Did you know that over 70 percent of data breaches are linked to poor security protocols or misunderstood compliance requirements? In an era where cyber threats can cripple businesses overnight, understanding how ISO 27001 certification really works matters more than ever. Many companies believe myths about its complexity and cost, missing out on practical tools for protecting sensitive data, ensuring resilience, and building trust with clients and partners.
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive Framework | ISO 27001 is not just a compliance checkbox; it provides a holistic framework for effective information security management applicable to all organization sizes. |
| Continuous Journey | Achieving ISO 27001 certification is an ongoing commitment requiring regular assessments, risk management updates, and proactive practices. |
| Rigorous Documentation | Successful certification mandates specific, detailed documentation and records that reflect actual practices and facilitate continuous improvement. |
| Strategic Advantage | Certification bolsters competitive differentiation by demonstrating robust security measures, enhancing trust with clients and stakeholders. |
Table of Contents
- ISO 27001 Certification Explained And Common Myths
- Key Requirements And Documentation Standards
- Certification Process And Audit Steps
- Benefits For Tech And Finance Organizations
- Risks, Costs, And Common Pitfalls
ISO 27001 Certification Explained and Common Myths
ISO 27001 is a global standard for information security management that helps organizations protect sensitive data and manage cybersecurity risks systematically. Contrary to popular misconceptions, this certification is not just a document or compliance checkbox but a comprehensive framework applicable to businesses of all sizes. According to research from ISMS Online, the standard is scalable and cost-effective for organizations ranging from small startups to large enterprises.
Several persistent myths surround ISO 27001 certification that can mislead organizations. First, many believe it's exclusively for large corporations with extensive IT departments. This is false. Information security management is crucial for every organization, regardless of size. Another common misconception is that ISO 27001 is primarily about creating extensive documentation. In reality, the documentation must reflect actual operational practices and risk management strategies.
The most critical misunderstanding is viewing ISO 27001 certification as a one-time achievement rather than an ongoing process. ISOSerious emphasizes that certification marks the beginning of a continuous improvement journey. Organizations must:
- Regularly assess and update security protocols
- Conduct periodic risk assessments
- Maintain a proactive approach to information security
- Adapt to evolving technological and threat landscapes
By understanding these nuances, businesses can transform ISO 27001 from a compliance requirement into a strategic framework for robust information security management.
Key Requirements and Documentation Standards
ISO 27001 certification demands a comprehensive and structured approach to information security management. According to DSA LTA, the standard requires organizations to develop a systematic framework that goes far beyond simple documentation. Information Security Management Systems (ISMS) must include formal risk assessments, clear policies, internal audits, and continuous improvement mechanisms.
The documentation standards are rigorous and specific. 27001 Store highlights the mandatory documents organizations must prepare, which include:
- ISMS scope definition
- Comprehensive security policy
- Clearly defined security objectives
- Detailed risk assessment methodology
- Statement of Applicability (SoA)
- Comprehensive risk treatment plan
- Formal risk assessment report
Beyond documentation, organizations must maintain critical records demonstrating their commitment to information security. These include training documentation, audit results, management review outcomes, and records of corrective actions. The goal is not just to create paperwork, but to establish a living, breathing system that evolves with emerging technological and security challenges.
Here's a summary of key ISO 27001 documentation requirements and supporting records:
| Mandatory Documents | Description | Example Records |
|---|---|---|
| ISMS Scope Definition | Defines boundaries of ISMS | Scope statement |
| Security Policy | Organization's security principles | Security policy document |
| Security Objectives | Measurable security goals | Objectives tracking sheet |
| Risk Assessment Methodology | Approach for assessing risk | Risk assessment results |
| Statement of Applicability (SoA) | Lists applicable controls | SoA matrix |
| Risk Treatment Plan | Actions to address risks | Risk treatment tracking |
| Risk Assessment Report | Summary of identified risks | Audit and review logs |
| Management Review Outcomes | Results from management reviews | Review meeting minutes |
| Training Documentation | Staff security awareness records | Training logs<br>Certificates |
| Audit and Corrective Actions | Records of ISMS audits | Audit reports<br>Action logs |
Successful implementation requires more than checking boxes. Organizations must integrate these requirements into their operational DNA, ensuring that security isn't an afterthought but a fundamental aspect of their business strategy. This means regular reviews, continuous learning, and a proactive approach to identifying and mitigating potential security risks.

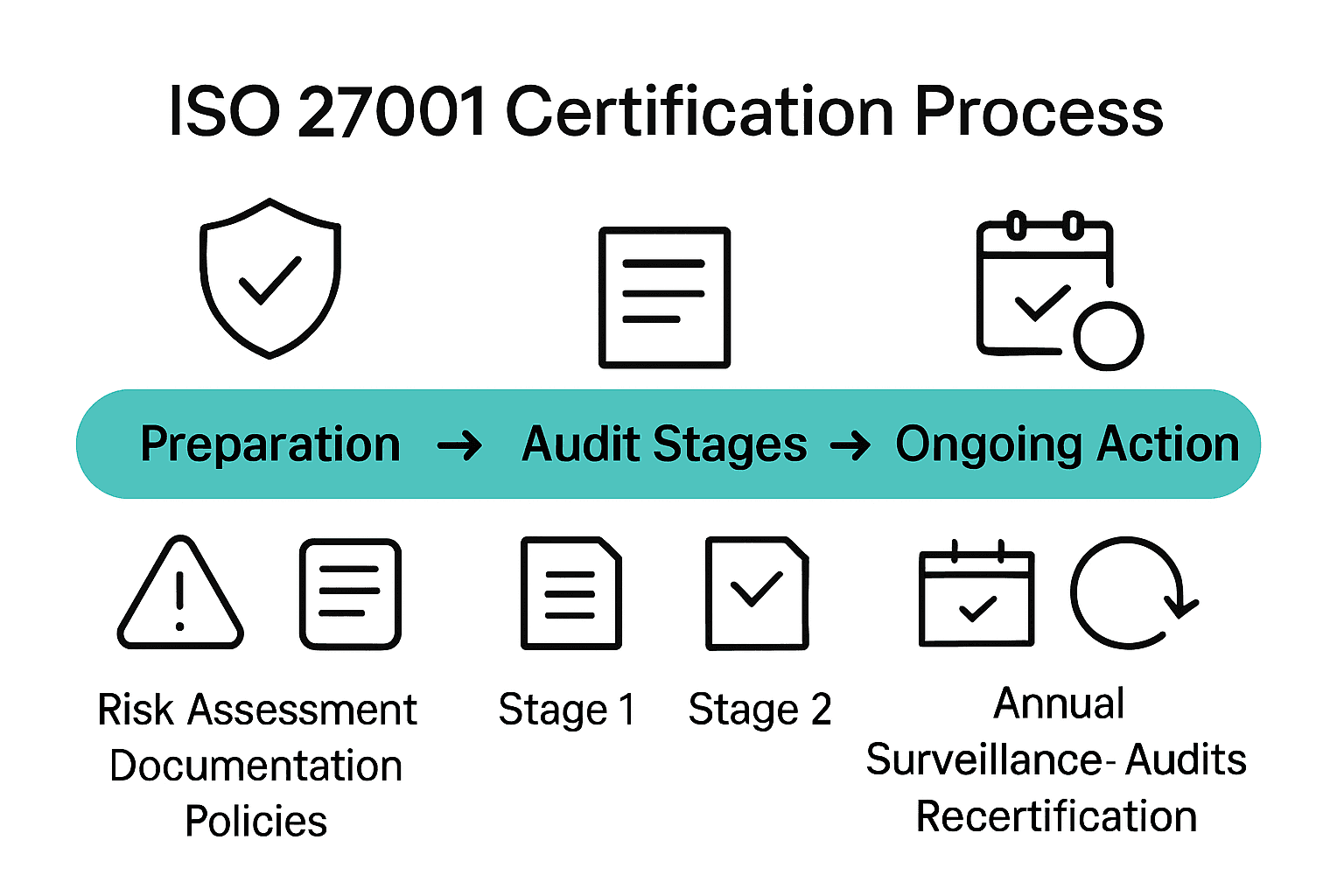
Certification Process and Audit Steps
The ISO 27001 certification journey is a structured, multi-stage process that demands meticulous planning and execution. According to Insight Assurance, organizations must navigate a comprehensive pathway to achieve and maintain certification. The process begins with implementing robust risk treatments and controls, followed by developing detailed documentation that aligns with the Statement of Applicability (SoA).
Secureframe outlines the critical audit phases that organizations will encounter. The certification process typically involves:
- Stage 1 Audit: ISMS Design Review
- Comprehensive documentation examination
- Initial assessment of information security framework
- Identification of potential gaps and improvement areas
- Stage 2 Audit: Certification Implementation Review
- Detailed evaluation of actual implementation
- Verification of Annex A controls
- On-site process and control effectiveness assessment
The certification is not a one-time achievement but an ongoing commitment. After initial certification, organizations must undergo annual surveillance audits to maintain their status. These periodic reviews ensure continuous compliance and provide opportunities for ongoing improvement of the Information Security Management System.
The final stage involves a recertification audit conducted at the end of the three-year certification period.
 This comprehensive review reassesses the organization's entire information security approach, requiring demonstrable evidence of continuous improvement, risk management, and adherence to ISO 27001 standards. Successful navigation of these steps transforms certification from a compliance exercise into a strategic approach to information security management.
This comprehensive review reassesses the organization's entire information security approach, requiring demonstrable evidence of continuous improvement, risk management, and adherence to ISO 27001 standards. Successful navigation of these steps transforms certification from a compliance exercise into a strategic approach to information security management.
Benefits for Tech and Finance Organizations
ISO 27001 certification delivers transformative advantages for tech and finance organizations navigating increasingly complex cybersecurity landscapes. According to 4C Partners, the certification enables companies to demonstrate compliance with critical global regulations like GDPR and HIPAA, while simultaneously building robust trust with clients and stakeholders who demand rigorous security protocols.
Competitive Differentiation emerges as a key benefit. Deloitte emphasizes that certification is more than a compliance checkbox—it's a strategic tool that enhances organizational resilience. The framework provides tangible advantages such as:
- Proactive risk management approach
- Reduced potential financial losses from security breaches
- Simplified regulatory compliance processes
- Enhanced stakeholder confidence
- Systematic approach to information security
For tech and finance sectors, where data is the most critical asset, ISO 27001 certification offers a structured methodology to protect sensitive information. The standard enables organizations to implement comprehensive risk assessment processes, create scalable security frameworks, and demonstrate a commitment to protecting client and organizational data. This approach not only mitigates potential security threats but also positions companies as responsible, forward-thinking industry leaders who prioritize comprehensive security strategies.
Ultimately, ISO 27001 certification transforms information security from a technical requirement into a strategic business advantage. Organizations gain a competitive edge by showcasing their ability to manage risks systematically, protect critical assets, and maintain the highest standards of information security in an increasingly complex digital ecosystem.
Risks, Costs, and Common Pitfalls
Pursuing ISO 27001 certification is not without its challenges. According to NQA, organizations frequently encounter critical pitfalls that can derail their information security management efforts. The most significant risks stem from insufficient top-management engagement, superficial risk assessments, and a failure to integrate the Information Security Management System (ISMS) comprehensively into existing organizational processes.
Implementation Challenges are multifaceted. 10 Factor Infra highlights three primary obstacles organizations must navigate:
- Resource constraints (financial and human capital)
- Complex integration with existing business processes
- Overwhelming documentation requirements
- Uncertain immediate return on investment
- High costs of consulting, audits, and implementation tools
The most common pitfalls organizations encounter include neglecting ongoing improvement, creating poorly documented processes, and treating the ISMS as an isolated compliance exercise. This approach undermines the fundamental purpose of ISO 27001: creating a dynamic, adaptive security framework. Companies often make critical mistakes such as under-resourcing their information security teams, providing inadequate staff training, and overlooking third-party security risks.
Successful ISO 27001 implementation requires a strategic, holistic approach. Organizations must view certification as a continuous journey rather than a destination. This means dedicating sufficient resources, maintaining leadership commitment, conducting thorough and realistic risk assessments, and creating a culture of ongoing security awareness and improvement. The investment, while substantial, ultimately provides significant long-term value in risk mitigation and organizational resilience.
Turn ISO 27001 Security Demands Into a Competitive Advantage
Preparing for ISO 27001 certification can feel overwhelming. The article highlights the burden of documentation, ever-changing compliance requirements, and the need for ongoing evidence of robust information security practices. For tech and finance organizations, the pressure to complete security questionnaires quickly and accurately is another obstacle. Inefficiencies here can lead to lost deals, delayed contracts, and undercut the trust you are working to build.

Experience how Skypher transforms ISO 27001 challenges into opportunities. With our AI-powered Questionnaire Automation Tool, you can answer hundreds of security questions in minutes, effortlessly support your ISO 27001 documentation, and maintain flawless audit trails. Real-time collaboration and integrations with over 30 essential risk management platforms mean you spend less time wrestling with compliance and more time focusing on innovation.
Make your next audit or security review faster, smarter, and less stressful. Discover the full impact of automation and see how your team can move from compliance pressure to proof of trust. Get started at Skypher.
Frequently Asked Questions
What is ISO 27001 certification?
ISO 27001 certification is a global standard for information security management that helps organizations systematically protect sensitive data and manage cybersecurity risks.
Who can benefit from ISO 27001 certification?
ISO 27001 certification is applicable to organizations of all sizes and is beneficial for both large corporations and small businesses aiming to strengthen their information security management practices.
What are the key documentation requirements for ISO 27001?
Key documentation requirements for ISO 27001 include defining the ISMS scope, developing a comprehensive security policy, establishing security objectives, conducting risk assessments, and maintaining records of audits and corrective actions.
How long does the ISO 27001 certification process take?
The ISO 27001 certification process typically involves a multi-stage approach, including Stage 1 and Stage 2 audits, and requires ongoing surveillance audits annually to maintain certification, with a full recertification occurring at the end of the three-year certification period.
Recommended
- Understanding SOC 2 AICPA: Your Guide to Compliance
- Understanding SOC II Type 1: What You Need to Know
- Understanding SOC 1 Compliance: Key Concepts Explained
- 7 Steps to Create a Complete SOC 2 Compliance Checklist
- Understanding SSAIB Compliance: Safeguarding Your Security System - 247 CCTV Security Ltd
