Cybersecurity is an urgent conversation in today's digital world. In the next few years, global cybersecurity spending is projected to exceed USD 1.75 trillion, illustrating just how serious organizations are about protecting their assets. But here’s the kicker: many people think cybersecurity is all about firewalls and antivirus software. The truth is far more complex. It•s not just about defense; it•s a constantly evolving battleground where proactive strategies and understanding human behavior are just as crucial as technical solutions.
Table of Contents
- What Is Cyber Security
- Types Of Cyber Threats Explained
- Key Principles Of Cyber Protection
- Branches Of Information Security
- Future Of Cybersecurity And Trends
Quick Summary
| Takeaway | Explanation |
|---|---|
| Cybersecurity is crucial for digital defense | Maintaining the integrity, confidentiality, and accessibility of digital information is essential as cyber threats become more sophisticated and prevalent. |
| Understanding diverse cyber threats is key | Knowledge of various threat types, including malware, social engineering, and advanced persistent threats, is critical for developing effective cybersecurity strategies. |
| Risk management is a foundational principle | Continuous identification and mitigation of vulnerabilities through risk assessment are essential for maintaining a robust cybersecurity posture. |
| Emerging technologies drive cybersecurity evolution | The integration of AI and the adaptation to quantum computing will shape future cybersecurity strategies, requiring organizations to innovate and adapt continuously. |
| Global cooperation is necessary for effective defense | As cyber risks transcend geographical boundaries, prioritizing international collaboration and intelligence sharing will enhance overall cybersecurity efficacy. |
What is Cyber Security?
Cybersecurity is a critical digital defense strategy designed to protect computer systems, networks, applications, and data from malicious attacks, unauthorized access, and potential breaches. In an increasingly interconnected world, cybersecurity serves as the digital shield that guards organizations, governments, and individuals against evolving technological threats.
The Core Purpose of Cybersecurity
At its fundamental level, cybersecurity aims to maintain the integrity, confidentiality, and accessibility of digital information. Unlike traditional security measures, cyber security operates in an invisible yet complex digital landscape where threats can emerge instantly and spread globally within seconds. IBM research projects that global cybersecurity spending will exceed USD 1.75 trillion between 2021-2025, underscoring the critical importance of robust digital protection strategies.
The discipline encompasses multiple layers of protection, including technological solutions, strategic policies, and human awareness. These layers work together to create a comprehensive defense mechanism against potential cyber threats such as malware, ransomware, phishing attacks, and sophisticated network intrusions.
Types of Cybersecurity Domains
Cybersecurity is not a monolithic concept but a multifaceted approach with specialized domains addressing different aspects of digital security:
- Network Security: Protects the internal network infrastructure from unauthorized access and potential vulnerabilities
- Application Security: Focuses on securing software and applications against potential exploitation
- Information Security: Ensures the protection of sensitive data from unauthorized disclosure or manipulation
- Operational Security: Manages processes and decisions for handling and protecting digital assets
The Growing Importance of Cybersecurity
The digital transformation of businesses and societies has dramatically increased cybersecurity's significance. Employment projections indicate that information security analyst roles are expected to grow 32% from 2022 to 2032, significantly outpacing average job market growth. This surge reflects the escalating complexity and frequency of cyber threats. Moreover, the economic impact of cybercrime is staggering. Global estimates suggest that cybercrime could cost the world economy approximately USD 10.5 trillion annually by 2025. These figures highlight why cybersecurity is no longer optional but a fundamental requirement for sustainable digital operations.
Moreover, the economic impact of cybercrime is staggering. Global estimates suggest that cybercrime could cost the world economy approximately USD 10.5 trillion annually by 2025. These figures highlight why cybersecurity is no longer optional but a fundamental requirement for sustainable digital operations.
Ultimately, cybersecurity represents a dynamic, continuously evolving field that demands constant vigilance, adaptive strategies, and a proactive approach to identifying and mitigating potential digital risks. As technology advances, so too must our methods of protecting the digital ecosystems we increasingly depend upon.
Types of Cyber Threats Explained
The digital landscape is riddled with increasingly sophisticated cyber threats that continuously evolve, challenging organizations and individuals to stay ahead of potential security breaches. Understanding these diverse threat types is crucial for developing effective cybersecurity strategies and protecting digital assets.
Malicious Software (Malware) Threats
Malware represents a broad category of harmful software designed to infiltrate, damage, or disrupt computer systems. Statista research indicates that malware remains one of the most prevalent cyber threats, encompassing multiple dangerous variants:
- Viruses: Self-replicating programs that spread by attaching themselves to clean files
- Ransomware: Malicious software that encrypts system data and demands payment for restoration
- Spyware: Covert programs that secretly collect user information without consent
- Trojans: Deceptive programs disguised as legitimate software to gain system access
Modern malware has become increasingly complex, with global cybercrime projections suggesting potential economic damages reaching $13.82 trillion by 2028, highlighting the enormous financial impact of these digital threats.
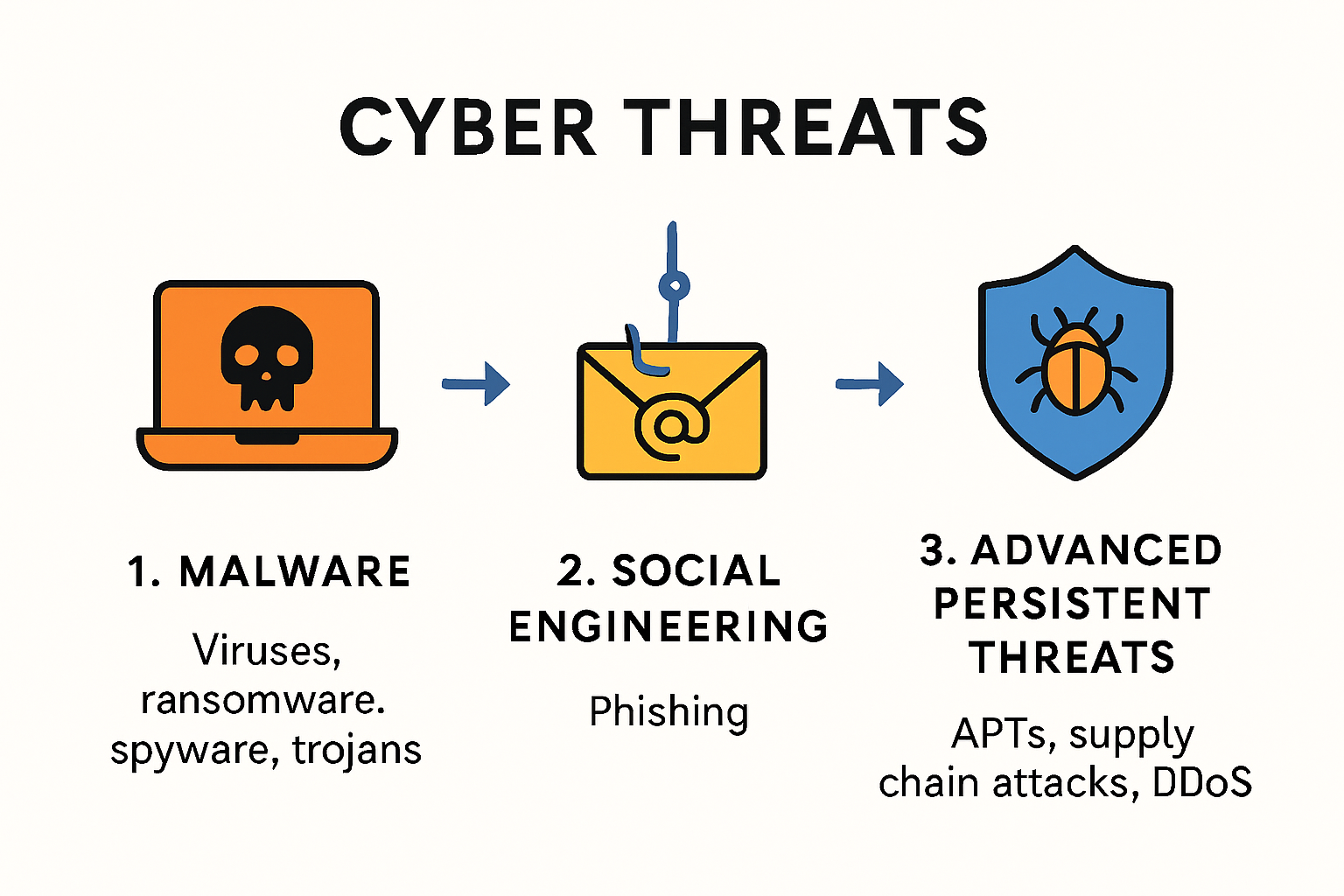
Social Engineering and Psychological Manipulation
Social engineering attacks exploit human psychology rather than technical vulnerabilities, making them particularly insidious. These attacks manipulate individuals into revealing sensitive information or performing actions that compromise security. Phishing remains the most common social engineering technique, where attackers impersonate trusted entities to trick users into sharing credentials or downloading malicious content.
Advanced social engineering strategies now include:
- Sophisticated email spoofing
- Carefully crafted impersonation attempts
- Targeted psychological manipulation
- Deep fake technologies
Advanced Persistent Threats and Complex Attack Vectors
More sophisticated cyber threats involve complex, multi-stage attacks designed to penetrate robust security systems. Cybersecurity experts categorize these advanced persistent threats (APTs) as highly strategic intrusions that often target specific organizations or industries.
These complex threats include:
- Supply chain attacks targeting interconnected technological ecosystems
- Distributed denial of service (DDoS) attacks overwhelming system resources
- Man-in-the-middle attacks intercepting communication channels
- Insider threats originating from compromised internal personnel
The escalating complexity of cyber threats demands continuous adaptation. With projected global cybercrime costs potentially exceeding $24 trillion by 2027, organizations must invest in sophisticated, multi-layered defense mechanisms that anticipate and mitigate emerging digital risks.
Understanding these threat types is not just about technical knowledge—it's about developing a proactive, comprehensive approach to digital security that recognizes the human and technological dimensions of potential cyber risks.
Key Principles of Cyber Protection
Cyber protection is a strategic discipline that goes beyond mere technological implementation, representing a holistic approach to safeguarding digital assets, infrastructure, and organizational integrity. As cyber threats continue to evolve, understanding and implementing core protection principles becomes paramount for effective digital defense.
Risk Management and Strategic Assessment
Cybersecurity experts emphasize that comprehensive risk management forms the foundational principle of cyber protection. This involves systematically identifying, evaluating, and mitigating potential vulnerabilities within an organization's digital ecosystem. Risk assessment is not a one-time event but a continuous process that requires ongoing monitoring and adaptation.
Effective risk management includes:
- Comprehensive vulnerability scanning
- Regular security audits
- Threat landscape analysis
- Predictive threat modeling
- Prioritizing potential risks based on potential impact
The Global Cybersecurity Outlook highlights that by 2025, nearly half of cyber leaders will transition to new roles, indicating the dynamic nature of risk management and the need for continuous learning and strategic flexibility.
Network Security and Access Control
Network security represents a critical principle of cyber protection, focusing on creating robust barriers against unauthorized access and potential intrusions. This principle involves implementing multi-layered defense mechanisms that protect the organization's digital infrastructure from various attack vectors.
Key network security strategies include:
- Implementing strong firewall configurations
- Utilizing advanced encryption protocols
- Developing segmented network architectures
- Establishing strict authentication mechanisms
- Creating comprehensive access control policies
Access control goes beyond simple password protection, encompassing sophisticated identity verification methods such as multi-factor authentication, biometric verification, and role-based access restrictions. By limiting system access to authorized personnel, organizations can significantly reduce potential breach points.
Continuous Monitoring and Incident Response
Cybersecurity research suggests that future cyber defense strategies must balance technological capabilities with adaptive human expertise. Continuous monitoring and rapid incident response represent crucial principles in maintaining digital resilience.
Effective monitoring and response frameworks require:
- Real-time threat detection systems
- Automated alert mechanisms
- Comprehensive logging and forensic capabilities
- Pre-defined incident response protocols
- Regular simulation and training exercises
The goal is not just detecting threats but developing a proactive approach that anticipates potential security incidents and minimizes their potential impact. This requires a combination of advanced technological tools and well-trained human expertise.
Ultimately, cyber protection principles are interconnected strategies that demand a holistic, adaptive approach. Organizations must view cybersecurity not as a static defense mechanism but as a dynamic, evolving discipline that requires continuous learning, technological innovation, and strategic thinking.
Branches of Information Security
Information security encompasses a complex and multifaceted landscape of specialized disciplines designed to protect digital assets, data integrity, and organizational infrastructure. As technological ecosystems become increasingly sophisticated, understanding the diverse branches of information security becomes crucial for comprehensive digital defense strategies.
Network and Infrastructure Security
Network security represents a foundational branch focusing on protecting the communication channels and computational infrastructure that enable digital interactions. World Economic Forum research highlights the critical nature of this branch, with ransomware remaining the top organizational cybersecurity concern for 45% of surveyed entities.
Key components of network and infrastructure security include:
- Firewall management
- Intrusion detection systems
- Virtual private network (VPN) implementations
- Network segmentation strategies
- Protocol security configurations
This branch requires continuous monitoring and adaptive strategies to counter evolving digital threat landscapes, ensuring robust protection against unauthorized access and potential system vulnerabilities.
Application and Data Security
Gartner research underscores the emerging challenges in application security, particularly with the rise of generative AI technologies that are transforming data protection paradigms. Modern application security goes beyond traditional structured data protection, now encompassing complex unstructured data environments like text, images, and dynamic digital content.
Critical aspects of application and data security include:
- Secure software development practices
- Data encryption methodologies
- Access control mechanisms
- Vulnerability assessment
- Continuous security testing
With the proliferation of cloud computing and distributed systems, application security has become increasingly complex, requiring multi-layered defensive strategies that anticipate potential exploitation vectors.
Emerging Cybersecurity Domains
MIT research highlights the transformative impact of artificial intelligence on information security, revealing how technological advancements are simultaneously creating new protective capabilities and introducing unprecedented challenge landscapes.
Emerging cybersecurity domains now include:
- Artificial intelligence security
- Cloud security architecture
- Internet of Things (IoT) protection
- Blockchain security
- Quantum computing defense strategies
These emerging domains represent the frontier of information security, where traditional defensive models are being reimagined through advanced technological lenses. Professionals in these fields must continuously adapt, learning to leverage cutting-edge technologies while anticipating potential security implications.
Information security is not a static discipline but a dynamic, evolving ecosystem that requires constant vigilance, innovative thinking, and a holistic understanding of technological interdependencies. As digital landscapes become more complex, the branches of information security will continue to grow, intersect, and redefine themselves to meet emerging challenges.
Future of Cybersecurity and Trends
The landscape of cybersecurity is rapidly transforming, driven by technological innovation, evolving threat landscapes, and the increasing complexity of digital ecosystems. As organizations navigate an increasingly interconnected world, understanding emerging trends becomes crucial for developing robust, adaptive security strategies.
Artificial Intelligence and Machine Learning Integration
Gartner research highlights a significant shift in cybersecurity paradigms, with generative AI redefining data protection approaches. The focus is expanding from traditional structured data protection to comprehensive security strategies covering unstructured data like text, images, and complex digital content.
Key AI-driven cybersecurity developments include:
- Predictive threat detection
- Automated vulnerability assessment
- Real-time anomaly identification
- Enhanced incident response mechanisms
- Advanced behavioral analytics
Artificial intelligence is not just a defensive tool but a transformative technology that enables more proactive, intelligent security frameworks. By leveraging machine learning algorithms, organizations can anticipate and mitigate potential threats before they materialize.
Quantum Computing and Cryptographic Evolution
Google's cybersecurity forecast emphasizes the critical importance of preparing for post-quantum cryptography. As quantum technologies advance, traditional encryption methods become increasingly vulnerable, necessitating a fundamental reimagining of cryptographic strategies.
Emerging cryptographic trends include:
- Quantum-resistant encryption protocols
- Cryptographic agility frameworks
- Advanced key management systems
- Distributed trust mechanisms
- Blockchain-based security architectures
Organizations must proactively develop flexible cryptographic infrastructures capable of adapting to rapidly evolving technological landscapes. This requires interdisciplinary collaboration between cybersecurity experts, cryptographers, and quantum computing specialists.
Global Interconnectedness and Geopolitical Dynamics
The World Economic Forum's Global Cybersecurity Outlook underscores the increasing significance of geopolitical tensions in shaping cybersecurity strategies. As digital ecosystems become more interconnected, cyber risks transcend traditional geographical boundaries, demanding sophisticated, collaborative approaches to global digital defense.
Key considerations in this evolving landscape include:
- International cybersecurity cooperation
- Cross-border threat intelligence sharing
- Harmonized regulatory frameworks
- Diplomatic conflict resolution mechanisms
- Resilience-focused security strategies
The future of cybersecurity is not about building impenetrable walls but creating adaptive, responsive systems that can quickly detect, understand, and neutralize emerging threats. This requires a holistic approach that balances technological innovation, human expertise, and strategic foresight.
As we move forward, cybersecurity will increasingly become a critical component of organizational strategy, national security, and global digital governance. The ability to anticipate, adapt, and innovate will distinguish successful digital defense frameworks from vulnerable ones.
Frequently Asked Questions
What is cybersecurity?
Cybersecurity is a set of strategies and practices aimed at protecting computer systems, networks, applications, and data from malicious attacks and unauthorized access. It encompasses technological solutions and strategic policies designed to safeguard digital information in an increasingly interconnected world.
Why is cybersecurity important in 2025?
As cyber threats become more sophisticated and prevalent, maintaining the integrity, confidentiality, and accessibility of digital information is crucial. The projected economic impact of cybercrime could reach approximately USD 10.5 trillion annually by 2025, making robust cybersecurity not just optional but essential for sustainable operations.
What are the main types of cyber threats?
Key types of cyber threats include malware (like viruses and ransomware), social engineering (such as phishing), and advanced persistent threats (APTs), which involve complex, strategic multi-stage attacks targeting specific organizations or industries.
How can organizations improve their cybersecurity posture?
Organizations can enhance their cybersecurity by implementing effective risk management strategies, robust network security measures, continuous monitoring, and comprehensive incident response protocols. Emphasizing employee training and awareness also plays a crucial role in fortifying cybersecurity defenses.
Enhance Your Cyber Defense with Skypher
In the ever-evolving landscape of cyber threats, understanding and addressing vulnerabilities is paramount. As highlighted in our Cybersecurity Wiki, the significance of proactive strategies and continuous monitoring cannot be overstated. Every organization, especially in tech and finance, faces the challenge of efficiently managing security questionnaires, an essential yet often cumbersome task that can compromise your cybersecurity posture.
Don't let the complexity of cybersecurity slow you down. With Skypher's AI-driven Questionnaire Automation Tool, you can complete security reviews faster and with greater accuracy, seamlessly integrating with over 40 third-party risk management platforms. Imagine reducing the time spent on proof of concepts and contracts, allowing your team to focus on what truly matters: securing your digital assets and maintaining client trust.
!
Ready to elevate your cybersecurity approach? Experience the efficiency and effectiveness of Skypher today! Visit https://skypher.co and unlock your potential to respond to security questionnaires with confidence and speed. Don't wait—empower your organization against the growing tide of cyber threats now!
