effectively. |
How AI Transforms Modern Network Security
Artificial intelligence is revolutionizing network security by introducing unprecedented capabilities for threat detection, prevention, and response. Traditional security models are rapidly giving way to intelligent systems that can anticipate, analyze, and neutralize cybersecurity risks with remarkable precision and speed.
Predictive Threat Intelligence
AI-powered network security goes beyond reactive approaches by implementing advanced predictive threat intelligence mechanisms. Learn more about adaptive security strategies that leverage machine learning algorithms to identify potential vulnerabilities before they can be exploited. According to the CyberSentinel research, emerging AI systems can now detect anomalous network behaviors with over 92% accuracy, significantly reducing the window of potential cyber attack opportunities.
These intelligent systems continuously analyze network traffic patterns, user behaviors, and system interactions to create dynamic risk profiles. By understanding baseline network operations, AI can instantly recognize deviations that might indicate a potential security breach. This approach transforms network security from a static defense mechanism to an adaptive, intelligent shield that evolves alongside emerging threat landscapes.
Real Time Adaptive Response
The most groundbreaking aspect of AI in network security is its ability to provide real time adaptive responses. According to the cloud computing security study, AI-driven systems can now automatically isolate compromised network segments, reconfigure firewall rules, and initiate containment protocols within milliseconds of detecting a potential threat.
Traditional security approaches required human intervention and manual analysis, creating significant delays in threat mitigation. AI eliminates these bottlenecks by implementing instant, intelligent decision making. Machine learning models can assess the severity of potential security incidents, prioritize responses, and execute precise countermeasures without human interaction.
Comprehensive Threat Modeling
Organizational cybersecurity is experiencing a paradigm shift through AI-enhanced threat modeling. The systematic review on generative AI in cybersecurity highlights how artificial intelligence enables more comprehensive and dynamic threat assessment frameworks. These advanced systems can simulate complex attack scenarios, predict potential vulnerability chains, and develop proactive defense strategies.
By integrating large language models and machine learning algorithms, AI can now generate sophisticated threat models that consider multiple attack vectors simultaneously. This approach allows organizations to anticipate and prepare for potential security challenges before they materialize, creating a more resilient and intelligent security infrastructure.
As network environments become increasingly complex and distributed, AI emerges as the critical technology enabling robust, adaptive, and intelligent security solutions. The future of network security is not about building higher walls, but about creating smart, responsive systems that can dynamically understand, predict, and neutralize potential risks.
Top Use Cases for AI in Network Protection
Artificial intelligence is transforming network protection strategies by introducing sophisticated approaches that go far beyond traditional security mechanisms. As cyber threats become increasingly complex, AI emerges as a critical technology enabling organizations to defend their digital infrastructure with unprecedented precision and adaptability.
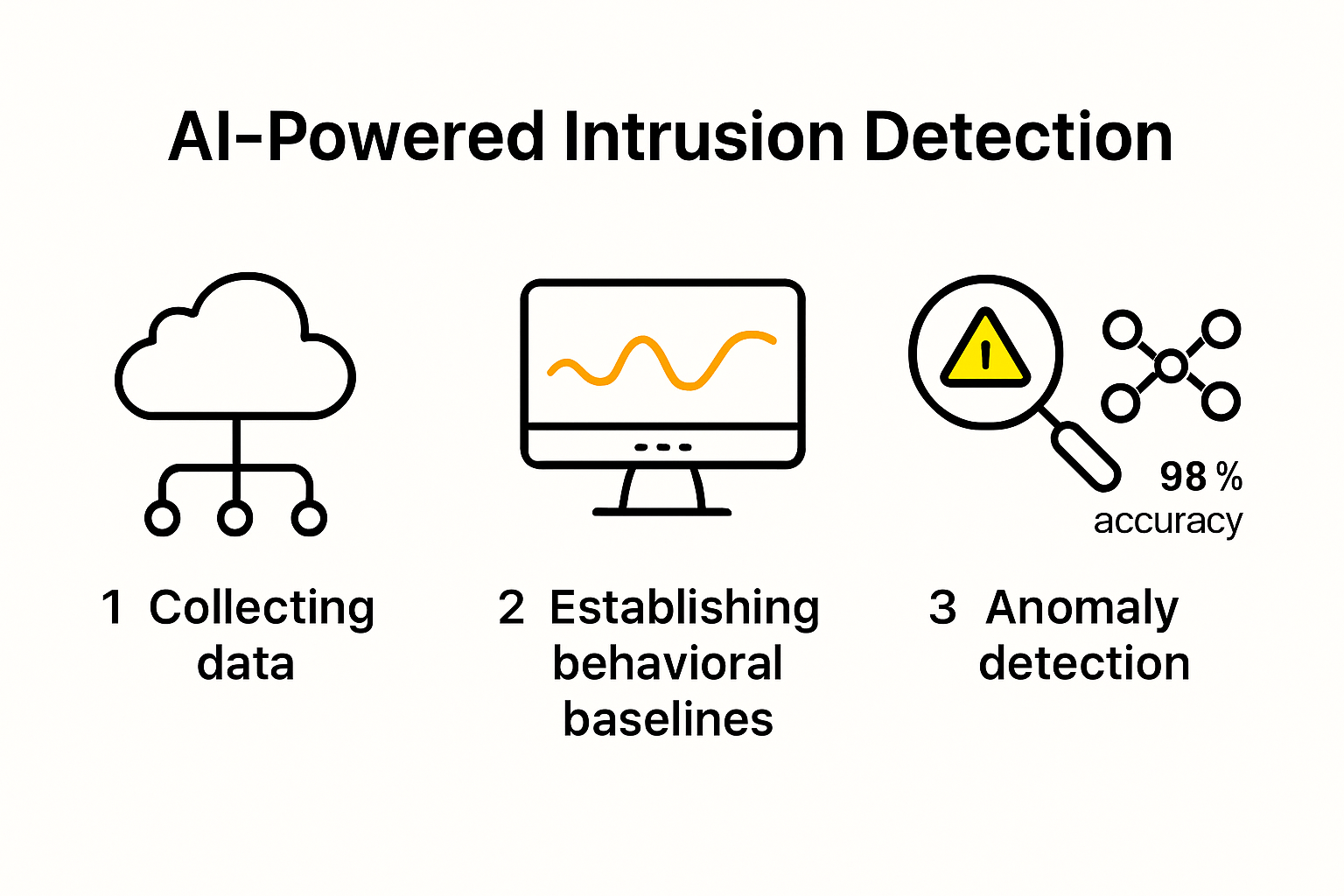
Advanced Intrusion Detection and Prevention
AI-powered intrusion detection systems represent a quantum leap in network security. Explore advanced security automation techniques that enable proactive threat management. According to the CyberSentinel research, modern AI systems can detect anomalous network behaviors with over 92% accuracy, substantially reducing potential vulnerability windows.
These intelligent systems continuously monitor network traffic, analyzing millions of data points in real time to identify potential security breaches. Machine learning algorithms create dynamic behavioral baselines, instantly flagging activities that deviate from normal patterns. Unlike traditional rule-based systems, AI can adapt and learn, recognizing emerging threat signatures that human analysts might miss.
Automated Threat Hunting and Incident Response
Automated threat hunting represents another critical use case where AI demonstrates remarkable capabilities. The cloud computing security study reveals that AI-driven systems can autonomously investigate potential security incidents, correlate complex threat indicators, and initiate targeted remediation protocols within milliseconds.
Traditional threat hunting required extensive manual investigation, consuming significant time and human resources. AI transforms this process by implementing intelligent, data-driven methodologies. Machine learning models can rapidly sift through vast amounts of log data, identifying subtle connections and potential attack vectors that would typically escape human detection.
Predictive Vulnerability Management
Predictive vulnerability management emerges as a groundbreaking application of AI in network protection. The systematic review on generative AI in cybersecurity highlights how artificial intelligence enables organizations to anticipate and mitigate potential security risks before they can be exploited.
By analyzing historical data, current network configurations, and emerging threat intelligence, AI can generate comprehensive risk assessments. These models simulate potential attack scenarios, identifying potential vulnerability chains and recommending preemptive security interventions. This approach shifts cybersecurity from a reactive to a proactive paradigm, allowing organizations to address potential weaknesses systematically.
As network environments become increasingly complex and distributed, AI stands at the forefront of intelligent security solutions. By combining advanced machine learning, predictive analytics, and autonomous response capabilities, AI is redefining how organizations protect their digital assets against an ever-evolving threat landscape.
To clarify the top applications and differences, here's a comparison table of key AI use cases in network protection:
| Use Case | Main Function | Key Benefits |
|---|---|---|
| Advanced Intrusion Detection & Prevention | Identifies and blocks anomalous network behavior | 92%+ accuracy; proactive threat detection |
| Automated Threat Hunting & Incident Response | Investigates and responds to incidents automatically | Rapid response; reduces manual workloads |
| Predictive Vulnerability Management | Anticipates and assesses potential vulnerabilities | Proactive mitigation; enhanced resilience |
Risks, Challenges, and Ethical Considerations
As artificial intelligence becomes increasingly integral to network security, organizations must navigate a complex landscape of technological, ethical, and regulatory challenges. The rapid advancement of AI capabilities brings unprecedented opportunities but also introduces significant risks that require careful consideration and strategic management.
AI System Vulnerabilities and Potential Exploitation
Explore AI security governance strategies that address emerging technological risks. According to the cybersecurity vulnerability research, AI systems themselves can become targets of sophisticated attacks designed to manipulate their decision making processes. These adversarial techniques can potentially trick AI algorithms into misclassifying threats or creating false security assessments.
The complexity of machine learning models creates inherent vulnerabilities. Attackers can develop sophisticated techniques like data poisoning, where malicious inputs are strategically introduced to compromise the AI's learning mechanisms. This means that the very systems designed to protect networks could potentially be turned into instruments of compromise if not carefully designed and continuously monitored.
Regulatory and Ethical Compliance Challenges
The integration of AI into network security raises profound ethical and regulatory questions. The global AI regulatory study emphasizes the critical need for comprehensive frameworks that ensure transparency, accountability, and privacy protection. Organizations must develop robust governance models that balance technological innovation with fundamental ethical principles.
Key ethical considerations include preventing algorithmic bias, ensuring transparent decision making processes, and maintaining individual privacy rights. AI systems must be designed to make fair and unbiased decisions, avoiding discriminatory patterns that could emerge from training data. This requires ongoing auditing, diverse training datasets, and sophisticated algorithmic design that prioritizes ethical considerations.
Global Coordination and Standardization Efforts
Addressing AI security challenges demands unprecedented levels of international collaboration. The Georgetown and Stanford Cyber Policy Center workshop highlighted the necessity of developing globally harmonized approaches to AI security governance. Different jurisdictions currently have varying regulatory standards, creating potential gaps in comprehensive cybersecurity strategies.
Effective global coordination requires creating shared standards for AI development, deployment, and monitoring. This includes establishing clear protocols for information sharing, developing consistent risk assessment methodologies, and creating mechanisms for rapid response to emerging AI-related security threats. Multinational cooperation becomes essential in creating resilient, adaptive security ecosystems that can respond to increasingly sophisticated cyber risks.
The future of network security lies not just in technological advancement, but in our ability to create intelligent, ethical, and collaborative approaches to managing AI technologies. Organizations must view AI not as a standalone solution, but as a complex tool requiring continuous oversight, refinement, and principled implementation.
The following table summarizes some of the major risks, challenges, and ethical considerations related to AI in network security as discussed above:
| Risk/Challenge | Description |
|---|---|
| AI System Vulnerabilities | AI models can be manipulated or attacked (e.g., adversarial attacks, data poisoning) |
| Regulatory & Ethical Compliance | Need for transparency, accountability, and privacy protection in AI systems |
| Algorithmic Bias | Potential for AI decisions to reflect or amplify biases in training data |
| Global Coordination & Standardization | Varying regulatory standards and lack of international harmonization |
Best Practices for Adopting AI Solutions
Successful implementation of artificial intelligence in network security requires a strategic, methodical approach that balances technological innovation with organizational readiness. Organizations must develop comprehensive strategies that go beyond mere technological deployment and address the complex ecosystem of people, processes, and technological infrastructure.
Incremental and Risk-Based AI Implementation
Learn about strategic AI adoption frameworks that minimize potential risks. According to the SANS Institute Guidelines, organizations should adopt AI solutions incrementally, starting with low-risk use cases and progressively expanding capabilities.
This approach involves carefully selecting initial AI applications that have minimal potential for significant disruption. By starting with narrow, well-defined use cases, organizations can build institutional knowledge, develop robust governance frameworks, and create a culture of responsible AI adoption. Each implementation phase should include comprehensive testing, performance evaluation, and continuous monitoring to ensure alignment with organizational security objectives.
Establishing Robust AI Governance Frameworks
Developing comprehensive AI governance is crucial for responsible technological integration. The World Economic Forum white paper emphasizes the importance of creating centralized AI governance boards that provide strategic oversight, establish clear policies, and ensure ethical AI deployment.
These governance frameworks should include detailed protocols for AI system development, deployment, monitoring, and decommissioning. Key components include defining clear accountability structures, establishing ethical guidelines, creating mechanisms for ongoing performance assessment, and developing transparent decision making processes. Organizations must also implement robust data management practices that protect sensitive information and ensure compliance with evolving regulatory requirements.

Comprehensive Security and Training Protocols
According to the CISA Cybersecurity Information Sheet, securing the entire AI ecosystem requires a holistic approach that extends beyond technological solutions. This involves developing comprehensive security protocols that protect the data used to train and operate AI systems, as well as investing in continuous staff training and skill development.
Organizations must create multi-layered security strategies that include rigorous data protection mechanisms, advanced encryption techniques, and continuous monitoring of AI system interactions. Equally important is developing a workforce capable of understanding, managing, and effectively utilizing AI technologies. This requires ongoing training programs that help employees understand AI capabilities, limitations, and potential security risks.
Successful AI adoption in network security is not about implementing the most advanced technology, but about creating a balanced, strategic approach that integrates technological innovation with organizational capabilities. By focusing on incremental implementation, robust governance, and comprehensive security protocols, organizations can harness the transformative potential of AI while maintaining a proactive and responsible approach to cybersecurity.
Frequently Asked Questions
What are the key benefits of using AI in network security?
AI enhances network security through predictive threat intelligence, real-time adaptive responses, and automated threat hunting, significantly improving threat detection and response times.
How does AI improve predictive threat intelligence in network security?
AI utilizes machine learning algorithms to analyze network traffic patterns and user behaviors, identifying vulnerabilities and potential threats with over 92% accuracy before they can be exploited.
What challenges do organizations face when integrating AI into their network security?
Organizations must navigate AI system vulnerabilities, regulatory compliance issues, and ethical concerns, including preventing algorithmic bias and ensuring transparent decision-making processes.
What best practices should organizations follow when adopting AI solutions for network security?
Organizations should implement AI incrementally, establish robust governance frameworks, and develop comprehensive security training protocols to effectively harness AI's potential while minimizing risks.
Take the Next Step in AI-Powered Network Security
If adapting to fast-changing cyber threats and managing complex security demands feels overwhelming, you're not alone. The article showed how artificial intelligence can anticipate threats and automate real-time responses, but many organizations still struggle with outdated manual processes. The pressure to prove strong security to clients and regulators can slow your responses and put deals at risk. Now is the time to bring AI from theory to practice for your security operations and sales enablement.

Ready to automate security workflows and gain instant control over risk assessments? Discover how Skypher's AI Questionnaire Automation Tool equips your team to eliminate bottlenecks in security reviews and accelerate the proof of concept process. Visit https://skypher.co to see how you can close security gaps, win trust with every questionnaire response, and protect your business for 2025. Make your move today and experience the next generation of AI-driven security compliance.
Recommended
- AI powered recommendation engine - Saasy - Webflow HTML Website Template
- The ever growing number of security questionnaires and what you and your company can do to face it
- Features
- Skypher - Security Questionnaires Automation
- AI Skills to Learn in 2025
- Der ultimative Leitfaden zur künstlichen Intelligenz: Eine tiefgehende Erkundung
