Every year, cyber threats get smarter while businesses scramble to keep up. Shockingly, over 80 percent of organizations have reported at least one data breach in the past year. Most people think layering on more technology will keep information safe, but ISO 27001 flips that idea on its head by focusing just as much on people and processes as on gadgets and code.
Table of Contents
- What Is Framework Iso 27001 And Why Use It
- Core Components Of The Iso 27001 Framework
- Steps To Successfully Implement Iso 27001
- Comparing Iso 27001 To Other Security Frameworks
Quick Summary
| Takeaway | Explanation |
|---|---|
| ISO 27001 is essential for information security | This framework provides a systematic method for managing sensitive information and mitigating risks effectively. |
| Continuous improvement is mandatory | Organizations must regularly evaluate and update their security practices to adapt to emerging threats. |
| Conduct thorough risk assessments | Identifying and prioritizing risks is crucial for developing effective security controls and strategies. |
| Training and awareness are vital | Ensuring staff is trained on information security policies fosters a culture of security throughout the organization. |
| Select the right framework based on needs | Organizations should evaluate their specific context, maturity, and regulatory requirements when choosing a security framework. |
What Is Framework ISO 27001 and Why Use It
Information security has become a critical concern for organizations worldwide. The framework ISO 27001 provides a systematic approach to managing and protecting sensitive information assets in an increasingly complex digital environment.Understanding the Core Principles of ISO 27001
ISO/IEC 27001 is an internationally recognized standard that establishes a comprehensive methodology for information security management. At its core, the framework provides organizations with a structured approach to identifying, managing, and mitigating information security risks.
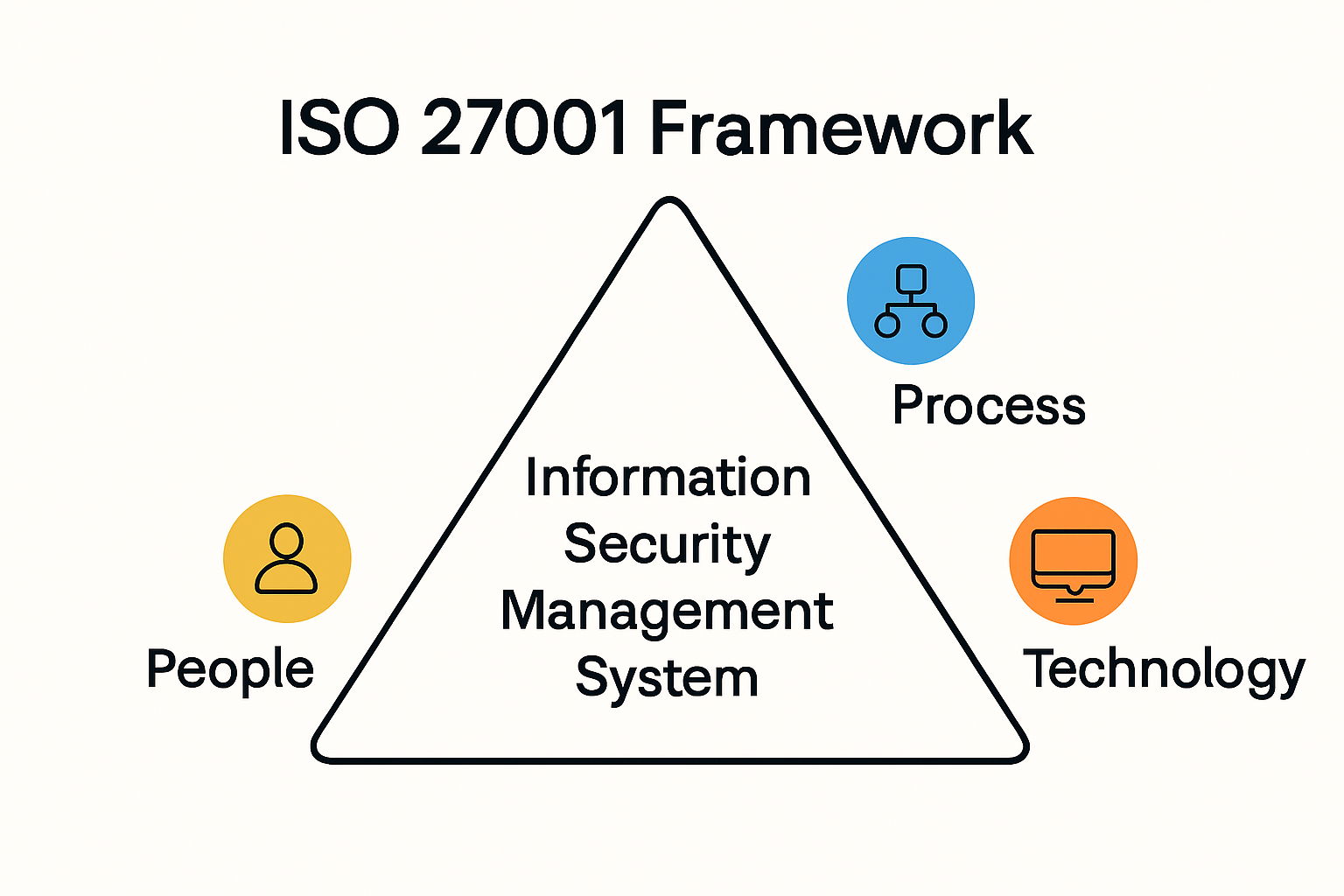
The standard goes beyond simple technical controls. It requires organizations to develop a holistic information security management system (ISMS) that addresses people, processes, and technology. According to research from MDPI, implementing ISO 27001 enables organizations to systematically examine information security risks and design comprehensive security controls that adapt to evolving threats.
Key Benefits of Adopting the Framework
Organizations choose the framework ISO 27001 for several compelling reasons:
- Risk Management: Provides a structured approach to identifying and mitigating information security risks
- Compliance: Helps meet legal and regulatory requirements across various industries
- Credibility: Demonstrates a commitment to protecting sensitive information to stakeholders and customers
The framework offers more than just a checklist of security measures. It creates a dynamic system that continuously assesses and improves an organization's information security posture. By implementing ISO 27001, companies can develop a proactive approach to managing security challenges.
Implementation and Organizational Impact
Successful adoption of the framework requires a comprehensive strategy. Organizations must conduct thorough risk assessments, develop robust security policies, and create mechanisms for ongoing monitoring and improvement. The process involves multiple stages, including initial assessment, control implementation, and continuous evaluation.
Unlike static security approaches, ISO 27001 emphasizes the importance of continuous improvement. It requires organizations to regularly review and update their information security practices, ensuring they remain effective against emerging threats. This dynamic approach sets the framework apart from more rigid security models.
For businesses operating in sensitive sectors like finance, healthcare, and technology, the framework ISO 27001 is not just a recommendation but a critical component of maintaining organizational resilience. It provides a proven methodology for protecting valuable information assets and building trust with stakeholders.
Ultimately, ISO 27001 represents more than a technical standard. It is a strategic approach to information security that integrates risk management, technological controls, and organizational culture into a cohesive system of protection and continuous improvement.
Core Components of the ISO 27001 Framework
The ISO 27001 framework represents a comprehensive approach to information security management, built on a series of interconnected components that work together to create a robust protective system. Understanding these core components is crucial for organizations seeking to implement an effective information security strategy.
Organizational Context and Risk Assessment
At the heart of the ISO 27001 framework lies a critical process of understanding organizational context and conducting comprehensive risk assessments. According to NIST Special Publication 800-171, this component involves a detailed examination of an organization's internal and external environments that might impact information security.
The risk assessment process requires organizations to:
- Identify Information Assets: Catalog and classify all critical information resources
- Evaluate Potential Threats: Analyze potential vulnerabilities and potential impact of security breaches
- Determine Risk Levels: Quantify and prioritize risks based on likelihood and potential damage

Information Security Management System (ISMS) Implementation
NIST SP 800-53 highlights the critical nature of establishing a comprehensive Information Security Management System (ISMS). This systematic approach goes beyond mere technical controls, integrating people, processes, and technology into a cohesive security framework.
Key elements of an effective ISMS include:
- Policy Development: Creating clear, comprehensive information security policies
- Control Implementation: Designing and deploying specific security controls
- Continuous Monitoring: Establishing mechanisms for ongoing security assessment
Performance Evaluation and Continuous Improvement
The ISO 27001 framework is not a static model but a dynamic system of continuous improvement. Organizations must regularly evaluate their information security performance, conduct internal audits, and make necessary adjustments to their security approach.
This cyclical process involves:
- Regular Audits: Systematic reviews of security controls and their effectiveness
- Management Reviews: Senior leadership assessment of the overall security strategy
- Corrective Action: Implementing improvements based on audit findings
The framework demands a proactive approach to information security. Rather than treating security as a one-time implementation, ISO 27001 requires organizations to view it as an ongoing process of adaptation and refinement.
For businesses operating in complex technological environments, the framework provides a structured methodology to manage information security risks. It offers a holistic approach that considers technological, human, and procedural aspects of security management.
By integrating these core components, organizations can develop a resilient information security strategy that not only protects against current threats but also remains adaptable to emerging challenges in the digital landscape.
To help clarify the interconnected components of the ISO 27001 framework, the following table summarizes their key roles:
| Core Component | Key Activities & Focus |
|---|---|
| Organizational Context & Risk Assessment | Identify assets, evaluate threats, determine risk levels |
| ISMS Implementation | Develop policies, implement controls, monitor security |
| Performance Evaluation & Continuous Improvement | Conduct audits, management reviews, apply corrective actions |
Steps to Successfully Implement ISO 27001
Implementing the ISO 27001 framework requires a strategic and methodical approach. Organizations must navigate a complex landscape of technical, procedural, and cultural challenges to successfully establish an effective Information Security Management System (ISMS).
Initial Planning and Organizational Preparation
Successful implementation begins with comprehensive preparation. According to ISACA, the first critical step involves creating a detailed inventory of information assets and conducting thorough risk assessments.
Key initial activities include:
- Leadership Commitment: Securing top management support and allocating necessary resources
- Asset Identification: Cataloging all information assets across the organization
- Scope Definition: Clearly defining the boundaries of the Information Security Management System
This preparatory phase requires organizations to take a holistic view of their information ecosystem, understanding the interconnections between different systems, processes, and data repositories.
Risk Assessment and Control Implementation
SANS Institute research emphasizes the critical nature of comprehensive risk assessment and control implementation. Organizations must develop a systematic approach to identifying, analyzing, and mitigating information security risks.
The risk management process involves:
- Risk Identification: Mapping potential threats and vulnerabilities
- Risk Analysis: Evaluating the potential impact and likelihood of identified risks
- Control Selection: Choosing appropriate security controls from ISO 27001's Annex A
- Risk Treatment: Developing strategies to address and mitigate identified risks
This stage requires a nuanced understanding of the organization's unique risk landscape, moving beyond generic security approaches to develop tailored protection strategies.
Training, Documentation, and Continuous Improvement
Implementation is not a one-time event but an ongoing process of refinement. The SANS Institute highlights the importance of staff training and continuous awareness as critical components of successful ISO 27001 implementation.
Key focus areas include:
- Comprehensive Documentation: Creating clear, detailed security policies and procedures
- Staff Training: Developing ongoing security awareness programs
- Internal Audits: Regularly assessing the effectiveness of the ISMS
- Management Reviews: Conducting periodic evaluations of the overall security strategy
Successful implementation requires more than technical controls. It demands a cultural shift that embeds information security principles into every aspect of organizational operations.
Organizations must view ISO 27001 implementation as a journey of continuous improvement. The framework provides a structured approach, but true security comes from ongoing commitment, adaptability, and a proactive stance toward emerging threats.
By following these steps and maintaining a flexible, forward-thinking approach, organizations can develop a robust information security management system that protects critical assets and builds stakeholder confidence.
The ISO 27001 implementation process is made up of several key stages. The following table outlines each stage and its main activities:
| Implementation Stage | Main Activities |
|---|---|
| Initial Planning | Leadership commitment, asset identification, scope definition |
| Risk Assessment & Controls | Identify and analyze risks, select and implement controls, risk treatment |
| Training & Continuous Improvement | Documentation, staff training, internal audits, management reviews |
Comparing ISO 27001 to Other Security Frameworks
Information security frameworks provide critical guidance for organizations seeking to protect their digital assets. ISO 27001 stands out as a comprehensive approach, but understanding its relationship to other security frameworks helps organizations make informed decisions about their security strategies.
ISO 27001 vs NIST Frameworks
Security Compass research highlights significant differences between ISO 27001 and NIST frameworks. While both aim to enhance information security, they approach risk management from distinct perspectives.
Key comparative aspects include:
- Scope: ISO 27001 is globally applicable across industries, whereas NIST 800-53 primarily targets U.S. government agencies and federal contractors
- Flexibility: ISO 27001 offers a risk-based approach allowing customization, while NIST provides more prescriptive control measures
- Certification: ISO 27001 provides formal certification, NIST frameworks offer guidance without official certification
To make the differences between ISO 27001 and NIST frameworks easy to compare, the following table summarizes their main characteristics:
| Aspect | ISO 27001 | NIST Frameworks |
|---|---|---|
| Scope | Global, all industries | Primarily US government & contractors |
| Approach | Risk-based, customizable | Prescriptive controls |
| Certification | Formal certification available | No official certification |
Shared Principles and Unique Characteristics
Eden Data research reveals important similarities and differences among security frameworks. Despite originating from different governing bodies, these frameworks share fundamental cybersecurity principles.
Common characteristics include:
- Risk Management: Both emphasize systematic risk identification and mitigation
- Holistic Approach: Focus on comprehensive security strategies beyond technical controls
- Scalability: Designed to accommodate organizations of varying sizes and complexity
Practical Considerations for Framework Selection
InfoTrust analysis suggests organizations should consider multiple factors when selecting a security framework. The choice depends on specific organizational needs, regulatory requirements, and operational context.
Critical selection criteria include:
- Regulatory Compliance: Understand industry-specific security requirements
- Organizational Maturity: Assess current security capabilities and implementation readiness
- Resource Availability: Evaluate the resources required for framework adoption
While ISO 27001 provides a robust, internationally recognized standard, it is not a one-size-fits-all solution. Organizations must carefully evaluate their unique security landscape, considering factors such as industry regulations, technological infrastructure, and specific risk profiles.
The most effective approach often involves understanding multiple frameworks and developing a tailored strategy that combines best practices from different standards. This hybrid approach allows organizations to create a more resilient and adaptive information security management system.
Ultimately, the goal is not just to comply with a specific framework but to develop a comprehensive, dynamic approach to information security that protects critical assets and builds stakeholder confidence.
Frequently Asked Questions
What is ISO 27001?
ISO 27001 is an internationally recognized standard that provides a systematic approach for managing and protecting sensitive information assets through an Information Security Management System (ISMS).
Why should organizations adopt ISO 27001?
Organizations adopt ISO 27001 to effectively manage information security risks, ensure compliance with legal requirements, and demonstrate their commitment to protecting sensitive information to stakeholders and customers.
What are the key steps to implement ISO 27001?
Key steps to implement ISO 27001 include initial planning and organizational preparation, risk assessment and control implementation, and ongoing training and continuous improvement of the information security practices.
How does ISO 27001 compare to other security frameworks?
ISO 27001 offers a risk-based, customizable approach to information security suitable across various industries, whereas NIST frameworks are primarily more prescriptive and focused on U.S. government entities. ISO 27001 also provides formal certification, unlike NIST frameworks.
Bring ISO 27001 Compliance and Security Questionnaire Automation Together
Achieving and maintaining ISO 27001 compliance means dealing with endless security questionnaires, complex documentation, and the pressure to prove your security controls are reliable. Many organizations struggle with manual processes that eat up valuable time, delay projects, and add stress to growing teams. The article highlighted critical steps like risk assessment, managing controls, and continuous improvement, but the real challenge comes when you have to answer detailed security questionnaires for clients and regulators.

Skypher makes this easier from day one. Our AI Questionnaire Automation Tool lets you answer security reviews and ISO 27001-related questionnaires fast and with accuracy. Teams collaborate in real time, automate repetitive tasks, and integrate evidence from existing tools to reduce friction and cut delays. Want to eliminate slowdowns in your ISO 27001 process and win trust with every response? Visit Skypher now and see how automation supports your compliance goals today.
