Over half of American businesses now identify ISO 27001 certification as a key hiring requirement for information security roles. Protecting sensitive data is no longer just a corporate issue. For individuals, gaining this globally recognized certification means direct access to top jobs and greater professional credibility. This guide reveals what you need to know about the certification process, types of credentials, and how American professionals use ISO 27001 to advance their careers in a rapidly evolving digital world.
Table of Contents
- ISO 27001 Certification Basics For Individuals
- Types Of ISO 27001 Certifications Available
- Key Skills And Knowledge Areas Covered
- Certification Process And Eligibility Requirements
- Career Benefits And Real-World Job Applications
- Common Challenges And How To Overcome Them
Key Takeaways
| Point | Details |
|---|---|
| Value of ISO 27001 Certification | ISO 27001 certification validates expertise in managing information security management systems, enhancing career prospects in cybersecurity and related sectors. |
| Certification Pathways | Multiple certification levels, including Foundation, Lead Implementer, and Master, cater to varying skill levels and professional objectives. |
| Key Skills Required | Emphasis on both technical knowledge and soft skills is vital for effectively implementing and managing information security protocols. |
| Overcoming Challenges | Candidates often face challenges with knowledge complexity and professional experience; strategic preparation and continuous learning are crucial for success. |
ISO 27001 Certification Basics for Individuals
The ISO 27001 certification represents a critical professional credential for cybersecurity and information security professionals seeking to validate their expertise in managing information security management systems (ISMS). ISO/IEC 27001 is an international standard that provides a comprehensive framework for establishing, implementing, and continuously improving organizational information security protocols.
Individuals pursuing this certification can expect a rigorous process that tests their understanding of information security principles, risk management strategies, and best practices. The certification demonstrates proficiency in developing and maintaining robust security frameworks that protect sensitive organizational data. Key competencies assessed include understanding system controls, implementing security policies, managing potential vulnerabilities, and creating comprehensive risk mitigation strategies.
The certification process typically involves several critical steps for candidates:
- Completing a recognized training program
- Passing a standardized examination
- Demonstrating practical knowledge of information security concepts
- Meeting specific professional experience requirements
Professionals across various sectors find the ISO 27001 certification valuable, including:
- Information Security Managers
- Cybersecurity Professionals
- Risk Management Specialists
- Compliance Officers
- IT Auditors
By obtaining this ISO 27001 certification, individuals signal their commitment to maintaining the highest standards of information security practices, making themselves more attractive to potential employers and demonstrating advanced technical competence in an increasingly complex digital landscape.
Types of ISO 27001 Certifications Available
ISO 27001 certifications offer professionals multiple pathways to demonstrate their expertise in information security management. PECB provides a comprehensive range of certifications designed to validate skills across different professional roles and organizational needs, ensuring individuals can showcase their specific competencies in information security.
The primary certification levels typically include:
- Foundation Level: An entry-level certification introducing fundamental ISMS concepts
- Lead Implementer: Focuses on practical skills for designing and implementing information security management systems
- Lead Auditor: Prepares professionals to conduct comprehensive security audits and assessments
- Master Certification: Advanced credential demonstrating comprehensive knowledge of complex ISMS frameworks
Each certification level targets different professional objectives and skill sets. The Foundation Level provides basic theoretical knowledge, while Lead Implementer certifications emphasize hands-on implementation strategies. Advanced credentials like the Master Certification are tailored for seasoned professionals seeking to demonstrate deep, strategic understanding of information security management.

Professionals can strategically choose certifications based on their career trajectory and organizational requirements. For instance, IT security specialists might pursue Lead Auditor credentials, while management-track professionals could benefit from the comprehensive Master Certification. Each certification requires specific training, examinations, and often proof of professional experience, ensuring that certified individuals maintain rigorous professional standards.
The certification landscape continues to evolve, with emerging compliance standards like SOC II complementing traditional ISO 27001 frameworks. This dynamic environment underscores the importance of continuous learning and professional development in information security management.
Key Skills and Knowledge Areas Covered
Information security management demands a comprehensive skill set that extends far beyond technical knowledge. PECB certification handbooks outline critical competency domains that professionals must master to effectively protect organizational information assets and implement robust security frameworks.
The key knowledge areas typically encompass:
- Information Security Fundamentals
- Risk assessment methodologies
- Security control frameworks
- Threat landscape analysis
- Technical Implementation Skills
- ISMS design and architecture
- Security policy development
- Control implementation strategies
- Governance and Compliance
- Regulatory requirement understanding
- Audit preparation techniques
- Continuous improvement frameworks
Lead Implementer certifications focus specifically on practical skills for designing, implementing, and maintaining information security management systems. Professionals must demonstrate proficiency in strategic planning, risk mitigation, and creating adaptive security frameworks that can evolve with emerging technological challenges.
Beyond technical competencies, successful information security professionals must cultivate critical soft skills. These include strategic communication, cross-functional collaboration, problem-solving under pressure, and the ability to translate complex technical concepts for non-technical stakeholders. Emerging compliance standards like SOC II further emphasize the need for holistic, adaptive security expertise that balances technical precision with strategic organizational understanding.
Certification Process and Eligibility Requirements
ISO 27001 certifications represent a structured professional pathway with clearly defined requirements and comprehensive evaluation processes. The certification journey begins with a rigorous application and assessment procedure designed to ensure only qualified professionals receive professional credentials in information security management.
The typical certification process involves several key stages:
- Professional Preparation
- Complete authorized training program
- Develop comprehensive understanding of ISMS frameworks
- Accumulate relevant professional experience
- Examination
- Pass standardized certification exam
- Demonstrate theoretical and practical knowledge
- Meet minimum score requirements
- Application Submission
- Create online certification account
- Submit professional documentation
- Undergo detailed eligibility review
Candidates must meet specific professional experience requirements that vary depending on the certification level. Entry-level certifications typically require minimal professional experience, while advanced credentials demand substantial documented experience in information security management, risk assessment, and ISMS implementation.
Eligibility criteria generally encompass educational background, professional training, and practical work experience. Professionals from diverse backgrounds including IT, cybersecurity, risk management, and compliance can pursue these certifications. Emerging compliance frameworks like SOC II complement these certification pathways, creating comprehensive professional development opportunities for information security specialists.
Career Benefits and Real-World Job Applications
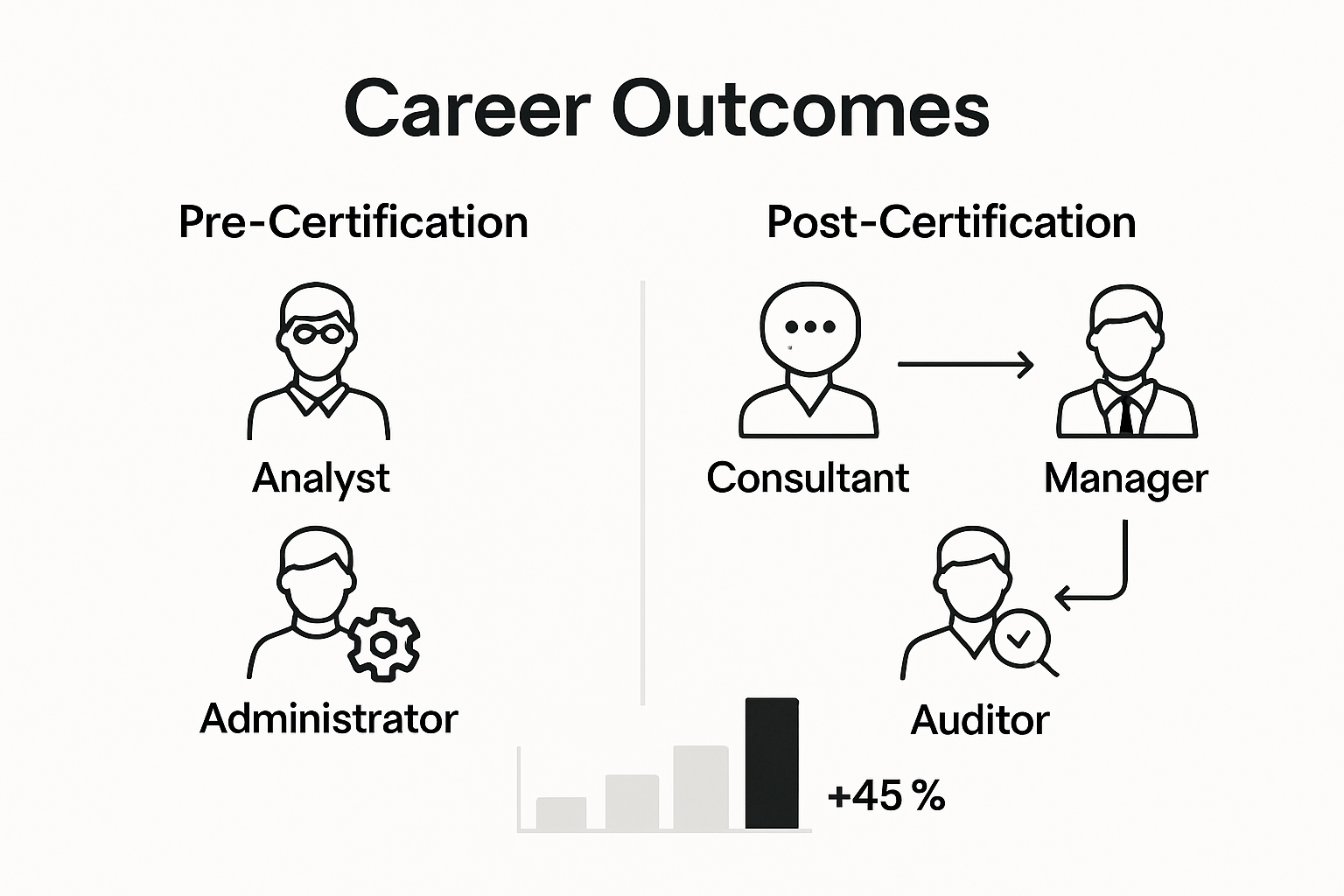
ISO 27001 certification transforms professional trajectories by providing a strategic credential that demonstrates advanced information security expertise. Certification significantly enhances career prospects by validating an individual's comprehensive understanding of information security management systems across diverse industry landscapes.
Potential career opportunities for certified professionals include:
- Security Leadership Roles
- Information Security Manager
- Chief Information Security Officer (CISO)
- Cybersecurity Strategy Director
- Technical Specialist Positions
- Security Architect
- Compliance Officer
- Risk Management Analyst
- Consulting and Advisory Positions
- Information Security Consultant
- Governance and Compliance Advisor
- Third-Party Risk Management Specialist
The Master certification specifically positions professionals for advanced leadership roles, signaling deep expertise in developing, implementing, and managing sophisticated information security frameworks. Certified individuals typically command higher salaries, with advanced certifications potentially increasing earning potential by 20-30% compared to non-certified counterparts.
Beyond immediate career opportunities, emerging compliance frameworks like SOC II demonstrate the growing complexity of information security ecosystems. Professionals with ISO 27001 certification are uniquely positioned to navigate these intricate regulatory landscapes, offering organizations strategic insights into protecting critical digital assets and managing evolving cybersecurity challenges.
Common Challenges and How to Overcome Them
ISO 27001 certification presents a complex journey with multiple potential obstacles for professionals seeking to advance their information security credentials. Candidates frequently encounter significant challenges throughout the certification process that require strategic preparation, continuous learning, and proactive problem-solving approaches.
Key challenges and strategic solutions include:
- Knowledge Complexity
- Challenge: Understanding intricate ISMS frameworks
- Solution: Comprehensive training programs
- Approach: Structured self-study and practical workshops
- Professional Experience Requirements
- Challenge: Meeting specific work experience criteria
- Solution: Strategic career planning
- Approach: Targeted role selection and skill development
- Technical Implementation
- Challenge: Applying theoretical knowledge practically
- Solution: Hands-on training and simulations
- Approach: Real-world project involvement
Certification candidates must carefully navigate professional experience requirements that demand both theoretical understanding and practical application. Successful professionals develop a multifaceted approach, combining structured learning with continuous professional development and active engagement in information security projects.
Ultimately, overcoming certification challenges requires a holistic strategy that integrates theoretical knowledge, practical skills, and ongoing learning. Emerging compliance frameworks like SOC II underscore the importance of adaptability and continuous improvement in the dynamic information security landscape. Professionals who view certification as a journey of continuous growth, rather than a singular achievement, are best positioned to excel in this rapidly evolving field.
Accelerate Your ISO 27001 Certification Journey with Skypher
Achieving ISO 27001 certification demands precise knowledge, practical skills, and the ability to manage complex security questionnaires effectively. Professionals face challenges like navigating intricate ISMS frameworks and meeting stringent compliance requirements. Skypher’s AI Questionnaire Automation Tool is designed to eliminate these hurdles by automating the entire security review process, allowing you to focus on mastering your certification content and advancing your career.

Experience how Skypher streamlines responses to security questionnaires with lightning-fast AI-powered automation, real-time collaboration features, and seamless API integrations with over 40 third-party risk management platforms. Prepare for your ISO 27001 exams more efficiently and showcase your expertise with confidence. Start transforming your information security workflow today by visiting Skypher and discover how our advanced platform supports your certification and long-term career success.
Frequently Asked Questions
What is ISO 27001 certification?
ISO 27001 certification is an internationally recognized credential that validates an individual's expertise in managing information security management systems (ISMS) to protect sensitive information within organizations.
What are the key requirements to obtain ISO 27001 certification?
To obtain ISO 27001 certification, candidates typically need to complete a recognized training program, pass a standardized exam, demonstrate practical knowledge of information security concepts, and meet specific professional experience requirements depending on the certification level.
How can ISO 27001 certification impact my career?
ISO 27001 certification can significantly enhance your career prospects by validating your expertise in information security management. Certified professionals are often more attractive to employers, command higher salaries, and qualify for advanced roles in cybersecurity and compliance.
What types of ISO 27001 certifications are available for individuals?
ISO 27001 offers various certification levels, including Foundation Level, Lead Implementer, Lead Auditor, and Master Certification, each targeting different competencies and career objectives in information security management.
