Most organizations worry about cyber threats and scramble to stay ahead of attacks. Yet a stunning fact stands out. Over 90 percent of data breaches happen because of human error, not technical flaws. Surprised? Most teams pour money into expensive software but overlook the everyday habits of their staff. Fixing that blind spot starts with one shift most companies never realize they need.
Table of Contents
- Step 1: Evaluate Your Current Security Posture
- Step 2: Identify Training Needs And Objectives
- Step 3: Develop A Comprehensive Training Program
- Step 4: Implement Engaging Training Delivery Methods
- Step 5: Measure Effectiveness And Adapt Training Approaches
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Evaluate Current Security Posture | Assessing your security strengths and vulnerabilities helps create a focused training program tailored to your organization's needs. |
| 2. Identify Specific Training Needs | Analyze initial assessment data to pinpoint knowledge gaps and align training topics with identified security risks. |
| 3. Develop Engaging Training Programs | Combine various learning methods, such as online modules and simulations, to enhance employee understanding and retention of cybersecurity practices. |
| 4. Implement Interactive Delivery Methods | Use diverse training formats like gamified lessons and real-world scenarios to actively engage employees in security awareness. |
| 5. Measure Effectiveness and Adapt | Continuously evaluate training impact through metrics and feedback, enabling data-driven improvements to the security awareness program. |
Step 1: Evaluate Your Current Security Posture
Evaluating your current security posture is a critical first step in developing an effective security awareness and training program. This foundational assessment helps you understand your organization's existing cybersecurity strengths, vulnerabilities, and potential risk areas. By conducting a comprehensive review, you'll create a targeted approach that addresses specific security challenges unique to your team.
Begin your evaluation by performing a thorough organizational security assessment. This process involves gathering data from multiple sources within your company. Start with comprehensive interviews and surveys with key stakeholders across different departments including IT, human resources, legal, and operations. These conversations will reveal existing security practices, potential knowledge gaps, and current employee understanding of cybersecurity protocols.
Next, conduct a detailed technical assessment of your current security infrastructure. This means reviewing your existing security tools, network configurations, access management systems, and incident response protocols. Learn more about identifying security gaps through the Cybersecurity and Infrastructure Security Agency's guidelines. Pay special attention to areas like password management, multi factor authentication, remote work security, and employee device policies.
Documenting your findings is crucial. Create a comprehensive report that highlights current security strengths, identifies potential vulnerabilities, and outlines specific areas where security awareness and training can make the most significant impact. Your report should include quantitative metrics such as the number of potential security risks identified, current employee security knowledge levels, and potential financial or operational risks associated with existing security gaps.
Here is a checklist summarizing key verification criteria and documentation steps to guide your evaluation of the current security posture.
| Verification Criteria | Description |
|---|---|
| Employee Understanding of Protocols | Percentage of staff who know and follow security policies |
| Number of Identified Vulnerabilities | Count of security risks found across different departments |
| Security Training Completion Rates | Proportion of employees who finished required security training |
| Financial Risk Exposure | Estimated financial impact from existing security gaps |
| Frequency of Security Posture Assessments | How often security posture is reviewed and updated |
| Documentation of Findings | Record of strengths, vulnerabilities, and target areas for training |
To validate your assessment, establish clear verification criteria. These might include:
- Percentage of employees who understand current security protocols
- Number of identified security vulnerabilities across different departments
- Existing security training completion rates
- Potential financial risk exposure from current security practices
Remember that this evaluation is not a one time event but an ongoing process. Technology and threat landscapes evolve rapidly, so your security posture assessment should be repeated regularly to ensure continuous improvement and adaptation to emerging cybersecurity challenges.
Step 2: Identify Training Needs and Objectives
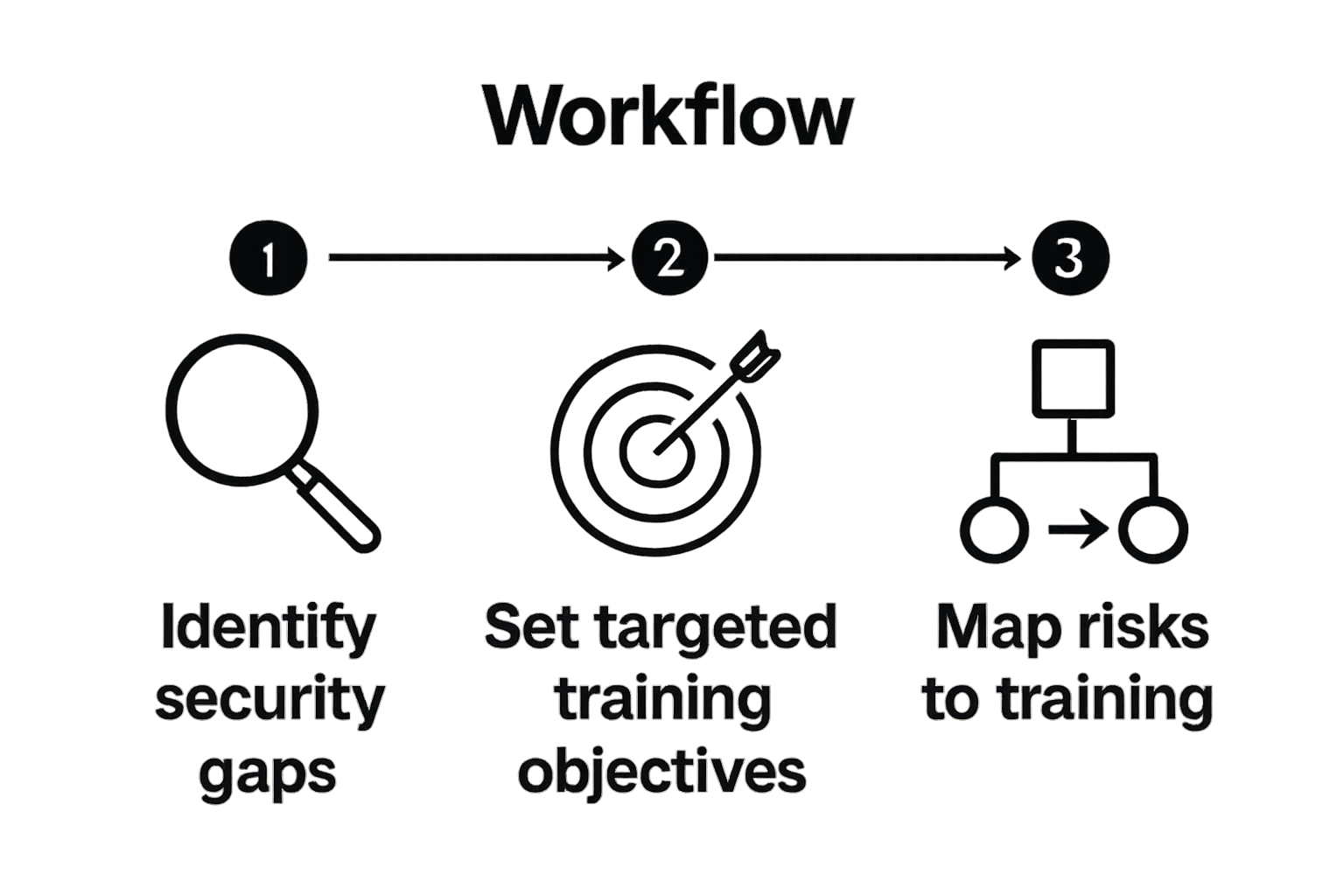
Identifying specific security awareness and training needs is a strategic process that transforms your initial security posture assessment into a targeted, actionable learning plan. This crucial step bridges the gap between understanding your current security landscape and developing a comprehensive training approach that addresses your organization's unique vulnerabilities.
Begin by analyzing the data collected during your initial security posture evaluation. Look for patterns of knowledge gaps, common security misconceptions, and areas where employees demonstrate limited understanding of cybersecurity best practices. According to NIST guidelines on building security awareness programs, the most effective training programs are those directly aligned with an organization's specific risk profile.
Develop a detailed matrix that maps identified security risks to specific training objectives. This might include addressing challenges like phishing awareness, password management, social engineering prevention, and secure remote work practices. Consider the different skill levels and roles within your organization, recognizing that a financial analyst may require different security training compared to an IT support technician.
Engaging stakeholders is critical during this phase. Schedule collaborative sessions with department heads, team leaders, and security professionals to gain deeper insights into role specific security challenges. These conversations will help you create nuanced training objectives that resonate with different teams and address their unique operational contexts.
Your training needs identification should result in a comprehensive document that outlines:
- Specific security knowledge gaps identified
- Prioritized training topics based on organizational risk
- Targeted learning objectives for different employee groups
- Measurable outcomes expected from the training program
Verify the effectiveness of your training needs identification by conducting a preliminary skills assessment. This can include short knowledge quizzes, scenario based evaluations, or simulated security challenge exercises that help you benchmark current employee understanding and track future improvements. Remember that identifying training needs is an ongoing process requiring regular reassessment as technological landscapes and security threats continue to evolve.
Step 3: Develop a Comprehensive Training Program
Developing a comprehensive security awareness and training program transforms your identified needs into a structured, engaging learning experience that empowers employees to become active defenders of your organization's cybersecurity. This step requires a strategic approach that combines multiple learning methodologies, technologies, and interactive experiences to ensure maximum knowledge retention and behavioral change.
Start by designing a multi modal training curriculum that addresses different learning styles and preferences. This means creating a blend of interactive online modules, live workshops, video tutorials, real world simulation exercises, and periodic knowledge assessment tests. Recognize that employees learn differently, so your program should offer diverse content delivery methods that keep participants engaged and motivated.
Technology plays a crucial role in modern security training. Explore comprehensive cybersecurity training resources recommended by the SANS Institute to understand cutting edge approaches. Implement learning management systems that allow for personalized learning paths, tracking individual progress, and generating detailed performance reports. These platforms can help you customize training intensity and content based on an employee's existing security knowledge and role within the organization.
Consider developing scenario based training modules that simulate real world cybersecurity challenges. These might include phishing email simulations, social engineering scenarios, secure password creation exercises, and incident response role playing activities. By presenting practical, contextual learning experiences, you transform abstract security concepts into tangible skills that employees can immediately apply in their daily work environments.
Your comprehensive training program should include key elements such as:
- Customized learning paths for different organizational roles
- Interactive and engaging multimedia content
- Regular assessment and knowledge verification mechanisms
- Continuous learning and refresher modules
- Tracking and reporting capabilities
To verify the effectiveness of your training program, establish clear metrics and evaluation criteria. This includes measuring knowledge retention rates, tracking improvements in simulated security challenge performance, and gathering qualitative feedback from participants. Remember that a truly comprehensive security awareness program is not a one time event but an ongoing, evolving process that adapts to emerging technological challenges and organizational needs.
Step 4: Implement Engaging Training Delivery Methods
Implementing engaging training delivery methods is crucial to transforming security awareness from a mundane compliance requirement into an interactive, memorable learning experience. The goal is to create training approaches that capture employees' attention, encourage active participation, and ultimately drive meaningful behavioral change in cybersecurity practices.
Begin by diversifying your training delivery mechanisms to cater to different learning preferences and engagement levels. This means moving beyond traditional lecture style presentations and embracing interactive and immersive learning experiences. According to NIST guidelines on security awareness training, successful programs incorporate multiple delivery formats that keep participants actively involved and motivated.
Develop a mix of training modalities that include digital simulations, gamified learning experiences, live workshops, and real world scenario based exercises. For instance, create phishing simulation modules where employees interact with mock email threats, learning to identify and respond to potential security risks in a controlled environment. Implement cybersecurity challenge platforms that reward employees for successfully navigating complex security scenarios, turning learning into an engaging and competitive experience.
The table below highlights several training modalities and delivery methods, along with their characteristics and how they contribute to security awareness.
| Delivery Method | Engagement Level | Typical Use | Example Activity |
|---|---|---|---|
| Interactive Online Modules | High | Foundational knowledge | Self-paced e-learning content |
| Live Workshops | Moderate-High | In-depth or group learning | Facilitated group training sessions |
| Simulations | High | Realistic threat scenarios | Phishing email exercises |
| Gamified Challenges | High | Motivation through competition | Security quizzes and leaderboards |
| Knowledge Assessments | Moderate | Progress checks | Post-training quizzes |
Technology plays a critical role in modern training delivery. Utilize learning management systems that support adaptive learning paths, allowing content to dynamically adjust based on an individual's current knowledge level and performance. These platforms can track progress, provide personalized feedback, and generate comprehensive reports that help you understand the effectiveness of your training program.
Your training delivery strategy should include key components such as:
- Interactive online modules with real time feedback
- Hands on practical exercises and simulations
- Periodic knowledge assessment tests
- Personalized learning experiences
- Continuous performance tracking
To verify the effectiveness of your training delivery methods, establish clear metrics for engagement and knowledge retention. This might include measuring completion rates, tracking improvements in simulated security challenge performance, and collecting qualitative feedback from participants. Regularly review and refine your delivery approach, recognizing that effective security awareness training is an evolving process that requires continuous adaptation to emerging technological challenges and organizational needs.
Step 5: Measure Effectiveness and Adapt Training Approaches
Measuring the effectiveness of your security awareness and training program is a critical step that transforms your training initiative from a static compliance exercise into a dynamic, continuously improving organizational capability. This process involves systematic evaluation, data collection, and strategic refinement of your security awareness strategies.
Begin by establishing comprehensive measurement frameworks that go beyond simple completion rates. According to CISA's Insider Threat Mitigation Guide, effective measurement requires a multifaceted approach that captures both quantitative and qualitative insights into your security awareness program's impact. Develop a robust set of metrics that track knowledge acquisition, behavioral changes, and tangible security improvements across your organization.
Implement a series of assessment tools designed to provide deep insights into your training program's effectiveness. This includes conducting simulated security challenges like phishing email tests, social engineering scenario evaluations, and practical cybersecurity skills assessments. These targeted exercises help you understand not just what employees know, but how they actually perform when confronted with real world security threats. Track individual and team performance metrics, identifying patterns of strength and areas requiring additional focus or intervention.
Data analysis becomes crucial in this stage. Utilize advanced analytics platforms that can aggregate and interpret training performance data, generating actionable insights. Look for trends such as recurring security knowledge gaps, variations in performance across different departments, and the correlation between training interventions and actual security incident reduction. Your goal is to create a continuous improvement feedback loop that allows your security awareness program to evolve dynamically.
Your effectiveness measurement strategy should include key components such as:
- Quantitative performance metrics and knowledge assessments
- Simulated security challenge results
- Comparative analysis of pre and post training security behaviors
- Incident response and risk mitigation tracking
- Employee feedback and perception surveys
Verify the success of your measurement approach by establishing baseline performance indicators and tracking meaningful improvements over time. Remember that measuring effectiveness is not a one time event but an ongoing process of refinement. Regularly review your metrics, solicit feedback from participants, and be prepared to make data driven adjustments to your security awareness and training program. The most successful organizations view security awareness as a continuous journey of learning, adaptation, and improvement.

Secure Your Team’s Future with Smarter Security Automation
Are you struggling to turn security awareness into real, measurable action for your organization? Even with a well-structured training program, teams often face bottlenecks when handling complex security reviews and responding to detailed security questionnaires. Gaps in coordination and slow processes can leave your company exposed, delay sales, and frustrate both internal stakeholders and clients.

What if you could reinforce your team’s cybersecurity posture while making security reviews faster and more accurate? Skypher offers an AI-driven Questionnaire Automation Tool that complements your training efforts by automating the response process for security reviews. Boost your efficiency with real-time collaboration, seamless integrations, and instant access to a customizable Trust Center. Say goodbye to endless manual updates and help your team put their security awareness into action.
Discover how Skypher’s platform can help your business mitigate risks, win client trust, and meet compliance standards without extra effort. Visit Skypher’s homepage now to see how you can transform your security operations and take the next step toward a stronger cybersecurity culture.
Frequently Asked Questions
What is the first step in enhancing security awareness and training for my team?
Evaluating your current security posture is the first step. This involves assessing your organization's cybersecurity strengths, vulnerabilities, and potential risks to create a targeted training program.
How do I identify training needs for my team?
Start by analyzing the data collected during your security posture evaluation. Look for knowledge gaps and misconceptions among employees, and develop specific training objectives that align with your organization's unique vulnerabilities.
What methodologies should be included in a comprehensive training program?
A well-rounded training program should include a mix of interactive online modules, live workshops, video tutorials, real-world simulations, and periodic knowledge assessments to cater to different learning styles.
How can I measure the effectiveness of my security awareness training program?
Establish comprehensive measurement frameworks that track both quantitative and qualitative metrics, such as knowledge retention rates, performance on simulated security challenges, and employee feedback, to continuously improve your program.