Security questions have been a staple of online account protection for years. Surprising as it may seem, over 60 percent of users can easily guess the answers to common security questions. This stark reality comes from the fact that many of these questions rely on publicly accessible or easily guessed information. Despite their long-standing usage, security questions are increasingly recognized as a weak link in the cybersecurity chain. The truth is, relying solely on them can leave your accounts open to potential breaches.
Table of Contents
- What Is A Common Security Question?
- Why Security Questions Can Pose Risks
- Better Ways To Secure Your Accounts
- Security Question Examples To Avoid
Quick Summary
| Takeaway | Explanation |
|---|---|
| Security questions pose significant risks | They can be easily compromised through social engineering and predictable answers, making them less reliable for authentication. |
| Use multi-factor authentication (MFA) | MFA combines multiple verification methods, dramatically improving account security and reducing the likelihood of unauthorized access. |
| Avoid questions with publicly discoverable answers | Questions that rely on easily accessible personal information significantly increase vulnerability; examples include birthplace and high school names. |
| Create unique and complex security questions | Effective questions should have personal significance but be difficult for others to guess, ensuring stronger protection against potential breaches. |
| Adopt proactive account protection strategies | Incorporate ongoing monitoring, zero-trust models, and advanced techniques to enhance the overall security of digital accounts. |
What is a Common Security Question?
Security questions are a fundamental authentication method used to verify a user's identity by requiring them to answer personal queries that ideally only they would know. These questions serve as an additional layer of protection beyond traditional passwords, helping to confirm a user's identity during account recovery, password resets, or accessing sensitive information.
Understanding the Purpose of Security Questions
At their core, security questions are designed to create a personalized verification mechanism. Unlike standard passwords, these questions rely on unique personal knowledge that is typically difficult for others to guess or discover. A classic example of a security question might be "What was the name of your first pet?" or "In what city were you born?"
According to Okta, security questions can be either user-defined or system-generated. User-defined questions allow individuals to create their own personalized queries, while system-defined questions provide a standardized set of options. The goal is to establish a verification method that is simultaneously memorable for the user and challenging for potential unauthorized access attempts.
Characteristics of Effective Security Questions
Not all security questions are created equal. Research from Science Buddies highlights several critical attributes of good security questions:
- Memorability: The question must be something the user can consistently remember
- Specificity: Answers should be relatively unchanging over time
- Difficulty to Guess: The response should not be easily discoverable by others
- Limited Variability: Answers should have minimal potential for variation
For instance, a poor example of a security question would be "What is your favorite color?" This type of question is problematic because favorite colors can change, and the answer might be easily guessed or discovered through casual conversation. A stronger example might be "What was the model of your first car?" which tends to be more specific and less likely to change.
Cybersecurity experts recommend creating security questions that balance personal significance with genuine complexity. The most secure security questions are those that produce answers which are simultaneously unique to the individual, difficult for others to research, and consistent over time.
While security questions provide an additional authentication layer, they are not infallible. Modern cybersecurity strategies increasingly recommend using multi-factor authentication that combines multiple verification methods, such as security questions with temporary codes or biometric verification, to create more robust protection against unauthorized access.
Ultimately, a good security question is like a personal puzzle piece - uniquely yours, hard for others to replicate, and consistently recognizable to you alone.
Why Security Questions Can Pose Risks
 While security questions are widely used as an authentication method, they inherently contain significant vulnerabilities that can compromise user data and system integrity. Understanding these risks is crucial for developing more robust security strategies and protecting sensitive information from potential breaches.
While security questions are widely used as an authentication method, they inherently contain significant vulnerabilities that can compromise user data and system integrity. Understanding these risks is crucial for developing more robust security strategies and protecting sensitive information from potential breaches.
Information Accessibility and Social Engineering
One of the primary risks associated with security questions stems from the ease of information discovery. Modern digital landscapes, particularly social media platforms, provide unprecedented access to personal details that can be exploited by malicious actors. According to Cybersecurity Ventures, social engineering techniques have become increasingly sophisticated, allowing attackers to gather seemingly innocuous personal information that could potentially answer security questions.
For example, a security question asking "What high school did you attend?" could be easily answered by someone who finds this information through public social media profiles, yearbooks, or online alumni networks. Similarly, questions like "What is your mother's maiden name?" can often be discovered through genealogy websites, public records, or even casual conversations.
Predictability and Limited Answer Variations
Security questions frequently suffer from inherent predictability. Research from NIST reveals that many security questions have limited answer variations, making them vulnerable to systematic guessing attacks. Attackers can develop algorithms that generate probable answers based on statistical likelihood and common responses.
Consider these problematic security question patterns:
- Questions with geographically or culturally limited answers
- Questions that have statistically predictable response ranges
- Questions requiring simple, short answers that can be systematically tested
A hacker might use computational methods to generate hundreds or thousands of potential answers to a security question, dramatically increasing their chances of successful unauthorized access. The computational power available today makes such brute-force approaches increasingly feasible.
Technological Vulnerabilities and Future Threats
Emerging technological trends introduce even more complex security challenges. The World Economic Forum's Global Cybersecurity Outlook highlights the growing risk of "Harvest Now, Decrypt Later" attacks, where malicious actors collect encrypted data with the intention of decrypting it once advanced computing technologies become available.
With the potential advent of quantum computing, traditional security mechanisms like security questions become even more precarious. The average cost of a data breach has reached $4.4 million, underscoring the critical importance of evolving authentication methods beyond simple question-and-answer formats.
Modern cybersecurity experts recommend moving towards more dynamic authentication strategies such as:
- Multi-factor authentication
- Biometric verification
- Time-limited access tokens
- Behavioral authentication techniques
While security questions might seem convenient, they represent a legacy authentication method increasingly misaligned with contemporary digital security requirements. Organizations and individuals must recognize these inherent risks and proactively adopt more sophisticated, resilient verification approaches that can withstand evolving technological threats.
Better Ways to Secure Your Accounts
Securing digital accounts requires a comprehensive and adaptive approach that goes beyond traditional security questions. Modern cybersecurity demands sophisticated strategies that leverage advanced technologies and proactive protection mechanisms to safeguard sensitive information.
Multi-Factor Authentication: A Robust Defense Strategy
Multi-factor authentication (MFA) represents a significant advancement in account security. According to Okta, combining multiple verification methods creates a robust defense against unauthorized access. MFA typically involves three primary authentication factors:
- Something You Know: Passwords or security questions
- Something You Have: Mobile devices or hardware tokens
- Something You Are: Biometric data like fingerprints or facial recognition
By requiring two or more of these factors, MFA dramatically reduces the likelihood of successful unauthorized access. Even if an attacker discovers one authentication element, they would still need additional verification to breach the account.
Advanced Password Management Techniques
NIST guidelines for 2025 recommend reimagining password creation and management. Key recommendations include:
- Creating longer, more complex passwords
- Eliminating mandatory periodic password changes
- Implementing secure password checking against known compromise databases
- Using unique passwords for each account
Password managers offer an excellent solution, generating and securely storing complex, unique passwords across multiple platforms. These tools encrypt password databases and often include additional security features like two-factor authentication and breach monitoring.
Proactive Account Protection Strategies
Beyond authentication methods, comprehensive account security involves ongoing vigilance and strategic protective measures. Cybersecurity experts recommend several advanced techniques:
- Regular security audits of account access and permissions
- Monitoring for potential data breaches
- Using virtual private networks (VPNs) for secure internet connections
- Enabling login notifications and suspicious activity alerts
- Implementing hardware security keys for critical accounts
Additionally, organizations should adopt zero-trust security models that continuously verify user identities and limit access permissions. This approach assumes no inherent trust, requiring repeated authentication and minimal access privileges.
The landscape of digital security is continuously evolving. What works today might become vulnerable tomorrow. Staying informed about emerging technologies, understanding potential risks, and adopting a proactive, layered security approach are crucial for protecting personal and professional digital assets.
Ultimately, effective account security is not about implementing a single solution but creating a comprehensive, adaptive strategy that combines technological tools, user awareness, and continuous learning.
Security Question Examples to Avoid
Not all security questions provide equal protection. Some questions are inherently weak, exposing users to significant risks of unauthorized access. Understanding which security questions compromise your digital safety is crucial for maintaining robust account protection.
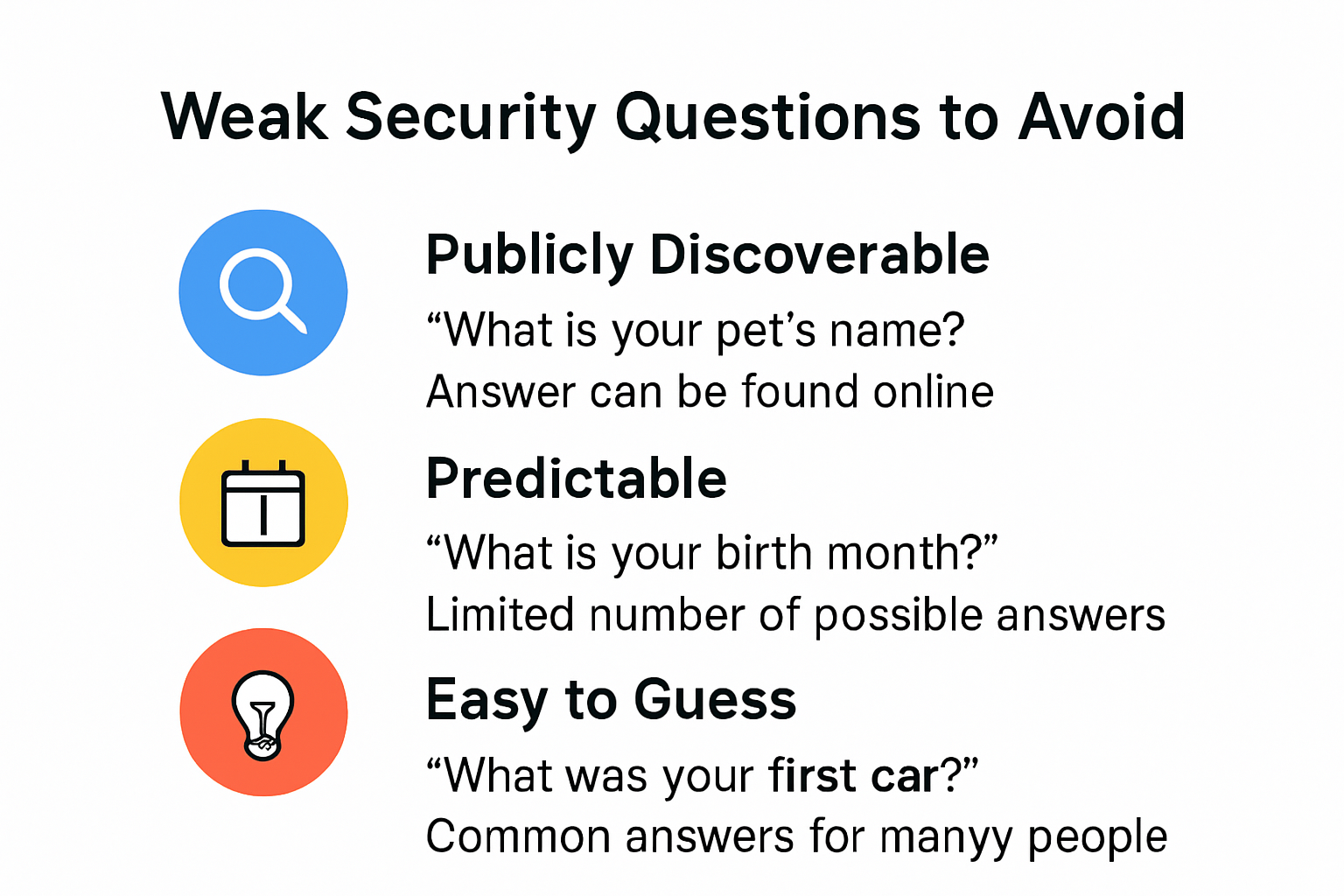
Publicly Discoverable Personal Information
Security questions that rely on information easily found through public sources represent a major vulnerability. According to Optimal IDM, questions that can be quickly discovered through social media, public records, or casual conversations should be strictly avoided.
Examples of dangerous security questions include:
- "What is your mother's maiden name?"
- "Where were you born?"
- "What high school did you attend?"
- "What is your hometown?"
- "What is your pet's name?"
These questions seem personal but are often readily available through online profiles, genealogy websites, or casual conversations. A determined attacker could potentially gather this information through minimal social engineering or basic internet research.
Overly Simple and Predictable Questions
Okta's security guidelines emphasize the risks of questions with limited, predictable answer ranges. Questions that can be systematically guessed or have statistically common responses dramatically increase the likelihood of unauthorized access.
Poor security question examples that should be avoided:
- "What is your favorite color?"
- "What is your favorite food?"
- "What is your favorite movie?"
- "What is your favorite sports team?"
These questions suffer from multiple security weaknesses:
- High probability of guessing
- Potential for multiple correct answers
- Answers that might change over time
- Responses that can be easily learned through casual interaction
Dynamic Personal Questions with Limited Variability
Some security questions appear sophisticated but still contain inherent vulnerabilities. Questions that seem unique but have limited answer variations can be systematically compromised by attackers using computational techniques.
Problematic question categories include:
- Questions with culturally limited answer pools
- Questions requiring short, simple responses
- Questions with statistically predictable answer patterns
- Questions that can be brute-forced through algorithmic guessing
Cybersecurity experts recommend creating unique, complex security questions that:
- Have highly personalized answers
- Are not easily discoverable online
- Remain consistent over extended periods
- Cannot be systematically guessed
Instead of traditional security questions, modern authentication strategies increasingly recommend:
- Multi-factor authentication
- Biometric verification
- Dynamic, time-limited access tokens
- Behavioral authentication techniques
Protecting your digital identity requires continuous adaptation. What seems secure today might become vulnerable tomorrow. Regularly reviewing and updating your authentication methods is crucial in maintaining robust digital security.
Frequently Asked Questions
What are security questions?
Security questions are personal queries used to verify a user's identity, typically during account recovery or password resets. They serve as an extra layer of protection beyond passwords.
Why are security questions considered risky?
Security questions can be risky because many rely on information that can be easily discovered through social media or public records, making them vulnerable to unauthorized access.
How can I create effective security questions?
To create effective security questions, choose queries that have specific, memorable answers which are not easily guessable or discoverable by others. Avoid common or easily searchable topics.
What alternatives are there to using security questions?
Alternatives to security questions include multi-factor authentication (MFA), biometric verification, and using password managers that improve overall account security.
Strengthen Your Security with Skypher
As you’ve learned about the vulnerabilities of traditional security questions, it’s crucial to enhance your cybersecurity strategy. Modern threats require advanced protections beyond outdated methods. Skypher offers the perfect solution to fill this gap in your security protocols. Our AI-driven Questionnaire Automation Tool streamlines the process of managing security assessments, allowing organizations to respond quickly and confidently to risks.

Imagine a scenario where your team can produce security reviews significantly faster while ensuring higher accuracy – all in real time. With integrations into over 40 third-party risk management platforms, you can regain control of your security processes, automate tedious tasks, and fortify your organizational resilience against breaches. Don’t let outdated security techniques hold you back. Enhance your cybersecurity posture today by visiting Skypher and discover how our solutions can help you tackle modern security challenges with confidence!
