Data breaches cost organizations an average of $4.45 million each, and that number is climbing every year. As cyber threats grow more complex, clear strategies for managing risks and complying with regulations are not just helpful but crucial. Understanding how Governance, Risk Management, and Compliance work together shapes the foundation of stronger, more resilient IT security systems that protect both data and reputation.
Table of Contents
- Defining GRC IT Security And Key Concepts
- Core Frameworks, Standards, And Models Used
- Roles, Responsibilities, And Compliance Obligations
- Automation Tools For GRC In IT Security
- Common Challenges And Risk Mitigation Strategies
Key Takeaways
| Point | Details |
|---|---|
| GRC Framework Importance | GRC IT Security integrates governance, risk management, and compliance to enhance cybersecurity strategies and regulatory alignment. |
| Core Frameworks | Organizations utilize frameworks like ISO/IEC 27001 and COBIT for structured risk management and IT governance. |
| Role of Automation | Automation tools in GRC streamline processes, enhance compliance, and enable proactive risk management through real-time assessments. |
| Addressing Challenges | Organizations must foster interdepartmental communication and adopt adaptable frameworks to effectively navigate GRC implementation challenges. |
Defining GRC IT Security and Key Concepts
Governance, Risk Management, and Compliance (GRC) in IT security represents a strategic framework that enables organizations to effectively manage technological risks while maintaining regulatory alignment. According to research from IBM, GRC integrates multiple critical organizational processes to protect digital assets and ensure comprehensive security oversight.
At its core, GRC IT Security encompasses three fundamental components: governance (establishing security policies and structures), risk management (identifying and mitigating potential technological threats), and compliance (ensuring adherence to industry regulations and standards). Organizations leverage GRC frameworks to create systematic approaches that transform cybersecurity from reactive defense to proactive strategy.
Key objectives of GRC IT Security include:
- Developing comprehensive security policies
- Identifying and quantifying potential technological risks
- Implementing robust control mechanisms
- Ensuring continuous regulatory compliance
- Creating transparent reporting structures
For deeper insights into these concepts, explore our guide on understanding the GRC framework, which provides a comprehensive breakdown of how these strategies protect modern digital infrastructures.
Core Frameworks, Standards, and Models Used
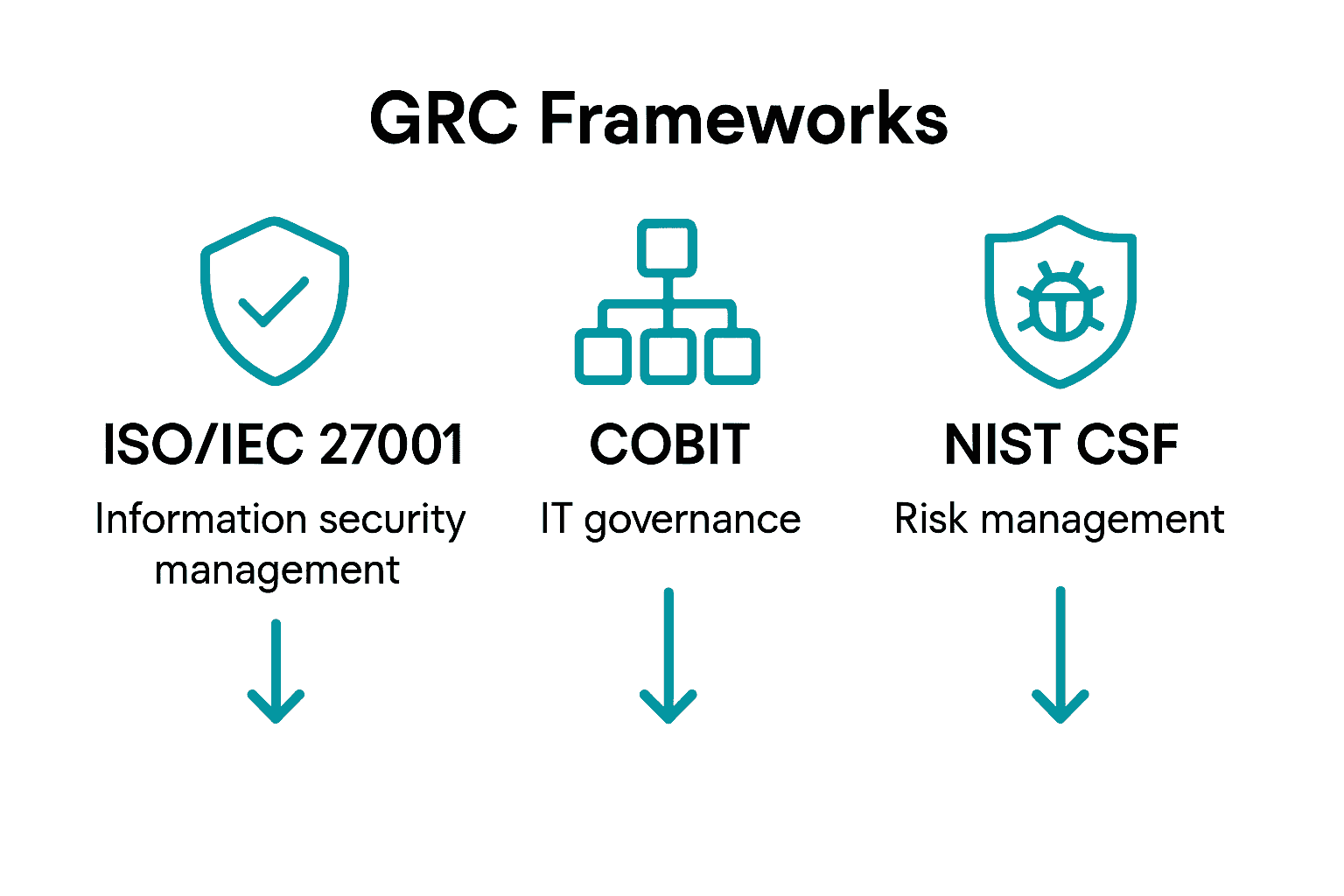
In the realm of GRC IT Security, several robust frameworks and standards have emerged to guide organizations in managing technological risks and maintaining comprehensive security protocols. ISO/IEC 27001 stands out as a critical international standard that provides comprehensive guidelines for establishing and maintaining an information security management system (ISMS), enabling organizations to systematically approach cybersecurity challenges.
COBIT (Control Objectives for Information and Related Technologies) represents another pivotal framework in the GRC landscape. According to ISACA's documentation, this framework offers a structured approach to IT management and governance, defining precise processes with clear inputs, outputs, activities, objectives, and performance measurement mechanisms.
Key frameworks organizations typically leverage include:
Here's a comparison of major GRC IT Security frameworks and their core focus:
| Framework | Primary Focus | Typical Use Case |
|---|---|---|
| ISO/IEC 27001 | Information Security<br>Management | Building an ISMS<br>Regulatory alignment |
| COBIT | IT Governance<br>Process Control | IT management<br>Enterprise oversight |
| NIST CSF | Risk Management<br>Cyber Resilience | Critical infrastructure<br>Risk assessment |
| COSO ERM | Enterprise Risk<br>Management | Strategic risk<br>Organization-wide controls |
| ITIL | IT Service<br>Management | Service delivery<br>Process improvement |
- ISO/IEC 27001: Information Security Management Standard
- COBIT: IT Governance and Management Framework
- NIST Cybersecurity Framework: Risk Management Guidelines
- COSO ERM: Enterprise Risk Management Model
- ITIL: IT Service Management Best Practices
These frameworks provide organizations with structured methodologies to assess, manage, and mitigate technological risks while ensuring compliance and maintaining robust security infrastructures.
 Learn more about cybersecurity strategies in our comprehensive guide, which explores how these frameworks can be effectively implemented.
Learn more about cybersecurity strategies in our comprehensive guide, which explores how these frameworks can be effectively implemented.
Roles, Responsibilities, and Compliance Obligations
In the complex ecosystem of GRC IT Security, professionals play critical roles in developing and maintaining robust organizational security frameworks. According to research from TrustCloud, GRC professionals are tasked with developing governance frameworks, conducting comprehensive risk assessments, and ensuring continuous compliance across technological domains.
Key roles in the GRC IT Security landscape include Chief Information Security Officers (CISOs), Risk Managers, Compliance Officers, and IT Security Analysts. Each role carries distinct responsibilities that collectively create a comprehensive security strategy. These professionals collaborate to identify potential vulnerabilities, implement protective measures, and maintain ongoing monitoring of organizational technological ecosystems.
Critical responsibilities within GRC IT Security encompass:
- Developing and implementing comprehensive security policies
- Conducting regular risk assessments and vulnerability analyses
- Monitoring regulatory compliance requirements
- Creating incident response and mitigation strategies
- Ensuring transparent reporting and documentation
For professionals looking to excel in this dynamic field, explore our guide with essential tips for GRC analysts, which provides insights into navigating the complex landscape of IT security governance and compliance.
Automation Tools for GRC in IT Security
In the rapidly evolving landscape of cybersecurity, automation tools have become critical components for effective Governance, Risk, and Compliance (GRC) strategies. According to research from TrustCloud, automation significantly reduces manual workloads, minimizes human error, and enables compliance teams to focus on more strategic initiatives.
The emergence of advanced automation technologies has transformed traditional GRC approaches. Cutting-edge tools now leverage artificial intelligence and machine learning to streamline complex compliance processes, conduct real-time risk assessments, and provide comprehensive monitoring capabilities. These technologies enable organizations to adapt quickly to changing regulatory landscapes and emerging security threats.
Key capabilities of modern GRC automation tools include:
- Continuous compliance monitoring
- Automated risk assessment and scoring
- Real-time vulnerability detection
- Streamlined reporting and documentation
- Integration with existing security infrastructure
- Predictive threat analysis
For organizations looking to understand the transformative potential of automation in security processes, explore our insights on security questionnaire automation, which demonstrates how technological solutions can dramatically improve organizational efficiency and security posture.
Common Challenges and Risk Mitigation Strategies
Navigating the complex landscape of GRC IT Security presents numerous challenges for organizations seeking to establish robust cybersecurity frameworks. According to research from Auxilion, common implementation challenges include integration complexity, communication barriers, and resource constraints that can significantly impede the development of comprehensive security processes.
Risk mitigation requires a strategic approach that addresses potential pitfalls head-on. Organizations must be cautious of common mistakes, such as maintaining siloed departmental approaches, over-relying on technology without establishing proper underlying processes, and attempting to implement too many changes simultaneously. These missteps can lead to overwhelming complexity and reduced effectiveness in cybersecurity management.
Key strategies for overcoming GRC IT Security challenges include:
- Establishing cross-departmental communication channels
- Developing comprehensive yet flexible security frameworks
- Implementing phased risk management approaches
- Investing in continuous employee training
- Creating adaptive and scalable security protocols
- Regularly conducting comprehensive risk assessments
For organizations looking to enhance their vendor risk management strategies, explore our comprehensive guide to third-party vendor risk assessment, which provides actionable insights into mitigating external security risks effectively.
Enhance Your GRC IT Security Strategy with Smarter Automation
Navigating the complexities of Governance, Risk, and Compliance in IT security demands efficient tools that reduce manual effort while improving accuracy. The challenges highlighted in the article around risk assessments, continuous compliance, and real-time monitoring can slow your team down and increase pressure on resources. Skypher offers a powerful solution with its AI Questionnaire Automation Tool designed specifically for organizations facing intricate security reviews. Our platform supports numerous formats, integrates with over 40 leading third-party risk management systems, and enables your team to complete even hundreds of questions in minutes with real-time collaboration features.

Don’t let cumbersome security questionnaires hinder your compliance momentum. Experience how automating responses, managing risk documentation effectively, and maintaining a customizable Trust Center transforms your GRC processes today. Visit Skypher to discover why medium to large enterprises across tech and finance trust us to streamline their security workflows. Explore how our AI Questionnaire Automation Tool and Collaboration and Real-Time Integration capabilities empower your cybersecurity efforts with proven speed and precision.
Frequently Asked Questions
What are the three main components of GRC IT Security?
GRC IT Security comprises three fundamental components: governance, which involves establishing security policies; risk management, which focuses on identifying and mitigating technological threats; and compliance, ensuring adherence to industry regulations.
How can organizations implement effective GRC frameworks?
Organizations can implement effective GRC frameworks by leveraging structured methodologies like ISO/IEC 27001 for information security, COBIT for IT governance, and other standards that guide risk assessment and management processes.
What roles are essential within GRC IT Security?
Key roles within GRC IT Security include Chief Information Security Officers (CISOs), Risk Managers, Compliance Officers, and IT Security Analysts, each responsible for various aspects of governance, risk management, and compliance.
What are the benefits of using automation tools in GRC IT Security?
Automation tools improve GRC IT Security by reducing manual workloads, minimizing human error, conducting real-time risk assessments, and enabling continuous compliance monitoring, thereby enhancing overall security efficiency and adaptability.
