Manual compliance processes drain valuable hours for security teams, yet SOC report reviews remain vital for every American and international tech firm leveraging cloud solutions. With more than 60 percent of breaches linked to third-party failures, the demand for efficient, automated AWS SOC submissions continues to rise. Mid to large technology organizations now face pressure to validate robust cybersecurity practices quickly and confidently, prompting urgent exploration of tools that enhance both accuracy and peace of mind.
Table of Contents
- Defining AWS SOC Reports And Their Purpose
- Types Of AWS SOC Reports And Key Differences
- How AWS SOC Reports Support Cloud Compliance
- Automation Tools For AWS SOC Report Management
- Avoiding Common Pitfalls In SOC Submissions
Key Takeaways
| Point | Details |
|---|---|
| Understanding SOC Reports | SOC reports are vital for assessing and validating internal security controls of technology service organizations, particularly AWS, focusing on security and compliance. |
| Types of SOC Reports | The main types are SOC 1, SOC 2, and SOC 3, each tailored for specific audiences and purposes, with SOC 2 being crucial for cloud service providers. |
| Automation in Compliance | Implementing automation tools, including Infrastructure as Code and SIEM platforms, significantly enhances SOC report management efficiency and accuracy. |
| Avoiding Submission Pitfalls | Organizations must carefully document their controls and audit processes to avoid common issues that can undermine the integrity of SOC report submissions. |
Defining AWS SOC Reports and Their Purpose
System and Organization Controls (SOC) reports represent a critical framework for technology service organizations to validate their internal security controls. Developed by the American Institute of Certified Public Accountants (AICPA), these comprehensive audit reports help organizations demonstrate effective controls across critical operational domains.
AWS SOC reports specifically focus on evaluating cloud infrastructure security mechanisms through five primary trust service criteria: security, availability, processing integrity, confidentiality, and privacy. These reports provide third-party validation that Amazon Web Services maintains rigorous control standards protecting client data and system operations. Organizations leveraging AWS can utilize these reports to understand the platform's robust security infrastructure and compliance mechanisms.
The primary purpose of SOC reports extends beyond mere documentation. They serve as a critical risk management tool, enabling businesses to assess vendor security practices, validate control effectiveness, and ensure alignment with industry regulatory requirements. SOC reports help organizations manage third-party risks by providing detailed assurance about vendors' control frameworks, ultimately supporting transparent and secure technological ecosystems.
Pro tip: When reviewing AWS SOC reports, focus specifically on the trust service criteria most relevant to your organization's unique security and compliance requirements.
Types of AWS SOC Reports and Key Differences
SOC reporting encompasses three primary types, each serving distinct purposes in assessing organizational controls and security frameworks. SOC reports range from financial assessments to comprehensive security evaluations, providing organizations with nuanced insights into their operational effectiveness and risk management strategies.
The three primary SOC report types include SOC 1, SOC 2, and SOC 3, each with unique characteristics and target audiences. SOC 1 reports concentrate on financial reporting controls, specifically examining how an organization's information technology systems impact financial statement accuracy. SOC 2 reports offer a more comprehensive security assessment, diving deep into five critical trust service criteria: security, availability, processing integrity, confidentiality, and privacy. These reports are particularly crucial for cloud service providers like AWS, as they validate robust security mechanisms protecting client data and operational infrastructure.

SOC 3 reports differ significantly from their counterparts by providing a publicly accessible summary of SOC 2 audit results. Unlike SOC 1 and SOC 2 reports, which are typically confidential and distributed to specific stakeholders, SOC 3 reports offer a generalized overview of an organization's control environment suitable for broader distribution. This transparency allows potential clients and partners to quickly assess an organization's commitment to security and compliance without revealing sensitive technical details.
Here's a quick comparison of AWS SOC report types for reference:
| SOC Report Type | Main Focus | Audience | Distribution |
|---|---|---|---|
| SOC 1 | Financial reporting controls | Auditors, regulators | Restricted, specific parties |
| SOC 2 | Trust service criteria and security | Technical stakeholders, clients | Restricted, contractual partners |
| SOC 3 | Public summary of SOC 2 | General public, prospects | Publicly available, broad access |
Pro tip: When evaluating cloud service providers, prioritize SOC 2 reports as they offer the most comprehensive insights into security controls and operational practices.
How AWS SOC Reports Support Cloud Compliance
Cloud service providers face increasingly complex security challenges that demand robust, transparent compliance mechanisms. AWS SOC reports serve as a critical framework for demonstrating comprehensive security controls, offering organizations a detailed mechanism to validate their cloud infrastructure's integrity and operational resilience.
The primary value of AWS SOC reports lies in their ability to provide independent, third-party validation of security practices across five critical trust service criteria. Security assessments focus on preventing unauthorized access, availability controls ensure system reliability, processing integrity validates data accuracy, confidentiality protects sensitive information, and privacy controls safeguard personal data. These comprehensive evaluations enable AWS to prove that its cloud infrastructure meets rigorous industry standards, giving clients confidence in the platform's security architecture.
Compliance verification becomes significantly more straightforward through SOC reports, particularly for regulated industries like healthcare and financial services. SOC 2 reports specifically help organizations in highly regulated sectors meet complex compliance requirements by providing a standardized, independent assessment of control effectiveness. This approach allows businesses to quickly understand and mitigate potential security risks associated with cloud computing, transforming complex regulatory challenges into manageable, transparent processes.
Pro tip: Request and thoroughly review the most recent SOC 2 report when evaluating cloud service providers, focusing specifically on the trust service criteria most relevant to your organization's unique security requirements.
Automation Tools for AWS SOC Report Management
Automation technologies are revolutionizing security compliance management within cloud environments, offering unprecedented capabilities for streamlining AWS SOC report processes. Organizations can now leverage sophisticated tools that transform complex compliance requirements into efficiently managed, repeatable workflows.
AWS provides multiple automation mechanisms to support SOC report management. Infrastructure as Code (IaC) tools like AWS CloudFormation enable teams to define and provision cloud infrastructure consistently, ensuring standardized security configurations. Continuous monitoring tools automatically track system configurations, detect potential compliance deviations, and generate real-time reports that align with SOC reporting requirements. These automated systems dramatically reduce manual intervention, minimizing human error and accelerating the compliance verification process.
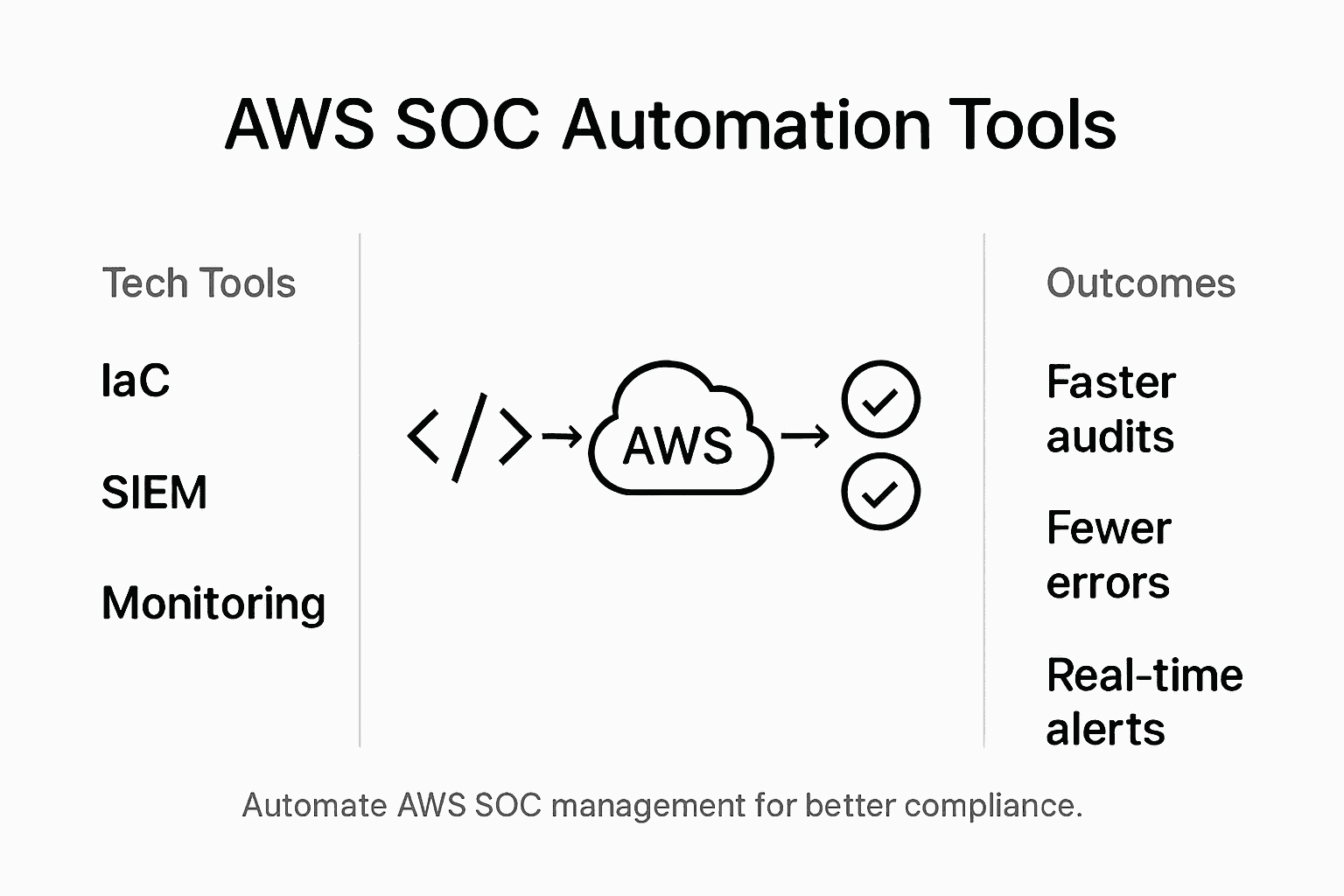
Security Information and Event Management (SIEM) technologies play a critical role in comprehensive SOC report automation. Advanced SIEM tools integrate data from multiple sources to provide holistic security insights and support compliance reporting. These platforms enable organizations to aggregate security events, perform sophisticated threat analysis, and generate detailed compliance documentation with unprecedented speed and accuracy. By automating log collection, correlation, and reporting, businesses can maintain robust security postures while significantly reducing the administrative overhead associated with SOC report preparation.
These automation tools play distinct roles in AWS SOC report management:
| Tool Category | Purpose | Example AWS Technologies |
|---|---|---|
| Infrastructure as Code | Ensures consistent security setups | AWS CloudFormation |
| Continuous Monitoring | Tracks compliance and detects issues | AWS Config, AWS CloudWatch |
| SIEM Platforms | Aggregates and analyzes events | Amazon Security Lake, AWS GuardDuty |
Pro tip: Implement a comprehensive automation strategy that combines Infrastructure as Code, continuous monitoring tools, and integrated SIEM platforms to create a robust, self-documenting compliance management ecosystem.
Avoiding Common Pitfalls in SOC Submissions
SOC report submissions present complex challenges that can derail even well-prepared organizations, requiring strategic approaches to mitigate potential compliance risks. Understanding these potential pitfalls is crucial for maintaining the integrity and effectiveness of security control assessments.
One of the most significant challenges organizations encounter involves misinterpreting audit documentation and control frameworks. Scope misalignment frequently occurs when companies fail to comprehensively document their system boundaries, leading to incomplete or inaccurate representations of their security controls. Effective SOC report reviews demand meticulous attention to the auditor's opinion, system description, and operating effectiveness of implemented controls. Critical evaluation requires examining material exceptions, understanding qualified opinions, and ensuring all trust service criteria receive appropriate scrutiny.
Technical teams must also address operational limitations that can compromise SOC report quality. Common technical pitfalls include insufficient automation, excessive false positive alerts, and inadequate incident response capabilities. Organizations should invest in robust monitoring systems, implement sophisticated filtering mechanisms to reduce alert fatigue, and develop clear, documented processes for managing potential security events. By creating a proactive compliance strategy that emphasizes continuous improvement and precise documentation, businesses can transform potential vulnerabilities into demonstrable security strengths.
Pro tip: Conduct periodic internal mock audits to identify and address potential control gaps before official SOC report submissions, treating these rehearsals as critical opportunities for refining your compliance approach.
Accelerate Your AWS SOC Report Compliance with Skypher
Navigating AWS SOC reports involves managing complex security criteria and detailed documentation that can overwhelm even the most experienced teams. From ensuring accurate control scopes to streamlining continuous monitoring and audit responses, the process demands precision and speed to avoid costly delays and compliance risks. Skypher understands these challenges and offers an AI-driven SaaS platform tailored to optimize your security questionnaire workflows—making SOC compliance faster, more accurate, and less stressful.

Experience the power of our AI Questionnaire Automation Tool, designed specifically for organizations in tech and finance facing rigorous AWS SOC report demands. Skypher integrates seamlessly with over 40 risk management platforms, including ServiceNow and Slack, enabling real-time collaboration and automated responses to hundreds of security questions in under a minute. Our customizable Trust Center and powerful API integrations ensure your compliance teams can focus on what matters most while maintaining impeccable audit readiness. Take control now and reduce your proof of concept cycles by boosting operational productivity and enhancing client trust. Visit Skypher to transform how you handle security compliance and submit SOC reports with confidence.
Frequently Asked Questions
What are AWS SOC reports, and why are they important?
AWS SOC reports, developed by the AICPA, validate the internal security controls of technology service organizations, ensuring they meet rigorous standards for protecting client data and system operations. They are crucial for risk management and ensuring compliance with industry regulations.
What are the main types of AWS SOC reports?
The three primary types of AWS SOC reports are SOC 1, SOC 2, and SOC 3. SOC 1 focuses on financial reporting controls, SOC 2 covers security assessments based on trust service criteria, and SOC 3 provides a public summary of SOC 2 results for broader access.
How do AWS SOC reports help with cloud compliance?
AWS SOC reports provide third-party validation of security practices across key areas such as security, availability, processing integrity, confidentiality, and privacy. They assist companies in regulated industries by demonstrating compliance with relevant standards and simplifying the compliance verification process.
What automation tools can assist in managing AWS SOC reports?
Automation tools like Infrastructure as Code (IaC) tools, continuous monitoring systems, and Security Information and Event Management (SIEM) technologies help streamline SOC report management by ensuring consistent security configurations, tracking compliance deviations, and supporting detailed compliance documentation.