Securing sensitive data in global tech and finance firms requires more than a standard checklist. As threats shift and regulatory demands intensify, ISO 27001 consultancy delivers tailored information security frameworks that address unique business risks instead of generic solutions. For CISOs and compliance officers aiming to simplify complex questionnaires and strengthen their security posture, expert guidance provides clarity and confidence through every phase of compliance—ensuring both operational resilience and stakeholder trust.
Table of Contents
- What ISO 27001 Consultants Do and Why They Matter
- Variations in Consultant Services and Engagement Models
- Key Skills, Certifications, and Selection Criteria
- Core Phases of ISO 27001 Consultancy Engagement
- Costs, Benefits, and Common Pitfalls to Avoid
Key Takeaways
| Point | Details |
|---|---|
| Role of ISO 27001 Consultants | They assist organizations in developing and maintaining effective Information Security Management Systems to mitigate cyber risks. |
| Diverse Engagement Models | Consultants offer tailored services ranging from advisory roles to full implementation based on organizational needs. |
| Key Skills and Certifications | Successful consultants possess technical expertise, strategic thinking, and relevant certifications in information security management. |
| Strategic Transformation Process | The consultancy engagement should be viewed as a holistic strategic process rather than a mere compliance task for lasting impact. |
What ISO 27001 Consultants Do and Why They Matter
ISO 27001 consultants are cybersecurity professionals who specialize in helping organizations design, implement, and maintain robust Information Security Management Systems (ISMS). Their primary mission involves guiding businesses through the complex process of establishing comprehensive security frameworks that protect digital assets and mitigate potential cyber risks.
These expert consultants play a critical role in translating the flexible ISO 27001 standard into actionable security strategies tailored to each organization's unique environment. Unlike generic security checklists, ISO 27001 consultants understand that cybersecurity requires a nuanced, risk-based approach. They conduct thorough assessments to identify specific vulnerabilities, design custom control mechanisms, and help organizations develop systematic processes for ongoing risk management and continuous improvement.
The value of ISO 27001 consultants extends far beyond simple compliance. They serve as strategic partners who help organizations build resilient security infrastructures that demonstrate commitment to protecting sensitive information. By navigating complex regulatory requirements, these professionals enable businesses to establish credibility with clients, partners, and stakeholders while creating frameworks that can adapt to evolving technological landscapes.
Pro tip: When selecting an ISO 27001 consultant, prioritize professionals with proven experience across multiple industries and a track record of successful implementation, not just theoretical knowledge.
Variations in Consultant Services and Engagement Models
ISO 27001 consultants offer a diverse range of services tailored to meet organizations' unique security needs and maturity levels. Engagement models vary significantly from comprehensive end-to-end implementations to targeted strategic advisory roles. Some consultants specialize in providing foundational risk management frameworks, while others offer highly customized solutions that address industry-specific compliance requirements.
These engagement models typically fall into several key categories. Advisory services focus on strategic guidance, where consultants provide expert recommendations and roadmaps for developing robust Information Security Management Systems (ISMS). Full implementation services represent a more comprehensive approach, where consultants manage the entire compliance journey from initial assessment through documentation, control selection, and employee training. Hybrid models also exist, allowing organizations to select specific areas of support based on their existing capabilities and budget constraints.
The scope of consultant services can range from short-term certification projects to long-term continuous improvement partnerships. Different implementation approaches align with organizational objectives, such as phased implementations that follow systematic plan-do-check-act cycles or rapid certification approaches for businesses facing urgent compliance deadlines. Some consultants offer ongoing support to help organizations maintain and evolve their security frameworks, ensuring they remain adaptable to emerging technological and regulatory challenges.
Here's a quick comparison of common ISO 27001 consultant engagement models:
| Engagement Model | Typical Duration | Scope of Services | Ideal For |
|---|---|---|---|
| Advisory Only | Weeks to months | Strategic guidance, risk advice | Mature organizations needing expertise |
| Full Implementation | Several months | End-to-end support, full ISMS build | Businesses new to ISO 27001 |
| Hybrid/Partial Support | Flexible | Targeted, customizable assistance | Firms with existing security teams |
| Ongoing Partnership | Multi-year | Continuous improvement, periodic reviews | Organizations seeking long-term compliance |
Pro tip: Before engaging an ISO 27001 consultant, conduct a thorough internal assessment of your organization's current security maturity to select the most appropriate service model and maximize the consultant's potential impact.
Key Skills, Certifications, and Selection Criteria
Successful ISO 27001 consultants possess a sophisticated blend of technical expertise, strategic thinking, and communication skills. Specific professional certifications serve as critical indicators of a consultant's capability to navigate complex information security landscapes. These professionals must demonstrate deep knowledge of risk management frameworks, auditing techniques, and the ability to translate technical requirements into actionable business strategies.

Key certifications that distinguish top-tier ISO 27001 consultants include the CQI-IRCA ISO 27001 Lead Auditor, Certified Information Systems Security Professional (CISSP), and ISO 27001 Lead Implementer credentials. These qualifications validate a consultant's comprehensive understanding of information security management systems, risk assessment methodologies, and compliance requirements. Beyond formal certifications, organizations should evaluate consultants based on their practical experience, industry-specific knowledge, and proven track record of successful ISMS implementations across diverse business environments.
The selection process for an ISO 27001 consultant extends beyond technical credentials. Auditing competence and regulatory understanding are paramount, requiring professionals who can not only interpret complex security standards but also customize implementation strategies to unique organizational contexts. Top consultants excel in communication, can bridge technical and executive perspectives, and demonstrate the agility to adapt security frameworks to evolving technological and regulatory landscapes.
Pro tip: Request detailed case studies and references from potential ISO 27001 consultants, focusing on projects similar to your organization's size, industry, and specific security challenges.
Core Phases of ISO 27001 Consultancy Engagement
ISO 27001 consultancy engagements follow a structured approach designed to systematically transform an organization's information security management. Certification process involves critical phases that guide businesses from initial assessment through comprehensive implementation and continuous improvement. These phases are not merely administrative checkboxes but strategic interventions that fundamentally reshape an organization's approach to information security.
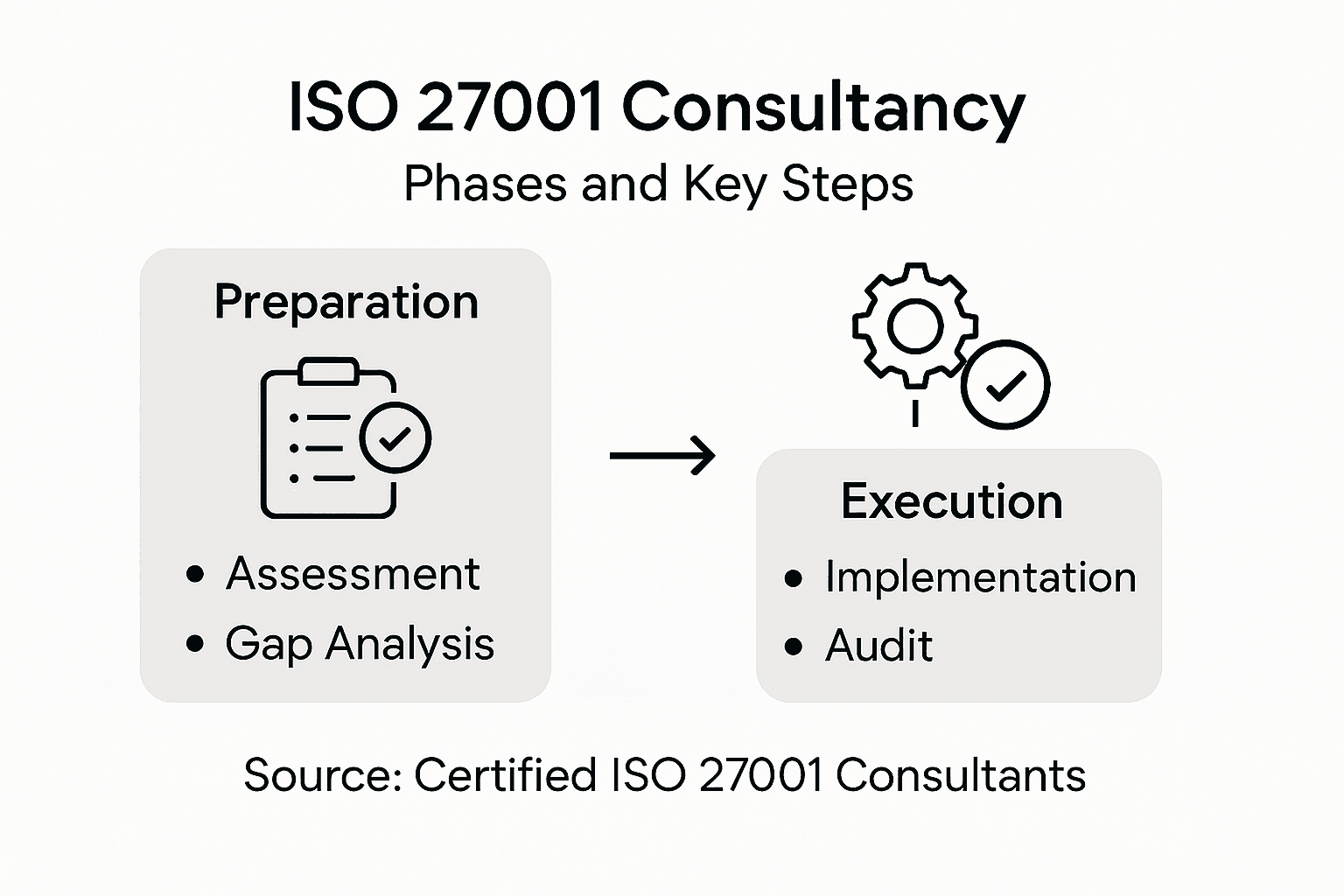
The engagement typically begins with a comprehensive initial assessment, where consultants conduct a detailed evaluation of the organization's existing information security landscape. This diagnostic phase involves defining the precise scope of the Information Security Management System (ISMS), identifying critical assets, and understanding current risk management practices. Consultants then develop a detailed risk assessment and treatment plan, meticulously selecting appropriate security controls from ISO 27001's Annex A that align with the organization's unique operational context and potential vulnerabilities.
Implementation requires systematic documentation and organizational alignment, where consultants help develop critical policies, procedures, and technical controls. This phase goes beyond creating paperwork, focusing on embedding a security-conscious culture throughout the organization. The final stages involve rigorous internal audits, readiness reviews, and preparation for certification, ensuring that the newly developed ISMS meets the stringent requirements of the ISO 27001 standard and effectively mitigates potential security risks.
Use this summary to understand key phases in a typical ISO 27001 consultancy engagement:
| Phase | Main Activities | Outcome |
|---|---|---|
| Initial Assessment | Identify assets and risks | Defined ISMS scope |
| Risk Treatment | Select controls and strategies | Risk mitigation plan |
| Implementation | Draft policies, train staff | Security framework embedded |
| Audit & Certification | Internal checks, readiness reviews | ISO 27001 certification achieved |
| Continuous Improvement | Regular updates, training | Ongoing risk resilience |
Pro tip: Approach the ISO 27001 consultancy engagement as a strategic transformation process, not just a compliance exercise, by actively involving leadership and fostering organization-wide security awareness.
Costs, Benefits, and Common Pitfalls to Avoid
The ISO 27001 consultancy journey represents a significant investment that requires careful financial and strategic planning. Consulting expenses encompass multiple dimensions, including consultant fees, internal resource allocation, training costs, technological implementations, and certification audit expenses. While these upfront investments can seem substantial, they pale in comparison to the potential financial losses from unmitigated cybersecurity risks.
The benefits of ISO 27001 consultancy extend far beyond mere compliance, delivering tangible operational and reputational advantages. Organizations gain a comprehensive framework for identifying, managing, and reducing information security risks, which translates into enhanced business resilience. Strategic planning mitigates potential implementation challenges by establishing clear expectations and preventing common pitfalls such as inadequate risk management, insufficient management commitment, and treating certification as a one-time administrative exercise.
Common pitfalls organizations must proactively avoid include underestimating resource requirements, failing to secure leadership support, and adopting a narrow, compliance-only perspective. Successful ISO 27001 implementation demands a holistic approach that integrates security practices into the organizational culture, emphasizing continuous improvement and adaptability. By understanding potential challenges and strategically addressing them, businesses can transform the ISO 27001 consultancy process from a regulatory requirement into a powerful mechanism for building robust, trustworthy information security capabilities.
Pro tip: Develop a comprehensive internal communication strategy that explains the strategic value of ISO 27001 to stakeholders across all organizational levels, ensuring broad understanding and support.
Accelerate Your ISO 27001 Compliance Journey with Smart Automation
Navigating the complex phases of ISO 27001 implementation demands not only expertise but also efficient tools to manage security requirements and stakeholder collaboration. The challenges of rigorous documentation, continuous risk treatment, and timely readiness assessments can overwhelm organizations striving to build resilient security infrastructures. Skypher empowers medium to large organizations, especially in tech and finance, to overcome these obstacles with its AI-driven Questionnaire Automation Tool that dramatically reduces the time spent on security reviews while boosting accuracy and consistency.

Unlock the full potential of your ISO 27001 consultancy efforts by integrating Skypher’s customizable Trust Center and real-time collaboration features that streamline communication among teams and external auditors. With over 30 API integrations including popular platforms like ServiceNow and Slack, Skypher simplifies maintaining compliance and managing the continuous improvement process outlined in ISO 27001. Visit Skypher’s platform today and transform your security compliance from a resource-intensive task into a seamless strategic advantage.
Frequently Asked Questions
What is the role of an ISO 27001 consultant?
ISO 27001 consultants help organizations design, implement, and maintain Information Security Management Systems (ISMS) to protect digital assets and manage cyber risks effectively.
How do ISO 27001 consultants differ from standard cybersecurity advisors?
Unlike generic cybersecurity advisors, ISO 27001 consultants provide specialized guidance on ISO 27001 standards, focusing on risk-based approaches and tailored security strategies for each organization's unique needs.
What are the common engagement models offered by ISO 27001 consultants?
Engagement models vary and can include advisory services, full implementation, hybrid support, or ongoing partnership, allowing organizations to choose the best fit based on their security maturity and budget.
What are the key skills to look for in an ISO 27001 consultant?
Essential skills include technical expertise in information security, risk management knowledge, relevant certifications (like CQI-IRCA ISO 27001 Lead Auditor), and strong communication skills to effectively bridge technical and strategic perspectives.