Everyone talks about cybersecurity threats getting more complex every year and it feels like no business is safe. Yet what usually gets missed is that pentesting can uncover what automated scans might never find. In fact, up to 93 percent of security teams reported missing critical vulnerabilities until a pentest revealed them. Most people assume pentesting is just a checkbox for compliance, but the real edge comes when it’s approached as a strategic shield against real attacks. This might completely change how you think about securing your organization.
Table of Contents
- Understanding Pentesting In Business Environments
- Planning And Preparing Your Pentest Process
- Executing A Pentest: Methods And Tools
- Addressing Risks And Compliance Requirements
Quick Summary
| Takeaway | Explanation |
|---|---|
| Penetration testing identifies hidden vulnerabilities | It helps organizations discover weaknesses before they can be exploited by attackers, enhancing overall security. |
| Define clear objectives for pentests | Establish specific goals and scope to guide the assessment and focus on relevant risks and systems. |
| Utilize established pentesting methodologies | Employ frameworks like black box and white box testing to ensure thorough examination and effective coverage. |
| Document findings and recommendations clearly | Prioritize vulnerabilities and provide actionable remediation strategies that facilitate timely security improvements. |
| View pentesting as an ongoing process | Implement continuous assessments for sustained security and risk management, rather than treating it as a one-time event. |
Understanding Pentesting in Business Environments
In the complex world of cybersecurity, penetration testing represents a critical strategy for organizations to proactively identify and mitigate potential security vulnerabilities. Pentesting goes beyond traditional security assessments by simulating real-world cyberattacks to expose weaknesses in an organization's digital infrastructure.
The Strategic Importance of Penetration Testing
Penetration testing is not just a technical exercise but a strategic business risk management approach. Organizations face increasingly sophisticated cyber threats that can compromise sensitive data, disrupt operations, and cause significant financial and reputational damage. The Cybersecurity and Infrastructure Security Agency (CISA) emphasizes that penetration testing services help organizations measure compliance with security policies and assess their overall cybersecurity risk landscape.
Businesses across various sectors recognize that waiting for a breach to occur is no longer a viable strategy. Proactive security testing allows companies to:
- Identify Vulnerabilities: Discover hidden security weaknesses before malicious actors can exploit them
- Validate Security Controls: Test the effectiveness of existing security mechanisms and incident response protocols
- Demonstrate Due Diligence: Provide concrete evidence of robust security practices to stakeholders, clients, and regulatory bodies
Pentesting as a Comprehensive Security Assessment
The U.S. Department of the Interior's Office of the Chief Information Officer highlights that effective penetration testing involves simulating real-life attacks to comprehensively evaluate an organization's security posture. This process is not about simply finding technical vulnerabilities but understanding how these weaknesses could be exploited in actual scenarios.
Modern pentesting encompasses a holistic approach that evaluates multiple dimensions of an organization's security infrastructure. This includes assessing network architecture, application security, human factors, and potential social engineering vulnerabilities. By mimicking the tactics of potential attackers, security professionals can provide actionable insights that go beyond traditional vulnerability scanning.
For B2B security professionals, pentesting represents more than a compliance checkbox. It is a dynamic, ongoing process of understanding and mitigating evolving cyber risks. Learn more about our comprehensive security assessment tools that can help your organization stay ahead of potential security threats.
The ultimate goal of penetration testing is not to create fear but to empower organizations with knowledge. By understanding potential vulnerabilities and attack vectors, businesses can develop more resilient, adaptive security strategies that protect their most valuable assets.
Planning and Preparing Your Pentest Process
Penetration testing demands meticulous planning and preparation to ensure a comprehensive and effective security assessment. This critical phase sets the foundation for a successful pentest by establishing clear objectives, defining scope, and preparing the necessary resources and permissions.
Defining Clear Objectives and Scope
The SANS Institute emphasizes the importance of establishing precise objectives before initiating a penetration test. Organizations must critically evaluate their specific security concerns and define explicit goals for the assessment. This involves identifying which systems, networks, and applications will be included in the testing process.
Key considerations for scoping a penetration test include:
- System Boundaries: Clearly delineate which systems are in-scope and out-of-scope
- Testing Limitations: Establish rules of engagement that protect critical infrastructure
- Compliance Requirements: Ensure the pentest aligns with industry and regulatory standards
The OWASP Web Security Testing Guide recommends a comprehensive approach to pre-engagement activities. This includes conducting thorough intelligence gathering, performing initial threat modeling, and developing a detailed testing strategy that addresses potential vulnerabilities across different system components.
Preparing the Testing Environment
Preparing the testing environment is a critical step that requires careful coordination and technical precision. The Defense Industrial Base Sector Coordinating Council highlights the necessity of obtaining explicit permissions and creating a controlled testing environment that minimizes potential disruptions to business operations.
Organizations should take several preparatory steps:
- Secure written authorization from senior management
- Develop a comprehensive communication plan
- Create isolated testing environments that mirror production systems
- Establish clear communication channels with the pentesting team
- Prepare incident response protocols in case of unexpected discoveries
Team Coordination and Risk Management
Successful pentesting requires seamless coordination between internal teams and external security professionals. Learn more about managing complex security assessments to understand the intricate dynamics of security testing.
Effective pentesting preparation involves:
- Selecting qualified and experienced security professionals
- Ensuring all stakeholders understand the testing objectives
- Developing a robust risk management framework
- Creating detailed documentation of the testing process
- Establishing clear reporting and follow-up mechanisms
By investing time and resources in comprehensive planning and preparation, organizations can maximize the value of their penetration testing efforts. This strategic approach transforms pentesting from a mere compliance exercise into a powerful tool for continuous security improvement and risk mitigation.
Executing a Pentest: Methods and Tools
Executing a penetration test requires a strategic approach that combines technical expertise, sophisticated tools, and comprehensive methodologies. The implementation phase transforms planning into actionable security insights through systematic vulnerability identification and exploitation techniques.
Penetration Testing Methodologies
The OWASP Testing Guide provides a comprehensive framework for systematic security assessment. Professional penetration testers typically employ multiple established methodologies to ensure thorough coverage and reliable results.
Key penetration testing methodologies include:
- Black Box Testing: Simulating an external attacker with zero prior knowledge of the system
- White Box Testing: Conducting tests with complete system information and internal architecture insights
- Gray Box Testing: Utilizing partial system knowledge to perform targeted vulnerability assessments
Each methodology offers unique advantages in uncovering potential security weaknesses. The selection depends on specific organizational requirements, system complexity, and desired depth of investigation.
To help you compare the different penetration testing methodologies discussed, the following table summarizes their key characteristics and advantages:
| Methodology | System Knowledge | Typical Use Case | Key Advantage |
|---|---|---|---|
| Black Box Testing | None | Simulates external attacker with no system info | Reveals vulnerabilities open to outsiders |
| White Box Testing | Full | Insider with complete knowledge | Comprehensive assessment of all layers |
| Gray Box Testing | Partial | Some system knowledge, simulates internal threat | Balances realism with thoroughness |
Essential Penetration Testing Tools
NIST's cybersecurity resources highlight the critical role of specialized tools in executing comprehensive security assessments. Modern penetration testing relies on a sophisticated arsenal of software and techniques designed to probe, analyze, and exploit potential vulnerabilities.
Critical categories of pentesting tools include:
- Network Scanning Tools: Identify open ports, services, and potential entry points
- Vulnerability Assessment Platforms: Automatically detect known security weaknesses
- Exploitation Frameworks: Simulate advanced attack scenarios
- Wireless Network Testing Tools: Evaluate wireless infrastructure security
- Social Engineering Simulation Tools: Test human factor vulnerabilities
Execution and Reporting Strategies
Successful pentesting goes beyond merely identifying vulnerabilities. It requires a structured approach to executing tests, documenting findings, and providing actionable recommendations. Learn more about comprehensive security assessment methodologies to understand the nuanced process of security evaluation.
Key execution considerations include:
- Maintaining strict ethical boundaries during testing
- Minimizing potential operational disruptions
- Documenting all discovered vulnerabilities with precise technical details
- Prioritizing risks based on potential business impact
- Developing clear, actionable remediation strategies
Penetration testing is not a one-time event but a continuous process of security validation. By combining robust methodologies, advanced tools, and systematic execution, organizations can proactively identify and mitigate potential security risks before they can be exploited by malicious actors.
The ultimate goal remains transforming theoretical vulnerabilities into concrete, manageable security improvements that enhance overall organizational resilience.
Addressing Risks and Compliance Requirements
Addressing risks and compliance requirements is a critical aspect of penetration testing that goes far beyond technical vulnerability assessment. Organizations must navigate a complex landscape of regulatory frameworks, industry standards, and potential legal implications while ensuring comprehensive security protection.
Regulatory Compliance Frameworks
Codacy's cybersecurity blog provides an extensive overview of regulatory frameworks that mandate penetration testing across various industries. Multiple standards require organizations to demonstrate proactive security measures through systematic vulnerability assessments.
Key regulatory standards that impact penetration testing include:
- PCI-DSS: Payment Card Industry Data Security Standard
- HIPAA: Health Insurance Portability and Accountability Act
- GDPR: General Data Protection Regulation
- ISO 27001: Information Security Management Systems Standard
- NIST Cybersecurity Framework: National Institute of Standards and Technology guidelines
Each framework establishes specific requirements for security testing, emphasizing the need for comprehensive and documented vulnerability assessments that protect sensitive organizational data.
The following table summarizes major regulatory frameworks that require or recommend penetration testing, along with their main focus areas:
| Regulatory Standard | Industry/Application | Focus Area |
|---|---|---|
| PCI-DSS | Payment processing | Payment data security |
| HIPAA | Healthcare | Protected health information (PHI) |
| GDPR | All (EU personal data) | Data protection and privacy |
| ISO 27001 | All industries | Information security management |
| NIST Cybersecurity | U.S. government & industry | Risk management & security controls |
Risk Management and Mitigation Strategies
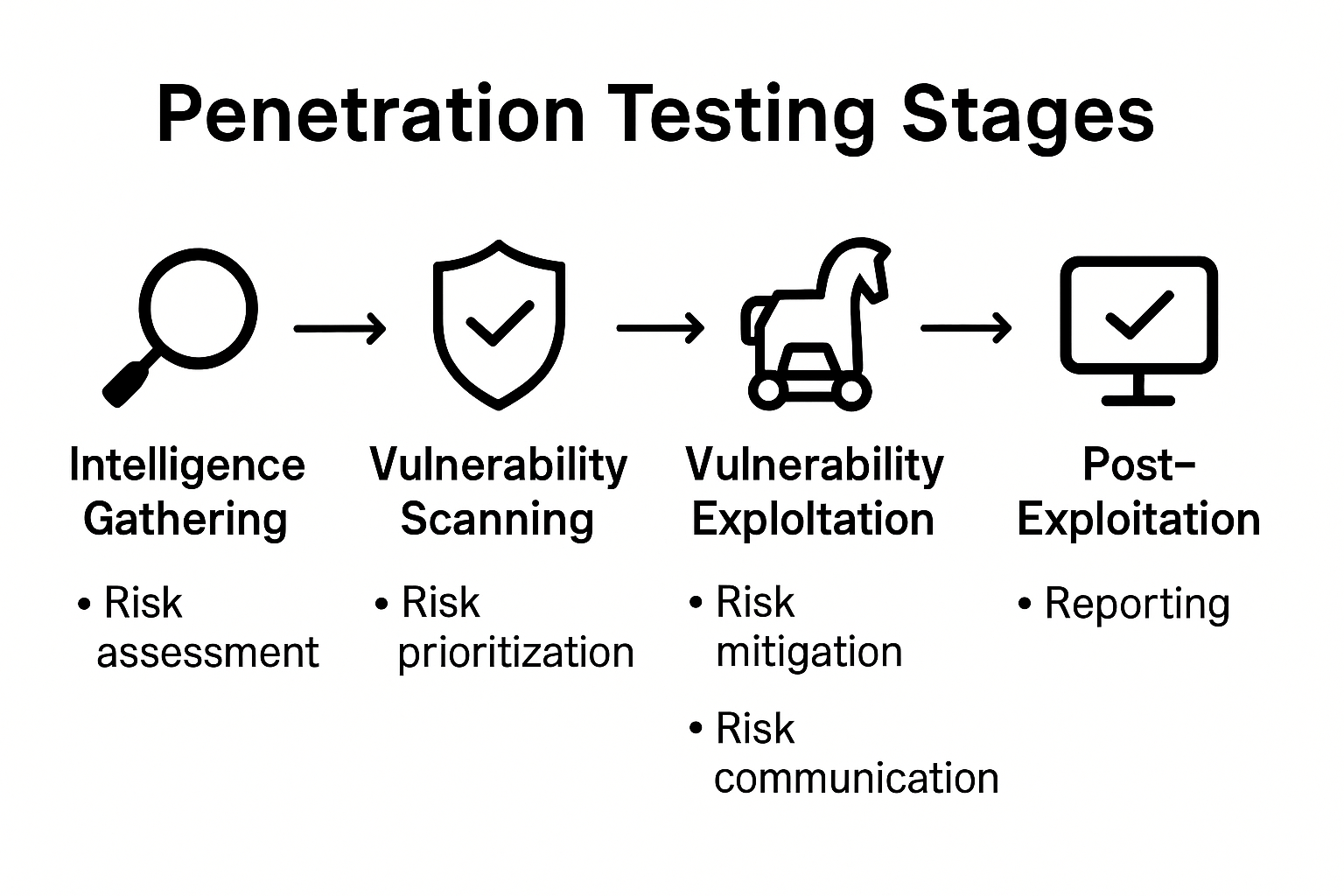
Academic research from Cornell University outlines five fundamental stages of penetration testing that are crucial for effective risk management: intelligence gathering, vulnerability scanning, vulnerability exploitation, privilege escalation, and post-exploitation activities.
Effective risk management during penetration testing involves:
- Conducting thorough pre-test risk assessments
- Establishing clear boundaries for testing activities
- Developing comprehensive incident response protocols
- Creating detailed documentation of discovered vulnerabilities
- Implementing systematic remediation tracking
Comprehensive Reporting and Continuous Improvement
TechTarget's security resources emphasize the importance of rigorous reporting and continuous improvement in addressing cybersecurity risks. Learn more about managing complex security assessment processes to understand the nuanced approach required for effective risk management.
Key reporting considerations include:
- Prioritizing vulnerabilities based on potential business impact
- Providing clear, actionable remediation recommendations
- Establishing a timeline for addressing identified security weaknesses
- Creating a mechanism for tracking and verifying implemented fixes
- Developing a continuous monitoring and reassessment strategy
Successful risk management and compliance in penetration testing requires a holistic approach that balances technical expertise, regulatory requirements, and strategic business objectives. Organizations must view penetration testing not as a singular event but as an ongoing process of security validation and continuous improvement.
By systematically addressing risks and maintaining compliance with industry standards, businesses can build robust security frameworks that protect their most valuable digital assets and maintain stakeholder confidence.

Frequently Asked Questions
What is penetration testing and why is it important for businesses?
Penetration testing, or pentesting, is a simulated cyberattack on an organization's digital infrastructure to identify security vulnerabilities. It is important for businesses because it helps uncover hidden weaknesses before they can be exploited by attackers, validates security controls, and demonstrates due diligence to stakeholders.
How should I prepare for a penetration test?
Preparation for a penetration test involves defining clear objectives and scope, coordinating with internal and external teams, securing necessary permissions, and preparing the testing environment. This ensures the pentest runs smoothly and securely without disrupting business operations.
What methodologies are commonly used in penetration testing?
Common methodologies in penetration testing include Black Box Testing (no prior knowledge of the system), White Box Testing (full system information), and Gray Box Testing (partial knowledge). Each methodology offers different advantages depending on the specific goals and requirements of the assessment.
How do I interpret and act on the findings from a penetration test?
Interpreting findings from a penetration test involves prioritizing vulnerabilities based on potential business impact and developing actionable remediation strategies. Key recommendations should be documented clearly, and organizations should establish a timeline and process for addressing the identified weaknesses.
Turn Pentesting Insights Into Instant Questionnaire Wins
Finding hidden vulnerabilities through pentesting is only part of the journey. Once you uncover risks, proving your security strengths to clients and partners can become a new challenge. Security questionnaires pile up and every question counts when building trust and moving deals forward. If your team feels overwhelmed by endless requests or worried about slow responses derailing sales, you are not alone.

Skypher takes your newfound pentest knowledge and transforms dreaded security reviews into a streamlined, automated process. Our AI-driven Questionnaire Automation Tool helps you answer security questions faster and more accurately, saving your team hours of manual work. Connect insights from your penetration tests directly to your responses, proving your commitment to security while winning client confidence. Visit Skypher now to see how you can close deals faster and showcase your security success in every assessment.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- Blog - Skypher
- Lalita Hardier - Saasy - Webflow HTML Website Template
- Guides - Saasy - Webflow HTML Website Template
- 5 Ways to Secure Your Small Business and Prevent Data Breach-Bista
- Ecommerce Website Testing: Optimize Conversions for 2025 Success
