In the realm of data security, understanding SOC 2 reports is essential. These reports are critical for any organization that seeks to demonstrate its commitment to protecting client information. Over 80 percent of data breaches result from human error or negligence, making robust compliance not just important but necessary. But here's the kicker: many companies mistakenly believe a simple report will suffice. The reality is, SOC 2 Type 1 and Type 2 reports serve distinct purposes. Opting for the wrong one could compromise your security credibility. It's time to uncover which report truly fits your organization's needs.
Table of Contents
- What Are Soc 2 Type 1 And Type 2 Reports
- Key Differences In Scope And Timeframe
- When To Choose Type 1 Or Type 2
- Achieving And Maintaining Soc 2 Compliance
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 Type 1 is a snapshot | Type 1 reports evaluate control design at a specific point in time, providing a brief overview of intended security measures. |
| SOC 2 Type 2 demonstrates ongoing performance | Type 2 reports assess both the design and operational effectiveness of controls over an extended period, usually 6 to 12 months, showcasing continuous compliance. |
| Strategic choice between Type 1 and Type 2 | Organizations often start with Type 1 reports to establish foundational security controls before progressing to Type 2 for deeper assurance, particularly in regulated industries. |
| Continuous compliance is essential | SOC 2 compliance requires ongoing effort, including regular internal audits, evidence collection, and updates to security policies to foster a culture of continuous improvement. |
| Documentation is critical | Achieving and maintaining SOC 2 compliance relies on thorough documentation, including management assertions and evidence mapping to Trust Services Criteria, ensuring effective control implementation. |
What are SOC 2 Type 1 and Type 2 Reports?
In the complex landscape of cybersecurity and data protection, SOC 2 reports have emerged as critical tools for organizations to demonstrate their commitment to robust security practices. These reports, developed by the American Institute of Certified Public Accountants (AICPA), provide comprehensive evaluations of an organization's internal controls and information security protocols.
Understanding the Fundamental Differences
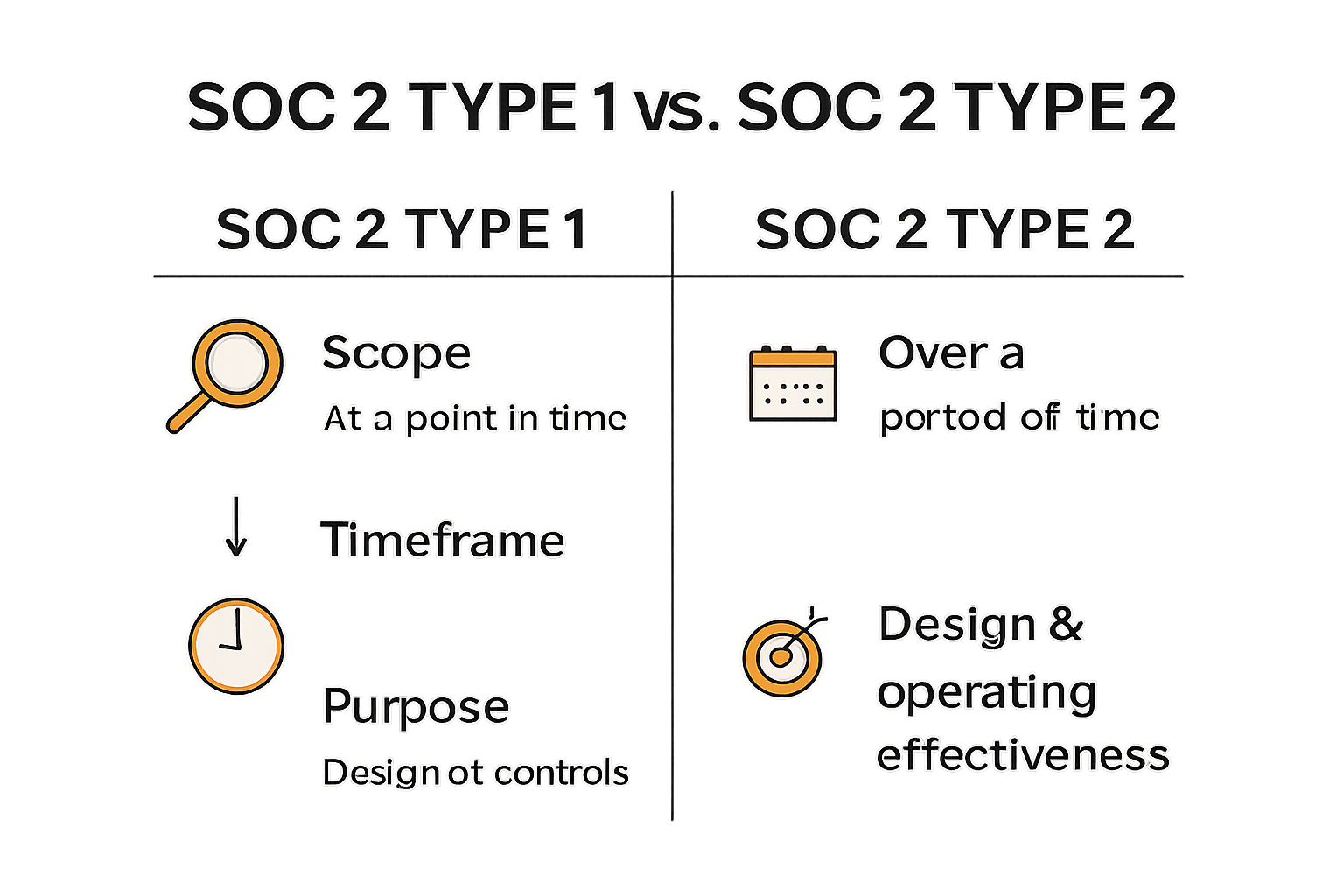
SOC 2 reports come in two distinct types - Type 1 and Type 2 - each serving a unique purpose in assessing an organization's security controls. The key difference lies in their scope, depth, and time frame of evaluation.
A SOC 2 Type 1 report focuses on a specific moment in time, examining the design of an organization's internal controls. Think of it as a snapshot that captures how security controls are structured and intended to work. According to AICPA guidelines, this report evaluates whether the controls are suitably designed to meet the five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
In-Depth Operational Assessment
In contrast, a SOC 2 Type 2 report provides a more comprehensive and dynamic assessment. Unlike the Type 1 report's snapshot approach, Type 2 involves a detailed examination of how controls actually perform over an extended period, typically six to twelve months. This report not only assesses the design of controls but also tests their operational effectiveness through rigorous testing and observation.
 The key distinctions between SOC 2 Type 1 and Type 2 reports can be summarized as follows:
The key distinctions between SOC 2 Type 1 and Type 2 reports can be summarized as follows:
-
Type 1 Report:
- Evaluates control design at a specific point in time
- Provides a snapshot of intended security measures
- Typically shorter and less extensive
-
Type 2 Report:
- Assesses both design and operational effectiveness
- Covers a sustained period of control implementation
- Includes detailed testing and verification of control performance
Research from Audit Board highlights that while both reports are crucial, the Type 2 report offers a more comprehensive view of an organization's security posture. It's particularly valuable for stakeholders, clients, and partners who want concrete evidence of sustained security practices.
For businesses operating in industries with stringent security requirements, such as cloud service providers, financial technology, and healthcare, these SOC 2 reports serve as critical validation of their commitment to protecting sensitive information. They demonstrate not just an intention to secure data, but a proven track record of maintaining robust security controls.
Whether an organization opts for a Type 1 or Type 2 report depends on its specific needs, industry requirements, and the level of assurance it wants to provide to stakeholders. While a Type 1 report can be a good starting point, many organizations ultimately pursue Type 2 reports to showcase their ongoing dedication to comprehensive security practices.
Key Differences in Scope and Timeframe
In the intricate world of cybersecurity compliance, understanding the nuanced differences between SOC 2 Type 1 and Type 2 reports is crucial for organizations seeking to demonstrate their commitment to robust security practices. The variations in scope and timeframe between these two report types significantly impact their depth, credibility, and value to stakeholders.
Temporal Dimensions of Assessment
The most fundamental distinction between SOC 2 Type 1 and Type 2 reports lies in their temporal approach to evaluating an organization's internal controls. According to Security Compass, SOC 2 Type 1 reports capture a momentary "snapshot" of an organization's control environment at a specific point in time. In contrast, SOC 2 Type 2 reports provide a comprehensive view of control effectiveness over an extended period, typically ranging from 6 to 12 months.
This temporal difference is more than just a technical nuance—it represents a profound shift in how security controls are evaluated. A Type 1 report offers a static picture of control design, while a Type 2 report presents a dynamic narrative of sustained security performance.
Depth of Examination and Evidence Collection
The scope of examination differs dramatically between these two report types. Research from Drata reveals that SOC 2 Type 1 audits primarily focus on the design of internal controls, assessing whether the controls are appropriately structured to meet the Trust Services Criteria. These audits are essentially a theoretical evaluation of how security measures should work.
In contrast, SOC 2 Type 2 audits demand a much more rigorous approach. Auditors must:
- Collect concrete evidence of control effectiveness
- Conduct extensive testing over the entire reporting period
- Verify operational performance through random sampling
- Demonstrate sustained implementation of security protocols
The key distinctions in scope can be summarized as follows:
-
Type 1 Scope:
- Evaluates control design at a single point in time
- Provides theoretical assessment of security measures
- Limited depth of examination
-
Type 2 Scope:
- Assesses both design and operational effectiveness
- Provides empirical evidence of control performance
- Comprehensive, time-based evaluation
Implications for Organizational Credibility
The choice between a Type 1 and Type 2 report carries significant implications for an organization's perceived security maturity. Scrut Automation notes that while Type 1 reports can be a starting point, they offer limited assurance to stakeholders. Type 2 reports, with their extensive time-based assessment, provide a more compelling narrative of an organization's sustained commitment to security.
For industries with stringent compliance requirements—such as cloud computing, financial services, and healthcare—the comprehensive nature of a Type 2 report becomes increasingly critical. It transforms security from a theoretical concept to a proven, ongoing practice.
Ultimately, the decision between a Type 1 and Type 2 report depends on an organization's specific needs, maturity level, and the expectations of its stakeholders. While Type 1 reports offer a quick glimpse into security controls, Type 2 reports tell a more complete story of an organization's security posture and continuous improvement efforts.
When to Choose Type 1 or Type 2
Navigating the complex landscape of SOC 2 compliance requires strategic decision-making about which report type best aligns with an organization's specific needs, maturity level, and compliance objectives. Understanding the nuanced scenarios where Type 1 or Type 2 reports are most appropriate can significantly impact an organization's security posture and stakeholder confidence.
Strategic Entry Points for Compliance
According to Secure Frame, organizations typically enter their SOC 2 compliance journey through a Type 1 report as an initial stepping stone. This approach allows businesses to establish a foundational understanding of their security control design before committing to the more extensive Type 2 assessment.
A Type 1 report becomes particularly strategic in scenarios such as:
- Emerging startups demonstrating initial security commitment
- Organizations preparing for more comprehensive future audits
- Companies needing quick evidence of control design
- Businesses with limited compliance resources
Comprehensive Evaluation Considerations
Research from Audit Board highlights that Type 2 reports become essential when organizations need to provide substantial evidence of sustained security performance. These reports are critically important for:
- Technology Service Providers: Demonstrating consistent security practices to enterprise clients
- Financial Technology Companies: Proving ongoing risk management capabilities
- Healthcare Technology Platforms: Establishing long-term data protection commitments
- Cloud Service Providers: Showcasing continuous control effectiveness
The decision matrix between Type 1 and Type 2 reports involves evaluating multiple strategic factors:
-
Resource Availability:
- Type 1: Lower time and financial investment
- Type 2: More comprehensive but resource-intensive
-
Stakeholder Requirements:
- Type 1: Initial compliance demonstration
- Type 2: Detailed operational assurance
-
Organizational Maturity:
- Type 1: Early-stage compliance preparation
- Type 2: Advanced security management
Progression and Continuous Improvement
Security Compass research suggests that most organizations view SOC 2 compliance as a progressive journey. Typically, companies start with a Type 1 report to establish baseline security controls and then transition to Type 2 reports to demonstrate sustained effectiveness.
This progression allows organizations to:
- Build incremental compliance capabilities
- Develop robust internal security processes
- Gradually enhance stakeholder trust
- Systematically improve control mechanisms
For many technology and service-oriented businesses, the transition from Type 1 to Type 2 represents more than a compliance checkbox—it's a strategic commitment to continuous security enhancement. The Type 2 report becomes a powerful narrative of an organization's dedication to maintaining high security standards.
Ultimately, the choice between Type 1 and Type 2 is not a one-size-fits-all decision. It requires careful assessment of organizational goals, client expectations, industry regulations, and internal capabilities. By understanding the strategic implications of each report type, businesses can make informed decisions that strengthen their security posture and build stakeholder confidence.
Achieving and Maintaining SOC 2 Compliance
Navigating the complex terrain of SOC 2 compliance requires a strategic, methodical approach that goes far beyond a simple checklist. Organizations must develop a comprehensive framework that not only satisfies initial audit requirements but also establishes a sustainable culture of continuous security improvement.
Foundational Documentation and Preparation
According to Secure Frame, achieving SOC 2 compliance hinges on developing three critical documents: the management assertion, system description, and control matrix. These documents serve as the comprehensive evidence base that demonstrates an organization's security posture to auditors.
Key preparation steps include:
- Conducting a comprehensive internal security assessment
- Identifying and documenting existing control mechanisms
- Mapping controls to specific Trust Services Criteria
- Developing robust policies and procedures
- Creating detailed evidence collection processes
Trust Services Criteria Implementation
Research from Sprinto highlights that SOC 2 compliance documentation must be tailored to the specific Trust Services Criteria (TSC) selected for the audit. Organizations must demonstrate comprehensive controls across five potential criteria:
- Security: Protecting system resources against unauthorized access
- Availability: Ensuring system accessibility as committed
- Processing Integrity: Maintaining system processing completeness and accuracy
- Confidentiality: Protecting confidential information
- Privacy: Managing personal information according to established commitments
Each criterion requires nuanced documentation and evidence that proves not just the existence of controls, but their consistent and effective implementation.
Continuous Compliance and Improvement
Expert guidance from Secureframe emphasizes that SOC 2 compliance is not a one-time achievement but an ongoing journey of continuous improvement. The management assertion becomes a critical document that explains how an organization's systems fulfill service commitments and meet selected Trust Services Criteria.
Successful ongoing compliance involves:
- Regular internal audits and control assessments
- Continuous monitoring of security controls
- Prompt addressing of identified vulnerabilities
- Periodic review and update of security policies
- Training and awareness programs for employees
Organizations must adopt a proactive approach, treating SOC 2 compliance as a dynamic process rather than a static certification. This means developing a security culture that prioritizes continuous improvement, adapts to emerging threats, and maintains rigorous documentation of control effectiveness.
The most successful organizations view SOC 2 compliance not as a burden, but as a strategic opportunity to demonstrate their commitment to security, build customer trust, and differentiate themselves in an increasingly competitive market. By developing robust internal processes, maintaining meticulous documentation, and fostering a culture of security awareness, businesses can transform compliance from a regulatory requirement into a significant competitive advantage.
Frequently Asked Questions
What is the main difference between SOC 2 Type 1 and Type 2 reports?
SOC 2 Type 1 reports assess the design of internal controls at a specific point in time, while SOC 2 Type 2 reports evaluate both the design and operational effectiveness of those controls over a period of 6 to 12 months.
When should an organization choose a SOC 2 Type 1 report?
Organizations typically choose a SOC 2 Type 1 report as a starting point to establish foundational security controls, especially emerging startups or those with limited compliance resources.
Why is SOC 2 Type 2 considered more comprehensive than Type 1?
SOC 2 Type 2 reports provide a thorough assessment of control effectiveness by including extensive testing, empirical evidence of performance, and demonstrating sustained adherence to security practices over time.
How does an organization maintain continuous compliance with SOC 2?
To maintain continuous compliance with SOC 2, organizations should conduct regular internal audits, monitor security controls, update policies as needed, and foster a security-aware culture among employees.
Streamline Your SOC 2 Compliance Journey with Skypher
Navigating the intricacies of SOC 2 compliance—whether you opt for a Type 1 or Type 2 report—can be daunting, especially when time and efficiency are of the essence. As you learned, SOC 2 Type 2 reports require ongoing evidence of security performance, which can be challenging without a reliable system in place. That's where Skypher comes in. Our **AI-driven Questionnaire Automation Tool simplifies and accelerates the security questionnaire response process, enabling you to meet compliance requirements with ease.

Imagine drastically reducing the time spent gathering evidence and documentation for your SOC 2 assessments. With features like real-time collaboration, a Custom Trust Center, and integrations with over 40 third-party risk management platforms, you can enhance your security posture while improving productivity across your teams. Don’t wait for compliance deadlines to loom—leverage Skypher’s solutions to maintain continuous compliance today!
