Cyberattacks are growing bolder every year and companies know the risks run deep. Yet here is the twist. Organizations that implement ISO cybersecurity standards can cut their security vulnerabilities by up to 60 percent compared to those without structured frameworks. Think the main benefit is just ticking off compliance checklists? Actually, these standards give businesses a real shot at operational efficiency and stronger market credibility all at once.
Table of Contents
- Understanding Cybersecurity Standards ISO
- Key Benefits Of Adopting ISO Standards
- How ISO 27001 Protects Your Organization
- Steps To Achieve ISO Cybersecurity Compliance
Quick Summary
| Takeaway | Explanation |
|---|---|
| ISO cybersecurity standards provide a comprehensive framework | These standards offer structured methodologies for identifying and mitigating digital threats, making them adaptable for various organizational sizes and industries. |
| Strategic risk management enhances operational efficiency | Implementing ISO standards shifts organizations from reactive to proactive security management, improving their ability to identify and mitigate risks. |
| ISO 27001 serves as a robust information security management system | It enables organizations to systematically address security vulnerabilities through risk assessments and holistic protection strategies. |
| Achieving ISO compliance involves a systematic approach | Organizations must perform thorough assessments, develop tailored security policies, and establish continuous improvement processes to succeed. |
| ISO certification enhances credibility and market access | Certification signals commitment to security practices, improving stakeholder confidence and facilitating entry into stringent market sectors. |
Understanding Cybersecurity Standards ISO

Cybersecurity standards ISO represent critical frameworks that help organizations protect their digital infrastructure and manage information security risks effectively. These internationally recognized guidelines provide comprehensive blueprints for establishing robust security practices across diverse technological environments.
The Core Purpose of ISO Cybersecurity Standards
ISO cybersecurity standards serve as strategic roadmaps for organizations seeking to develop comprehensive security management systems. International Organization for Standardization defines these standards as systematic approaches to identifying, assessing, and mitigating potential digital threats. The primary objectives include creating structured methodologies for risk management, establishing consistent security protocols, and enabling organizations to proactively defend against evolving cyber risks.
Key characteristics of these standards include their adaptability across different industries and organizational sizes. Whether a small startup or a multinational corporation, these frameworks offer scalable strategies for information security. According to Cybersecurity Ventures, organizations implementing ISO standards can reduce their potential security vulnerabilities by up to 60% compared to those without structured security frameworks.
ISO Cybersecurity Standard Families
The ISO family of cybersecurity standards encompasses multiple interconnected specifications designed to address various aspects of digital security. The most prominent standards include:
- ISO/IEC 27001: Focuses on information security management systems (ISMS), providing requirements for establishing comprehensive security controls
- ISO/IEC 27005: Offers guidelines for information security risk management processes
- ISO/IEC 27032: Provides specific guidance for cybersecurity implementation and digital threat mitigation
National Institute of Standards and Technology emphasizes that these standards are not static documents but evolving frameworks that adapt to emerging technological challenges. They represent dynamic blueprints for organizations navigating complex digital ecosystems.
Implementing these standards requires a strategic approach. Organizations must conduct thorough risk assessments, develop customized security policies, and continuously monitor and update their security infrastructure. The goal is not just compliance but creating a proactive security culture that anticipates and neutralizes potential threats before they can cause significant damage.
Beyond technical specifications, ISO cybersecurity standards also address human factors. They recognize that effective security is not just about technology but also about training personnel, creating awareness, and developing organizational resilience against potential cyber incidents. This holistic approach distinguishes these standards from more narrow technical guidelines.
For businesses and institutions, adopting ISO cybersecurity standards is no longer optional but a strategic imperative. As digital transformation accelerates and cyber threats become increasingly sophisticated, these frameworks provide a structured, internationally recognized approach to managing information security risks.
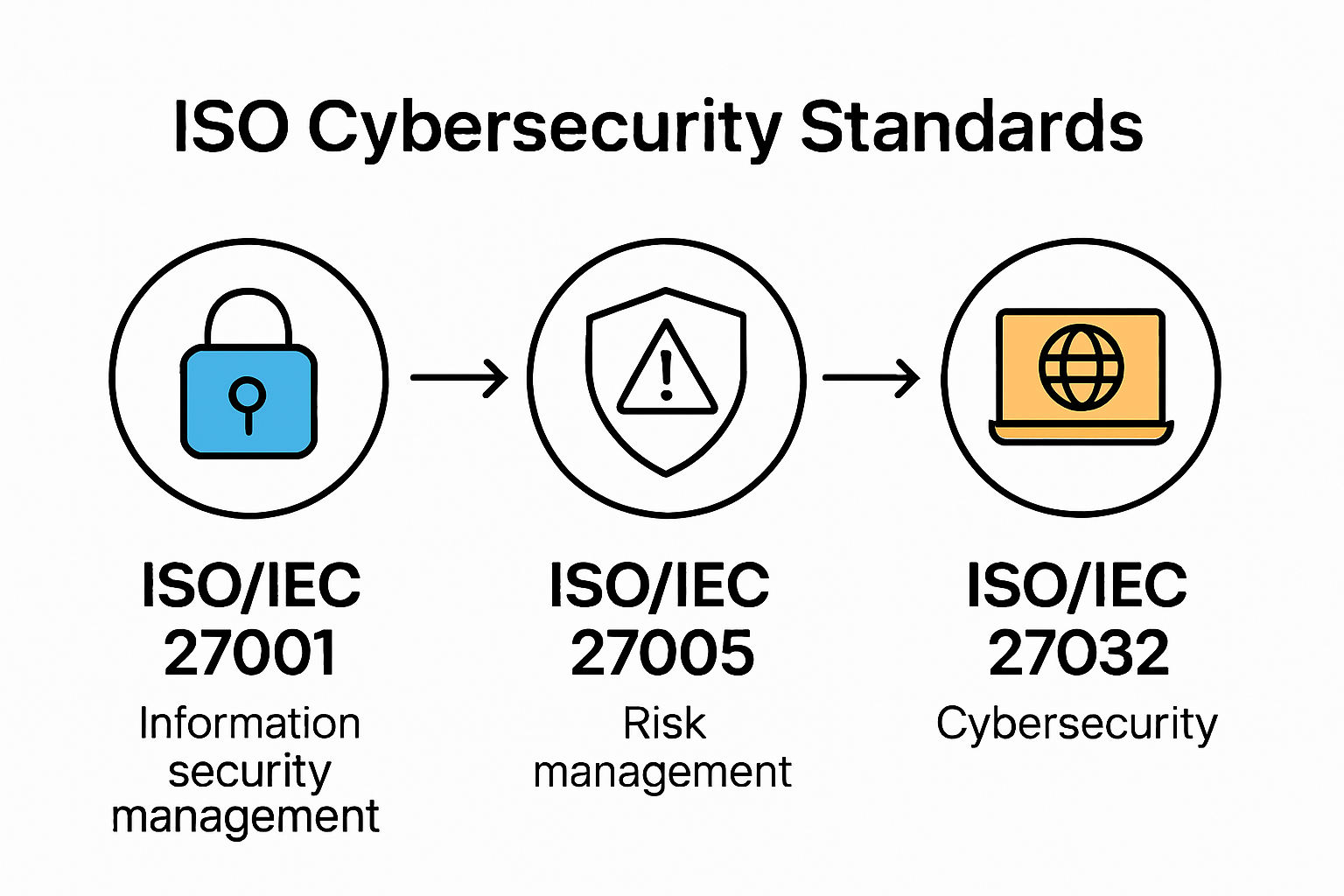
To help you quickly compare the key ISO cybersecurity standards referenced in this section, the following table summarizes their primary focus and organizational benefits:
| Standard | Focus Area | Organizational Benefit |
|---|---|---|
| ISO/IEC 27001 | Information Security Management System (ISMS) | Establishes comprehensive security controls |
| ISO/IEC 27005 | Security Risk Management | Guides information security risk management processes |
| ISO/IEC 27032 | Cybersecurity Implementation & Threat Mitigation | Provides actionable guidance for combating cyber threats |
Key Benefits of Adopting ISO Standards
Adopting ISO cybersecurity standards offers organizations strategic advantages that extend far beyond simple compliance. These internationally recognized frameworks provide comprehensive approaches to managing digital risks and enhancing overall organizational resilience.
Strategic Risk Management and Operational Efficiency
ISO standards transform cybersecurity from a reactive defensive strategy to a proactive risk management approach. Gartner Research indicates that organizations implementing ISO standards experience up to 45% improvement in their ability to identify and mitigate potential security vulnerabilities. By establishing systematic processes for risk assessment and management, businesses can anticipate threats before they materialize.
The structured methodology embedded in ISO standards enables organizations to develop comprehensive security frameworks that are both flexible and robust. Companies gain a clear roadmap for identifying potential risks, evaluating their potential impact, and implementing targeted mitigation strategies. This approach allows for continuous improvement and adaptation in an ever-changing technological landscape.
Enhanced Organizational Credibility and Trust
Certification to ISO cybersecurity standards serves as a powerful signal of an organization's commitment to robust security practices. Security Boulevard reports that organizations with ISO certification experience significant improvements in stakeholder confidence. Key benefits include:
- Competitive Differentiation: Demonstrates superior security practices to clients and partners
- Regulatory Alignment: Helps meet complex legal and compliance requirements
- Customer Trust: Provides tangible evidence of commitment to data protection
Moreover, these standards facilitate easier market access, particularly in industries with stringent security requirements. International clients and partners often view ISO certification as a prerequisite for establishing business relationships, effectively opening doors to new market opportunities.
Financial and Operational Advantages
Beyond security improvements, ISO standards deliver measurable financial benefits. Cybersecurity Ventures suggests that organizations implementing comprehensive ISO frameworks can reduce potential security-related financial losses by up to 60%. This reduction stems from decreased incident frequencies, faster response times, and more efficient resource allocation.
The standardized approach also streamlines internal processes, reducing redundancies and creating more efficient security management protocols. Organizations benefit from clearer communication channels, more predictable security workflows, and a unified approach to managing digital risks across different departments and technological platforms.
Implementing ISO cybersecurity standards is not merely a technical exercise but a strategic business decision. These frameworks provide a holistic approach to security that addresses technological, human, and organizational dimensions. By embracing these standards, businesses can transform their cybersecurity from a cost center to a strategic asset that drives innovation, builds trust, and creates competitive advantages in an increasingly complex digital ecosystem.
How ISO 27001 Protects Your Organization
ISO 27001 represents a comprehensive framework for protecting organizations against increasingly sophisticated digital threats, offering a systematic approach to information security management that goes beyond traditional defensive strategies. This international standard provides a robust blueprint for identifying, managing, and mitigating information security risks across an organization's entire technological ecosystem.
Comprehensive Risk Management Framework
Oxford University's Information Security Research Center highlights that ISO 27001 enables organizations to develop a structured methodology for identifying and addressing potential security vulnerabilities. The standard requires organizations to conduct thorough risk assessments that examine every aspect of information handling, from digital systems to human interactions.
The risk management process involves several critical steps:
- Systematic Identification: Comprehensively mapping potential security threats
- Detailed Assessment: Evaluating the potential impact and likelihood of each identified risk
- Strategic Mitigation: Developing targeted strategies to address and minimize potential security breaches
By implementing this systematic approach, organizations can create a proactive security environment that anticipates and neutralizes potential threats before they can cause significant damage. Gartner Research indicates that organizations using such comprehensive frameworks can reduce their potential security vulnerabilities by up to 55%.
Holistic Information Protection Strategy
ISO 27001 goes beyond technical controls, addressing the human and organizational aspects of information security. The standard recognizes that effective protection requires a comprehensive approach that includes technological solutions, employee training, and organizational policies. According to NSF International, this holistic approach ensures that security is not just a technical challenge but an integrated organizational strategy.
Key protection mechanisms include:
- Establishing clear information security policies
- Implementing robust access control measures
- Creating comprehensive incident response protocols
- Developing continuous monitoring and improvement processes
Regulatory Compliance and Organizational Resilience
Cambridge Cybersecurity Institute emphasizes that ISO 27001 provides a framework for meeting complex regulatory requirements across multiple industries. Organizations can demonstrate their commitment to information security, potentially reducing legal and financial risks associated with data breaches.
The standard's rigorous certification process offers multiple benefits:
- Validates an organization's information security practices
- Provides a competitive advantage in security-conscious markets
- Reduces potential financial losses from security incidents
Moreover, ISO 27001 certification signals to clients, partners, and stakeholders that an organization takes information security seriously. This can enhance trust, improve business relationships, and potentially open doors to new market opportunities.
Implementing ISO 27001 is not a one-time effort but a continuous journey of improvement. Organizations must regularly review and update their information security management systems, ensuring they remain effective against evolving technological threats. By embracing this standard, businesses can transform information security from a potential vulnerability into a strategic organizational strength.
The following table outlines the main benefits organizations receive by implementing ISO 27001, as discussed throughout this section:
| Benefit | Description |
|---|---|
| Comprehensive Risk Management | Identifies, assesses, and mitigates security threats |
| Holistic Protection Strategy | Integrates technical, human, and policy-driven controls |
| Regulatory Compliance | Facilitates meeting legal/regulatory requirements |
| Competitive Advantage | Enhances credibility and market opportunities |
| Reduced Financial Losses | Lowers risk and cost of security incidents |
| Organizational Resilience | Increases ability to adapt to evolving threats |
Steps to Achieve ISO Cybersecurity Compliance
Achieving ISO cybersecurity compliance requires a strategic, systematic approach that transforms organizational security practices from reactive measures to proactive, comprehensive frameworks. Successful implementation demands careful planning, dedicated resources, and a commitment to continuous improvement.
Initial Assessment and Scoping
Neumetric Consulting emphasizes that the first critical step involves conducting a comprehensive organizational assessment. This initial phase requires leadership to define the precise scope of the Information Security Management System (ISMS), identifying all technological assets, business processes, and potential security touchpoints.
Key considerations during this phase include:
- Asset Inventory: Documenting all information systems, networks, and data repositories
- Current Security Landscape: Evaluating existing security controls and potential vulnerabilities
- Organizational Boundaries: Determining the exact boundaries of the ISMS implementation
Security Boulevard reports that organizations that invest significant time in thorough initial assessments are 40% more likely to achieve successful ISO certification on their first attempt.
Risk Assessment and Management Strategy
Risk assessment represents the cornerstone of ISO cybersecurity compliance. Organizations must develop a systematic approach to identifying, analyzing, and mitigating potential security threats. Cambridge Cybersecurity Institute recommends a multi-dimensional risk assessment approach that considers technological, human, and procedural risk factors.
Effective risk management involves:
- Comprehensive threat identification
- Detailed vulnerability analysis
- Prioritization of potential security risks
- Development of targeted mitigation strategies
The goal is not just to identify risks but to create a dynamic framework that can adapt to evolving technological landscapes and emerging threat vectors.
Implementation and Continuous Improvement
Implementing ISO cybersecurity standards requires more than technical controls. National Institute of Standards and Technology highlights the importance of creating a holistic security culture that integrates technological solutions with organizational policies and human behaviors.
Critical implementation steps include:
- Developing comprehensive security policies
- Creating employee training programs
- Implementing technical security controls
- Establishing incident response mechanisms
- Setting up continuous monitoring systems
Successful implementation requires ongoing commitment. Organizations must view ISO compliance as a continuous journey rather than a one-time achievement. Regular internal audits, periodic risk reassessments, and adaptive strategy modifications ensure that the cybersecurity framework remains robust and relevant.
The certification process itself involves rigorous external audits where independent assessors evaluate the organization's ISMS against strict ISO standards. Preparation is key. Organizations must maintain meticulous documentation, demonstrate consistent implementation of security practices, and show a clear commitment to continuous improvement.
Ultimately, achieving ISO cybersecurity compliance is about creating a resilient, adaptive security ecosystem that protects organizational assets while enabling innovation and growth. By following a structured approach and maintaining a commitment to excellence, organizations can transform cybersecurity from a potential vulnerability into a strategic organizational strength.
Frequently Asked Questions
What are ISO cybersecurity standards?
ISO cybersecurity standards are systematic frameworks designed to help organizations identify, assess, and mitigate information security risks. These internationally recognized guidelines provide a structured approach to establishing robust security practices across various industries.
How can implementing ISO standards reduce security vulnerabilities?
Organizations that implement ISO standards can reduce their security vulnerabilities by up to 60% compared to those without structured frameworks. These standards help organizations proactively manage risks, enhancing their overall security posture.
What is the significance of ISO 27001 in cybersecurity?
ISO 27001 is a key standard focusing on information security management systems (ISMS). It provides comprehensive requirements for establishing security controls and enables organizations to systematically address security vulnerabilities through risk assessments and mitigation strategies.
What steps are involved in achieving ISO cybersecurity compliance?
Achieving ISO cybersecurity compliance involves several steps: conducting an initial assessment and scoping, performing a comprehensive risk assessment, implementing necessary security measures, and committing to continuous improvement to maintain and enhance security practices.
Ready to Simplify ISO Cybersecurity Compliance for 2025?
Struggling with time-consuming security questionnaires while striving for ISO-standard risk management and operational efficiency? Most organizations know the stress of managing compliance, documentation, and stakeholder trust under tight deadlines. As discussed in our article, the right ISO frameworks reduce vulnerabilities and can set your company apart. Now imagine achieving all of that without the manual workload or risk of errors.

Automate your entire security questionnaire process with Skypher. Our AI-driven platform streamlines every step, letting your team complete reviews faster and with total accuracy. Experience advanced features like real-time collaboration and an integrated Trust Center. Stand out in tech and finance by proving your ISO security readiness with speed and confidence. See how easy ISO compliance can be—book a demo or get started today before your next audit cycle begins.
