ISO 27001 audits are often seen as intimidating hurdles for any organization focused on cybersecurity. Here is the twist. Over 80 percent of companies that adopt a proactive audit strategy discover threats they never expected. Yet, what surprises most people is that these audits are not just about ticking boxes for compliance. When done right, they can actually reveal opportunities for stronger trust, sharper risk management, and a real competitive edge.
Table of Contents
- Understanding ISO 27001 Audits And Their Purpose
- Step-By-Step ISO 27001 Audit Process Explained
- Essential Checklist For A Successful Audit
- Proven Strategies To Pass ISO 27001 Audits
Quick Summary
| Takeaway | Explanation |
|---|---|
| ISO 27001 Audits as Strategic Tools | ISO 27001 audits are critical processes that help organizations protect information assets, identify vulnerabilities, and demonstrate cybersecurity practices. They should be viewed as opportunities for strategic improvement rather than mere compliance exercises. |
| Two-Stage Certification Process | The ISO 27001 audit involves a two-stage certification process: the Stage 1 Audit, which reviews documentation, and the Stage 2 Audit, which assesses on-site implementation of security controls. Both stages are crucial for achieving certification. |
| Importance of Comprehensive Documentation | Developing and maintaining extensive documentation, including risk assessments and security policies, is vital for a successful ISO 27001 audit. This documentation reflects the organization's commitment to information security management. |
| Continuous Improvement and Compliance | Organizations must maintain ongoing compliance through surveillance audits, continuous improvement initiatives, and regular internal assessments to uphold their ISO 27001 certification status. |
| Cultural Commitment to Security | Cultivating a culture of security awareness through training and workshops is essential. Engaging employees in security practices ensures that information security is integrated into the organization's daily operations. |
Understanding ISO 27001 Audits and Their Purpose
ISO 27001 audits represent a critical process for organizations seeking to protect their information assets and demonstrate robust cybersecurity practices. These comprehensive evaluations systematically examine an organization's Information Security Management System (ISMS) to ensure it meets rigorous international standards for information protection and risk management.
The Core Purpose of ISO 27001 Audits
At its foundation, an ISO 27001 audit serves as a strategic mechanism for identifying and mitigating information security vulnerabilities. Research from the International Organization for Standardization reveals that these audits are not merely compliance exercises but comprehensive assessments that help organizations build resilient security frameworks.
The primary objectives of ISO 27001 audits include:
- Risk Assessment: Systematically identifying potential security threats and vulnerabilities within the organization's information systems
- Control Effectiveness: Evaluating the implementation and performance of existing security controls
- Continuous Improvement: Providing actionable insights for enhancing information security strategies
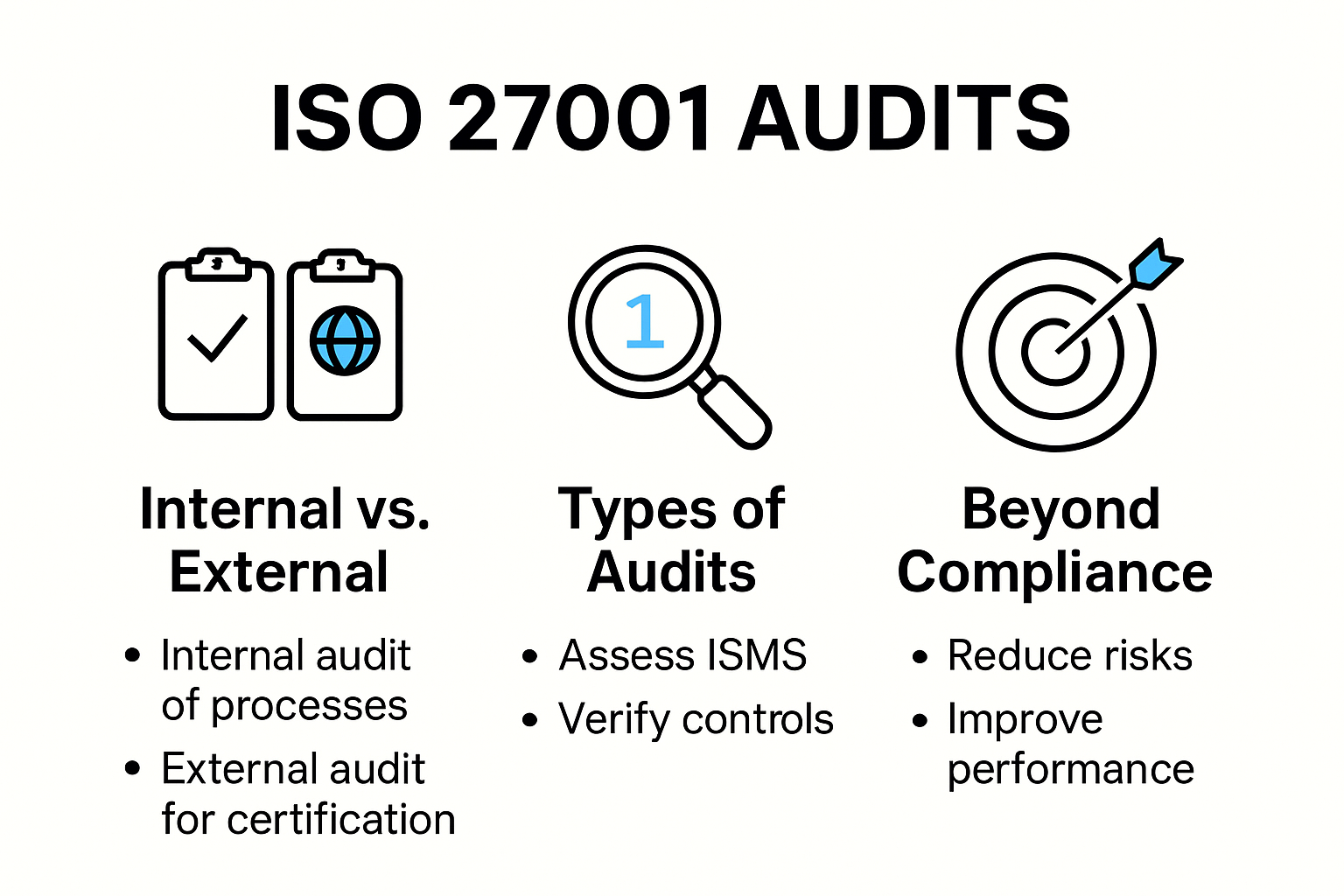
Audit Types and Their Significance
ISO 27001 audits typically encompass two primary variations: internal and external audits. Audit and Risk Management experts explain that each type plays a unique role in maintaining comprehensive information security.
Internal audits represent proactive self-assessments conducted by the organization's own personnel. These audits enable companies to:
- Identify potential security gaps before external assessments
- Validate the effectiveness of existing security protocols
- Prepare comprehensively for certification or recertification processes
External audits, conducted by independent certification bodies, provide an objective third-party evaluation of the organization's ISMS. These rigorous assessments determine whether an organization meets the stringent requirements for ISO 27001 certification.
To provide a clear comparison between internal and external ISO 27001 audits, the following table highlights their main characteristics and purposes:
| Audit Type | Who Conducts It | Main Purpose | Key Benefits |
|---|---|---|---|
| Internal Audit | Organization's own staff | Identify security gaps, validate protocols, prepare for certification | Early risk detection, cost-effective, builds audit readiness |
| External Audit | Independent certification body | Assessment for ISO 27001 certification | Objective certification, industry credibility, stakeholder assurance |
Strategic Benefits Beyond Compliance
Information Security Governance experts emphasize that ISO 27001 audits extend far beyond mere regulatory compliance. They represent a strategic approach to information security that delivers tangible organizational benefits.
Successful ISO 27001 audits demonstrate an organization's commitment to:
- Protecting sensitive information from potential breaches
- Building stakeholder trust through verified security practices
- Implementing systematic approaches to risk management
- Reducing potential financial and reputational damages from security incidents
Organizations that approach ISO 27001 audits as opportunities for strategic improvement rather than bureaucratic requirements will unlock significant value. These audits provide a structured methodology for continuously enhancing information security capabilities, ultimately creating more resilient and trustworthy technological ecosystems.
Step-by-Step ISO 27001 Audit Process Explained
The ISO 27001 audit process represents a meticulous journey through comprehensive information security assessments. Organizations embarking on this process must navigate a structured pathway that transforms their information security management system into a robust and compliant framework.
Preparing for the Audit Journey
Cybersecurity experts from CyberUpgrade emphasize that successful ISO 27001 audits begin with thorough preparation. The initial stage involves defining the precise scope of the Information Security Management System (ISMS).
Key preparatory activities include:
- Boundary Definition: Clearly identifying which organizational departments, processes, and technological systems will be included in the audit
- Risk Landscape Mapping: Conducting an extensive risk assessment to understand potential vulnerabilities
- Documentation Development: Creating comprehensive policies and procedures that align with ISO 27001 requirements

The Two-Stage Certification Audit Process
Insight Assurance professionals outline a critical two-stage certification audit approach that systematically evaluates an organization's information security practices.
Here is a summarized table outlining the two main stages of the ISO 27001 certification audit process and their specific focus areas:
| Stage | Focus Area | Main Activities |
|---|---|---|
| Stage 1 Audit | Documentation Review | Review ISMS documentation, check alignment to ISO 27001, identify gaps, assess readiness for on-site audit |
| Stage 2 Audit | On-Site Implementation | On-site evaluation, interview personnel, validate real application, examine evidence, determine certification readiness |
Stage 1 Audit (Documentation Review):
- Certification auditors perform a comprehensive review of the organization's ISMS documentation
- Verify alignment with ISO 27001 standard requirements
- Identify potential gaps or nonconformities in documented processes
- Assess the organization's readiness for the on-site assessment
Stage 2 Audit (On-Site Implementation Assessment):
- Auditors conduct detailed on-site evaluations
- Validate actual implementation of documented security controls
- Interview key personnel to understand practical application of security protocols
- Examine evidence of effective information security practices
- Determine whether the organization meets full certification requirements
Maintaining Continuous Compliance
Wikipedia's Information Security research highlights that ISO 27001 certification is not a one-time achievement but an ongoing commitment to information security excellence.
Post-certification activities include:
- Surveillance Audits: Regular periodic assessments to ensure continued compliance
- Continuous Improvement: Implementing feedback and addressing identified vulnerabilities
- Annual Recertification: Comprehensive reviews to maintain certification status
Successful organizations approach ISO 27001 audits as strategic opportunities for enhancing their information security posture. By treating these audits as more than mere compliance exercises, they transform potential challenges into pathways for organizational resilience and technological trust.
Essential Checklist for a Successful Audit
Navigating an ISO 27001 audit requires meticulous preparation and a strategic approach to demonstrating information security excellence. A comprehensive checklist serves as a critical roadmap for organizations seeking to successfully pass their certification assessment.
Foundational Documentation Preparation
IT Governance experts emphasize the critical importance of comprehensive documentation in preparing for an ISO 27001 audit. Organizations must develop and maintain a robust set of documents that clearly articulate their Information Security Management System (ISMS).
Key documentation requirements include:
- Risk Assessment Documentation: Detailed records of identified risks, their potential impact, and selected mitigation strategies
- Policy Frameworks: Comprehensive security policies covering information protection, access control, and incident response
- Evidence of Implementation: Concrete proof of how security controls are actually being executed within the organization
Critical Control and Compliance Verification
ISMS Online security experts recommend a systematic approach to verifying information security controls. This involves a comprehensive review of the organization's security mechanisms across multiple dimensions.
Essential verification points include:
- Access Control Systems: Validate user authentication processes, password policies, and access management protocols
- Asset Management: Maintain a comprehensive inventory of all information assets and their associated security requirements
- Operational Security Protocols: Demonstrate robust procedures for handling sensitive information, managing technological resources, and protecting critical systems
Continuous Improvement and Audit Readiness
Information Security Governance professionals highlight that successful ISO 27001 audits are not about achieving a one-time certification but maintaining an ongoing commitment to information security excellence.
Key strategies for maintaining audit readiness include:
- Regular Internal Audits: Conduct periodic self-assessments to identify and address potential vulnerabilities
- Management Review: Implement systematic processes for senior leadership to review and validate the effectiveness of the ISMS
- Continuous Training: Develop ongoing employee education programs to ensure consistent understanding of security protocols
The Statement of Applicability (SoA) represents a critical document in this process. This comprehensive document details which security controls have been implemented, why they were selected, and how they align with the organization's specific risk landscape.
Organizations that approach ISO 27001 audits as more than a compliance exercise will transform these assessments into strategic opportunities for enhancing their overall information security posture. By maintaining a proactive, comprehensive approach to documentation, control verification, and continuous improvement, businesses can demonstrate their commitment to protecting critical information assets and building stakeholder trust.
Proven Strategies to Pass ISO 27001 Audits
Successfully navigating ISO 27001 audits requires a strategic and proactive approach to information security management. Organizations must develop comprehensive strategies that demonstrate not just compliance, but a genuine commitment to protecting critical information assets.
Building a Robust Risk Management Framework
NordLayer cybersecurity experts emphasize the critical importance of developing a comprehensive risk assessment strategy. This involves creating a systematic approach to identifying, analyzing, and mitigating potential security vulnerabilities.
Key elements of an effective risk management framework include:
- Systematic Risk Identification: Conducting thorough and regular assessments of potential security threats
- Impact Analysis: Evaluating the potential consequences of identified risks
- Risk Treatment Planning: Developing targeted strategies to mitigate or eliminate identified security risks
Implementing a Comprehensive Information Security Management System
Information Security Professionals recommend developing a holistic Information Security Management System (ISMS) that goes beyond simple compliance. This approach requires creating a comprehensive framework that addresses multiple dimensions of information security.
Critical components of an effective ISMS include:
- Clear Policy Development: Establishing well-defined, comprehensive security policies
- Documented Procedures: Creating detailed guidelines for managing information security
- Continuous Improvement Mechanisms: Implementing processes for ongoing system evaluation and enhancement
Cultivating a Culture of Security Awareness
Cybersecurity Training Experts highlight the crucial role of human factors in information security. Successful ISO 27001 audits depend not just on technical controls, but on creating a organization-wide culture of security awareness.
Strategic approaches to building security awareness include:
- Comprehensive Training Programs: Developing ongoing education initiatives for all employees
- Regular Security Workshops: Conducting interactive sessions to reinforce security protocols
- Simulated Security Scenarios: Creating practical exercises that test and improve employee response to potential security threats
Successful organizations understand that passing an ISO 27001 audit is more than a technical exercise. It requires a holistic approach that combines robust technical controls, comprehensive documentation, and a deeply ingrained culture of information security.
By treating the audit as an opportunity for continuous improvement rather than a mere compliance checkbox, organizations can transform their approach to information security. This proactive strategy not only helps pass audits but creates a resilient security posture that protects critical assets and builds stakeholder confidence.
Frequently Asked Questions
What is the purpose of ISO 27001 audits?
ISO 27001 audits aim to evaluate an organization's Information Security Management System (ISMS), identify security vulnerabilities, assess the effectiveness of existing controls, and ensure compliance with international standards.
How does the ISO 27001 certification process work?
The ISO 27001 certification process consists of two stages: Stage 1 involves a documentation review to assess readiness, while Stage 2 includes an on-site evaluation of the implemented security measures and practices.
What should my organization do to prepare for an ISO 27001 audit?
To prepare for an ISO 27001 audit, organizations should define the scope of the ISMS, conduct a risk assessment, develop comprehensive documentation, and ensure all security controls are effectively implemented and tested.
How can we maintain continuous compliance after achieving ISO 27001 certification?
Organizations can maintain continuous compliance by conducting regular surveillance audits, implementing continuous improvement initiatives, and performing internal assessments to address any vulnerabilities or non-conformities.
Transform Your ISO 27001 Audit Experience with Skypher
Many organizations face long hours and constant stress preparing for ISO 27001 audits because of manual document checks and repetitive security questionnaires. You already know how burdensome it can be to keep up with extensive documentation and ensure your audit readiness is up to standard. Missing just a single detail can put both your compliance and client trust at risk.

Take the pressure off your team and simplify your audit preparation with Skypher. Our AI-powered platform automates your security questionnaire process and centralizes key ISMS documents, so you can demonstrate compliance with confidence. Enjoy faster response times, seamless integration with over 40 risk management tools, plus real-time collaboration for your whole team—all features designed to support organizations preparing for audits like ISO 27001. Experience how easy it is to connect your documentation, proof, and controls by starting with Skypher’s automation tools today. Do not let tedious processes delay your audit success. Get started now and turn your next audit into an opportunity for real operational improvement.
