Building an I T security policy sounds like a technical chore, something reserved for IT departments and compliance checklists. Yet over 90 percent of security breaches start with human error or poorly managed policies. That flips everything you thought about cybersecurity on its head. The real difference comes not from fancy software but from setting up clear rules and training your people to outsmart threats as they evolve.
Table of Contents
- Key Elements Of An Effective I T Security Policy
- Aligning Security Policies With Business Objectives
- Best Practices For Implementation And Employee Training
- Policy Review, Compliance, And Continuous Improvement
Quick Summary
| Takeaway | Explanation |
|---|---|
| Conduct Comprehensive Risk Assessments | Thoroughly understand risks to create effective IT security policies focusing on vulnerabilities and impacts. |
| Implement Strict Access Controls | Utilize principles like least privilege and multi-factor authentication to secure access based on user roles. |
| Integrate Security with Business Objectives | Align IT security policies with business goals to enhance operational efficiencies while protecting assets. |
| Invest in Ongoing Employee Training | Develop continuous training programs to transform employees into proactive defenders of organizational security. |
| Establish a Culture of Continuous Improvement | Regularly assess and update policies to adapt to evolving threats and ensure compliance and effectiveness. |
Key Elements of an Effective I T Security Policy
Building a robust I T security policy requires a comprehensive approach that addresses the complex landscape of modern cybersecurity challenges. Organizations must develop a strategic framework that not only protects critical assets but also provides clear guidance for employees and stakeholders.
Comprehensive Risk Assessment and Governance
Effective I T security policies begin with a thorough understanding of organizational risk. The Software Engineering Institute at Carnegie Mellon University emphasizes the critical role of senior leadership in establishing a comprehensive cybersecurity governance structure. This involves identifying potential vulnerabilities, evaluating potential impacts, and creating a systematic approach to managing security risks.
Key components of a robust risk assessment include:
To help quickly compare and understand the critical elements of risk assessment and governance discussed in the article, the following summary table organizes the key components:
| Key Component | Description |
|---|---|
| Threat Identification | Mapping out potential security threats specific to the organization's infrastructure and industry |
| Asset Inventory | Documenting all critical digital and physical assets that require protection |
| Vulnerability Analysis | Conducting regular assessments to uncover potential weaknesses in existing systems |
- Threat Identification: Mapping out potential security threats specific to the organization's infrastructure and industry
- Asset Inventory: Documenting all critical digital and physical assets that require protection
- Vulnerability Analysis: Conducting regular assessments to uncover potential weaknesses in existing systems
Access Control and User Management
The National Center for Education Statistics highlights the importance of implementing strict access control mechanisms. The principle of least privilege becomes paramount in modern security strategies. This approach ensures that users are granted only the minimum level of access necessary to perform their specific job functions.
Implementing robust access control involves several critical strategies:
This table summarizes the main strategies for implementing robust access control and user management, making it easier to reference and compare them:
| Strategy | Key Focus |
|---|---|
| Identity Management | Comprehensive user authentication protocols |
| Multi Factor Authentication | Multiple verification steps for system access |
| Role Based Access Control | Access levels defined by organizational roles |
- Identity Management: Developing comprehensive user authentication protocols
- Multi Factor Authentication: Requiring multiple verification steps for system access
- Role Based Access Control: Defining specific access levels based on organizational roles
Continuous Monitoring and Policy Evolution
An effective I T security policy is never static. It requires continuous monitoring, regular updates, and a proactive approach to emerging security challenges. Organizations must establish mechanisms for ongoing assessment, employee training, and rapid response to potential security incidents.
Critical elements of continuous monitoring include:
- Regular Security Audits: Conducting comprehensive reviews of existing security measures
- Incident Response Planning: Developing clear protocols for addressing potential security breaches
- Employee Training Programs: Ensuring ongoing education about security best practices
Successful I T security policies go beyond mere technical configurations. They represent a holistic approach to protecting organizational assets, managing risks, and creating a culture of security awareness. By implementing these key elements, organizations can develop a resilient and adaptive security framework that responds effectively to the dynamic threat landscape.
Aligning Security Policies With Business Objectives
Creating an effective I T security policy requires more than technical safeguards. Organizations must strategically align their security approaches with overarching business objectives to ensure that protection mechanisms enhance rather than hinder operational efficiency.
Strategic Integration of Security Frameworks
The National Institute of Standards and Technology emphasizes the critical importance of integrating security policies seamlessly with organizational mission and strategic goals. This approach transforms security from a purely defensive mechanism to a strategic business enabler.
Successful strategic integration involves:
- Operational Alignment: Ensuring security protocols support core business processes
- Risk Balanced Approach: Developing security measures that protect assets without restricting innovation
- Compliance Considerations: Maintaining regulatory requirements while supporting business growth
Performance and Productivity Optimization
Effective security policies should not create barriers but instead facilitate smoother operational workflows. By understanding business objectives, organizations can design security frameworks that actively contribute to organizational performance. This means creating flexible policies that adapt to changing business needs while maintaining robust protective measures.
Key strategies for optimization include:
- Streamlined Access Controls: Designing permission structures that enable efficient work
- Intelligent Risk Management: Implementing security protocols that support rather than impede business activities
- Technology Integration: Selecting security tools that enhance rather than complicate existing technological ecosystems
Continuous Alignment and Adaptation
Business environments are dynamic, and security policies must evolve accordingly. Regular assessment and realignment ensure that security mechanisms remain relevant and effective. This requires ongoing communication between security teams, business leaders, and operational departments to maintain a holistic understanding of organizational objectives.
Critical adaptation elements include:
- Regular Policy Reviews: Conducting comprehensive assessments of existing security frameworks
- Stakeholder Engagement: Involving leadership from multiple departments in security policy development
- Metrics and Performance Tracking: Establishing clear indicators to measure security policy effectiveness
By treating security as a strategic business function rather than a standalone technical requirement, organizations can develop more comprehensive security approaches. This perspective transforms security from a cost center to a value generator, supporting business growth while protecting critical assets.
Ultimately, successful I T security policies are those that understand and support an organization's core mission. By aligning protection mechanisms with business objectives, companies can create resilient, adaptive security frameworks that drive both safety and strategic success.
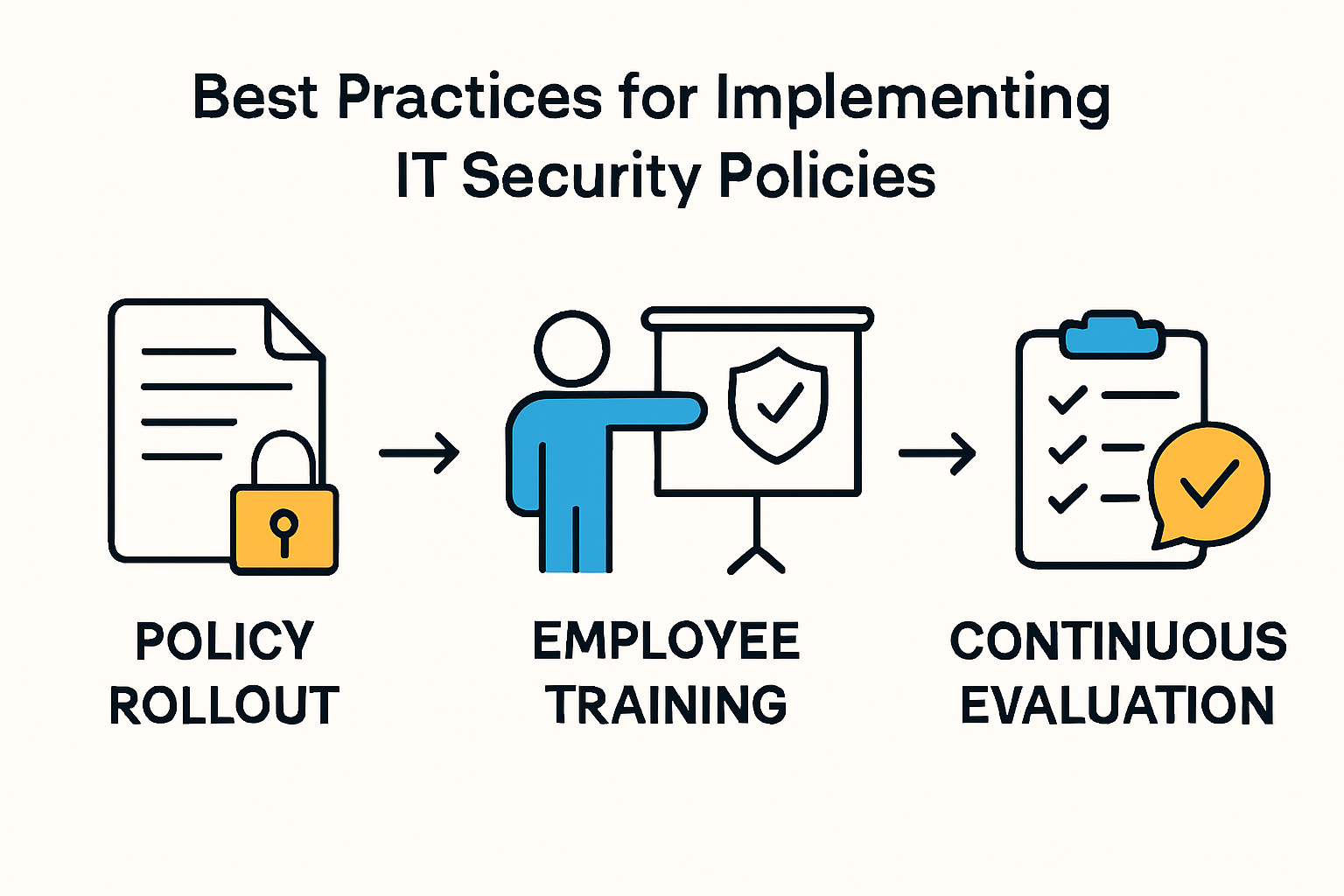
Best Practices for Implementation and Employee Training
Successful I T security policy implementation requires more than documentation. It demands a comprehensive strategy that transforms policy into actionable practices through systematic training and organizational commitment.
Structured Policy Rollout and Communication
The U.S. Department of Labor emphasizes the critical importance of developing a formal, well-documented cybersecurity program. Implementation is not a one-time event but a continuous process of communication, education, and reinforcement.
Key elements of an effective rollout include:
- Clear Documentation: Creating comprehensive yet understandable policy guidelines
- Staged Implementation: Introducing policy changes incrementally to minimize disruption
- Leadership Endorsement: Ensuring visible support from senior management
Comprehensive Employee Training Programs
Wayne State University recommends developing robust training initiatives that go beyond mere compliance. Effective security education transforms employees from potential vulnerabilities into active defenders of organizational assets.
Critical training components involve:
- Scenario Based Learning: Using realistic cybersecurity scenarios to demonstrate practical risks
- Interactive Workshops: Engaging employees through hands-on security simulations
- Role Specific Training: Customizing security education based on job responsibilities
Continuous Evaluation and Improvement
The National Institute of Standards and Technology highlights the importance of creating a dynamic security culture. Organizations must view security training as an ongoing process of assessment, learning, and adaptation.
Strategies for continuous improvement include:
- Regular Security Assessments: Conducting periodic evaluations of employee knowledge
- Feedback Mechanisms: Creating channels for employees to provide insights on policy effectiveness
- Adaptive Training Programs: Updating educational content to address emerging threats
Implementing an effective I T security policy requires a holistic approach that balances technical requirements with human factors. By investing in comprehensive training and creating a culture of security awareness, organizations can transform their workforce into a proactive line of defense against potential cyber threats.
Ultimately, successful implementation is not about rigid rules but about empowering employees to understand, internalize, and actively participate in protecting organizational assets. This approach turns security from a compliance requirement into a shared organizational value.
Policy Review, Compliance, and Continuous Improvement
Effective I T security policies are not static documents but dynamic frameworks that require ongoing evaluation, refinement, and adaptation. Organizations must develop robust mechanisms for continuous assessment and improvement to maintain their security posture in an ever-evolving technological landscape.
Systematic Policy Review and Assessment
Old Dominion University's IT Security Program Review standard emphasizes the critical importance of annual comprehensive reviews of information security programs. These assessments ensure policies remain suitable, adequate, and effective in addressing emerging technological and organizational challenges.
Key components of systematic policy review include:
- Comprehensive Evaluation: Conducting thorough assessments of existing security frameworks
- Contextual Analysis: Examining policy effectiveness against current business environments
- Regulatory Alignment: Ensuring continued compliance with industry and legal requirements
Continuous Monitoring and Risk Management
EDUCAUSE Review highlights the importance of an iterative approach to information security. This strategy involves continuous monitoring and incremental improvements that allow organizations to progressively strengthen their security infrastructure.
Effective continuous monitoring strategies involve:
- Real Time Risk Assessment: Implementing dynamic monitoring tools
- Incident Response Tracking: Documenting and analyzing security events
- Performance Metrics: Establishing quantifiable security effectiveness indicators
Compliance and Adaptive Improvement
NIST Special Publication 800-137A provides comprehensive guidance on developing robust Information Security Continuous Monitoring (ISCM) programs. This approach transforms compliance from a checkbox exercise to a strategic, proactive process of security enhancement.
Critical elements of adaptive improvement include:
- Regular Compliance Audits: Conducting systematic reviews of security protocols
- Emerging Threat Analysis: Continuously updating security measures based on evolving threat landscapes
- Technology Integration: Adapting policies to incorporate new security technologies and methodologies
Successful policy review goes beyond mere technical compliance. It requires a holistic approach that balances technological solutions, organizational processes, and human factors. By creating a culture of continuous improvement, organizations can develop resilient security frameworks that evolve alongside emerging challenges.

The ultimate goal of policy review is not perfection but perpetual adaptation. Security is a journey of ongoing learning, assessment, and strategic refinement. Organizations that embrace this philosophy transform their I T security policies from restrictive documents into dynamic, living strategies that protect and enable business growth.
Frequently Asked Questions
What are the key elements of an effective IT security policy?
Key elements include comprehensive risk assessment, access control and user management, continuous monitoring, and policy evolution.
How can organizations align their IT security policies with business objectives?
Organizations should ensure that security protocols support core business processes, maintain regulatory compliance, and develop a risk-balanced approach that does not restrict innovation.
What are the best practices for implementing IT security policies?
Best practices include structured policy rollout, comprehensive employee training programs, and continuous evaluation and improvement of security measures.
Why is continuous monitoring important in IT security?
Continuous monitoring is crucial as it allows organizations to quickly assess the effectiveness of security measures and adapt to new threats, ensuring a proactive approach to cybersecurity.
Accelerate Strong I T Security Policies With Proven Automation
Building an effective IT security policy often reveals a deeper struggle. It is not just about drafting rules. The ongoing headache is staying vigilant with continuous monitoring, compliance checks, and accurate communication across teams. As highlighted in the article, manual processes and human errors remain the top sources of risk and frustration, especially when completing endless security questionnaires or demonstrating policy alignment to clients and regulators.

Imagine reducing the time and stress spent managing security reviews while keeping your team focused on real security improvements. At Skypher, our AI-powered platform automates your security questionnaire responses, seamlessly connects with over 40 TPRM platforms, and powers faster, more accurate policy reviews. You can also centralize important trust documentation using our Custom Trust Center for enhanced transparency. Do not let outdated processes slow your progress.
Take the next step right now. See how Skypher can help you align your security policies with business objectives and turn compliance challenges into a competitive advantage.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- Smart Security Knowledge Base - Saasy - Webflow HTML Website Template
- The ever growing number of security questionnaires and what you and your company can do to face it
- Lalita Hardier - Saasy - Webflow HTML Website Template
