SOC 1 and SOC 2 might sound like alphabet soup, but they shape how companies prove their security and credibility every year. Here’s a curveball. SOC 2 reports cover five areas of trust—security, availability, processing integrity, confidentiality, and privacy—while SOC 1 targets just financial reporting. Yet the real surprise is that compliance is never a one-and-done deal, because both require ongoing assessments to maintain stakeholder trust year after year.
Table of Contents
- Soc1 And Soc2 Reports: What They Are
- Core Differences Between Soc1 And Soc2
- Choosing The Right Report For Your Business
- Common Myths About Soc1 And Soc2
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 1 Reports Focus on Financial Controls | SOC 1 reports are specifically designed to assess internal controls related to financial reporting, crucial for service organizations impacting clients' financial statements. |
| SOC 2 Reports Assess Broader Security Practices | SOC 2 reports evaluate an organization’s operational security based on five key Trust Services Criteria, offering a comprehensive view of security and privacy controls. |
| Choosing Between SOC 1 and SOC 2 | Organizations should assess their specific operational characteristics, industry requirements, and stakeholder expectations to determine the appropriate SOC report for their needs. |
| Both Report Types Can Be Type 1 or Type 2 | Type 1 reports evaluate the design of control systems at a specific point in time, while Type 2 reports assess their operational effectiveness over a defined period, particularly 6-12 months. |
| Ongoing Compliance is Necessary | SOC compliance is not a one-time event; organizations must continuously monitor and reassess their controls to maintain compliance and demonstrate a commitment to operational integrity. |
SOC1 and SOC2 Reports: What They Are
System and Organization Controls (SOC) reports represent critical compliance and security documentation that organizations use to demonstrate their commitment to data protection and operational integrity. These specialized audit reports provide deep insights into an organization's internal controls, offering transparency and reassurance to stakeholders, clients, and potential business partners.
Understanding the Fundamental Purpose of SOC Reports
SOC reports serve as comprehensive evaluations of an organization's control mechanisms, with SOC 1 and SOC 2 addressing different aspects of organizational performance. According to AICPA, these reports are designed to provide independent verification of an organization's control environment.
SOC 1 Reports: Financial Reporting Focus
SOC 1 reports specifically concentrate on internal controls related to financial reporting. These reports are crucial for service organizations that potentially impact their clients' financial statements. Research from Deloitte indicates that SOC 1 reports are typically used by organizations that provide services affecting financial processes, such as payroll processing, data center management, or cloud computing services that directly interact with financial systems.
SOC 2 Reports: Comprehensive Security and Privacy Evaluation
In contrast, SOC 2 reports provide a broader assessment of an organization's security practices. ISACA explains that these reports evaluate controls based on five key Trust Services Criteria:
- Security: Protecting against unauthorized system access
- Availability: Ensuring systems are operational and accessible
- Processing Integrity: Verifying system processing completeness and accuracy
- Confidentiality: Maintaining restricted information access
- Privacy: Managing personal information collection, use, and retention

Key Differences in Reporting Types
Both SOC 1 and SOC 2 reports can be issued in two primary formats: Type 1 and Type 2. AICPA clarifies the distinctions:
- Type 1 Reports: Evaluate the design of control systems at a specific point in time
- Type 2 Reports: Assess the operational effectiveness of controls over a defined period, typically 6-12 months
Organizations choose between these report types based on their specific compliance requirements, industry standards, and stakeholder expectations. While SOC 1 reports are more financially oriented, SOC 2 reports provide a comprehensive view of an organization's overall security and operational practices.
Understanding these reports is crucial for businesses seeking to demonstrate their commitment to robust internal controls, data protection, and operational excellence. By obtaining these certifications, organizations can build trust, enhance their credibility, and provide tangible evidence of their commitment to maintaining high standards of performance and security.
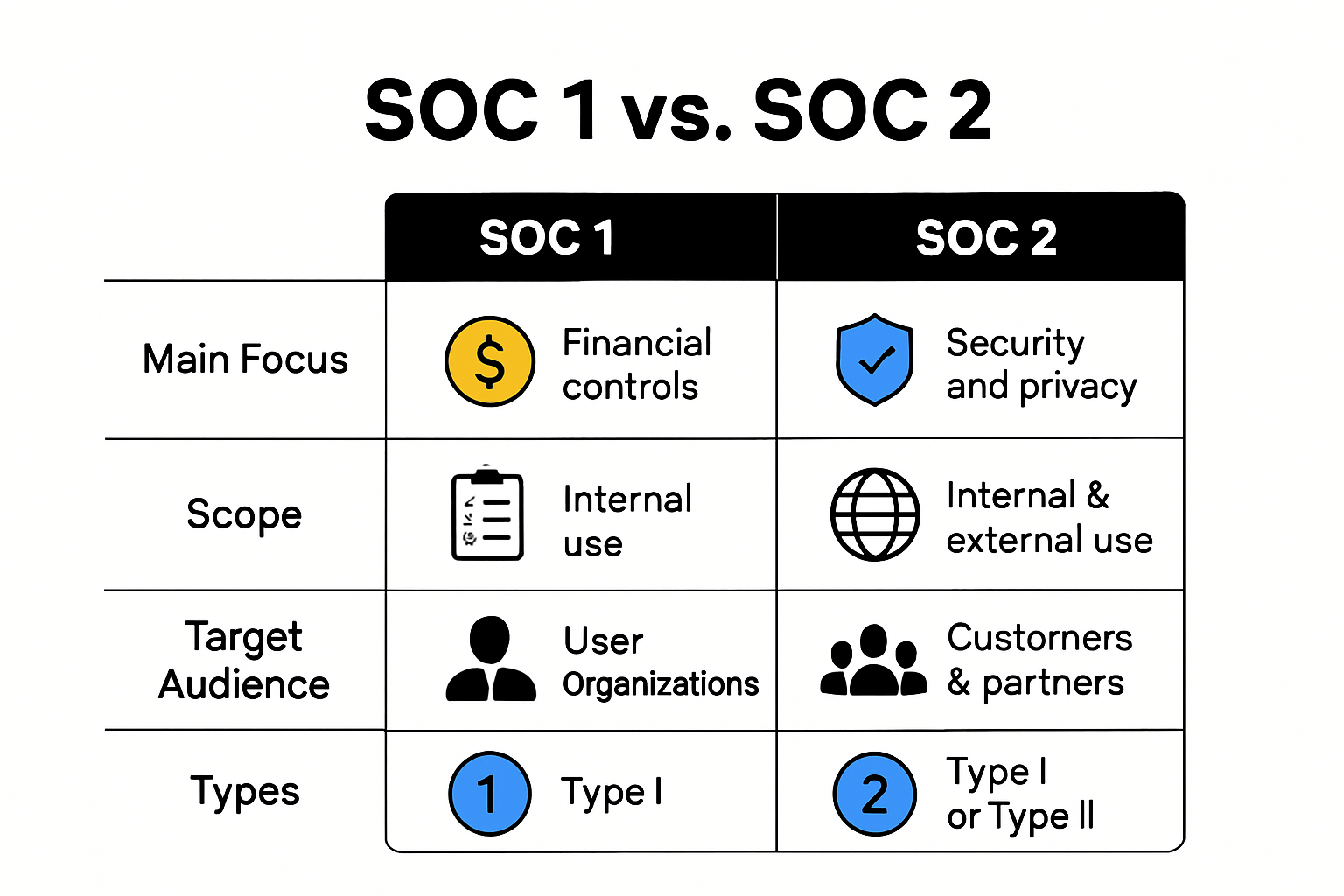
To help clarify the distinctions between SOC 1 and SOC 2 reports, the following table compares their key features:
| Aspect | SOC 1 | SOC 2 |
|---|---|---|
| Primary Focus | Financial reporting controls | Security, availability, processing integrity, |
| confidentiality, privacy (Trust Services Criteria) | ||
| Report Audience | Financial auditors, investors, | Clients, business partners, regulators, |
| organizations impacted by | cybersecurity stakeholders | |
| financial statements | ||
| Ideal For | Payroll/financial service | Technology, cloud, data management, |
| providers, transaction systems | organizations handling sensitive customer information | |
| Applicable Controls | Financial controls | Operational and security/privacy controls |
| Types Available | Type 1 and Type 2 | Type 1 and Type 2 |
| Certifying Body | AICPA | AICPA |
Core Differences Between SOC1 and SOC2
The distinction between SOC 1 and SOC 2 reports is critical for organizations seeking to demonstrate their commitment to robust control mechanisms and stakeholder trust. While both report types emerge from the American Institute of Certified Public Accountants (AICPA) framework, they serve fundamentally different purposes and address distinct organizational aspects.
Purpose and Scope of Control Assessment
SOC 1 and SOC 2 reports diverge significantly in their primary objectives and evaluation focus. Deloitte highlights that SOC 1 reports concentrate exclusively on financial reporting controls, whereas SOC 2 reports provide a comprehensive assessment of an organization's broader operational security and privacy practices.
Financial vs. Operational Control Frameworks
SOC 1 reports are tightly aligned with financial reporting controls. These reports assess internal mechanisms that directly impact an organization's financial statements. KPMG explains that service organizations handling financial processes like payroll, accounting systems, or transaction processing require SOC 1 certifications to demonstrate the reliability of their financial control environment.
In contrast, SOC 2 reports evaluate an organization's non-financial control systems. ISACA emphasizes that these reports examine five critical Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
Audience and Reporting Perspectives
The intended audience for SOC 1 and SOC 2 reports differs substantially. PwC provides insights into the distinct target audiences for each report type:
- SOC 1 Reports: Primarily targeting financial auditors, investors, and stakeholders concerned with financial reporting accuracy
- SOC 2 Reports: Addressing a broader audience including potential clients, business partners, regulators, and cybersecurity professionals interested in comprehensive operational security
Compliance and Risk Management Implications
Organizations must strategically choose between SOC 1 and SOC 2 reports based on their industry requirements and stakeholder expectations. Technology service providers, cloud computing companies, and data management firms often require SOC 2 reports to demonstrate their commitment to robust security practices. Financial service providers and organizations with significant financial processing responsibilities typically prioritize SOC 1 compliance.
The reporting process for both SOC types involves rigorous independent assessments. Certified public accountants conduct thorough evaluations, examining control design (Type 1 reports) and operational effectiveness (Type 2 reports). This systematic approach ensures that organizations maintain high standards of internal control and transparency.
Understanding the nuanced differences between SOC 1 and SOC 2 reports enables organizations to select the most appropriate compliance documentation. By aligning their reporting strategy with specific organizational needs, businesses can effectively communicate their commitment to financial integrity, operational security, and stakeholder trust.
Choosing the Right Report for Your Business
Selecting the appropriate SOC report is a strategic decision that requires careful evaluation of your organization's specific operational characteristics, industry requirements, and stakeholder expectations. The choice between SOC 1 and SOC 2 reports can significantly impact your business's credibility, compliance posture, and ability to demonstrate operational excellence.
Assessing Organizational Needs and Industry Requirements
Determining the right SOC report begins with a comprehensive analysis of your organization's core business functions and potential risks. Gartner recommends conducting a thorough internal assessment that examines the following critical factors:
- Service Characteristics: The nature of services provided
- Data Handling Processes: Types of sensitive information managed
- Regulatory Compliance Obligations
- Stakeholder Reporting Requirements
Strategic Considerations for Report Selection
The selection process involves understanding the unique value proposition of each report type. PwC suggests a strategic approach to report selection based on organizational objectives:
-
SOC 1 Reporting Ideal For:
- Financial service providers
- Organizations processing financial transactions
- Companies directly impacting client financial statements
-
SOC 2 Reporting Ideal For:
- Technology service providers
- Cloud computing companies
- Data management and security-focused organizations
- Companies handling sensitive customer information
To better visualize which industries and business types typically benefit from each SOC report, the table below summarizes these recommendations:
| Report Type | Ideal For (Business Types) | Example Services/Industries |
|---|---|---|
| SOC 1 | Financial service providers, payroll companies, | Payroll processing, transaction systems, |
| data center firms directly impacting financial | accounting platforms, banking support services | |
| statements | ||
| SOC 2 | Technology providers, cloud & data companies, | SaaS, hosting/cloud providers, cybersecurity |
| organizations handling sensitive information | services, IT managed services |
Comprehensive Risk and Compliance Evaluation
Beyond immediate reporting needs, organizations must consider long-term strategic implications. McKinsey emphasizes the importance of a holistic approach to compliance and risk management.
Key Decision-Making Factors
Deciding between SOC 1 and SOC 2 reports involves evaluating multiple dimensions:
- Regulatory Environment: Different industries have unique compliance requirements
- Client Expectations: Stakeholder demands for transparency and security
- Operational Complexity: Depth of internal control mechanisms
- Risk Management Strategy: Proactive approach to identifying and mitigating potential vulnerabilities
Ernst & Young recommends a dynamic approach that allows for potential future reporting needs. Many organizations find value in pursuing both SOC 1 and SOC 2 reports to provide comprehensive assurance across financial and operational domains.
The most effective strategy involves consulting with compliance experts, conducting internal risk assessments, and aligning reporting approaches with broader organizational goals. By carefully evaluating your specific business context, you can select a SOC report that not only meets current requirements but also supports future growth and stakeholder confidence.
Common Myths About SOC1 and SOC2
Misunderstandings about SOC 1 and SOC 2 reports can lead organizations to make uninformed decisions about their compliance strategies. Debunking these myths is crucial for developing a comprehensive and effective approach to organizational control and security documentation.
Misconceptions About Report Purpose and Scope
Many organizations harbor fundamental misunderstandings about the nature and application of SOC reports. AICPA reveals several prevalent misconceptions that can significantly impact compliance strategies.
Myth 1: SOC Reports Are Universal Certifications
Contrary to popular belief, SOC 1 and SOC 2 reports are not universal certifications. Deloitte emphasizes that these are detailed attestation reports providing in-depth insights into an organization's control mechanisms. They represent a comprehensive evaluation of specific control environments, not a one-size-fits-all stamp of approval.
Myth 2: Only Large Enterprises Need SOC Reports
Small and medium-sized businesses often mistakenly believe SOC reports are exclusively for large corporations. KPMG argues that organizations of all sizes can benefit from SOC reporting. Smaller businesses can use these reports to:
- Demonstrate operational reliability
- Build customer trust
- Differentiate themselves in competitive markets
- Provide transparent insight into their control environments
Misunderstandings About Compliance and Implementation
Complexities surrounding SOC 1 and SOC 2 reports often lead to significant misconceptions about their implementation and ongoing maintenance. Ernst & Young provides critical insights into these common misunderstandings.
Myth 3: Compliance is a One-Time Event
ISACA strongly refutes the notion that SOC compliance is a single, static achievement. The reality is far more dynamic:
- SOC reports require annual reassessment
- Continuous monitoring of control effectiveness is essential
- Organizations must demonstrate ongoing commitment to maintaining established controls
- Regular internal audits and updates are crucial for maintaining compliance
Crucial Compliance Considerations
Organizations must recognize that SOC reporting is an evolving process, not a static document. PwC recommends a proactive approach that involves:
- Regular risk assessments
- Continuous control monitoring
- Adapting to changing regulatory landscapes
- Maintaining robust documentation
By dispelling these myths, organizations can develop a more nuanced and effective approach to SOC 1 and SOC 2 reporting. Understanding the true nature of these reports enables businesses to leverage them as powerful tools for demonstrating operational integrity, building stakeholder confidence, and managing organizational risks effectively.
Frequently Asked Questions
What is the main difference between SOC 1 and SOC 2 reports?
SOC 1 reports focus on internal controls related to financial reporting, while SOC 2 reports assess broader operational security practices based on five key Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
Who should obtain a SOC 1 report?
Organizations that provide services affecting financial processes, such as payroll processing or cloud computing services that interact with financial systems, should obtain a SOC 1 report to demonstrate the reliability of their financial controls.
What types of organizations benefit from SOC 2 reports?
Technology service providers, cloud computing companies, and organizations handling sensitive customer information are ideal candidates for SOC 2 reports, as these reports evaluate their commitment to robust security and privacy practices.
Are SOC 1 and SOC 2 reports one-time certifications?
No, SOC compliance is not a one-time event. Both SOC 1 and SOC 2 reports require ongoing assessments to maintain compliance and demonstrate a commitment to operational integrity annually.
Tackle SOC1 and SOC2 Demands Faster with AI Questionnaire Automation
Struggling with the constant pressure of security questionnaires tied to SOC1 and SOC2 compliance? Many growing businesses in tech and finance feel buried under repetitive requests and tight reporting deadlines. The need for transparent, accurate answers across trust criteria like security and confidentiality is higher than ever, especially when proof is required year after year. Manual processes can slow your team down, drain resources, and even risk losing client trust.

Why let security reviews and compliance bottlenecks stand in your way? Experience how Skypher enables you to complete SOC-related security questionnaires in a fraction of the time. Our AI Questionnaire Automation Tool integrates with trust platforms you already use and supports real-time collaboration for painless, audit-ready responses. Discover how top organizations are accelerating sales cycles while improving accuracy and stakeholder confidence. Explore the platform now to transform your SOC compliance experience.
