Over 80 countries now have dedicated data privacy laws, signaling a dramatic shift in how organizations handle personal information. Protecting sensitive data is no longer simply an IT task—it is a legal and ethical necessity with direct reputational impact. Understanding the true scope of data privacy compliance helps companies avoid steep penalties, build trust with customers, and confidently manage complex regulatory requirements in an increasingly data-driven world.
Table of Contents
- Defining Data Privacy Compliance and Its Scope
- Major Data Privacy Laws and Global Frameworks
- Types of Data Under Compliance Requirements
- Enterprise Responsibilities and Documentation Practices
- Risks, Penalties, and Common Compliance Pitfalls
Key Takeaways
| Point | Details |
|---|---|
| Data Privacy Compliance | Organizations must develop comprehensive policies to ensure responsible handling of personal data and adhere to legal and ethical standards. |
| Global Legislative Landscape | Familiarity with regulatory frameworks like GDPR is essential as they influence global data usage and compliance practices. |
| Types of Sensitive Data | Entities must recognize various data types that require stringent protections, including PII, financial, health, and biometric data. |
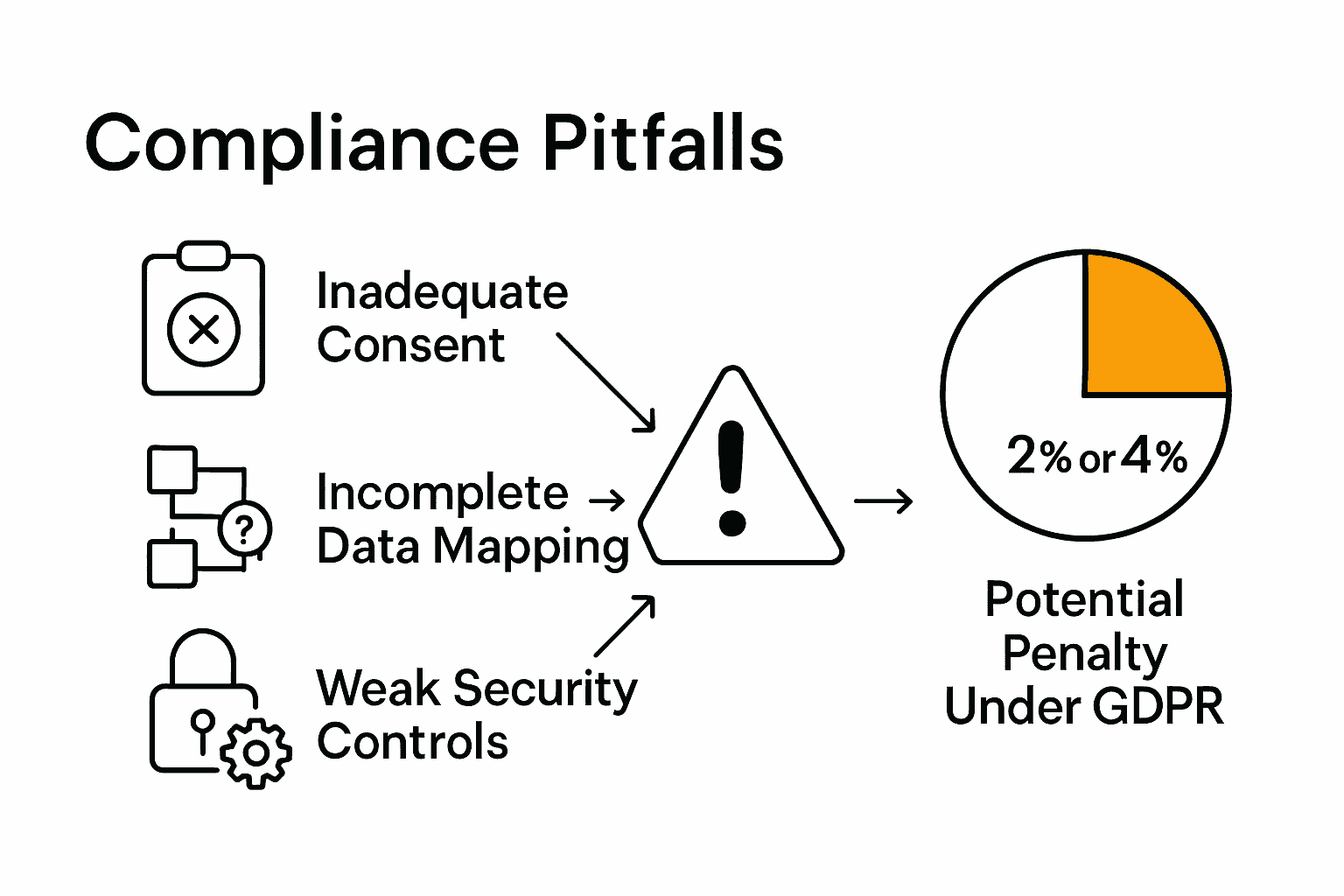
| Risks and Common Pitfalls | Organizations should address common compliance pitfalls, such as inadequate consent mechanisms and insufficient security controls, to mitigate risks associated with data breaches. |
Defining Data Privacy Compliance and Its Scope
Data privacy compliance represents a strategic framework designed to protect sensitive information and ensure organizations handle personal data responsibly and legally. As research from arxiv.org suggests, this approach goes beyond simply managing data tools, focusing instead on the outcomes and rights associated with data usage across different sectors.
Data privacy compliance fundamentally involves establishing and maintaining comprehensive policies that govern how personal information is collected, processed, stored, and shared. According to the Data Capsule paradigm, an innovative approach pairs personal data directly with specific processing policies, ensuring automatic adherence to privacy regulations throughout the entire data lifecycle.
The scope of data privacy compliance is multifaceted, encompassing several critical dimensions:
- Legal Protection: Adhering to regional and international data protection regulations
- Ethical Handling: Ensuring transparent and fair data management practices
- Risk Mitigation: Preventing unauthorized data access and potential breaches
- Individual Rights: Protecting personal information and supporting user consent mechanisms
For organizations navigating this complex landscape, understanding these nuanced requirements is crucial. Cybersecurity GRC: Essential Strategies for 2025 Success provides deeper insights into developing robust governance frameworks that integrate privacy compliance seamlessly into broader organizational strategies.
Ultimately, effective data privacy compliance is not just a regulatory checkbox but a fundamental commitment to respecting individual rights and maintaining trust in an increasingly data-driven world.
Major Data Privacy Laws and Global Frameworks
The landscape of data privacy laws is complex and continually evolving, with several key frameworks shaping global data protection standards. According to research from arxiv.org, the European Union's General Data Protection Regulation (GDPR) stands as a pivotal development, serving as a comprehensive model that has significantly influenced personal data usage regulations worldwide.
Global data privacy frameworks can be categorized into several critical dimensions:
- Regional Regulations: Laws specific to particular geographic areas
- Sector-Specific Standards: Industry-focused privacy requirements
- Cross-Border Guidelines: Frameworks governing international data transfers
- Comprehensive Privacy Laws: Overarching regulations like GDPR
International collaboration continues to refine these standards. The OECD recently established a landmark Declaration on Government Access to Personal Data, which aims to safeguard privacy and human rights during data access for national security and law enforcement purposes. This agreement represents a critical step in enhancing trust in cross-border data exchanges.
Organizations navigating this complex regulatory environment can benefit from understanding nuanced compliance strategies. Understanding the GRC Framework: Key Concepts Explained offers valuable insights into developing robust governance approaches that align with evolving global privacy standards.
As digital ecosystems become increasingly interconnected, understanding these frameworks is no longer optional but a fundamental business imperative. Companies must proactively adapt their data management practices to ensure compliance, protect individual rights, and maintain organizational integrity in a rapidly changing global landscape.
Types of Data Under Compliance Requirements
Data privacy compliance encompasses a wide range of sensitive information types that require meticulous protection and governance. According to Wikipedia, individuals have a fundamental right of access to their personal data, which is implemented through mechanisms like Subject Access Requests (SARs) that ensure transparency and individual control.
The primary categories of data subject to compliance requirements include:
- Personal Identifiable Information (PII): Names, social security numbers, contact details
- Financial Data: Bank accounts, credit card information, transaction records
- Health Information: Medical records, treatment histories, genetic data
- Biometric Data: Fingerprints, facial recognition patterns, voice prints
- Professional Information: Employment records, professional credentials
- Digital Interaction Data: IP addresses, browsing history, location tracking
Interestingly, the concept of data protection legislation has deep historical roots. Wikipedia's research highlights that Sweden enacted the world's first national data protection law in 1973, requiring licenses for information systems handling personal data and setting a groundbreaking precedent for global privacy regulations.
For organizations navigating these complex requirements, understanding sector-specific compliance nuances is crucial. Understanding the HIPAA Security Rule for Businesses provides valuable insights into healthcare-specific data protection protocols.
As digital ecosystems become increasingly sophisticated, the boundaries of sensitive data continue to evolve.
 Companies must remain proactive, implementing robust data classification strategies that not only meet current regulatory standards but anticipate future privacy protection challenges.
Companies must remain proactive, implementing robust data classification strategies that not only meet current regulatory standards but anticipate future privacy protection challenges.
Enterprise Responsibilities and Documentation Practices
Enterprise data privacy compliance demands a comprehensive and strategic approach to managing sensitive information. Research from arxiv.org introduces the innovative Data Capsule paradigm, which emphasizes embedding compliance directly into data processing practices by associating personal data with specific governing policies throughout its entire lifecycle.
Key enterprise responsibilities in data privacy documentation include:
- Policy Development: Creating clear, comprehensive data handling guidelines
- Risk Assessment: Systematically identifying and mitigating potential data vulnerabilities
- Consent Management: Documenting and tracking individual data usage permissions
- Audit Trail Maintenance: Recording all data processing activities and access logs
- Incident Response Planning: Establishing protocols for potential data breaches
- Training and Awareness: Educating employees about data privacy requirements
According to research from arxiv.org, modern regulatory frameworks focus on the outcomes and rights associated with data use, requiring enterprises to implement differential protections based on high-risk use cases. This approach necessitates a nuanced understanding of data processing that goes beyond mere technical compliance.
For organizations seeking to enhance their compliance strategies, 7 Essential Steps for a Security Compliance Checklist offers practical guidance for developing robust documentation practices.
Ultimately, effective enterprise data privacy is not a one-time achievement but an ongoing commitment.
Companies must continuously evolve their documentation practices, leveraging advanced technologies and maintaining a proactive approach to protecting individual rights and maintaining trust in an increasingly complex digital landscape.
Risks, Penalties, and Common Compliance Pitfalls
Data privacy compliance represents a critical challenge for organizations, with significant financial and reputational risks at stake. According to research from arxiv.org, the General Data Protection Regulation (GDPR) imposes stringent penalties that can reach up to 4% of a company's worldwide annual revenue, underscoring the severe consequences of non-compliance.
Common compliance pitfalls that organizations frequently encounter include:
- Incomplete Data Mapping: Failing to track all data flows and processing activities
- Inadequate Consent Mechanisms: Improper collection or documentation of user permissions
- Insufficient Security Controls: Weak protection of sensitive personal information
- Delayed Breach Notifications: Not reporting data incidents within required timeframes
- Poor Third-Party Risk Management: Overlooking vendor data handling practices
- Lack of Employee Training: Insufficient awareness about data protection protocols
International frameworks continue to evolve to address these challenges. The OECD has established critical guidelines aimed at safeguarding privacy and human rights, particularly in contexts involving national security and law enforcement data access.
Organizations seeking to mitigate these risks can benefit from understanding comprehensive vendor management strategies. What is Vendor Risk Management? Understanding Its Importance and Implementation provides valuable insights into managing external data protection challenges.
Ultimately, data privacy compliance is an ongoing journey. Proactive organizations must continuously assess their risks, update their practices, and maintain a robust culture of data protection that goes beyond mere regulatory checkbox compliance.
Simplify Data Privacy Compliance with Skypher
Navigating the complex world of data privacy compliance requires not only understanding laws like GDPR but also managing extensive security questionnaires and documentation efficiently. The challenges of incomplete data mapping, consent tracking, and risk mitigation call for a solution that streamlines these processes while ensuring accuracy and collaboration across teams. Skypher’s AI-powered Questionnaire Automation Tool is designed specifically for organizations in tech and finance seeking to reduce compliance workload and close gaps in data privacy management.

Take control of your compliance journey today by automating your security reviews and accelerating response times with Skypher’s integrations with over 40 third-party risk management platforms, Slack, ServiceNow, and more. Learn how to enhance your governance framework and trust with clients at Skypher’s homepage. Visit 7 Essential Steps for a Security Compliance Checklist to begin building a stronger documentation process, and explore how our Understanding the HIPAA Security Rule for Businesses content can enrich your strategy. Don’t wait for penalties or breaches to disrupt your business. Start streamlining your data privacy compliance today.
Frequently Asked Questions
What is data privacy compliance?
Data privacy compliance is a strategic framework that ensures organizations handle personal data responsibly and legally, protecting sensitive information according to established policies and regulations.
Why is compliance with data privacy regulations important?
Compliance with data privacy regulations is crucial to protect individual rights, maintain trust, avoid significant penalties, and mitigate risks associated with unauthorized data access and breaches.
What are some common types of data that require compliance?
Common types of data requiring compliance include Personal Identifiable Information (PII), financial data, health information, biometric data, and professional information, among others.
What are the risks of non-compliance with data privacy laws?
Non-compliance can lead to severe penalties, reputational damage, and financial loss. For example, under regulations like GDPR, penalties can reach up to 4% of a company's worldwide annual revenue.