Most American businesses that handle sensitive data rely on clear compliance to build trust, yet less than half understand the real difference between SOC 1 and SOC 2. These two standards are often confused, but knowing how they work can mean the difference between winning a client and losing credibility. Here you will find why these frameworks matter, what sets them apart, and which one genuinely protects your organization’s reputation.
Table of Contents
- SOC 1 And SOC 2 Explained Simply
- Key Differences In Purpose And Scope
- SOC 1 And SOC 2 Compliance Requirements
- Real-World Use Cases For B2B SaaS
- Risks And Common Mistakes To Avoid
Key Takeaways
| Point | Details |
|---|---|
| SOC 1 Focuses on Financial Reporting | SOC 1 reports assess controls primarily related to financial processes, ensuring accuracy and reliability in financial reporting. |
| SOC 2 Evaluates Non-Financial Controls | SOC 2 reports provide a broader assessment of operational controls, focusing on areas like security, confidentiality, and data integrity. |
| Importance of Compliance for Trust | Achieving SOC compliance enhances organizational credibility, demonstrating a commitment to robust internal controls and data protection standards. |
| Avoid Common Compliance Mistakes | Organizations should ensure adequate documentation and understanding of the specific SOC report required to prevent costly compliance errors. |
SOC 1 And SOC 2 Explained Simply
System and Organization Controls (SOC) reports represent critical compliance frameworks for service organizations seeking to validate their internal information system controls. SOC reporting standards were established by the American Institute of Certified Public Accountants (AICPA) to provide comprehensive assessments of organizational processes and security protocols.
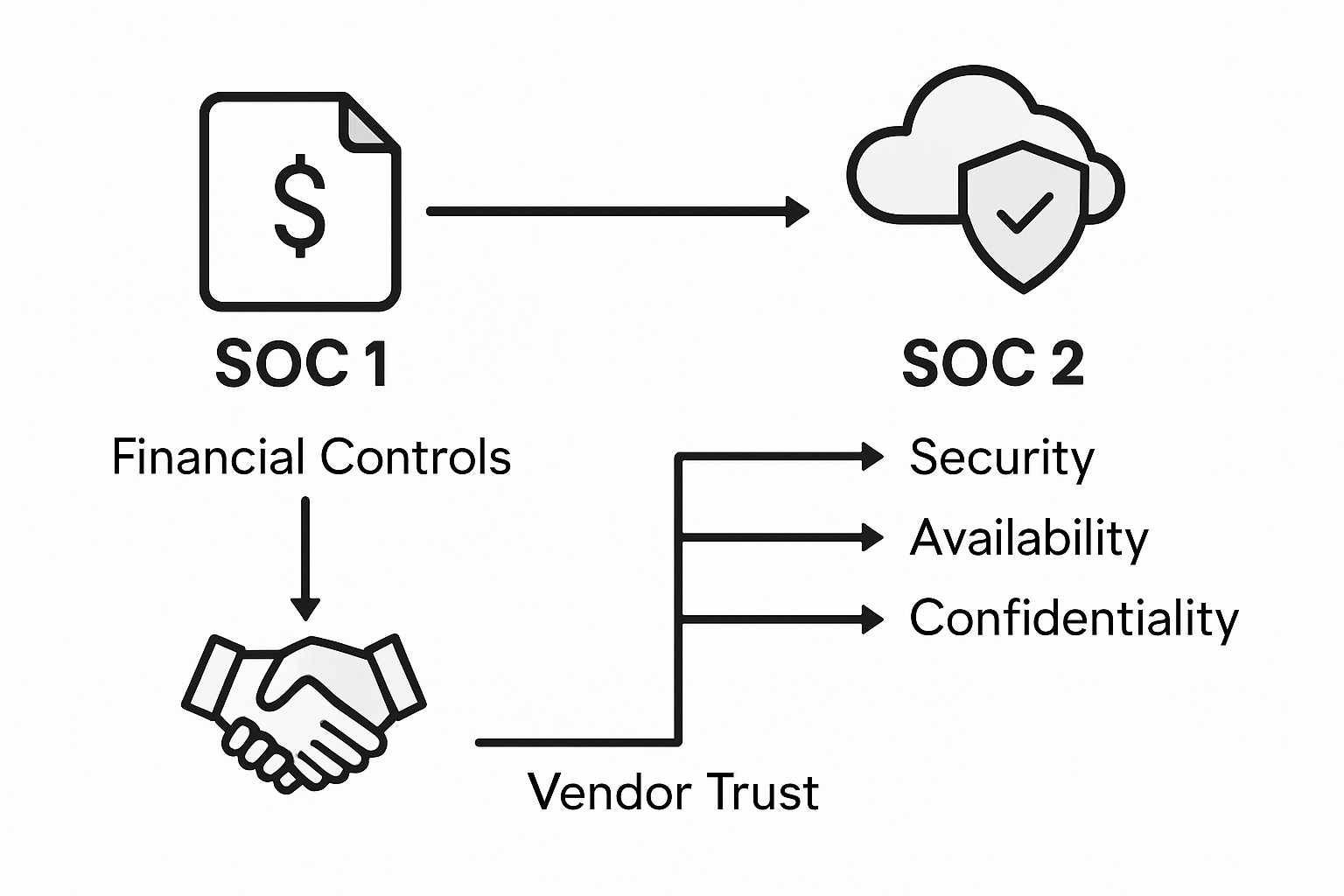
The fundamental difference between SOC 1 and SOC 2 reports lies in their specific focus and assessment goals. SOC 1 reports concentrate exclusively on controls relevant to financial reporting, ensuring accuracy and reliability in financial processes. In contrast, SOC 2 reports provide a broader evaluation of an organization's non-financial controls, specifically examining critical areas like data security, availability, processing integrity, confidentiality, and privacy.
When organizations pursue these compliance certifications, they demonstrate a commitment to robust internal controls and transparent operational practices. SOC compliance reports serve multiple strategic purposes for businesses:
- Validate the effectiveness of internal control mechanisms
- Provide assurance to stakeholders about organizational security practices
- Establish trust with clients and potential business partners
- Create a standardized framework for evaluating organizational risk management
For technology and financial service providers, these SOC reports are not just administrative documents but powerful tools for building credibility and showcasing organizational maturity in managing complex technological and financial ecosystems.
Key Differences In Purpose And Scope
The core distinction between SOC 1 and SOC 2 reports fundamentally hinges on their intended purpose and organizational focus. SOC report variations represent targeted assessment frameworks designed to address unique compliance and control requirements across different business domains.

SOC 1 Reports are narrowly scoped, concentrating exclusively on financial reporting controls. These reports examine the internal mechanisms that directly impact an organization's financial statements, providing assurance to stakeholders about the reliability and accuracy of financial processes. Typically, service organizations in accounting, banking, and financial service sectors prioritize SOC 1 certifications to demonstrate the integrity of their financial control environments.
In contrast, SOC 2 Reports offer a comprehensive evaluation of an organization's operational controls beyond financial metrics. These reports dive deep into critical technological and operational domains:
- Security: Assessing protective measures against unauthorized access
- Availability: Evaluating system accessibility and performance reliability
- Processing Integrity: Confirming data processing accuracy and completeness
- Confidentiality: Protecting sensitive information from unauthorized disclosure
- Privacy: Ensuring proper handling of personal and organizational data
The strategic implications of these reports extend far beyond mere compliance checkboxes. They serve as powerful tools for building trust, demonstrating organizational maturity, and providing transparent insights into an organization's internal control frameworks. Technology companies, cloud service providers, and data-driven enterprises frequently leverage SOC 2 reports to showcase their commitment to robust security and operational excellence.
SOC 1 And SOC 2 Compliance Requirements
SOC compliance frameworks represent intricate sets of requirements that organizations must meticulously implement to demonstrate their commitment to robust internal controls and data protection standards. These compliance frameworks are not mere checklist exercises but comprehensive assessments of an organization's operational integrity and risk management practices.
SOC 1 Compliance demands a laser-focused approach to financial reporting controls. Organizations pursuing this certification must establish and thoroughly document internal mechanisms that ensure the accuracy, reliability, and completeness of financial processes. This typically involves creating detailed control narratives, conducting rigorous testing of financial control effectiveness, and providing transparent documentation that demonstrates how financial risks are systematically managed and mitigated.
In contrast, SOC 2 Compliance offers a more expansive evaluation of organizational controls. Compliance requirements for SOC 2 are structured around five critical Trust Services Criteria:
- Security Controls: Protecting systems against unauthorized access
- Availability Controls: Ensuring consistent system accessibility
- Processing Integrity: Validating the accuracy of data processing
- Confidentiality: Safeguarding sensitive information
- Privacy: Managing personal data according to established principles
Successful SOC 2 compliance requires organizations to implement comprehensive control frameworks that go beyond traditional financial metrics. Technology companies, cloud service providers, and data-driven enterprises must demonstrate not just technical competence, but a holistic approach to protecting customer data and maintaining operational excellence. The process involves extensive documentation, independent audits, and a commitment to continuous improvement in security and privacy practices.
Real-World Use Cases For B2B SaaS
In the dynamic landscape of B2B Software as a Service (SaaS), SOC 1 and SOC 2 compliance certifications have become critical differentiators for technology companies seeking to establish trust and credibility. Data privacy best practices are increasingly important as organizations navigate complex regulatory environments and client expectations.
Cloud Service Providers represent a prime example of SOC compliance implementation. These companies handle massive amounts of sensitive customer data and must demonstrate rigorous security controls. A cloud storage platform, for instance, would leverage SOC 2 compliance to prove its commitment to protecting client information across multiple dimensions like security, availability, and confidentiality. This certification becomes a powerful marketing tool, instantly communicating to potential enterprise clients that the platform meets stringent operational standards.
For technology companies in specific sectors, SOC compliance offers targeted benefits:
- Financial Technology: Ensuring transaction security and data integrity
- Healthcare Software: Protecting patient information and maintaining HIPAA compliance
- Enterprise Resource Planning (ERP) Systems: Demonstrating financial control effectiveness
- Customer Relationship Management (CRM) Platforms: Securing sensitive customer data
- Cybersecurity Solutions: Proving internal control robustness
The strategic value of SOC certifications extends beyond mere compliance. For B2B SaaS organizations, these reports serve as powerful trust signals that can dramatically accelerate sales cycles, reduce vendor security assessments, and provide a competitive edge in markets where data protection is paramount. By proactively pursuing these certifications, companies communicate their commitment to operational excellence and customer data protection.
Risks And Common Mistakes To Avoid
SOC compliance challenges can quickly derail an organization's certification efforts if not carefully managed. Navigating the complex landscape of SOC 1 and SOC 2 requirements demands strategic preparation, deep understanding, and meticulous attention to detail.
One of the most critical mistakes organizations make is misidentifying the appropriate SOC report type. Many companies mistakenly attempt to apply SOC 2 controls to a SOC 1 audit or vice versa, leading to costly compliance failures. This fundamental misunderstanding can result in significant time and resource waste, potentially exposing the organization to unnecessary financial and reputational risks.
The most prevalent risks and common mistakes in SOC compliance include:
- Inadequate Documentation: Failing to maintain comprehensive and precise control narratives
- Insufficient Preparation: Underestimating the complexity and time required for compliance
- Control Inconsistency: Implementing controls that are not consistently applied across the organization
- Incomplete Scope Definition: Not clearly defining the systems and processes under assessment
- Lack of Continuous Monitoring: Treating compliance as a one-time event instead of an ongoing process
Compliance preparation strategies emphasize the importance of engaging experienced auditors and developing a proactive approach to risk management. Successful organizations view SOC compliance not as a checkbox exercise, but as a strategic opportunity to demonstrate operational excellence, build client trust, and create a robust framework for continuous improvement in security and control practices.
Simplify Your SOC 1 and SOC 2 Compliance with Skypher
Understanding the critical differences between SOC 1 and SOC 2 reports is just the first step toward building trust and securing your vendor security compliance. The challenge lies in efficiently managing the complex, time-consuming security questionnaires tied to these frameworks. Skypher’s AI Questionnaire Automation Tool is specifically designed to help organizations in tech and finance sectors accelerate their SOC compliance processes while reducing errors and operational costs.

Don’t let endless manual reviews stall your SOC 1 or SOC 2 certification journey. With Skypher, you gain access to real-time collaboration, seamless integrations with over 40 third-party risk management platforms, and a customizable Trust Center that clearly communicates your security posture. Take control of your vendor security compliance today by exploring how Skypher streamlines questionnaire responses and boosts your team’s productivity. Visit Skypher now and transform your security review process.
Learn more about bringing efficiency to your compliance at Skypher and discover practical automation solutions that keep your organization ahead of evolving SOC requirements.
Frequently Asked Questions
What is the main difference between SOC 1 and SOC 2?
SOC 1 focuses on controls relevant to financial reporting, ensuring the accuracy and reliability of financial processes. In contrast, SOC 2 evaluates non-financial controls, assessing areas such as data security, availability, processing integrity, confidentiality, and privacy.
Why are SOC 1 and SOC 2 reports important for vendor security compliance?
SOC 1 and SOC 2 reports validate the effectiveness of internal controls, provide assurance to stakeholders about security practices, establish trust with clients, and create a standardized framework for evaluating organizational risk management, which is crucial for vendor security compliance.
What industries typically require SOC 1 and SOC 2 compliance?
SOC 1 compliance is often prioritized by organizations in accounting, banking, and financial services, while SOC 2 compliance is relevant for technology companies, cloud service providers, and data-driven enterprises that handle sensitive information.
How do organizations prepare for SOC 1 and SOC 2 compliance?
Preparation for SOC 1 requires documentation of internal financial controls, rigorous testing, and transparent risk management practices. SOC 2 preparation demands comprehensive frameworks built around the Trust Services Criteria, including security and privacy measures, along with extensive documentation and independent audits.