Organizations are facing cyber threats that evolve every hour. Companies without a robust Information Security Management System are at exponentially higher risk of data breaches and financial loss, according to Gartner. You might assume the biggest challenge is installing the latest security software or buying more firewalls. The real surprise is that the strength of your whole security posture hinges on how you manage people, processes, and risk—not just technology. Here is where most businesses overlook the actual game plan that makes or breaks information security in 2025.
Table of Contents
- Understanding Information Security Management Systems
- Key Components And Benefits Of An Isms
- Step-By-Step Process To Implement An Isms
- Best Practices For Maintaining Your Isms In 2025
Quick Summary
| Takeaway | Explanation |
|---|---|
| Risk Management is Central | An effective ISMS relies on systematic risk management to identify, assess, and mitigate security threats, ensuring a robust security infrastructure. |
| ISMS as a Strategic Asset | Organizations benefit from implementing an ISMS by enhancing risk management, ensuring regulatory compliance, and fostering stakeholder confidence, thus transforming security concerns into business advantages. |
| Continuous Improvement is Essential | Maintaining an ISMS requires ongoing assessments, employee training, and adaptive strategies to address evolving threats and technological landscapes, promoting a culture of proactive protection. |
| Collaboration is Key | Successful ISMS implementation involves multidisciplinary collaboration across technical experts, risk managers, and leadership to align security strategies with organizational objectives. |
| Adopt Advanced Security Mechanisms | Utilizing advanced authentication methods, comprehensive data protection strategies, and continuous monitoring fosters a dynamic security environment that adapts to individual user behaviors and threat scenarios. |
Understanding Information Security Management Systems
Information Security Management Systems (ISMS) represent a strategic approach to protecting an organization's most critical asset: its information. These comprehensive frameworks go beyond simple technology solutions, creating a holistic approach to managing and securing digital and physical information resources.
Core Components of an ISMS
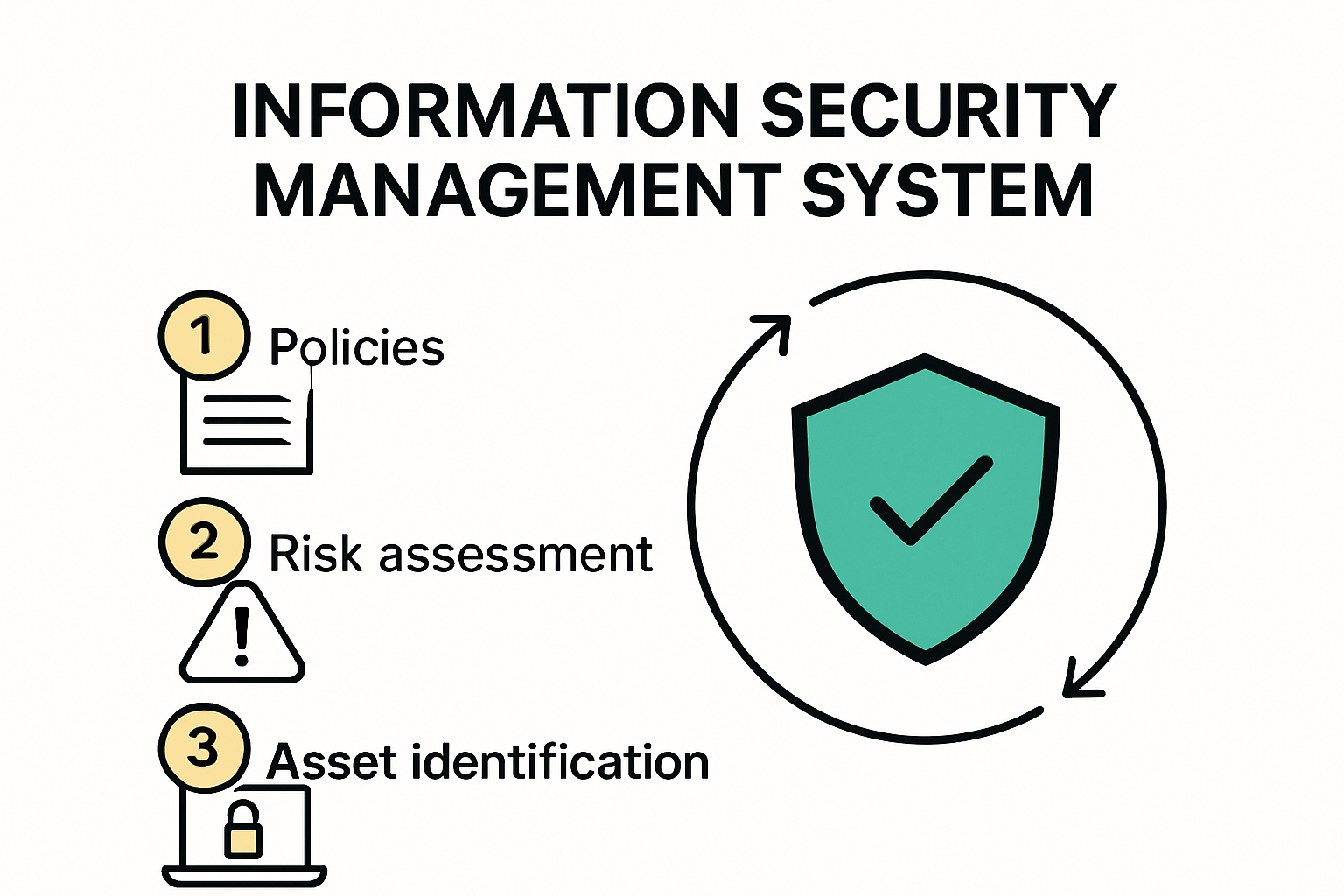
An effective Information Security Management System consists of interconnected elements that work together to create a robust security infrastructure. Risk management sits at the heart of this system, enabling organizations to identify, assess, and mitigate potential security threats systematically. According to International Organization for Standardization, an ISMS must include clear policies, defined processes, and continuous monitoring mechanisms.
The framework typically encompasses several critical dimensions:
- Policy Development: Establishing clear, actionable security guidelines that align with organizational objectives
- Asset Identification: Cataloging and classifying all information assets requiring protection
- Risk Assessment: Conducting comprehensive evaluations of potential security vulnerabilities
- Implementation of Controls: Deploying technical, administrative, and physical safeguards
Strategic Importance in Modern Organizations
In an era of increasing cyber threats, Information Security Management Systems have transformed from optional investments to mission critical strategies. Gartner Research indicates that organizations without comprehensive security management frameworks face exponentially higher risks of data breaches and financial losses.
The strategic value of an ISMS extends far beyond mere protection. It enables organizations to:
- Demonstrate compliance with regulatory requirements
- Build trust with customers and stakeholders
- Create a proactive security culture
- Reduce potential financial and reputational damages from security incidents
Modern ISMS approaches recognize that information security is not just a technological challenge but a complex organizational discipline. They integrate human factors, technological solutions, and strategic governance to create comprehensive protection strategies.
Implementing an effective Information Security Management System requires a multidisciplinary approach. Technical experts, risk managers, legal professionals, and executive leadership must collaborate to design, deploy, and maintain a robust security framework that adapts to evolving technological landscapes and emerging threat vectors.
While no security system can guarantee absolute protection, a well-designed ISMS significantly reduces an organization's vulnerability and enhances its ability to detect, respond to, and recover from potential security incidents. The key lies in continuous improvement, regular assessments, and a commitment to maintaining a dynamic and responsive security posture.
Key Components and Benefits of an ISMS
An Information Security Management System (ISMS) represents a sophisticated framework that goes far beyond basic technological solutions. By integrating multiple strategic components, organizations can create a comprehensive approach to protecting their most valuable digital assets.
Fundamental Components of ISMS
Effective Information Security Management Systems are built on a robust set of interconnected components that work synergistically to protect organizational information. According to Hyperproof, these critical elements include:
- Policy and Procedure Development: Creating clear, actionable guidelines that define security expectations and protocols
- Risk Assessment Processes: Systematically identifying, analyzing, and mitigating potential security vulnerabilities
- Access Control Mechanisms: Implementing strict authentication and authorization protocols to protect sensitive information
- Incident Response Planning: Developing comprehensive strategies for detecting, responding to, and recovering from security breaches

These components work together to create a dynamic and responsive security ecosystem. Neumetric emphasizes that successful implementation requires a holistic approach that integrates technological solutions with human expertise and organizational processes.
Strategic Benefits of ISMS Implementation
Organizations that successfully implement an Information Security Management System unlock multiple strategic advantages. Beyond basic protection, an ISMS provides comprehensive benefits that extend across multiple business dimensions:
- Enhanced Risk Management: Proactively identifying and mitigating potential security threats before they become critical issues
- Regulatory Compliance: Demonstrating adherence to international security standards and legal requirements
- Operational Efficiency: Streamlining security processes and reducing potential disruptions
- Stakeholder Confidence: Building trust with customers, partners, and investors through robust security practices
Research from Gartner suggests that organizations with comprehensive ISMS frameworks experience significantly reduced security incidents and improved overall operational resilience. The financial implications are substantial, with potential savings in risk mitigation and potential breach recovery.
Implementing an effective ISMS is not a one time event but a continuous journey of improvement. Organizations must commit to regular assessments, ongoing training, and adaptive strategies that evolve with changing technological landscapes and emerging threat vectors.
The most successful ISMS implementations recognize that information security is fundamentally a business strategy, not just a technical requirement. They integrate security considerations into every aspect of organizational decision making, creating a culture of proactive protection and continuous improvement.
While challenges exist in developing and maintaining an robust ISMS, the potential benefits far outweigh the initial investment. Organizations that approach information security as a strategic priority can transform potential vulnerabilities into opportunities for enhanced performance, innovation, and competitive advantage.
Step-by-Step Process to Implement an ISMS
Implementing an Information Security Management System (ISMS) requires a strategic, methodical approach that transforms organizational security from a reactive to a proactive discipline. The process demands comprehensive planning, stakeholder engagement, and a commitment to continuous improvement.
Establishing Foundational Objectives
Before diving into technical implementations, organizations must establish clear, measurable objectives for their ISMS. According to AuditBoard, this initial phase involves close collaboration with senior leadership to align security strategies with broader business goals.
Key considerations during objective setting include:
- Identifying Critical Information Assets: Cataloging sensitive data, systems, and processes that require protection
- Defining Organizational Risk Tolerance: Establishing acceptable risk levels and potential mitigation strategies
- Aligning with Business Strategy: Ensuring ISMS objectives support overall organizational growth and innovation
Successful objective setting requires a holistic view that transcends traditional IT security boundaries. TrustCloud recommends involving cross functional teams to create a comprehensive and nuanced understanding of organizational security needs.
Comprehensive Risk Assessment and Control Implementation
Risk assessment forms the cornerstone of an effective ISMS. Organizations must systematically identify, analyze, and evaluate potential security vulnerabilities across technological, human, and procedural domains. According to ISMS Online, the 2025 approach to risk management emphasizes addressing emerging challenges such as artificial intelligence and complex digital ecosystems.
The risk assessment process typically involves:
- Conducting detailed asset inventories
- Identifying potential threats and vulnerabilities
- Evaluating potential impact and likelihood of security incidents
- Developing targeted mitigation strategies
Following risk assessment, organizations must implement robust control mechanisms. These controls should be comprehensive, covering technical safeguards, administrative protocols, and physical security measures. The goal is creating a multi layered defense strategy that adapts to evolving threat landscapes.
Continuous Monitoring and Improvement
Implementing an ISMS is not a one time event but a continuous journey of refinement and adaptation. Regular audits, performance assessments, and iterative improvements are critical to maintaining an effective security posture.
Key elements of ongoing ISMS management include:
- Conducting periodic security assessments
- Updating risk management frameworks
- Providing continuous employee training
- Integrating emerging technological solutions
- Maintaining compliance with evolving regulatory standards
Organizations must foster a culture of security awareness where every team member understands their role in maintaining robust information protection. This requires transparent communication, regular training, and a commitment to learning from both successes and potential security incidents.
Successful ISMS implementation transforms information security from a technical requirement into a strategic organizational capability. By following a structured, comprehensive approach, organizations can build resilient security frameworks that protect critical assets while enabling innovation and growth.
Best Practices for Maintaining Your ISMS in 2025
Maintaining an Information Security Management System (ISMS) in 2025 requires a dynamic, adaptive approach that responds to rapidly evolving technological landscapes and emerging cyber threats. Organizations must move beyond static security models to create flexible, intelligent protection strategies.
Advanced Authentication and Access Control
In 2025, access management becomes increasingly sophisticated. Lumen Alta emphasizes the critical importance of implementing multi-factor authentication (MFA) across all critical systems. This approach significantly reduces unauthorized access risks by creating multiple verification layers.
Key authentication strategies include:
- Biometric Verification: Utilizing advanced facial recognition and fingerprint technologies
- Behavioral Authentication: Analyzing user interaction patterns to detect potential security anomalies
- Adaptive Authentication: Implementing context aware access controls that adjust security requirements based on user behavior and risk levels
These advanced authentication mechanisms go beyond traditional password protection, creating dynamic security environments that can adapt to individual user contexts and potential threat scenarios.
Data Protection and Encryption Strategies
Data protection in 2025 demands comprehensive encryption approaches that secure information across multiple dimensions. Faddom recommends a holistic encryption strategy that protects data at rest, in transit, and during processing.
Effective encryption practices include:
- Implementing end-to-end encryption for sensitive communications
- Using advanced encryption standards for stored data
- Developing robust key management protocols
- Protecting data across cloud, hybrid, and on-premises environments
Organizations must also focus on Zero Trust Architecture, which assumes no inherent trust in any network connection or user, requiring continuous verification for all access attempts.
Continuous Monitoring and Adaptive Framework Management
Successful ISMS maintenance in 2025 requires a proactive, intelligence-driven approach. NIST Cybersecurity Framework recommends continuous monitoring and adaptive risk management strategies that leverage artificial intelligence and machine learning technologies.
Critical components of adaptive ISMS management include:
- Automated threat detection and response systems
- Real-time security analytics
- Continuous vulnerability assessment
- Regular framework updates based on emerging threat intelligence
Organizations must cultivate a security culture that views information protection as a dynamic, collaborative process. This means investing in ongoing employee training, creating transparent communication channels, and developing agile response mechanisms.
The most successful ISMS implementations in 2025 will be those that balance technological sophistication with human expertise. By combining advanced technical solutions with strategic human insights, organizations can create robust, adaptive security ecosystems that protect against both known and emerging cyber threats.
Ultimately, maintaining an effective ISMS is not about achieving a static state of security, but about creating a continuous, evolving approach to information protection that can anticipate and respond to the complex digital challenges of the modern business environment.
Frequently Asked Questions
What is an Information Security Management System (ISMS)?
An Information Security Management System (ISMS) is a strategic framework that helps organizations protect their information assets through a systematic approach to managing risk, ensuring compliance, and establishing security policies and procedures.
Why is an ISMS important for organizations in 2025?
In 2025, an ISMS is crucial for organizations as it provides a structured way to identify, assess, and mitigate cyber threats, thus reducing the risk of data breaches and financial losses, while also demonstrating compliance with regulatory standards.
What are the key components of an ISMS?
Key components of an ISMS include policy and procedure development, risk assessment processes, access control mechanisms, incident response planning, and continuous monitoring and improvement of security practices.
How can organizations implement an ISMS effectively?
To implement an ISMS effectively, organizations should establish clear objectives, conduct comprehensive risk assessments, engage stakeholders across the organization, develop and deploy appropriate security controls, and commit to continuous monitoring and improvement of their security posture.
Ready to Turn Your ISMS Knowledge Into a Competitive Edge?
Building an effective Information Security Management System is more than a checklist. It means empowering your organization to handle risk, prove compliance, and foster trust—without getting buried in manual processes or endless security questionnaires. If the constant stress of keeping up with evolving threats and proving your security to clients feels draining, you're not alone. The article underscored that true risk management and stakeholder confidence depend on clear processes and automation, not more paperwork.

Let Skypher's AI-powered Questionnaire Automation Tool take the burden off your team's shoulders. Streamline security questionnaire responses, collaborate in real time, and showcase your compliance in a secure Custom Trust Center. Transform ISMS goals into real results by connecting with our solution today at Skypher. Your next audit or sales cycle could be your easiest yet—get started now and see efficiency in action.