HIPAA enforcement is shaking up how software companies handle sensitive health data and the risks are bigger than most realize. A single violation can lead to fines as high as $1.5 million per year for each compliance category plus public trust is on the line. Yet despite all the attention on technical safeguards and encryption the biggest gap often comes from simple organizational missteps like incomplete risk assessments or weak staff training. Most software leaders never see it coming.
Table of Contents
- Understanding HIPAA Enforcement And Its Scope
- Common Compliance Challenges For B2B Software
- Best Practices To Reduce HIPAA Enforcement Risks
- Responding To HIPAA Investigations And Audits
Quick Summary
| Takeaway | Explanation |
|---|---|
| Prioritize HIPAA compliance | HIPAA compliance is essential for software companies handling patient data to avoid significant penalties and reputational damage. |
| Conduct regular risk assessments | Continuous risk assessments help identify vulnerabilities in data handling practices and ensure compliance with HIPAA regulations. |
| Implement robust technical safeguards | Advanced encryption, access controls, and logging systems are crucial for protecting electronic protected health information (ePHI). |
| Foster a culture of compliance | Ongoing training and awareness programs are necessary for staff to effectively manage and protect sensitive health information. |
| Prepare for audits and investigations | Companies should maintain comprehensive documentation and readiness to address potential HIPAA audits and investigations swiftly. |
Understanding HIPAA Enforcement and Its Scope
HIPAA enforcement represents a critical framework for protecting patient health information in the digital age. Software companies operating in healthcare technology must navigate a complex regulatory landscape that demands rigorous compliance and proactive security measures.
The Enforcement Mechanism of HIPAA
The U.S. Department of Health and Human Services Office for Civil Rights (HHS OCR) serves as the primary enforcement body for HIPAA regulations. Their approach goes beyond simple punitive actions, focusing on comprehensive compliance and patient data protection. When potential violations are identified, the OCR initiates a multi-step process that can include:
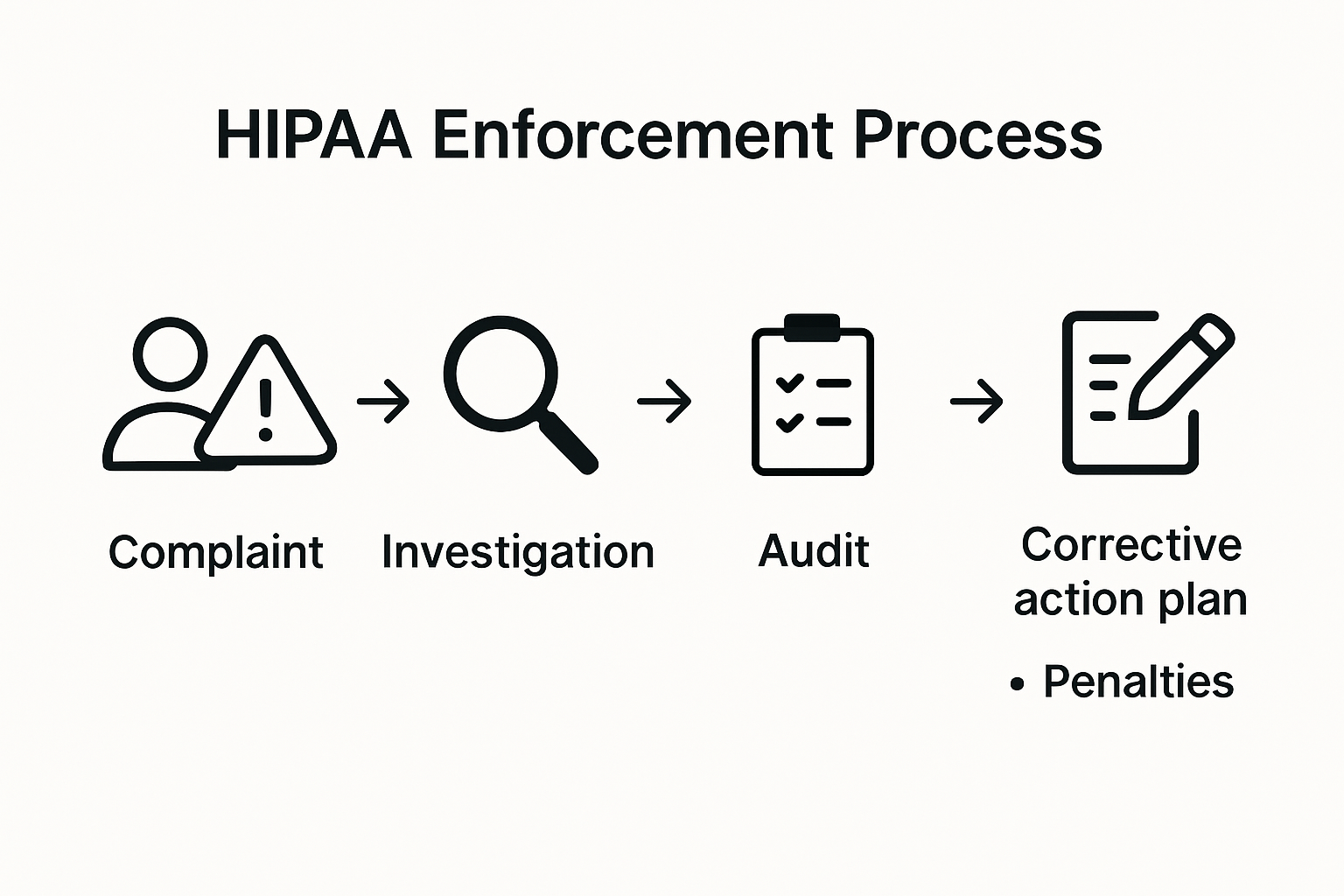
- Complaint Investigation: Responding to specific patient or organizational reports about potential privacy breaches
- Mandatory Audits: Systematic reviews of healthcare entities and their business associates
- Corrective Action Plans: Requiring organizations to implement specific improvements in their data handling processes
The HITECH Act significantly expanded HIPAA's enforcement capabilities, introducing more stringent penalties and broader investigative powers. This legislative update means software companies can no longer treat HIPAA compliance as an optional consideration.
Scope and Consequences of Non-Compliance
Research from the National Institutes of Health reveals that HIPAA enforcement has become increasingly sophisticated. The scope of enforcement extends far beyond traditional healthcare providers, encompassing any entity that handles protected health information (PHI), including software companies, cloud service providers, and third-party technology vendors.
The potential consequences of non-compliance are substantial. Penalties can range from modest fines for minor infractions to massive financial penalties for systematic or willful violations. Organizations may face:
- Monetary penalties up to $1.5 million per violation category per year
- Mandatory external audits and monitoring
- Potential criminal charges for severe breaches
- Significant reputational damage that can impact future business opportunities
For software companies, this means developing robust security infrastructure is not just a regulatory requirement but a critical business strategy. Every touchpoint that involves electronic protected health information (ePHI) must be carefully designed, implemented, and continuously monitored.
Effective HIPAA enforcement requires a proactive approach. Software organizations must implement comprehensive security protocols, conduct regular risk assessments, maintain detailed documentation, and create a culture of ongoing compliance. This involves not just technological solutions but also extensive staff training, clear policies, and a systematic approach to data protection.
Understanding the nuanced landscape of HIPAA enforcement is crucial. It is not merely about avoiding penalties but about establishing trust, protecting patient information, and demonstrating a commitment to the highest standards of data privacy and security.
Common Compliance Challenges for B2B Software
B2B software companies face intricate HIPAA compliance challenges that demand sophisticated technical and organizational strategies. Navigating these complex requirements requires a comprehensive understanding of potential pitfalls and proactive risk management approaches.
Technical Safeguards and Infrastructure Vulnerabilities
The HHS Office for Civil Rights consistently identifies significant technical challenges that B2B software providers encounter. Encryption, secure data transmission, and robust access controls represent critical areas where organizations frequently struggle. Academic research reveals that many cloud-based B2B solutions demonstrate substantial gaps in implementing comprehensive technical safeguards.
Key technical challenges include:
- Data Encryption: Ensuring end-to-end encryption for protected health information (PHI) across all transmission channels
- Access Management: Implementing granular user authentication and authorization mechanisms
- Audit Trail Maintenance: Creating comprehensive logging systems that track all PHI interactions
These technical requirements demand not just initial implementation but continuous monitoring and adaptation. Software companies must develop dynamic security infrastructures that can evolve with emerging technological landscapes and regulatory expectations.
Organizational Risk Management Complexities
Beyond technical requirements, B2B software providers must establish robust organizational frameworks that support HIPAA compliance. This involves developing comprehensive policies, conducting regular risk assessments, and creating a culture of privacy and security awareness. Learn more about managing security questionnaires effectively to understand the broader compliance ecosystem.
Organizational challenges often stem from:
Below is a summary table highlighting common technical and organizational challenges B2B software companies face with HIPAA compliance, along with corresponding examples mentioned in the article.
| Challenge Type | Specific Issue | Example or Description |
|---|---|---|
| Technical | Data Encryption | Ensuring end-to-end encryption for PHI across all channels |
| Technical | Access Management | Granular user authentication and authorization mechanisms |
| Technical | Audit Trail Maintenance | Creating comprehensive logging systems for PHI interactions |
| Organizational | Incomplete Risk Analysis | Failing to conduct thorough, periodic PHI exposure assessments |
| Organizational | Inadequate Staff Training | Not providing comprehensive and ongoing HIPAA education |
| Organizational | Documentation Gaps | Insufficient record-keeping of compliance efforts |
- Incomplete Risk Analysis: Failing to conduct thorough and periodic assessments of potential PHI exposure
- Inadequate Staff Training: Not providing comprehensive and ongoing education about HIPAA requirements
- Documentation Gaps: Insufficient record-keeping of compliance efforts and security protocols
Successful HIPAA compliance requires a holistic approach that integrates technological solutions with strategic organizational practices. Software companies must view compliance not as a checkbox exercise but as a fundamental aspect of their operational integrity.
The consequences of non-compliance extend far beyond potential financial penalties. Regulatory violations can result in significant reputational damage, loss of client trust, and potential exclusion from critical healthcare technology markets. B2B software providers must therefore adopt a proactive and comprehensive approach to HIPAA enforcement, treating compliance as a core business strategy rather than a peripheral concern.
Best Practices to Reduce HIPAA Enforcement Risks
Reducing HIPAA enforcement risks requires a strategic and comprehensive approach that goes beyond basic compliance checkboxes. Software companies must develop a proactive framework that anticipates potential vulnerabilities and demonstrates a genuine commitment to protecting protected health information (PHI).
Comprehensive Risk Assessment and Management
The U.S. Department of Health & Human Services emphasizes the critical importance of regular and thorough security risk assessments. These assessments are not one-time events but ongoing processes that require continuous evaluation and refinement.
Key components of an effective risk assessment include:
- Systematic Vulnerability Analysis: Identifying potential weak points in data handling processes
- Comprehensive Documentation: Maintaining detailed records of risk assessment methodologies and findings
- Periodic Review: Conducting regular reassessments to address emerging technological and regulatory changes
Research from the Journal of Medical Informatics highlights that organizations with robust, documented risk management strategies are significantly less likely to face severe HIPAA enforcement actions.
Technical and Organizational Safeguards
Implementing multi-layered technical and organizational safeguards is crucial for mitigating HIPAA enforcement risks. This approach requires a holistic strategy that integrates advanced technological solutions with comprehensive staff training and clear operational protocols.
Critical safeguard strategies include:
- Advanced Encryption Protocols: Implementing end-to-end encryption for all PHI transmission channels
- Access Control Mechanisms: Developing granular user authentication and authorization systems
- Incident Response Planning: Creating detailed protocols for identifying, reporting, and addressing potential security breaches
Effective safeguards go beyond technological implementation. They require creating a culture of privacy and security awareness that permeates every level of the organization.
Continuous Training and Compliance Education
Ongoing staff education represents a fundamental pillar of HIPAA risk mitigation. Software companies must develop comprehensive training programs that not only explain regulatory requirements but also foster a proactive approach to data protection.
Training should focus on:
- Practical Privacy Protocols: Teaching employees specific actions to protect PHI
- Scenario-Based Learning: Providing real-world examples of potential compliance challenges
- Regular Update Sessions: Keeping staff informed about evolving regulatory requirements
By treating HIPAA compliance as a dynamic, ongoing process rather than a static set of rules, software companies can significantly reduce their risk of enforcement actions. The goal is not just to avoid penalties but to establish a genuine commitment to protecting sensitive health information.
Ultimately, successful HIPAA risk reduction requires a proactive, integrated approach that combines technological innovation, comprehensive documentation, continuous education, and a genuine organizational commitment to privacy and security.
Responding to HIPAA Investigations and Audits
HIPAA investigations and audits represent critical moments for software companies handling protected health information (PHI). Responding effectively requires a strategic, well-documented, and transparent approach that demonstrates organizational commitment to compliance and patient data protection.
The table below outlines the typical steps involved in responding to HIPAA investigations and audits, summarizing key actions for each stage.
| Stage | Key Actions |
|---|---|
| Preparation | Maintain documentation; develop response protocols; perform self-audits |
| Investigation Notification | Assemble requested documents; notify key staff |
| Investigation Response | Provide transparent communication; gather evidence |
| Audit Process | Show systematic compliance; respond to auditor questions |
| Remediation & Mitigation | Address vulnerabilities; conduct root cause analysis; implement improvements |
Preparing for Potential Investigations
The U.S. Department of Health and Human Services outlines a comprehensive enforcement process that software companies must anticipate. According to recent data, the Office for Civil Rights (OCR) has received over 374,321 HIPAA complaints, highlighting the critical importance of being prepared for potential investigations.
Key preparation strategies include:
- Comprehensive Documentation: Maintaining detailed records of all PHI handling processes
- Rapid Response Protocols: Developing clear procedures for addressing investigation requests
- Internal Audit Readiness: Conducting regular self-assessments to identify potential vulnerabilities
Navigating the Audit Process
The Office of Inspector General (OIG) recommends a proactive approach to audit preparedness. Successful navigation of HIPAA investigations requires more than just reactive compliance. Organizations must demonstrate a systematic approach to protecting electronic protected health information (ePHI).
Critical audit response components include:
- Transparent Communication: Providing clear, honest responses to all investigator inquiries
- Evidence Collection: Assembling comprehensive documentation of compliance efforts
- Remediation Planning: Developing immediate and long-term corrective action strategies
Mitigating Potential Enforcement Actions
When faced with a HIPAA investigation, software companies must approach the process as an opportunity for improvement rather than a purely punitive experience. The goal is to demonstrate a genuine commitment to patient data protection and regulatory compliance.
Effective mitigation strategies involve:
- Proactive Correction: Immediately addressing any identified vulnerabilities
- Comprehensive Root Cause Analysis: Understanding the underlying reasons for potential compliance issues
- Systematic Improvement: Implementing long-term changes to prevent future incidents
The investigation process can be complex and potentially challenging. However, organizations that approach HIPAA investigations with transparency, preparedness, and a genuine commitment to improvement can often transform a potentially negative experience into an opportunity for enhancing their overall data protection strategies.
Ultimately, successful response to HIPAA investigations requires more than just technical compliance. It demands a holistic approach that integrates robust security measures, comprehensive documentation, transparent communication, and a proactive commitment to continuous improvement in protecting sensitive health information.

Frequently Asked Questions
What are the consequences of non-compliance with HIPAA for software companies?
Failure to comply with HIPAA can lead to substantial penalties, including fines up to $1.5 million per violation category per year, mandatory audits, and significant reputational damage that can impact future business opportunities.
How can software companies effectively prepare for HIPAA audits?
Effective preparation for HIPAA audits involves maintaining comprehensive documentation, developing rapid response protocols for investigation requests, and conducting regular self-assessments to identify and address potential vulnerabilities in data handling practices.
What are some common compliance challenges that B2B software companies face regarding HIPAA?
Common compliance challenges for B2B software companies include technical issues such as data encryption and access management, as well as organizational complexities like incomplete risk assessments and inadequate staff training.
What best practices should software companies implement to reduce HIPAA enforcement risks?
Best practices include conducting regular risk assessments, implementing robust technical safeguards, fostering a culture of compliance through continuous training, and preparing thoroughly for potential audits and investigations.
Take the Stress Out of HIPAA Compliance with Automated Security Responses
Are you feeling overwhelmed by the pressure of HIPAA enforcement and the need for airtight documentation? Struggling to keep up with continuous risk assessments, technical safeguards, and proper audit responses can stall your team's productivity and threaten your reputation. The article highlighted how missed details or inconsistent processes can invite hefty fines and damage client trust.

Now is the time to transform your compliance journey. Skypher supercharges your response to security questionnaires with automation that keeps your documentation current and audit-ready. Cut down on manual errors and empower your team to manage risk assessments confidently. Visit Skypher's homepage to see how our AI-driven tools help you prove compliance faster and avoid costly HIPAA enforcement issues.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- The ever growing number of security questionnaires and what you and your company can do to face it
- The Case for Security Questionnaire Automation
- Privacy Policy
- Odoo HIPAA Compliance Implementation by Bista Solutions
- Rampant EMS Billing Fraud in Healthcare – VectorCare