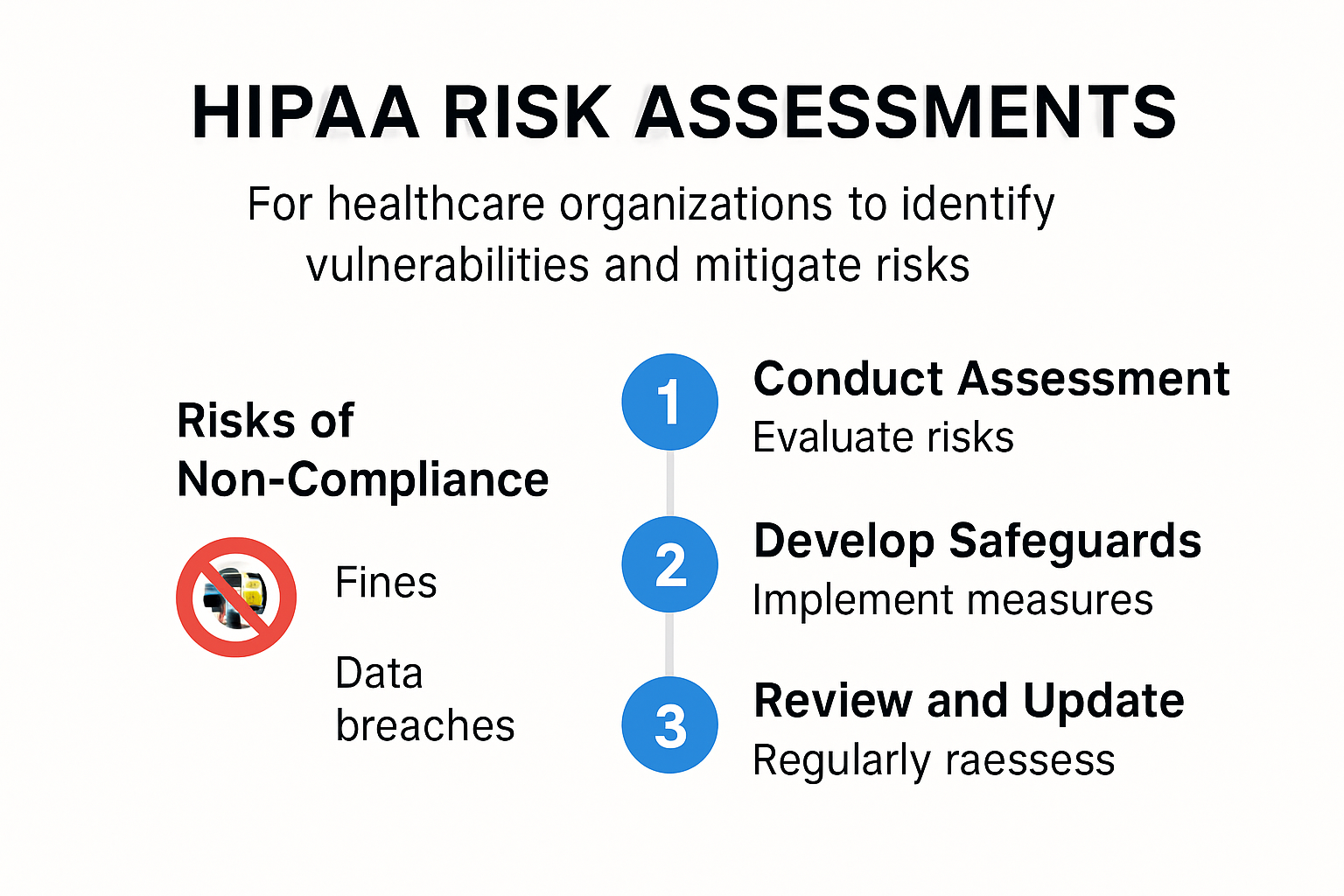
HIPAA risk assessments might sound like paperwork, but the stakes are sky high for healthcare providers. HIPAA violations can trigger fines of up to $50,000 per incident and even a single gap can shatter patient trust overnight. Most people expect the biggest threat comes from hackers and technical glitches. Actually, the real risks often start with overlooked staff training and neglected ongoing reviews. Digging into the latest compliance strategies isn’t just about checking off boxes anymore. It means staying one step ahead of costly penalties and unexpected data breaches.
Table of Contents
- Understanding Hipaa Risk Assessments And Why They Matter
- Step-By-Step Process For Conducting A Hipaa Risk Assessment
- Common Challenges And Mistakes To Avoid
- Best Practices In 2025 For Stronger Hipaa Compliance
Quick Summary
| Takeaway | Explanation |
|---|---|
| Comprehensive Risk Assessments are Mandatory | HIPAA risk assessments are essential for identifying vulnerabilities and ensuring compliance, protecting patient data from breaches. |
| Neglecting Assessments Leads to Serious Consequences | Failing to conduct proper assessments can result in hefty fines, legal actions, and damage to an organization’s reputation. |
| Dynamic and Continuous Process Required | Risk assessments should be ongoing, allowing organizations to adapt to new threats and improve their security posture continuously. |
| Importance of Staff Training | Comprehensive training in security protocols and awareness can significantly reduce vulnerabilities linked to human error. |
| Integration of Advanced Technologies | Leveraging AI and advanced security measures is crucial for maintaining effective risk management and HIPAA compliance in the evolving digital landscape. |
Understanding HIPAA Risk Assessments and Why They Matter
Healthcare providers face increasingly complex cybersecurity challenges that demand proactive and strategic approaches to protecting patient data. HIPAA risk assessments represent a critical mechanism for identifying, analyzing, and mitigating potential vulnerabilities in healthcare information systems.
The Core Purpose of HIPAA Risk Assessments
At its fundamental level, a HIPAA risk assessment serves as a comprehensive diagnostic tool that enables healthcare organizations to evaluate their current information security infrastructure. These assessments go far beyond a simple checklist exercise. They represent a systematic process of examining how protected health information (PHI) is stored, transmitted, and accessed within an organization.
The primary objectives of these assessments include:
- Vulnerability Detection: Identifying potential weaknesses in electronic health record systems, network configurations, and data management protocols
- Compliance Verification: Ensuring organizational practices align with HIPAA regulatory requirements
- Risk Mitigation Strategy: Developing targeted interventions to address discovered security gaps
Healthcare providers must recognize that risk assessments are not optional administrative tasks. They are mandatory requirements designed to protect patient privacy and prevent potentially devastating data breaches.
Financial and Legal Implications of Risk Assessment Neglect
Failure to conduct thorough HIPAA risk assessments can result in significant consequences. The Department of Health and Human Services can impose substantial financial penalties for non-compliance, with fines ranging from $100 to $50,000 per violation, depending on the severity and level of organizational negligence.
Moreover, beyond monetary penalties, healthcare organizations risk:
- Potential legal actions from patients
- Permanent damage to institutional reputation
- Loss of patient trust
- Potential suspension or revocation of operational licenses
Strategic Approach to Comprehensive Risk Assessment
Effective HIPAA risk assessments require a multifaceted approach that encompasses technological, procedural, and human factors. Healthcare providers must develop a comprehensive strategy that includes:
- Detailed inventory of all systems handling PHI
- Comprehensive analysis of potential security threats
- Evaluation of existing security controls
- Documentation of potential risks and recommended mitigation strategies
- Ongoing monitoring and periodic reassessment
By treating risk assessments as dynamic, continuous processes rather than static compliance exercises, healthcare organizations can create robust, adaptive security frameworks that evolve alongside emerging technological challenges.
Ultimately, HIPAA risk assessments are not merely regulatory obligations. They represent a fundamental commitment to patient privacy, data integrity, and organizational resilience in an increasingly complex digital healthcare environment.
Step-by-Step Process for Conducting a HIPAA Risk Assessment
A methodical approach is essential when conducting HIPAA risk assessments. Healthcare organizations must follow a structured process that ensures comprehensive evaluation and thorough documentation of potential vulnerabilities.
Preparing for the Risk Assessment
Before diving into the technical aspects of the assessment, organizations must establish a solid foundation. This preparation phase involves assembling a dedicated team with diverse expertise in cybersecurity, healthcare operations, and regulatory compliance.
Key preparation steps include:
- Team Composition: Select individuals from IT, legal, compliance, and clinical departments
- Scope Definition: Clearly outline the boundaries of the risk assessment
- Documentation Planning: Prepare templates and tracking mechanisms for recording findings
The assessment team must have a clear understanding of the organization's technological ecosystem, including all systems that interact with protected health information (PHI). This involves creating a comprehensive inventory of hardware, software, networks, and data storage mechanisms.
Comprehensive Vulnerability Identification
The core of the HIPAA risk assessment process involves meticulously identifying potential vulnerabilities across multiple domains. According to the National Institute of Standards and Technology, this step requires a systematic approach to detecting potential security weaknesses.
Critical areas of vulnerability assessment include:
- Electronic Protected Health Information (ePHI) storage systems
- Network infrastructure and access controls
- Physical security of data storage locations
- User authentication and access management protocols
- Third-party vendor security practices
Organizations must conduct both automated and manual assessments. Automated tools can scan for technical vulnerabilities, while manual reviews provide insights into procedural and human-factor risks that technology alone cannot detect.

Risk Mitigation and Documentation
After identifying vulnerabilities, healthcare providers must develop a comprehensive risk mitigation strategy. This involves prioritizing risks based on their potential impact and likelihood of occurrence. The Office for Civil Rights emphasizes the importance of creating actionable remediation plans.
Effective risk mitigation involves:
- Ranking identified vulnerabilities by severity
- Developing specific corrective action plans
- Establishing timelines for implementing security improvements
- Creating ongoing monitoring mechanisms
- Documenting all findings and proposed interventions
Documentation is crucial. Each identified risk should include:
- Detailed description of the vulnerability
- Potential impact on patient data protection
- Recommended remediation strategies
- Estimated resources required for correction
- Proposed timeline for addressing the issue
Healthcare organizations must view the HIPAA risk assessment as a dynamic, continuous process. Technology evolves rapidly, and new vulnerabilities emerge constantly. Regular reassessment ensures that security measures remain current and effective, protecting patient data from emerging threats.
Successful HIPAA risk assessments require a proactive, comprehensive approach that goes beyond mere compliance. They represent a critical strategy for maintaining patient trust, protecting sensitive information, and ensuring the integrity of healthcare information systems.
Common Challenges and Mistakes to Avoid
Healthcare organizations frequently encounter significant obstacles when implementing HIPAA risk assessments. Understanding these challenges can help providers develop more robust and effective security strategies.
Underestimating Scope and Complexity
One of the most prevalent mistakes healthcare providers make is oversimplifying the HIPAA risk assessment process. Many organizations mistakenly view these assessments as simple checkbox exercises, failing to recognize the intricate nature of comprehensive security evaluations.
Key misconceptions include:
- Assuming all systems are equally secure
- Neglecting to include all PHI touchpoints
- Overlooking third-party vendor relationships
- Treating risk assessments as one-time events
The HIPAA Journal highlights that incomplete assessments can leave critical vulnerabilities unaddressed, potentially exposing patient data to significant risks.
Technical and Human Factor Challenges
Healthcare organizations face complex challenges that extend beyond technological solutions. These challenges encompass both technical infrastructure and human behavior.
Technical challenges include:
- Rapidly evolving technology landscapes
- Integration of legacy systems with modern security protocols
- Managing diverse network environments
- Keeping pace with emerging cybersecurity threats
Human factor challenges are equally critical. According to Verizon's Data Breach Investigations Report, human error remains a significant contributor to security incidents. Healthcare providers must address:
- Inconsistent staff training
- Weak password practices
- Insufficient understanding of security protocols
- Resistance to implementing new security measures
Effective Mitigation Strategies
Overcoming these challenges requires a multifaceted approach that combines technological solutions, comprehensive training, and organizational commitment.
Recommended strategies include:
- Comprehensive Training Programs: Develop ongoing education initiatives that keep staff updated on latest security practices
- Regular Assessment Updates: Implement quarterly or semi-annual reassessments
- Advanced Technology Integration: Utilize AI-powered security monitoring tools
- Cultural Transformation: Create a security-first organizational mindset
Healthcare providers must recognize that HIPAA risk assessments are not static documents but dynamic processes requiring continuous attention and adaptation. The most successful organizations approach these assessments as strategic opportunities to enhance overall organizational resilience.
By proactively addressing common challenges, healthcare providers can transform potential vulnerabilities into strengths. This approach not only ensures regulatory compliance but also builds patient trust and demonstrates a genuine commitment to protecting sensitive health information.
Best Practices in 2025 for Stronger HIPAA Compliance
As healthcare technology continues to evolve, HIPAA compliance requires increasingly sophisticated approaches that blend cutting-edge technology with robust security strategies. Providers must adopt a proactive and comprehensive framework to protect patient data and maintain regulatory standards.
Technological Integration and Advanced Security Measures
In 2025, healthcare organizations must leverage advanced technologies to enhance their HIPAA compliance efforts. The integration of artificial intelligence, machine learning, and sophisticated cybersecurity tools will become critical components of effective risk management.
Key technological strategies include:
- AI-Powered Threat Detection: Implementing intelligent systems that can identify and respond to potential security breaches in real-time
- Advanced Encryption Technologies: Utilizing quantum-resistant encryption methods for data protection
- Continuous Monitoring Systems: Developing real-time security assessment platforms that provide ongoing vulnerability analysis
The National Institute of Standards and Technology emphasizes the importance of adaptive security architectures that can quickly respond to emerging technological challenges.
Comprehensive Staff Training and Cultural Transformation
Technology alone cannot ensure HIPAA compliance. Organizations must invest heavily in human-centric security approaches that transform organizational culture and individual behavior.
Critical training focus areas include:
- Advanced cybersecurity awareness programs
- Detailed understanding of PHI protection protocols
- Social engineering threat recognition
- Secure communication practices
- Incident response and reporting mechanisms
According to Cybersecurity Ventures, human error remains a significant vulnerability in healthcare security, making comprehensive training an essential component of compliance strategies.
Emerging Compliance and Risk Management Approaches
Healthcare providers must adopt more dynamic and predictive approaches to HIPAA compliance. This involves moving beyond reactive measures to anticipatory risk management strategies.
Recommended emerging practices include:
- Predictive Risk Modeling: Utilizing advanced analytics to forecast potential security vulnerabilities
- Comprehensive Vendor Security Assessments: Implementing rigorous third-party risk evaluation processes
- Integrated Compliance Platforms: Developing holistic systems that combine risk assessment, monitoring, and reporting
- Zero Trust Security Architecture: Implementing strict access controls and continuous authentication mechanisms
The most successful healthcare organizations will view HIPAA compliance as a strategic advantage rather than a mere regulatory requirement. By embracing innovative technologies, comprehensive training, and proactive risk management approaches, providers can create robust security ecosystems that protect patient data and build organizational resilience.
As healthcare continues to digitize and become more interconnected, the ability to adapt quickly and implement sophisticated security measures will distinguish leading healthcare providers. HIPAA compliance in 2025 demands a forward-thinking approach that balances technological innovation with human-centric security practices.
Frequently Asked Questions
What is the purpose of HIPAA risk assessments?
HIPAA risk assessments help healthcare providers identify vulnerabilities in their systems, ensure compliance with regulations, and protect patient data from breaches.
What are the consequences of neglecting HIPAA risk assessments?
Neglecting HIPAA risk assessments can lead to fines ranging from $100 to $50,000 per violation, potential legal actions from patients, and damage to the organization's reputation and patient trust.
How often should HIPAA risk assessments be conducted?
HIPAA risk assessments should be ongoing and periodic, ideally updated quarterly or semi-annually, to adapt to new threats and maintain security measures.
What are the common challenges faced during HIPAA risk assessments?
Common challenges include underestimating the scope and complexity of assessments, technical challenges with evolving technology, and human factor issues such as inconsistent staff training.
Transform Your HIPAA Risk Assessments Into Effortless Wins
Managing HIPAA risk assessments can feel overwhelming when every overlooked vulnerability or missed update puts your organization at risk of heavy fines and loss of trust. The article above highlights how human error, outdated reviews, and manual responses to security evaluations can jeopardize both compliance and patient data. If answering endless security questionnaires takes too much time or causes stress across your team, you are not alone.

Take control and make risk assessments a competitive advantage. Skypher empowers your organization with an AI-powered Questionnaire Automation Tool that drastically reduces the time and effort required to respond to compliance and security reviews. Bring your team together with real-time collaboration and integrations with over 40 risk management platforms. Protect your patients. Secure your reputation. See how Skypher keeps you ahead of regulatory requirements and lets you focus on what truly matters. Start today and leave the manual headaches behind.