Nearly 60 percent of major data breaches could have been prevented with proper security controls, yet many american firms still face overwhelming manual processes when tackling ISO 27001 compliance. For CISOs at growing technology companies, the relentless drumbeat of security questionnaires can drain valuable resources and create audit fatigue. Automating these workflows empowers organizations to gain real-time visibility, reduce errors, and confidently align with international standards like ISO 27001.
Table of Contents
- ISO 27001 Control Defined And Key Concepts
- Types Of Controls In ISO 27001 Standard
- Control Implementation And Documentation Process
- Obligations And Audit Requirements For Organizations
- Automation Benefits And Common Pitfalls
Key Takeaways
| Point | Details |
|---|---|
| ISO 27001 Framework | ISO 27001 provides a systematic framework for managing and mitigating information security risks across organizations. |
| Core Control Categories | It encompasses four control categories: Organizational, People, Physical, and Technological, each tailored to specific security needs. |
| Documentation Importance | Comprehensive documentation is crucial for policies and procedures, serving as the blueprint for effective information security management. |
| Automation Considerations | Automation enhances efficiency and accuracy in compliance processes but should complement human oversight to avoid pitfalls. |
ISO 27001 Control Defined and Key Concepts
ISO 27001 represents a comprehensive international standard for information security management, designed to help organizations protect their most critical digital assets. At its core, the standard provides a systematic framework for identifying, managing, and mitigating information security risks across an enterprise's technological ecosystem. Organizations implementing these security requirements establish robust processes that safeguard confidential information from potential breaches and unauthorized access.
The standard's fundamental approach centers on establishing an Information Security Management System (ISMS) that methodically addresses three core principles: confidentiality, integrity, and availability of information. Unlike generic security guidelines, ISO 27001 mandates a risk-based methodology where organizations conduct systematic risk assessments, implement tailored security controls, and maintain continuous monitoring and improvement processes. This dynamic framework enables businesses to adapt their security strategies to evolving technological landscapes and emerging threat environments.
Key components of ISO 27001 controls include comprehensive documentation, risk assessment protocols, security policy development, and ongoing performance measurement. Organizations must develop a structured approach that encompasses asset identification, threat evaluation, control selection, and regular effectiveness reviews. These controls are not one-size-fits-all but are meticulously customized to match an organization's unique operational context, technological infrastructure, and industry-specific regulatory requirements.

Pro tip: Begin your ISO 27001 implementation by conducting a thorough gap analysis of your current information security practices to identify areas requiring immediate attention and strategic improvement.
Types of Controls in ISO 27001 Standard
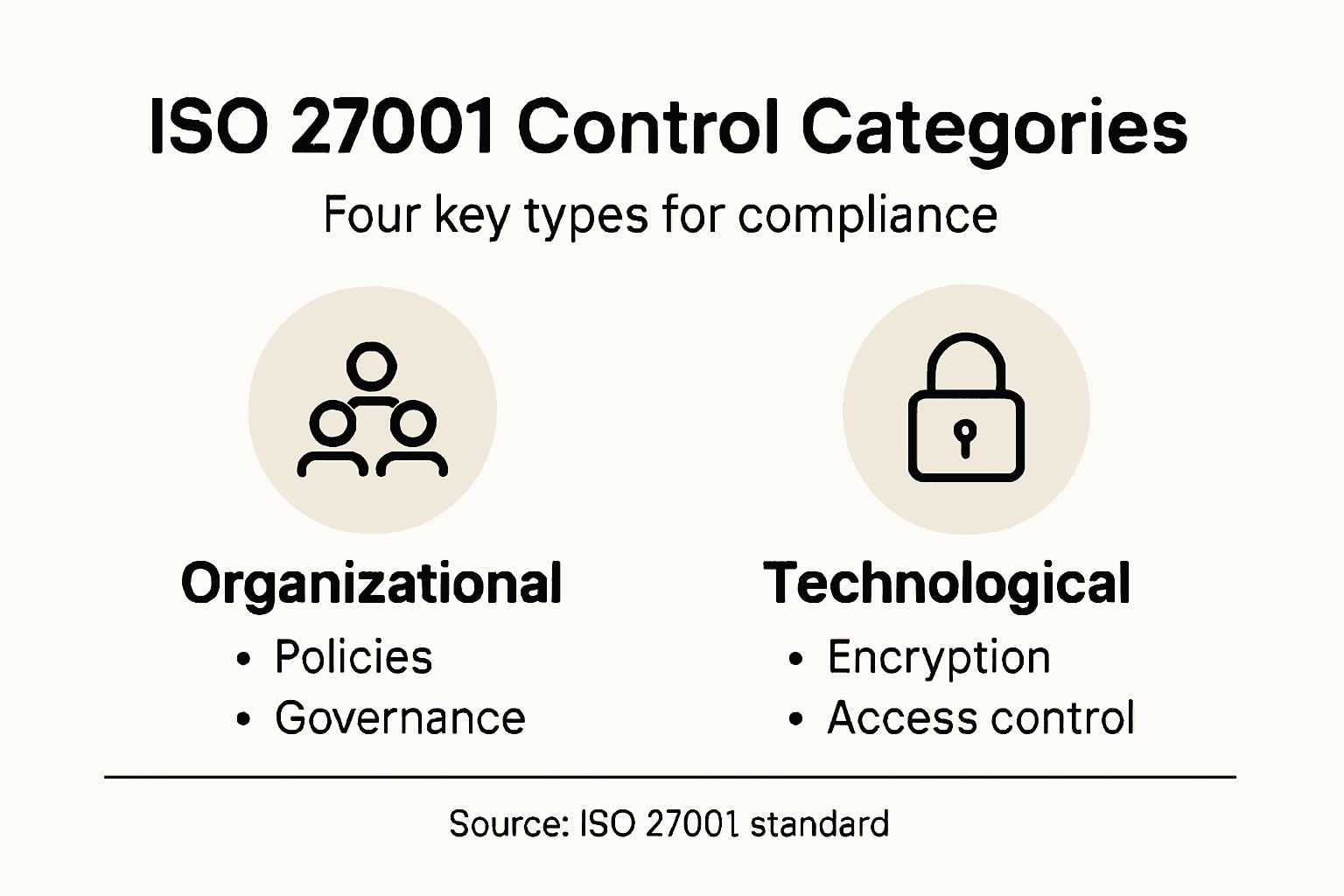
ISO 27001 establishes a comprehensive framework of security controls categorized into four essential domains, each addressing unique aspects of organizational information security. Annex A controls provide organizations with a structured approach to managing information security risks through detailed, systematic guidelines. These controls are not rigid prescriptions but flexible mechanisms that can be tailored to an organization's specific operational context and risk profile.
The four primary control categories represent a holistic approach to information security management. Organizational Controls focus on establishing governance frameworks, policy development, and strategic risk management processes. People Controls address human factors by managing security awareness, training programs, and employee screening procedures. Physical Controls encompass protective measures for facilities, equipment, and physical infrastructure, including access restrictions, environmental protections, and asset management. Technological Controls target digital security mechanisms, covering areas such as network protection, system authentication, cryptography, and operational software security.
Implementing these controls requires a strategic and nuanced approach. Organizations must conduct comprehensive risk assessments to determine which specific controls are most relevant to their unique environment. The Statement of Applicability becomes a critical document that documents an organization's control selection rationale, explaining why certain controls are implemented or excluded. This process ensures that security measures are not just comprehensive but precisely aligned with an organization's specific risk landscape and operational requirements.
Pro tip: Develop a dynamic risk assessment framework that regularly reviews and updates your control selection, ensuring your information security strategy remains adaptive and responsive to emerging technological threats.
Here is a summary of the four primary ISO 27001 control categories and their business impact:
| Control Category | Core Focus | Typical Examples | Business Impact |
|---|---|---|---|
| Organizational | Policies, governance, risk management | Security policy, risk approach | Reduces systemic security gaps |
| People | Training, awareness, personnel vetting | Security education, background checks | Minimizes human error risks |
| Physical | Facility protection, access controls | Entry systems, equipment locks | Prevents unauthorized physical access |
| Technological | System, network, and data protection | Encryption, firewalls, authentication | Defends against cyberattacks |
Control Implementation and Documentation Process
The ISO 27001 control implementation process is a structured methodology that demands meticulous planning, comprehensive documentation, and strategic execution. Organizational controls require systematic documentation that clearly defines policies, assigns specific roles, and establishes detailed procedures for risk management and compliance reporting. This documentation serves as the foundational blueprint for an organization's information security strategy, providing a clear roadmap for implementing and maintaining robust security controls.
Critical documentation components include the Information Security Policy, Risk Assessment Reports, and the Statement of Applicability. The Statement of Applicability is particularly crucial, as it provides a transparent inventory of selected security controls, explaining the rationale behind each control's inclusion or exclusion. Organizations must develop these documents with precision, ensuring they reflect the unique risk landscape, operational context, and regulatory requirements specific to their business environment. The documentation process is not a one-time event but a continuous cycle of assessment, implementation, monitoring, and refinement.
Successful control implementation requires a dynamic and integrated approach. Organizations must establish clear governance structures that define roles and responsibilities, create comprehensive training programs to ensure employee understanding, and develop mechanisms for ongoing monitoring and evaluation. This involves regular internal audits, periodic risk reassessments, and a commitment to continuous improvement. The goal is to create a flexible information security management system that can adapt to emerging technological threats, changing business objectives, and evolving regulatory landscapes.
Pro tip: Implement a centralized document management system that tracks version control, access permissions, and revision history for all ISO 27001 related documentation to ensure transparency and accountability.
Obligations and Audit Requirements for Organizations
ISO 27001 certification demands rigorous commitment from organizations to establish and maintain comprehensive Information Security Management Systems (ISMS). Organizations must systematically evaluate security risks through defined controls, ensuring continuous monitoring and periodic verification of their information protection strategies. This process requires a structured approach that goes beyond simple compliance, emphasizing proactive risk management and adaptive security frameworks.
The certification process involves multiple layers of audit requirements. Internal Audits are a critical component, requiring organizations to conduct regular self-assessments that critically examine the effectiveness of their security controls. External Certification Audits, performed by independent certification bodies, provide an objective evaluation of the organization's ISMS. These audits assess documentation completeness, control implementation, risk management processes, and the organization's ability to demonstrate consistent adherence to ISO 27001 standards. Key focus areas include management commitment, systematic risk control, and evidence of continual improvement.
Successful compliance requires a holistic approach that integrates technical, procedural, and human elements of information security. Organizations must develop comprehensive documentation that not only meets certification requirements but also provides a clear roadmap for security implementation. This includes detailed risk assessment reports, policy documents, incident response plans, and evidence of ongoing staff training and awareness programs. The audit process is not a one-time event but a continuous cycle of assessment, improvement, and verification that demands sustained organizational commitment.
Pro tip: Develop a comprehensive audit trail documentation system that captures all security-related activities, decisions, and improvements to streamline the certification and recertification process.
Automation Benefits and Common Pitfalls
ISO 27001 control automation represents a strategic approach to streamlining compliance processes, offering organizations powerful tools to enhance their information security management. AI-driven approaches to sales automation provide insights into how intelligent systems can transform complex compliance workflows. By leveraging advanced technologies, organizations can significantly reduce manual intervention, minimize human error, and create more consistent and reliable security management processes.
The primary benefits of automation include increased efficiency, enhanced accuracy, and improved scalability of security controls. Automated Risk Assessment tools can continuously monitor and evaluate potential security threats, providing real-time insights that traditional manual processes cannot match. Compliance Tracking Systems enable organizations to automatically document control implementations, track changes, and generate comprehensive audit trails with minimal human intervention. However, automation is not without challenges. Organizations must carefully design their automated systems to avoid over-reliance on technology and maintain critical human oversight and contextual understanding.
Common pitfalls in ISO 27001 control automation include insufficient customization, lack of flexibility, and potential blind spots in automated systems. Many organizations mistakenly view automation as a complete replacement for human expertise, rather than a complementary tool. Successful implementation requires a balanced approach that combines technological capabilities with human judgment. This means developing robust automation frameworks that can adapt to changing security landscapes, integrate with existing systems, and provide meaningful insights that support strategic decision-making.
Pro tip: Implement a hybrid automation strategy that combines AI-powered tools with periodic human review to ensure comprehensive and adaptive security control management.
The following table compares manual and automated approaches to ISO 27001 control management:
| Approach | Efficiency Level | Error Frequency | Best Use Case |
|---|---|---|---|
| Manual | Moderate, labor-intensive | Prone to human mistakes | Small-scale implementations |
| Automated | High, scalable process | Reduced, consistent | Large or dynamic environments |
Streamline Your ISO 27001 Compliance with AI-Driven Automation
Implementing and documenting ISO 27001 controls can be complex and time-consuming. As highlighted in the article, organizations face challenges in managing detailed risk assessments, maintaining comprehensive documentation, and ensuring continuous control monitoring to meet audit requirements. These pain points often slow down compliance efforts and increase the risk of human error, especially when handling extensive security questionnaires and integrating multiple control domains.
Skypher offers a powerful solution tailored for these challenges. With our AI Questionnaire Automation Tool, you can complete even the most complex security reviews in a fraction of the time, reducing manual workload and minimizing errors. Our platform supports real-time collaboration and seamless integration with over 40 third-party risk management platforms, including ServiceNow and Slack, enabling your teams to stay aligned and responsive. Take control of your information security with advanced features like a customizable Trust Center and automated audit trails designed to support your ISO 27001 journey.

Accelerate your ISO 27001 implementation and simplify compliance today by visiting Skypher to discover how our SaaS platform can transform your information security management. Experience enhanced efficiency, accuracy, and confidence with our AI-powered solutions designed for medium to large organizations in tech and finance. Begin your journey toward streamlined compliance now.
Frequently Asked Questions
What is ISO 27001 control and why is it important?
ISO 27001 control is a comprehensive framework designed to manage information security risks, ensuring the confidentiality, integrity, and availability of information. It is crucial for organizations to protect their digital assets from potential breaches and unauthorized access.
How do organizations implement ISO 27001 controls?
Organizations implement ISO 27001 controls by establishing an Information Security Management System (ISMS) that includes risk assessments, control selection, and ongoing monitoring. This structured approach allows businesses to customize their security measures to their unique operational contexts.
What are the main categories of ISO 27001 controls?
The main categories of ISO 27001 controls include Organizational, People, Physical, and Technological controls. These categories address various aspects of information security, such as governance policies, staff training, facility protection, and digital security measures.
What role does automation play in ISO 27001 compliance?
Automation in ISO 27001 compliance streamlines processes by increasing efficiency, enhancing accuracy, and improving scalability. Automated tools can continuously monitor risks and track compliance documentation, thereby reducing manual errors and ensuring timely updates.