HIPAA violations can cost organizations up to $1.5 million per year for a single breach, making proper risk assessment more critical than ever. Safeguarding protected health information demands a systematic approach that addresses every potential vulnerability from data storage to daily access. By following a clear step-by-step process, you can protect patient trust, meet regulatory requirements, and reduce costly penalties with confidence.
Table of Contents
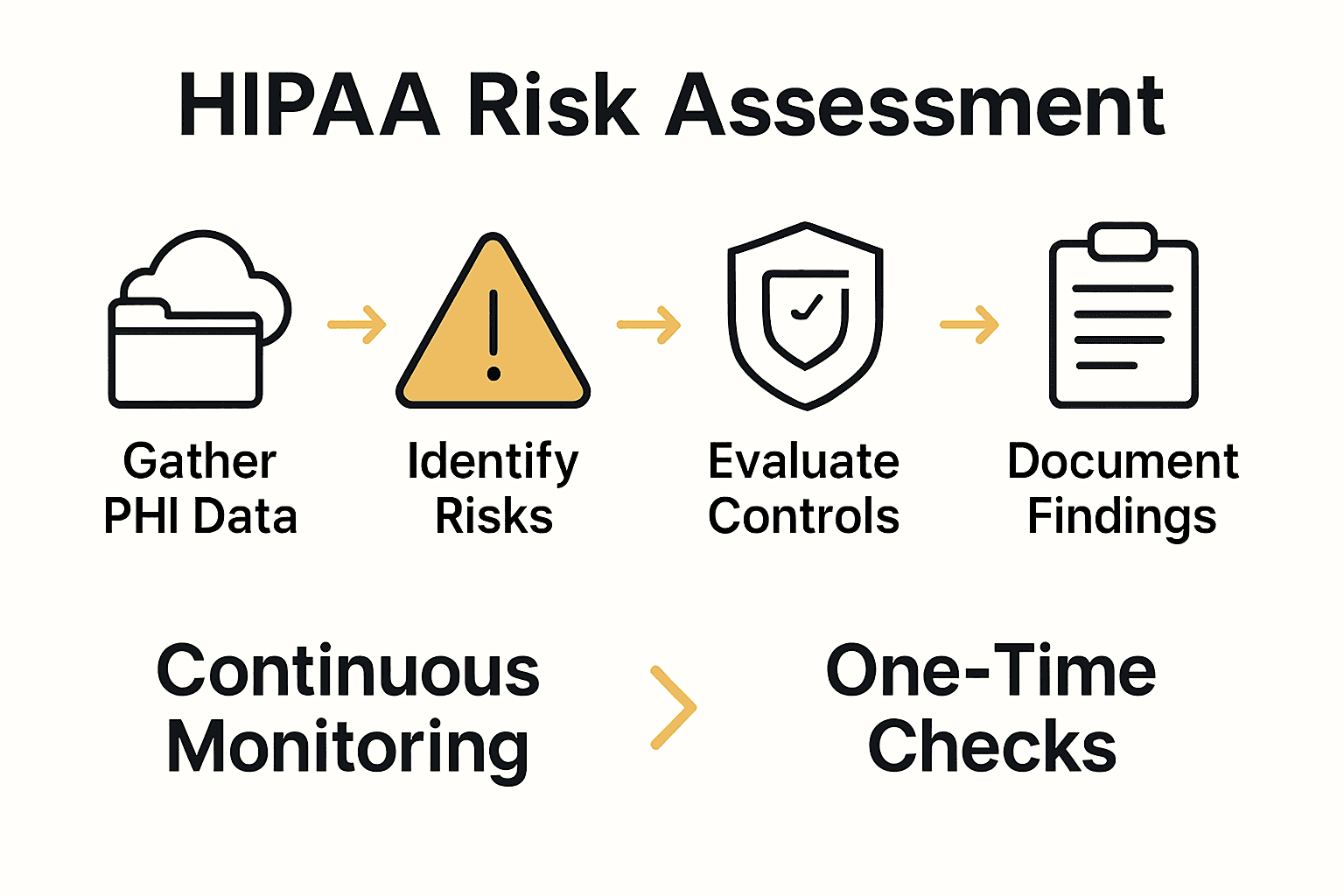
- Step 1: Gather And Organize HIPAA-Relevant Data
- Step 2: Identify Applicable Risks And Threats
- Step 3: Evaluate Controls And Assess Vulnerabilities
- Step 4: Document Findings And Mitigation Actions
- Step 5: Verify Risk Assessment Effectiveness
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Create a comprehensive PHI inventory | Document all locations of protected health information to enhance risk assessment accuracy. |
| 2. Identify internal and external threats | Conduct a thorough risk review to uncover vulnerabilities impacting patient data security. |
| 3. Evaluate the effectiveness of security controls | Systematically assess existing safeguards to identify weaknesses in data protection measures. |
| 4. Document all findings thoroughly | Maintain a detailed risk assessment report with clear mitigation strategies for compliance. |
| 5. Implement continuous monitoring practices | Establish an ongoing risk management approach to adapt to emerging threats and changes. |
Step 1: Gather and Organize HIPAA-Relevant Data
In this crucial first step of your HIPAA risk assessment, you will identify and catalog all electronic and physical systems that handle protected health information (PHI). According to HHS, this involves creating a comprehensive inventory of all devices and systems that interact with sensitive patient data.
Start by mapping out every location where PHI exists in your organization. This includes electronic health records, databases, cloud storage systems, physical file cabinets, email servers, mobile devices, and any other repositories holding patient information. As Accountable HQ recommends, document each system with specific details like storage method, access protocols, and current security measures.
Pro Tip: Create a detailed spreadsheet tracking each PHI location. Include columns for system name, data type, access permissions, current security controls, and potential vulnerabilities. This systematic approach will make your subsequent risk analysis much more thorough and actionable.

With your comprehensive PHI inventory complete, you are now ready to move to the next stage of assessing potential risks and vulnerabilities in your data management systems.
Step 2: Identify Applicable Risks and Threats
In this critical step of your HIPAA risk assessment, you will systematically uncover potential security vulnerabilities that could compromise the protection of electronic protected health information (ePHI). HHS emphasizes the importance of identifying threats that could impact the confidentiality, integrity, and availability of sensitive patient data.
Begin by conducting a comprehensive threat assessment across multiple domains. This includes evaluating internal risks such as employee access protocols, potential human errors, and system misconfigurations. External threats are equally crucial these involve cybersecurity risks like malware, phishing attacks, unauthorized network access, and potential data breaches from third party vendors. Consider scenarios such as accidental data exposure, intentional unauthorized access, system failures, and external cyber threats.
Pro Tip: Create a risk matrix that categorizes potential threats by their likelihood and potential impact. Rank each identified risk on a scale from low to critical, which will help you prioritize your mitigation strategies and allocate resources more effectively. Comprehensive Guide to Third Party Vendor Risk Assessment can provide additional insights into evaluating external risk factors.
With a clear understanding of your potential risks and threats, you are now prepared to move forward with analyzing and prioritizing these vulnerabilities to develop a robust HIPAA compliance strategy.
Step 3: Evaluate Controls and Assess Vulnerabilities
In this crucial phase of your HIPAA risk assessment, you will systematically review and analyze the effectiveness of your existing security controls and identify potential vulnerabilities in your electronic protected health information (ePHI) management systems. HHS emphasizes the importance of carefully evaluating current security measures to determine their ability to protect sensitive patient data.
Conduct a comprehensive vulnerability assessment by examining each system and process that handles ePHI. This involves a detailed review of technical safeguards such as access controls, encryption protocols, audit logs, and network security measures. Keragon recommends a thorough analysis that goes beyond surface level checks, including penetration testing, reviewing user access privileges, and examining potential weak points in your digital infrastructure. Pay special attention to areas like user authentication, data transmission security, and system backup procedures.
Pro Tip: Create a detailed vulnerability scorecard that rates each identified risk based on potential impact, likelihood of occurrence, and existing mitigation strategies. What is Vendor Risk Management? Understanding Its Importance and Implementation can provide additional insights into comprehensive risk evaluation techniques. Prioritize vulnerabilities that could potentially result in significant data breaches or compliance violations.
With a clear understanding of your current security controls and identified vulnerabilities, you are now prepared to develop a strategic plan for addressing and mitigating these potential risks.
Step 4: Document Findings and Mitigation Actions
In this critical documentation phase of your HIPAA risk assessment, you will systematically record all identified risks, vulnerabilities, and proposed mitigation strategies. HHS emphasizes that comprehensive documentation serves as crucial evidence of compliance and provides a foundational roadmap for ongoing risk management.
Create a detailed risk assessment report that includes a comprehensive breakdown of each identified vulnerability. Your documentation should encompass specific details such as the risk description, potential impact, likelihood of occurrence, existing controls, and recommended mitigation actions. Accountable HQ recommends structuring your report to include clear sections that outline the current state of security, identified gaps, and a strategic plan for addressing each vulnerability.
Pro Tip: Develop a standardized documentation template that allows for consistent tracking and easy updates. Ensure your report includes a prioritized action plan that ranks vulnerabilities by severity and potential impact, enabling your team to allocate resources effectively. SIG Assessment Guide 2025: Process, Benefits, and Tips can provide additional insights into creating comprehensive risk documentation.
With a meticulously documented risk assessment report, you are now prepared to present your findings to key stakeholders and begin implementing your strategic mitigation plan.
Step 5: Verify Risk Assessment Effectiveness
In this final phase of your HIPAA risk assessment, you will systematically validate and verify the effectiveness of your implemented security measures and risk mitigation strategies. HHS emphasizes that risk analysis is not a one-time event but an ongoing process that requires continuous evaluation and adaptation to emerging threats and organizational changes.
Conduct a comprehensive review of your risk assessment by performing multiple validation techniques. This includes internal audits, penetration testing, security simulations, and cross-referencing your documented vulnerabilities with actual system performance. Accountable HQ recommends scheduling annual comprehensive assessments to ensure your security controls remain robust and aligned with current regulatory requirements and emerging cybersecurity challenges.
Pro Tip: Implement a continuous monitoring approach that goes beyond annual assessments. Create a dynamic risk management framework that allows real-time tracking of security metrics, enabling your team to quickly identify and respond to potential vulnerabilities. 7 Essential Tips for Every GRC Analyst to Succeed can provide additional strategies for maintaining an agile and responsive risk management process.
With a thorough verification of your risk assessment effectiveness, you have established a strong foundation for ongoing HIPAA compliance and proactive cybersecurity management.
Simplify Your HIPAA Risk Assessment with Automated Security Questionnaire Solutions
Navigating the complex steps of a HIPAA risk assessment is challenging. From gathering PHI data to continuously verifying controls, every phase demands precision and timely responses. If your team is feeling overwhelmed by managing security questionnaires, maintaining thorough documentation, or coordinating mitigation plans, Skypher offers a streamlined solution designed specifically for organizations like yours.

Skypher’s AI Questionnaire Automation Tool accelerates completing security assessments by answering hundreds of questions in minutes. Benefit from real-time collaboration, seamless integrations with top third-party risk management platforms, and a customizable Trust Center that keeps your compliance efforts transparent and organized. Don’t let manual processes stall your HIPAA risk analysis or put patient data at risk. Visit Skypher now to explore how our platform helps B2B teams enhance accuracy, save valuable time, and power continuous risk verification without the headache. Start improving your HIPAA compliance workflow today by discovering the full capabilities at Skypher.
Frequently Asked Questions
What is the first step in assessing HIPAA risks for my B2B team?
Start by gathering and organizing all HIPAA-relevant data. Create a comprehensive inventory of all electronic and physical systems handling protected health information (PHI).
How do I identify potential risks during the HIPAA risk assessment process?
Identify potential risks by conducting a thorough threat assessment, evaluating both internal and external vulnerabilities. Focus on assessing employee access protocols and known cybersecurity risks like phishing or unauthorized access.
What controls should I evaluate during the HIPAA risk assessment?
Review the effectiveness of your existing security controls, including access controls, encryption, and network security measures. Conduct a vulnerability assessment to pinpoint weaknesses, ensuring you address high-risk areas first.
How can I document the findings from my HIPAA risk assessment?
Create a detailed risk assessment report that outlines identified risks, their potential impacts, and recommended mitigation strategies. Organize the document to clearly present current vulnerabilities, existing controls, and actions needed for compliance.
How do I verify the effectiveness of my risk assessment implementation?
Verify effectiveness by conducting internal audits and security simulations of your risk mitigation strategies. Schedule these reviews annually or more frequently to ensure ongoing compliance and adaptation to new threats.
What steps can I take to maintain continuous compliance with HIPAA regulations?
Implement a continuous monitoring approach for your security metrics and regularly update your risk management framework. Aim to perform routine evaluations, ideally every six months, to quickly identify and address any emerging vulnerabilities.
Recommended
- Understanding the HIPAA Security Rule for Businesses
- Comprehensive Guide to Third Party Vendor Risk Assessment
- SIG Assessment Guide 2025: Process, Benefits, and Tips
- Mitigate Vendor Management Risks Effectively in 2025
- Navigating the New Normal: A Proactive Approach to Healthcare Data Security - Stratgetic IT Consultants for Accountants
- Risk management and testing - Berriault and Associates Consulting Group
