Managing compliance with third-party vendors is a high-stakes task for any B2B company. Risk is everywhere and the consequences of a single vendor error can be staggering. Research shows that 63 percent of data breaches are linked to third-party vendors. It sounds overwhelming to keep tabs on dozens of providers, but most companies get this all wrong. The smartest teams are turning vendor management into a powerful advantage, not just another box to check.
Table of Contents
- Core Principles Of Compliance Vendor Management
- Building An Effective Vendor Oversight Program
- Key Risks And How To Mitigate Them
- Leveraging Technology For Better Compliance Outcomes
Quick Summary
| Takeaway | Explanation |
|---|---|
| Develop a Comprehensive Risk Assessment Framework | Implement systematic processes to evaluate vendors on cybersecurity, compliance, and financial stability. |
| Establish Continuous Monitoring Mechanisms | Regularly review vendor performance and compliance to identify potential risks early. |
| Implement Strong Contractual Governance | Create clear agreements detailing compliance expectations, security protocols, and consequences. |
| Leverage Technology for Compliance | Use automation and blockchain to enhance vendor data tracking and risk management capabilities. |
| Prioritize Cybersecurity in Vendor Relationships | Conduct thorough security assessments and impose mandatory security standards for all vendors. |
Core Principles of Compliance Vendor Management
Compliance vendor management represents a strategic approach organizations use to effectively assess, select, monitor, and manage third-party vendors while ensuring regulatory adherence and minimizing potential risks. Understanding the core principles is critical for businesses seeking to maintain robust security and operational integrity.
To help you quickly compare the core principles of compliance vendor management, the following table summarizes each principle along with its key components:
| Core Principle | Description | Key Components |
|---|---|---|
| Comprehensive Risk Assessment Framework | Systematic evaluation of vendors across key risk areas | Background checks, compliance review, security evaluation |
| Ongoing Monitoring and Performance Mgmt | Dynamic tracking of vendor performance and compliance | Audits, metrics, security reassessment, communication |
| Strategic Contractual Governance | Clear agreements defining compliance and consequences | Requirements, audit rights, breach protocols, standards |
Comprehensive Risk Assessment Framework
A fundamental principle of compliance vendor management involves developing a comprehensive risk assessment framework. Research from the American Institute of CPAs (AICPA) reveals that successful organizations implement systematic processes to evaluate potential vendors across multiple dimensions. This approach goes beyond surface-level evaluations and delves into detailed assessments of a vendor's cybersecurity protocols, regulatory compliance history, financial stability, and operational capabilities.
Key components of an effective risk assessment include:
- Vendor Background Verification: Conducting thorough background checks and examining the vendor's track record in handling sensitive information.
- Compliance Documentation Review: Analyzing existing compliance certifications, audit reports, and regulatory conformance evidence.
- Security Control Evaluation: Assessing the vendor's technological infrastructure, data protection mechanisms, and incident response capabilities.
Ongoing Monitoring and Performance Management
Research published on arXiv highlights the critical importance of continuous vendor performance monitoring. Organizations cannot treat vendor relationships as static arrangements but must implement dynamic evaluation mechanisms that track vendor performance, compliance status, and potential emerging risks.
Effective ongoing monitoring involves:
- Regular compliance audits and assessments
- Performance metrics tracking
- Periodic security control reassessments
- Maintaining transparent communication channels
This approach ensures that vendors consistently meet established standards and can quickly adapt to changing regulatory requirements. By implementing proactive monitoring strategies, businesses can identify potential compliance gaps before they escalate into significant operational or legal challenges.
Strategic Contractual Governance
The final core principle centers on establishing robust contractual frameworks that explicitly define compliance expectations, responsibilities, and consequences. Venable LLP's compliance management insights emphasize the necessity of clear, comprehensive agreements that outline precise compliance requirements, reporting mechanisms, and potential remediation processes.
Critical elements of strategic contractual governance include:
- Explicit compliance and security requirements
- Right-to-audit clauses
- Clear breach notification protocols
- Defined performance standards and consequences
- Mechanisms for contract modification and termination
By integrating these core principles into their vendor management approach, organizations can create a resilient, proactive framework that minimizes risks, ensures regulatory compliance, and supports sustainable business relationships. The key lies in treating vendor management as a strategic function rather than a mere administrative task.
Building an Effective Vendor Oversight Program
Building an effective vendor oversight program requires a strategic and comprehensive approach that goes beyond traditional compliance checkboxes. Organizations must develop a robust framework that enables proactive risk management, continuous evaluation, and alignment with business objectives.
Strategic Vendor Risk Assessment and Classification
Research from the Federal Reserve Bank of Philadelphia emphasizes the critical importance of conducting thorough due diligence and developing detailed risk assessments for each vendor relationship. This process involves categorizing vendors based on their potential impact on organizational operations, compliance requirements, and security risks.
Key components of an effective vendor risk assessment include:
- Risk Tier Categorization: Evaluating vendors across multiple risk dimensions such as data access, financial exposure, and regulatory compliance.
- Initial and Ongoing Due Diligence: Implementing comprehensive screening processes that examine vendor financial stability, operational capabilities, and historical performance.
- Comprehensive Documentation: Maintaining detailed records of vendor assessments, including background checks, compliance certifications, and risk profile documentation.
Continuous Performance Monitoring and Evaluation
ISACA's vendor management guidelines highlight the significance of establishing robust monitoring mechanisms that track vendor performance and compliance consistently. Organizations must move beyond periodic reviews and implement dynamic, real-time evaluation systems.
Effective monitoring strategies encompass:
- Regular performance scorecards
- Automated compliance tracking
- Periodic security and operational audits
- Transparent reporting mechanisms
- Structured communication protocols
This approach enables organizations to identify potential risks early, address performance gaps, and maintain alignment with established service level expectations.
Comprehensive Governance and Contractual Framework
Fannie Mae's STAR Reference Guide underscores the importance of establishing clear governance structures and contractual frameworks that define expectations, responsibilities, and compliance requirements. An effective oversight program must include precise mechanisms for vendor management, performance evaluation, and potential remediation.
Critical elements of a robust governance framework include:
- Clearly defined performance metrics
- Explicit compliance requirements
- Right-to-audit clauses
- Incident response and breach notification protocols
- Mechanisms for contract modification and termination
By implementing a comprehensive vendor oversight program that integrates strategic risk assessment, continuous monitoring, and strong governance principles, organizations can effectively manage third-party relationships while minimizing potential risks and ensuring regulatory compliance. The key lies in treating vendor management as a dynamic, strategic function that requires ongoing attention and proactive management.
Key Risks and How to Mitigate Them
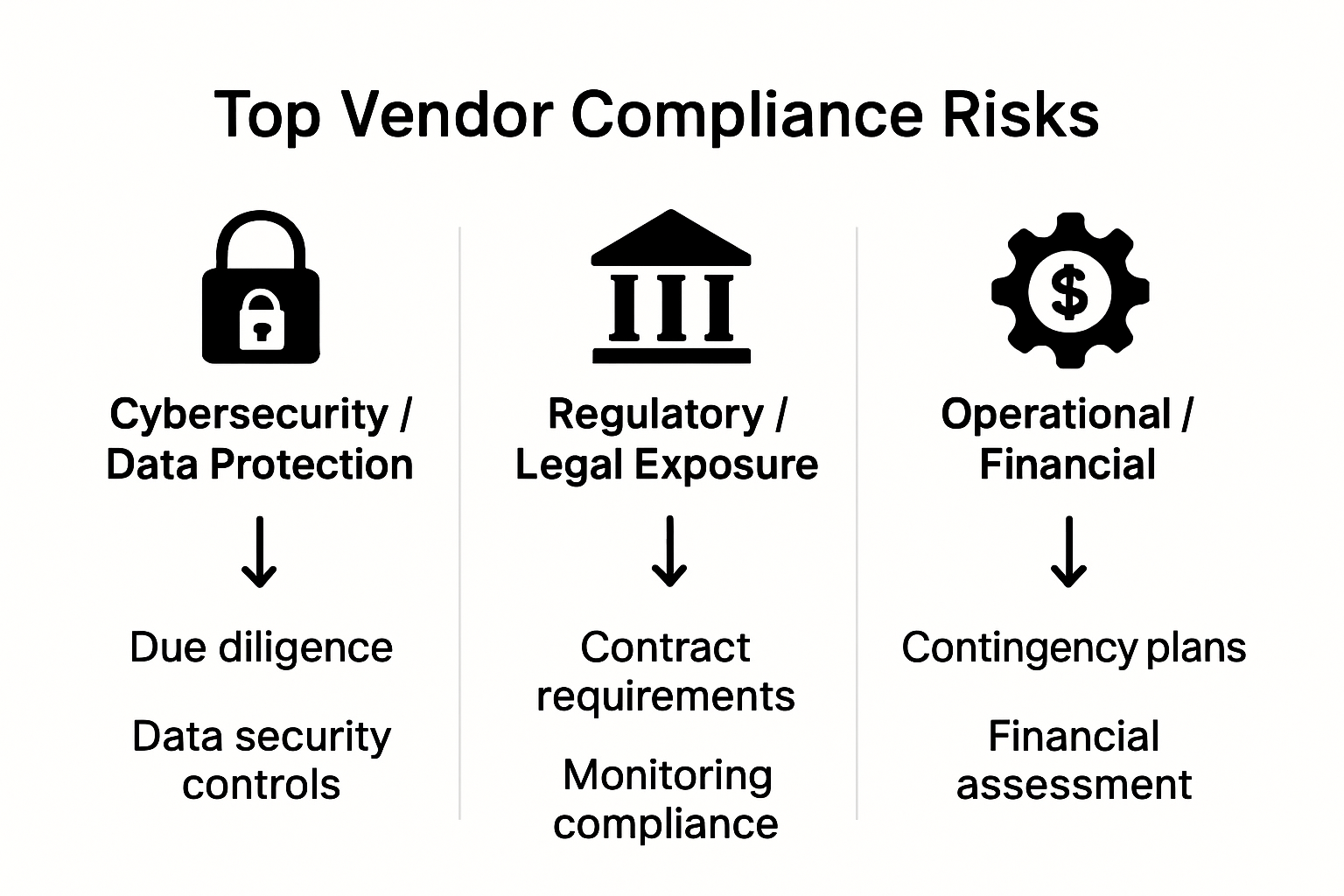
Compliance vendor management introduces complex risks that require strategic and proactive mitigation strategies. Understanding these potential vulnerabilities is crucial for organizations seeking to protect their operational integrity, data security, and regulatory compliance.
Below is a table outlining the most common key risks in compliance vendor management and the main mitigation strategies for each, as discussed in the article:
| Key Risk | Description | Main Mitigation Strategies |
|---|---|---|
| Cybersecurity & Data Protection | Exposure to cyber threats and data breaches via vendors | Security assessments, mandatory standards, monitoring, IRP |
| Regulatory Compliance & Legal Exposure | Legal responsibility for vendor actions, risk of violations | Compliance screening, audit clauses, contractual clarity |
| Operational & Financial Risks | Performance failures or instability impacting operations | Financial checks, contingency planning, vendor diversity |
Cybersecurity and Data Protection Risks
Research from the Federal Reserve Bank of Philadelphia reveals that cybersecurity vulnerabilities represent one of the most significant risks in vendor relationships. Third-party vendors with inadequate security protocols can create potential entry points for cybercriminals, potentially compromising sensitive organizational data.
Key mitigation strategies include:
- Comprehensive Security Assessments: Conducting thorough evaluations of vendor cybersecurity infrastructure
- Mandatory Security Standards: Establishing non-negotiable security requirements for vendor partnerships
- Continuous Monitoring: Implementing real-time security monitoring and threat detection mechanisms
- Incident Response Planning: Developing clear protocols for potential security breaches
Regulatory Compliance and Legal Exposure
Compliance research indicates that organizations remain legally responsible for vendor actions, even when direct operational control is limited. This creates significant potential for regulatory violations and associated financial penalties.
Effective risk mitigation approaches encompass:
- Rigorous vendor compliance screening
- Explicit contractual language defining compliance expectations
- Regular compliance audits and documentation reviews
- Clear accountability mechanisms
- Robust reporting and documentation systems
Operational and Financial Risks
Vendor relationships can introduce substantial operational disruption and financial uncertainty. Organizations must develop comprehensive strategies to manage potential vendor performance failures, financial instability, and strategic misalignment.
Critical risk mitigation techniques include:
- Detailed vendor financial health assessments
- Performance contingency planning
- Diversification of vendor relationships
- Structured exit strategies and contract flexibility
- Regular performance evaluations and benchmarking
Successful risk mitigation in compliance vendor management requires a holistic, proactive approach. Organizations must view vendor relationships as dynamic partnerships requiring constant evaluation, clear communication, and strategic alignment. By implementing comprehensive risk assessment frameworks, maintaining rigorous monitoring processes, and establishing clear expectations, businesses can transform potential vendor risks into opportunities for enhanced operational resilience and strategic growth.
Leveraging Technology for Better Compliance Outcomes
Technology has emerged as a transformative force in compliance vendor management, offering sophisticated tools and platforms that enable organizations to streamline risk assessment, enhance transparency, and create more intelligent, proactive compliance strategies.
Automated Compliance Assessment and Monitoring
Research on IT vendor management best practices demonstrates how automation technologies are revolutionizing vendor compliance processes. Advanced tools now provide real-time monitoring, predictive risk analytics, and comprehensive performance tracking that were previously impossible with manual methods.
Key technological capabilities include:
- Intelligent Risk Scoring: AI-powered algorithms that dynamically assess vendor compliance risks
- Automated Documentation Management: Systems that automatically collect, validate, and archive compliance documentation
- Continuous Compliance Tracking: Real-time monitoring platforms that provide instant alerts on potential compliance deviations
To gain deeper insights into streamlining these processes, learn more about accelerating security questionnaire responses.
Blockchain for Enhanced Transparency and Trust
Innovative research on blockchain technology reveals promising applications in vendor compliance management. Blockchain's inherent characteristics of immutability, decentralization, and transparent record-keeping offer unprecedented capabilities for creating trustworthy, verifiable vendor interaction records.
Blockchain technology provides several compelling advantages:
- Immutable audit trails
- Decentralized verification mechanisms
- Enhanced data integrity and security
- Transparent transaction and compliance tracking
- Reduced potential for fraudulent documentation
Collaborative Technology Platforms
Supply chain research highlights the transformative potential of collaborative technology platforms in vendor management. These integrated systems enable seamless communication, document sharing, and joint compliance management across organizational boundaries.
Advanced collaborative platforms offer:
- Centralized vendor information repositories
- Real-time communication channels
- Integrated performance evaluation tools
- Secure document exchange mechanisms
- Cross-functional compliance workflow management
Effective technological integration in compliance vendor management requires a strategic approach that goes beyond mere tool implementation. Organizations must develop comprehensive digital strategies that align technology capabilities with specific compliance objectives, organizational culture, and risk management frameworks.
By embracing these technological innovations, businesses can transform compliance vendor management from a traditional administrative function into a dynamic, intelligence-driven strategic process. The future of vendor compliance lies in leveraging smart technologies that provide unprecedented visibility, predictive insights, and proactive risk management capabilities.

Frequently Asked Questions
What are the core principles of compliance vendor management?
The core principles of compliance vendor management include a comprehensive risk assessment framework, ongoing monitoring and performance management, and strategic contractual governance. These principles help organizations effectively assess, select, monitor, and manage third-party vendors while minimizing risks.
How can businesses assess vendor cybersecurity risks?
Businesses can assess vendor cybersecurity risks by conducting thorough security assessments, reviewing compliance documentation, and identifying mandatory security standards that vendors must adhere to. This includes evaluating the vendor's technological infrastructure and incident response capabilities.
What strategies can organizations implement for ongoing vendor performance monitoring?
Organizations can implement strategies such as regular performance audits, tracking key performance metrics, maintaining transparent communication channels, and conducting periodic security reassessments to ensure vendor compliance and performance meet established standards.
Why is strategic contractual governance important in vendor management?
Strategic contractual governance is crucial because it establishes clear agreements that define compliance expectations, security protocols, and consequences for breaches. This clarity helps mitigate potential risks and ensures that both parties understand their responsibilities in the vendor relationship.
Ready to Eliminate Compliance Vendor Management Stress?
Keeping up with vendor compliance can be overwhelming as the article highlights the risks of manual monitoring and the consequences of missed details. In a world where data breaches are often traced back to third-party providers, your business cannot afford to rely on outdated processes. Many companies struggle to maintain consistent oversight, wasting valuable time and exposing themselves to regulatory and security risks. If you want to strengthen your compliance framework and transform risk management from a burden into a business advantage, there is a smarter way.

Skypher's AI Questionnaire Automation Tool streamlines your security questionnaire process, automates compliance assessment, and enhances team collaboration. Uncover real-time insights, speed up audits, and gain peace of mind by integrating your workflows with over 40 risk management platforms. Do not wait for a vendor oversight gap to become a costly emergency. Visit Skypher today to automate, protect, and win with confidence.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- The Case for Security Questionnaire Automation
- The ever growing number of security questionnaires and what you and your company can do to face it
- Increasing company efficiency: boosting collaboration with widespread adoption
- Steps to comply CCPA compliance by Bista Solutions
