HIPAA compliance is undergoing a significant transformation, with organizations facing stricter standards than ever before. By 2025, nearly 85 percent of healthcare entities will need to adopt advanced security measures to protect patient health information. But here’s the twist: many still view compliance as a mere checkbox exercise. In reality, approaching HIPAA compliance strategically can enhance operational efficiency and build stronger patient trust, leading to long-term success.
Table of Contents
- Key Requirements For HIPAA Compliance 2025
- Steps To Achieve And Maintain HIPAA Compliance
- Essential Tools And Resources For Success
Quick Summary
| Takeaway | Explanation |
|---|---|
| Comprehensive IT Asset Management is Crucial | Organizations must maintain a detailed IT asset inventory and conduct risk assessments to identify vulnerabilities and enhance data protection. |
| Advanced Data Protection Measures are Required | Implement full encryption of protected health information (PHI), multi-factor authentication, and advanced threat detection systems to ensure strong data security. |
| Meticulous Documentation is Essential | Keeping thorough records of compliance efforts, including administrative procedures and training logs, is vital for demonstrating commitment to patient data protection and preparedness for audits. |
| Vendor Management is Key | Maintain strong Business Associate Agreements (BAAs) to ensure vendors comply with HIPAA standards, with clear definitions of responsibilities and mechanisms for contract termination if needed. |
| Invest in Compliance and Security Tools | Utilize advanced compliance management software and identity access management solutions to streamline HIPAA adherence and protect sensitive health information effectively. |
Key Requirements for HIPAA Compliance 2025
HIPAA compliance continues to evolve, demanding more sophisticated approaches to protecting patient health information. Organizations must stay ahead of emerging technological and regulatory challenges to maintain comprehensive security and privacy standards.
Comprehensive IT Asset Management and Risk Assessment
Effective HIPAA compliance in 2025 starts with robust IT infrastructure management. Covered entities must develop and maintain a detailed information technology asset inventory that provides a complete picture of their digital ecosystem. Research from the Health and Human Services Department emphasizes the critical nature of comprehensive asset tracking.
Key requirements include:
- Conducting comprehensive network mapping
- Updating asset inventories at least every 12 months
- Performing detailed risk assessments that identify potential vulnerabilities
- Implementing proactive security measures based on assessment findings
Organizations must go beyond simple inventory lists. The goal is to create a dynamic understanding of how protected health information (PHI) moves through their systems, identifying potential points of vulnerability and implementing targeted security protocols.
Advanced Data Protection and Authentication Protocols
Data security has become increasingly complex, requiring multi-layered protection strategies. Cybersecurity experts recommend implementing comprehensive encryption and authentication measures that provide robust protection for sensitive health information.
Critical security requirements include:
- Full encryption of PHI both at rest and in transit
- Multi-factor authentication for all systems handling sensitive data
- Network segmentation to minimize potential breach impacts
- Advanced anti-malware and threat detection systems
The encryption requirement is particularly stringent. Organizations must ensure that every piece of protected health information is encrypted across all platforms, devices, and communication channels. This means protecting data during storage, transmission, and any intermediate processing stages.
Documentation and Compliance Tracking
Meticulous remains a cornerstone of HIPAA compliance. Organizations must maintain meticulous records that demonstrate their ongoing commitment to protecting patient information. Regulatory guidelines require comprehensive documentation of multiple compliance aspects.
Essential documentation elements include:
- Detailed administrative procedure logs
- Comprehensive workforce training records
- Systematic tracking of potential PHI breaches
- Clear documentation of employee compliance sanctions
- Thorough records of all patient privacy-related complaints
These documentation requirements are not mere bureaucratic exercises. They represent critical evidence of an organization's commitment to maintaining the highest standards of patient data protection. Each record serves as a potential defensive document in case of audits or potential legal challenges.
By embracing these key requirements, healthcare organizations can develop a proactive approach to HIPAA compliance that goes beyond minimal regulatory adherence. The focus is on creating a culture of continuous improvement and robust data protection that ultimately serves patient interests and maintains the highest standards of healthcare privacy.
Steps to Achieve and Maintain HIPAA Compliance
Successful HIPAA compliance is not a one-time achievement but a continuous process requiring strategic planning, systematic implementation, and ongoing monitoring. Healthcare organizations must develop a comprehensive approach that addresses multiple dimensions of regulatory requirements.
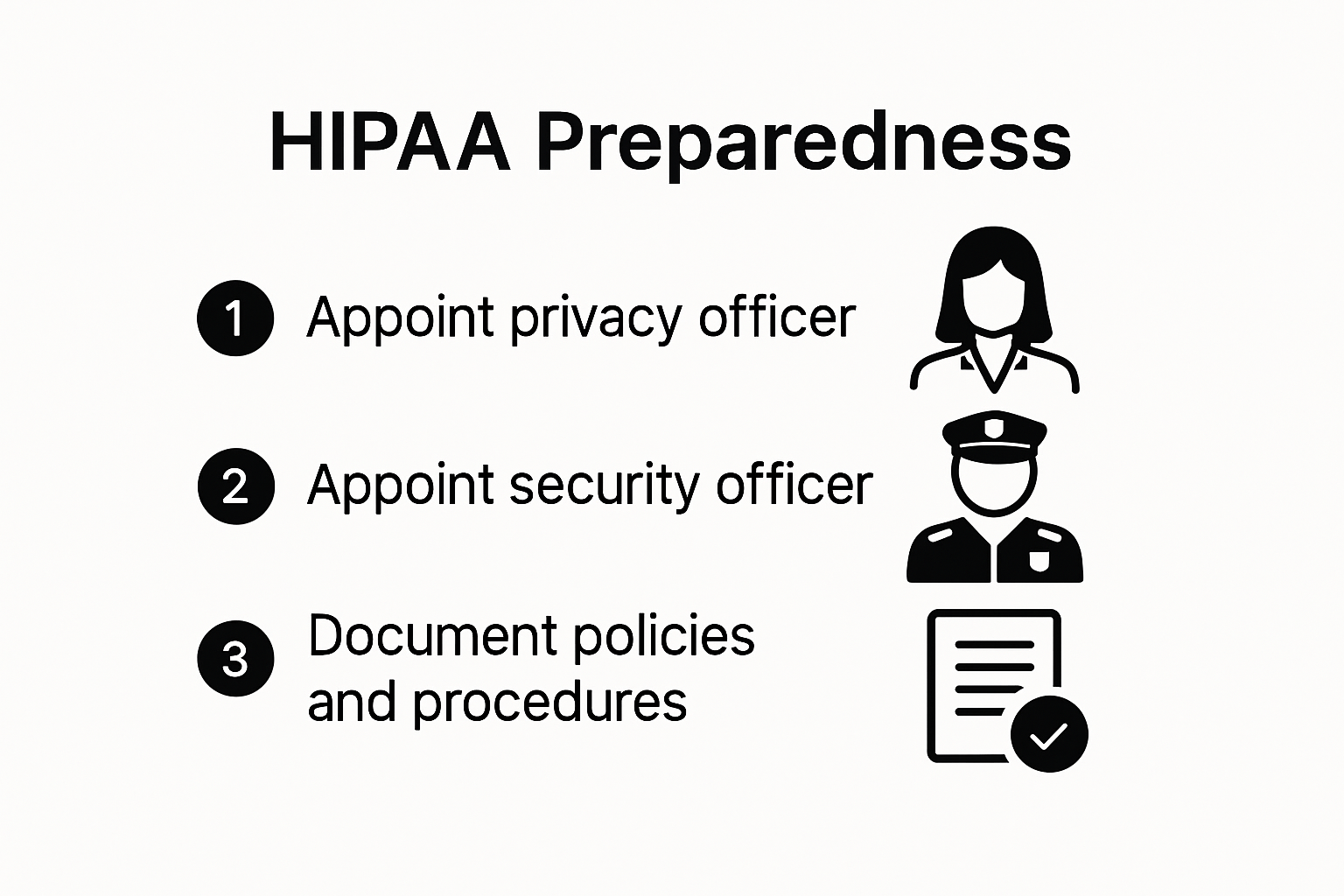
Foundational Organizational Preparedness
Establishing a solid compliance foundation begins with clear organizational structure and leadership commitment. HIPAA experts recommend appointing dedicated personnel responsible for privacy and security oversight. This typically involves creating two critical roles:
- HIPAA Privacy Officer: Responsible for developing and implementing privacy policies
- HIPAA Security Officer: Manages technical security infrastructure and protocols
These designated professionals must develop and maintain comprehensive written policies and procedures that explicitly outline how protected health information (PHI) will be handled, secured, and protected. The documentation should be living documents, regularly updated to reflect technological changes and emerging regulatory requirements.
Comprehensive Risk Assessment and Management
Cybersecurity research highlights the critical importance of conducting annual Security Risk Assessments (SRA). These assessments provide a systematic approach to identifying potential vulnerabilities in an organization's information management infrastructure.
Key components of an effective risk assessment include:
- Detailed mapping of all systems handling PHI
- Evaluation of current security controls
- Identification of potential technological and procedural vulnerabilities
- Assessment of cloud environments and remote access points
- Development of mitigation strategies for identified risks
Organizations must approach risk assessment as a dynamic process, recognizing that technological landscapes and threat environments continuously evolve. The goal is not just identifying risks but creating adaptive strategies that can respond to emerging challenges.
Vendor Management and Contractual Compliance
Modern healthcare ecosystems involve complex networks of vendors, partners, and service providers. Compliance experts emphasize the critical importance of managing these relationships through robust Business Associate Agreements (BAAs).
Effective vendor management requires:
- Annual review of all Business Associate Agreements
- Verification of each vendor's HIPAA compliance standards

- Comprehensive due diligence on third-party data handling practices
- Clear contractual definitions of PHI handling responsibilities
- Mechanisms for immediate contract termination if compliance standards are violated
These agreements are not merely administrative formalities but critical risk management tools. They ensure that every entity touching PHI understands and adheres to the same rigorous standards of protection and confidentiality.
Achieving and maintaining HIPAA compliance demands a holistic, proactive approach. It requires continuous education, technological adaptation, and an organizational culture committed to protecting patient information. By implementing these strategic steps, healthcare organizations can create robust frameworks that not only meet regulatory requirements but also build patient trust and demonstrate a genuine commitment to data privacy and security.
Essential Tools and Resources for Success
Navigating the complex landscape of HIPAA compliance requires sophisticated technological solutions and strategic resources. Healthcare organizations must invest in comprehensive tools that not only ensure regulatory adherence but also provide robust protection for patient health information.
Compliance Management and Monitoring Software
Compliance technology experts recommend implementing specialized software solutions designed to streamline HIPAA compliance efforts. These advanced platforms offer comprehensive features that transform complex regulatory requirements into manageable, actionable processes.
Key capabilities of effective compliance management tools include:
- Automated evidence collection for audit preparedness
- Real-time security posture monitoring
- Continuous risk assessment and gap identification
- Centralized policy enforcement and documentation
- Comprehensive reporting and tracking mechanisms
The most advanced platforms leverage artificial intelligence and machine learning to provide predictive insights, allowing organizations to address potential compliance vulnerabilities before they become critical issues.
Identity and Access Management Solutions
Cybersecurity research emphasizes the critical importance of robust identity management in protecting sensitive healthcare data. Modern access control systems go far beyond traditional username and password approaches, implementing multi-layered security protocols.
Essential identity management features include:
- Multi-factor authentication
- Role-based access controls
- Granular permission management
- Comprehensive user activity logging
- Automated access review and revocation processes
These solutions ensure that only authorized personnel can access specific types of protected health information, creating a dynamic and responsive security environment that adapts to organizational changes.
Comprehensive Security and Documentation Platforms
Technology integration specialists recommend holistic platforms that combine multiple compliance and security functions. These integrated solutions provide a unified approach to managing complex regulatory requirements.
Critical platform capabilities should include:
- Asset inventory and tracking systems
- Automated compliance documentation generation
- Continuous vulnerability scanning
- Incident response and management tools
- Secure communication and data transfer mechanisms
The most effective platforms offer seamless integration with existing healthcare information systems, ensuring minimal disruption to organizational workflows while maintaining the highest standards of data protection.
Successful HIPAA compliance in 2025 demands more than just technological tools. Organizations must cultivate a comprehensive approach that combines cutting-edge technology, strategic resource allocation, and a proactive organizational culture. By investing in sophisticated compliance and security solutions, healthcare providers can transform regulatory requirements from a challenging obligation into a strategic advantage that builds patient trust and demonstrates commitment to data protection.
Frequently Asked Questions
What are the key requirements for HIPAA compliance in 2025?
Organizations must focus on comprehensive IT asset management, advanced data protection protocols, and meticulous documentation of compliance efforts to meet the evolving HIPAA standards by 2025.
How can I achieve and maintain HIPAA compliance effectively?
Effective HIPAA compliance involves establishing a solid organizational structure, performing annual risk assessments, and managing vendor relationships through Business Associate Agreements (BAAs) to ensure compliance throughout the healthcare ecosystem.
Why is documentation essential for HIPAA compliance?
Meticulous documentation is critical as it provides evidence of an organization’s commitment to protecting patient data. It includes administrative logs, workforce training records, and tracking potential breaches to prepare for audits.
What tools can help streamline HIPAA compliance processes?
Investing in compliance management software, identity and access management solutions, and comprehensive security platforms can help organizations effectively manage their HIPAA compliance efforts and protect sensitive patient information.
Elevate Your HIPAA Compliance with Skypher
Navigating the complexities of HIPAA compliance can feel overwhelming. As highlighted in our latest article, organizations must adopt advanced data protection protocols and practice meticulous documentation to ensure they meet the evolving standards by 2025. Are your teams bogged down by burdensome security questionnaires and compliance processes?

With Skypher, you can transform this daunting task into a seamless experience. Our AI-Powered Questionnaire Automation Tool allows you to reduce the time needed for security reviews, leading to faster, more accurate responses. Imagine not only maintaining compliance with the latest HIPAA requirements but enhancing your operational productivity as well. Don't let compliance become a bottleneck in your workflow—act now to streamline your processes! Visit Skypher today to discover how our solutions can boost your compliance efforts and strengthen your cybersecurity posture.
