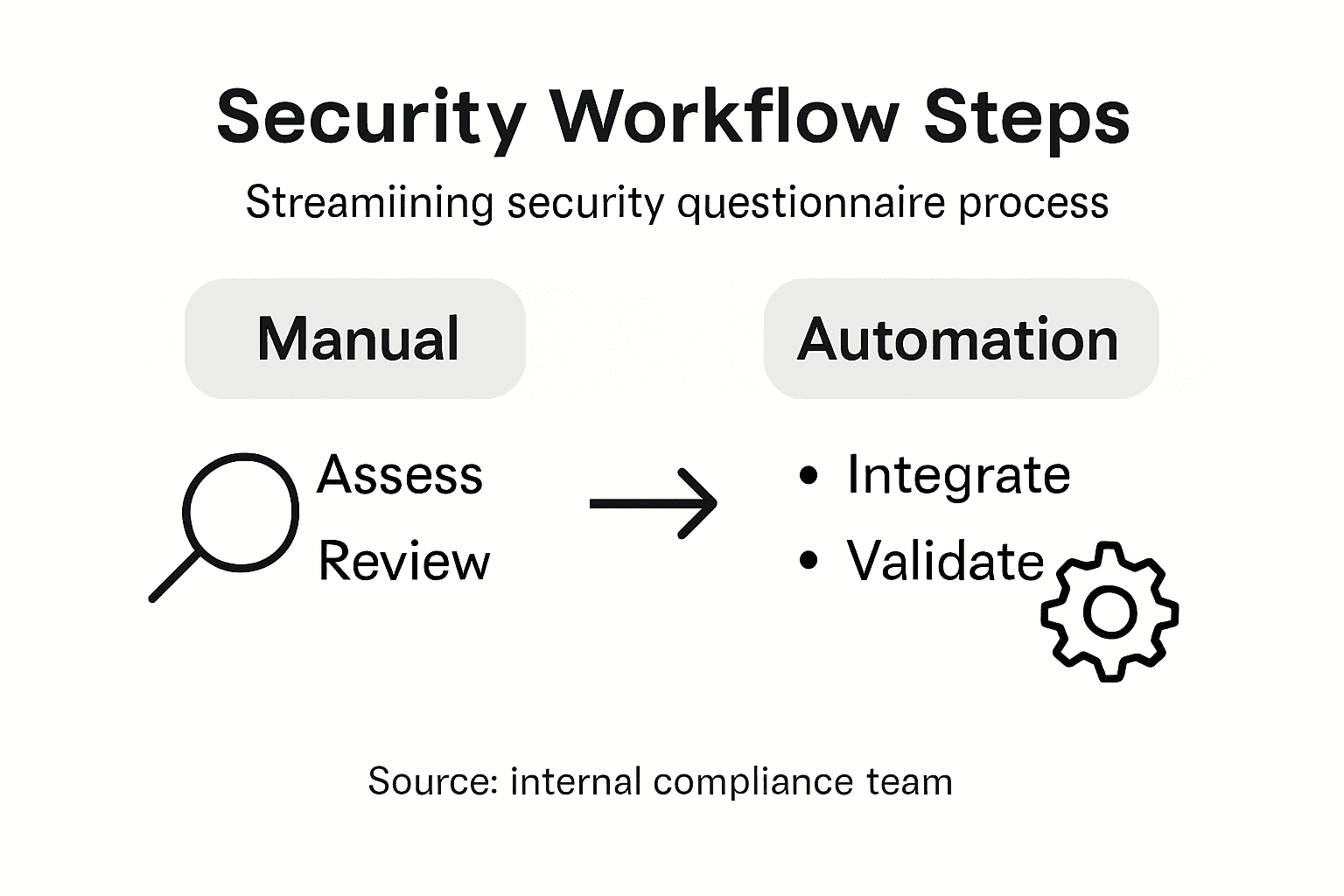
Over half of American compliance teams report spending more than 10 hours on each security questionnaire, draining resources and creating bottlenecks. When productivity matters, every inefficient step slows project timelines and exposes your organization to unnecessary risks. This guide reveals practical strategies for compliance administrators to overhaul security questionnaire workflows, spotlighting how automation and smart integration can simplify collaboration and drive real results.
Table of Contents
- Step 1: Assess Existing Security Questionnaire Processes
- Step 2: Implement AI-Driven Automation Tools
- Step 3: Integrate Core Platforms and Third-Party Services
- Step 4: Collaborate with Stakeholders for Real-Time Review
- Step 5: Verify Accuracy and Finalize Questionnaire Responses
Quick Summary
| Main Insight | Explanation |
|---|---|
| 1. Assess Workflow Efficiency | Evaluate your existing security questionnaire process to identify inefficiencies and improvement opportunities. |
| 2. Leverage AI Tools | Implement AI-driven automation to reduce manual processing time and improve accuracy in handling questionnaires. |
| 3. Integrate Systems Seamlessly | Connect automation tools with core platforms to streamline operations and ensure data accuracy across systems. |
| 4. Foster Real-Time Collaboration | Establish transparent communication channels among stakeholders for efficient, simultaneous document reviews. |
| 5. Ensure Rigorous Review Process | Create a systematic approach for verifying the accuracy of questionnaire responses before submission. |
Step 1: Assess Existing Security Questionnaire Processes
Assessing your organization's current security questionnaire workflow is the critical first step toward identifying inefficiencies and opportunities for improvement. This systematic evaluation will help you understand how your team currently manages and responds to complex security assessments.
Start by mapping out your entire security questionnaire process from initial receipt to final submission. Review current cybersecurity measurement approaches to understand how your existing methods align with industry standards. Document each stage of the workflow including who receives questionnaires, how they are routed, who answers specific sections, how responses are validated, and how final documents are compiled and submitted.
Collect quantitative data to support your assessment. Track metrics like average response time, number of questionnaires processed monthly, error rates, and collaboration bottlenecks. Conduct interviews with team members to uncover qualitative insights about current challenges. Pay special attention to recurring pain points such as duplicative work, information retrieval difficulties, and communication gaps between departments.
Pro tip: Create a visual workflow diagram that maps out each step of your security questionnaire process to help identify potential optimization opportunities.
Step 2: Implement AI-Driven Automation Tools
Implementing AI-driven automation tools will transform your security questionnaire workflow by dramatically reducing manual processing time and improving overall response accuracy. This strategic approach enables your team to handle complex security assessments more efficiently and consistently.
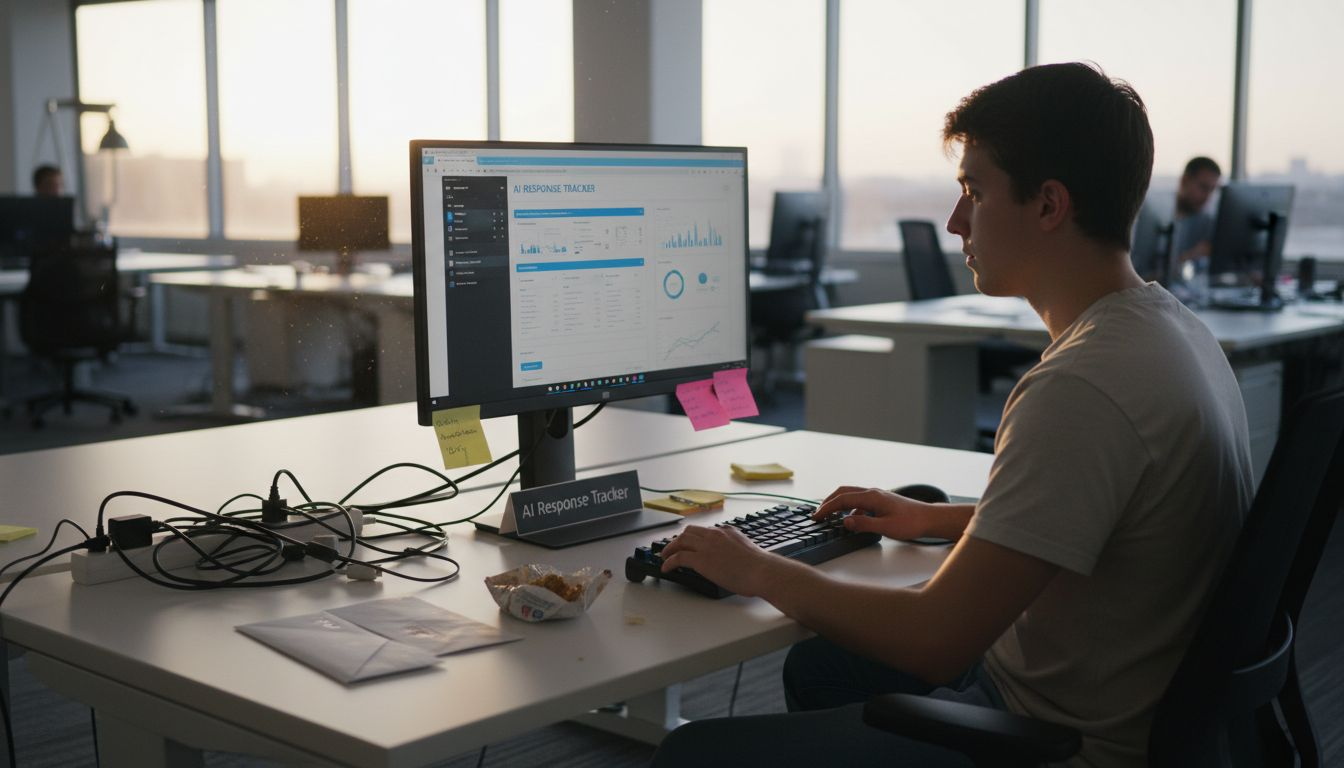
Begin by selecting an AI solution that can automate repetitive security tasks through advanced natural language processing capabilities. Evaluate potential tools based on their ability to understand context, extract relevant information, and generate accurate responses across different questionnaire formats. Look for solutions with machine learning algorithms that can adapt to your specific industry requirements and organizational documentation.
Integrate the chosen AI tool into your existing workflow by conducting a comprehensive pilot program. Start with a small subset of questionnaires to validate the tool's performance and accuracy. Configure the system to access your existing knowledge bases, compliance documentation, and standard response templates. Establish clear guidelines for human review and intervention to maintain quality control while leveraging AI capabilities for initial drafting and information retrieval.
Pro tip: Develop a staged implementation plan that allows gradual AI tool adoption, ensuring your team can adapt and optimize the automation process without disrupting current operations.
Here's a comparative overview of manual versus AI-driven security questionnaire processing:
| Aspect | Manual Processing | AI-Driven Automation |
|---|---|---|
| Average Response Time | Typically several days | Often hours or less |
| Error Rates | Higher due to human oversight | Lower with automated checks |
| Scalability | Limited by team capacity | High, supports large volume |
| Consistency | Varies between respondents | Uniform automated output |
Step 3: Integrate Core Platforms and Third-Party Services
Integrating your security questionnaire automation tools with core platforms and third-party services is crucial for creating a seamless and efficient workflow. This step will help you establish interconnected systems that enhance data sharing, accuracy, and overall compliance management.
Start by mapping enterprise system integrations through comprehensive open API connections. Identify key platforms such as risk management systems, identity verification tools, compliance tracking software, and communication channels that can streamline your security questionnaire process. Focus on solutions that offer robust API capabilities, enabling real-time data exchange and automated information synchronization across different organizational systems.
Carefully evaluate each potential integration point by assessing compatibility, security protocols, and data transfer mechanisms. Develop a detailed integration roadmap that prioritizes critical connections and minimizes potential disruptions to existing workflows. Implement integrations incrementally, starting with core platforms that have the most immediate impact on your security questionnaire management. Establish clear data governance standards to ensure consistent information handling and maintain compliance with regulatory requirements across all integrated systems.
Pro tip: Create a detailed integration matrix that documents each platform connection, mapping out specific data flows and establishing clear ownership for maintenance and troubleshooting.
Refer to this summary to understand key integration points for optimizing security questionnaire workflows:
| Integration Type | Purpose | Example Platform |
|---|---|---|
| Risk Management | Align security with business risk | LogicGate, Archer |
| Identity Verification | Confirm stakeholders’ credentials | Okta, Auth0 |
| Compliance Tracking | Monitor regulatory adherence | Vanta, OneTrust |
| Communication | Enable real-time review | Slack, Microsoft Teams |
Step 4: Collaborate with Stakeholders for Real-Time Review
Creating an effective collaborative environment for security questionnaire reviews requires strategic coordination and transparent communication across multiple organizational stakeholders. This step focuses on establishing seamless real-time review processes that enhance accuracy and responsiveness.
Begin by establishing collaborative research frameworks that enable continuous stakeholder engagement. Identify key participants from departments such as legal, compliance, information security, and risk management who will contribute to the security questionnaire review process. Implement a centralized platform that allows simultaneous document access, real-time commenting, and transparent tracking of modifications. Develop clear protocols for feedback submission, ensuring that each stakeholder understands their role and can provide input efficiently without creating bottlenecks in the review workflow.
Design a dynamic review mechanism that supports rapid iteration and collaborative problem solving. Establish time-sensitive review windows with defined escalation paths for critical sections that require immediate attention. Create a standardized communication protocol that enables stakeholders to flag potential issues, request clarifications, and validate responses quickly. Integrate notification systems that alert relevant team members about pending reviews, ensuring no critical feedback gets overlooked and maintaining a proactive approach to security questionnaire management.
Pro tip: Develop a stakeholder communication matrix that clearly defines review responsibilities, expected response times, and escalation procedures to streamline collaborative efforts.
Step 5: Verify Accuracy and Finalize Questionnaire Responses
Finishing your security questionnaire requires a meticulous verification process that ensures every response meets the highest standards of accuracy and compliance. This critical final stage transforms your draft into a comprehensive and reliable document ready for submission.
Conduct a comprehensive systematic review of questionnaire responses using a structured validation approach. Create a detailed checklist that covers key verification criteria including consistency across different sections, alignment with organizational policies, technical accuracy, and completeness of information. Engage subject matter experts from relevant departments to cross-validate complex technical or compliance related responses. Implement a multi-tier review process where responses pass through technical experts, compliance officers, and legal representatives to ensure comprehensive validation.
Establish a final quality assurance protocol that includes automated and manual verification techniques. Utilize advanced validation tools that can cross reference responses against internal documentation, compliance frameworks, and industry standards. Conduct a final read through that focuses on identifying potential contradictions, ambiguous language, or incomplete explanations. Develop a standardized scoring mechanism that rates each response based on clarity, comprehensiveness, and alignment with organizational security standards. Maintain a transparent audit trail documenting all modifications and review stages to support future compliance requirements and continuous improvement efforts.
Pro tip: Create a final verification template with predefined scoring criteria to streamline your review process and maintain consistent quality across different security questionnaires.
Unlock Effortless Security Questionnaire Management with Skypher
The article highlights the challenges organizations face when managing complex security questionnaires such as inefficiencies, manual errors, and collaboration bottlenecks. If you've experienced slow response times, struggle with maintaining accuracy, or need seamless real-time collaboration among stakeholders, you are not alone. Terms like AI-driven automation, real-time review, and API integrations point to the future of security questionnaire workflows, and Skypher captures these advancements perfectly.
Skypher's AI Questionnaire Automation Tool offers unmatched speed and precision, capable of answering hundreds of questions in under a minute while reducing human errors significantly. The platform supports integration with over 30 popular risk management tools and communication apps such as Slack and Microsoft Teams, enabling true collaboration and transparency. With customizable Trust Centers and multilingual support, you can streamline your security reviews and compliance checks effortlessly.
Experience firsthand how to accelerate your security questionnaire responses, enhance collaboration, and automate validation steps all in one place.

Ready to transform your compliance workflow Today Explore how Skypher can elevate your security questionnaire management with cutting-edge AI and seamless integrations Visit Skypher now and see why medium and large organizations in tech and finance trust us to reduce turnaround times and improve operational productivity. Learn more about our AI Questionnaire Automation Tool, discover our Collaboration and Real-Time Integration, and leverage extensive API Integrations with TPRM Platforms for an end-to-end solution.
Frequently Asked Questions
How do I assess our existing security questionnaire processes?
To assess your existing security questionnaire processes, start by mapping out the entire workflow from initial receipt to final submission. Document each stage, identify pain points, and collect quantitative data such as average response time and error rates within a month.
What are the benefits of implementing AI-driven automation tools in our security questionnaire workflow?
Implementing AI-driven automation tools can reduce manual processing time and improve response accuracy. Aim to handle complex assessments more efficiently by selecting an AI solution that automates repetitive tasks, potentially cutting response times from days to hours.
How can I integrate core platforms with our security questionnaire automation tools?
To integrate core platforms with automation tools, map out enterprise system connections and identify key platforms that will enhance data sharing. Develop an integration roadmap and start with critical connections to ensure you maintain a smooth workflow without disruptions.
What steps should I take to facilitate real-time reviews among stakeholders?
Facilitate real-time reviews by establishing a centralized platform for document access and feedback. Create clear protocols for feedback submission and set defined review windows to ensure timely responses, reducing bottlenecks in the review process.
How can I verify the accuracy of our security questionnaire responses?
To verify the accuracy of security questionnaire responses, implement a systematic review process that includes a detailed checklist of verification criteria. Engage subject matter experts to cross-validate key responses, aiming for a thorough review process that maintains high quality before final submission.
What tools can help streamline our security questionnaire workflow?
Consider adopting tools that automate repetitive tasks and provide centralized platforms for collaboration and document access. Using these tools can significantly enhance your workflow efficiency, potentially reducing response times and improving accuracy across the board.