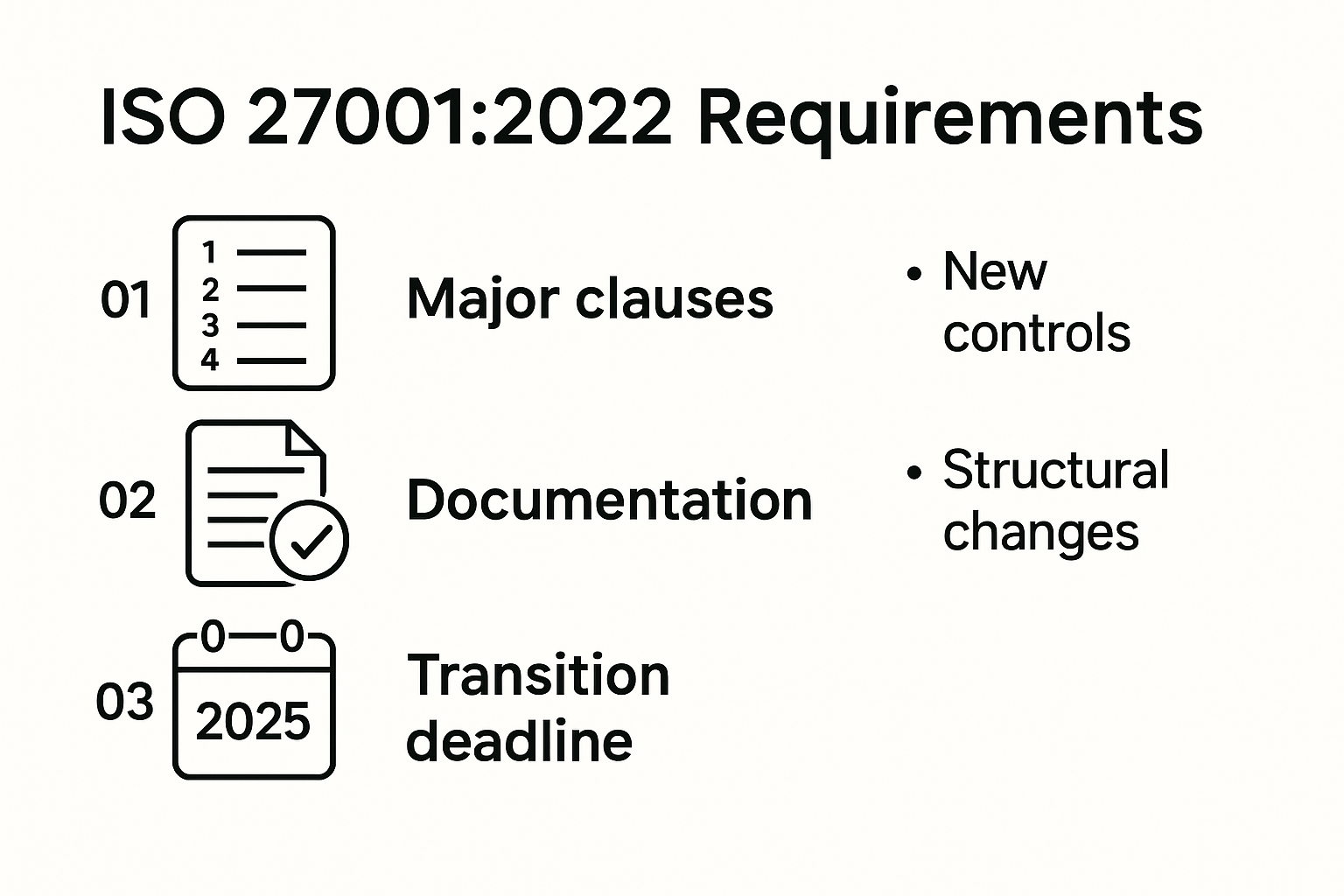
ISO 27001 is about to shake things up for companies handling sensitive data. By October 31, 2025, every certified organization must fully transition to the ISO 27001:2022 standard, with updated controls and stricter documentation. Sounds like a mere paperwork shuffle, right? Actually, those new requirements pack some serious changes—adding 11 new security controls, pushing the total to 93, and demanding deeper risk assessments than ever before. It’s not just about ticking boxes anymore. This latest rollout will separate the organizations that treat cybersecurity as a living practice from those just going through the motions.
Table of Contents
- Understanding Core ISO 27001 Requirement Sections
- Key Updates To ISO 27001 Requirement In 2025
- Strategies For Meeting ISO 27001 Requirement Effectively
- Common Mistakes To Avoid In ISO 27001 Implementation
Quick Summary
| Takeaway | Explanation |
|---|---|
| Transition Deadline | All ISO/IEC 27001 certifications must transition to the ISO 27001:2022 standard by October 31, 2025, requiring comprehensive updates to ISMS documentation and training. |
| Expanded Security Controls | The updated standard includes 11 new controls, bringing the total to 93, focusing on areas like cloud security and threat intelligence to address evolving digital threats. |
| Comprehensive Documentation | Organizations must maintain critical documentation, such as ISMS policies and risk assessment methodologies, to demonstrate their commitment to information security. |
| Risk Assessment Importance | Conducting thorough and ongoing risk assessments is vital; superficial evaluations can lead to overlooking critical vulnerabilities in the information security landscape. |
| Continual Improvement Culture | Successful ISO 27001 implementation requires fostering a culture of continuous learning and improvement, integrating security practices into daily operations and regular training. |
Understanding Core ISO 27001 Requirement Sections
ISO 27001 establishes a comprehensive framework for information security management that goes far beyond basic compliance. Organizations seeking to implement a robust Information Security Management System (ISMS) must understand the core requirement sections that form the backbone of this international standard.
The Structural Framework of ISO 27001 Requirements
The ISO 27001 standard is meticulously organized into 11 distinct clauses that provide a systematic approach to information security management. According to Strong DM, these clauses cover critical aspects of organizational information security from initial planning to continuous improvement. The standard's structure ensures that organizations develop a comprehensive and dynamic approach to protecting their information assets.
Key clauses include mandatory sections such as:
- Scope Definition: Establishing precise boundaries of the Information Security Management System
- Leadership Commitment: Demonstrating top management's active involvement and responsibility
- Planning: Identifying and addressing information security risks
- Support: Providing necessary resources and organizational competence
- Operation: Implementing specific security controls and procedures
- Performance Evaluation: Monitoring and measuring the effectiveness of the ISMS
- Continual Improvement: Ensuring ongoing enhancement of information security practices
Documentation and Compliance Requirements
Comprehensive documentation serves as the critical foundation of ISO 27001 compliance. Wattle Corp emphasizes that organizations must maintain a comprehensive set of documents that demonstrate their commitment to information security. These essential documentation requirements include:
- ISMS Policy: A formal document outlining the organization's overall approach to information security
- Risk Assessment Methodology: Detailed procedures for identifying and evaluating potential security risks
- Statement of Applicability (SoA): A comprehensive document detailing the specific controls implemented
- Incident Management Procedures: Clear protocols for responding to security incidents
- Internal Audit Reports: Systematic documentation of security assessments and findings
- Corrective Action Plans: Strategies for addressing identified security weaknesses
Defining the ISMS Scope
Amtivo highlights that defining the precise scope of the ISMS is a critical initial step for organizations. This process involves carefully specifying the boundaries, assets, technologies, and locations covered by the Information Security Management System. The Scope Statement must clearly articulate which parts of the organization are included, ensuring a targeted and focused approach to information security.
Successful implementation requires a holistic view that considers the organization's unique context, technological infrastructure, and specific security challenges. Organizations must go beyond a one-size-fits-all approach, tailoring their ISMS to address their specific risk landscape and operational requirements.
By understanding these core requirement sections, organizations can develop a robust, adaptable, and comprehensive approach to information security that not only meets international standards but also provides genuine protection against evolving digital threats.

Key Updates to ISO 27001 Requirement in 2025
The information security landscape continues to evolve rapidly, and the ISO 27001 standard is adapting to meet these complex challenges. As organizations prepare for significant changes, understanding the key updates to ISO 27001 requirements becomes crucial for maintaining robust information security practices.
Transition Deadline and Certification Requirements
LRQA highlights a critical milestone for organizations: all ISO/IEC 27001 certifications must transition to the ISO 27001:2022 standard by October 31, 2025. This three-year grace period represents a significant opportunity for organizations to comprehensively review and update their Information Security Management Systems (ISMS).
Key transition considerations include:
- Comprehensive Gap Analysis: Identifying differences between existing ISMS and new standard requirements
- Updated Documentation: Revising existing security policies and procedures
- Control Implementation: Integrating new security controls and requirements
- Staff Training: Ensuring team members understand new standard specifications
Expanded Security Controls and Focus Areas
According to ISMS Online, the ISO 27001:2022 standard introduces substantial updates to its control framework. The most notable change is the expansion of Annex A, which now includes 11 new controls, bringing the total to 93 distinct security controls. These additions reflect the rapidly changing digital threat landscape and address emerging security challenges.
Significant focus areas in the updated standard include:
- Cloud Security: Enhanced controls for managing cloud-based infrastructure and services
- Threat Intelligence: New mechanisms for detecting and responding to advanced cybersecurity threats
- Supply Chain Security: Improved guidelines for managing third-party risk and vendor security
- Remote Work Security: Updated controls addressing the challenges of distributed workforce environments
Strategic Implementation Approach
Successful adaptation to the new ISO 27001 requirements demands a strategic and methodical approach. Organizations must move beyond simple compliance and view these updates as an opportunity to strengthen their overall information security posture. ISMS Online recommends conducting a thorough gap analysis to identify areas requiring modification.
Effective implementation strategies include:
- Conducting a comprehensive review of existing security controls
- Mapping new requirements against current ISMS practices
- Developing a phased implementation plan
- Engaging cross-functional teams in the transition process
- Investing in continuous training and awareness programs
The 2025 updates to ISO 27001 represent more than a mere regulatory requirement. They signal a proactive approach to information security that acknowledges the complex, dynamic nature of digital threats. Organizations that view these changes as an opportunity for improvement rather than a compliance burden will be best positioned to protect their critical information assets and maintain a robust security infrastructure.
Strategies for Meeting ISO 27001 Requirement Effectively
Meeting ISO 27001 requirements demands a strategic and comprehensive approach that goes beyond mere checkbox compliance. Organizations must develop a proactive and integrated methodology to effectively implement and maintain their Information Security Management System (ISMS).
Comprehensive Policy Development and Resource Allocation
Codific emphasizes the critical importance of developing comprehensive policies and procedures that align directly with ISO 27001 standards. Successful implementation requires more than documentation it demands a cultural transformation within the organization.
Key policy development strategies include:
- Clear Documentation: Creating detailed, actionable security policies
- Leadership Commitment: Ensuring top management actively supports information security initiatives
- Resource Dedication: Allocating specific personnel and budget for ISMS management
- Regular Policy Review: Establishing mechanisms for continuous policy updates
Technology and Continuous Improvement Approach
Lansweeper highlights the significance of leveraging technology and maintaining a continuous improvement mindset. Organizations must integrate advanced tools and systematic evaluation processes to stay ahead of evolving security challenges.
Effective technological strategies include:
- Automated Compliance Tools: Implementing software for tracking and managing security controls
- Regular Internal Audits: Conducting systematic assessments of ISMS effectiveness
- Gap Analysis Technology: Using advanced tools to identify and address compliance gaps
- Real-Time Monitoring Systems: Deploying continuous security assessment technologies
Employee Training and Operational Integration
Transforming ISO 27001 requirements from theoretical guidelines to practical operational standards requires comprehensive employee engagement. Codific suggests integrating information security practices into daily operational workflows to create a sustainable security culture.
Key training and integration approaches include:
- Mandatory Security Training: Developing comprehensive educational programs for all employees
- Role-Specific Security Protocols: Creating targeted training modules for different organizational roles
- Incident Response Simulations: Conducting regular practical exercises to test security readiness
- Continuous Learning Platforms: Establishing ongoing education mechanisms for emerging security threats
Successful ISO 27001 implementation is not a destination but a continuous journey of improvement. Organizations must view these requirements as a dynamic framework for protecting their most critical information assets. By combining technological solutions, comprehensive policies, and a culture of continuous learning, businesses can transform ISO 27001 compliance from a regulatory requirement into a strategic advantage.
The most successful organizations will approach ISO 27001 not as a static set of rules, but as a flexible, adaptive system that evolves with their unique technological and operational landscape. This approach ensures not just compliance, but genuine, robust information security that protects against emerging digital threats.
Common Mistakes to Avoid in ISO 27001 Implementation
Implementing ISO 27001 requires precision, strategic planning, and a deep understanding of organizational security dynamics. While many organizations approach the standard with good intentions, several critical mistakes can undermine the effectiveness of their Information Security Management System (ISMS).
Inadequate Risk Assessment Strategies
Boulay Group emphasizes that superficial risk assessments represent one of the most significant pitfalls in ISO 27001 implementation. Organizations often conduct cursory evaluations that fail to capture the nuanced and evolving nature of information security risks.
Common risk assessment errors include:
- Incomplete Threat Identification: Overlooking emerging digital threats
- Insufficient Scope: Failing to comprehensively map organizational assets and vulnerabilities
- Static Risk Modeling: Treating risk assessment as a one-time event rather than a continuous process
- Lack of Quantitative Analysis: Relying on subjective rather than data-driven risk evaluations
Management Commitment and Organizational Alignment
Quality Digest highlights the critical importance of leadership engagement. Lack of genuine management commitment can transform ISO 27001 implementation from a strategic initiative into a mere compliance exercise.
Key leadership engagement challenges include:
- Inconsistent Support: Fluctuating management interest in information security
- Resource Constraints: Inadequate budget and personnel allocation
- Unclear Organizational Scope: Poorly defined boundaries of the Information Security Management System
- Disconnected Implementation: Treating ISMS as an isolated technical function
External Dependency and Internal Capability Gaps
Insight Assurance warns against over-reliance on external consultants. While external expertise can be valuable, successful ISO 27001 implementation requires deep internal understanding and commitment.
Critical internal capability considerations include:
- Vendor Dependency: Outsourcing critical security functions without building internal competence
- Knowledge Transfer Failures: Not developing internal expertise during consultant engagement
- Cultural Misalignment: Implementing generic solutions that do not match organizational culture
- Insufficient Training: Neglecting ongoing skill development for internal teams
Successful ISO 27001 implementation transcends technical compliance. It demands a holistic approach that integrates robust risk management, leadership commitment, and continuous organizational learning. Organizations must view the standard not as a destination but as a dynamic framework for evolving information security capabilities.
The most effective implementations emerge from a culture of security awareness, where every team member understands their role in protecting organizational information assets. By avoiding these common mistakes, organizations can transform ISO 27001 from a regulatory requirement into a strategic competitive advantage that genuinely enhances their security posture.
Frequently Asked Questions
What is the deadline for transitioning to the ISO 27001:2022 standard?
All ISO/IEC 27001 certifications must transition to the ISO 27001:2022 standard by October 31, 2025.
What are the key updates to the ISO 27001 requirements in 2025?
The 2025 updates include 11 new security controls, expanding the total to 93, along with stricter documentation and deeper risk assessments.
Why is risk assessment important in ISO 27001 compliance?
Thorough and ongoing risk assessments are vital for identifying critical vulnerabilities and ensuring that organizations adapt their security measures to emerging threats.
How can organizations effectively implement the ISO 27001 requirements?
Effective implementation requires comprehensive policy development, strategic resource allocation, leveraging technology, and engaging in ongoing employee training.
Take the Stress Out of ISO 27001 Updates With AI-Powered Security Questionnaire Automation
Are you struggling to update your compliance strategy for the new ISO 27001 requirements? Preparing for the expanded controls, increased documentation, and deeper risk assessments can feel overwhelming, especially as you juggle an ever-growing pile of security questionnaires from clients and auditors. Missing details or slow response times not only risk your certification but can put hard-earned client trust on the line.

Now is the time to streamline your process and safeguard your compliance edge. Skypher transforms how your team handles information security due diligence. Our AI-Powered Questionnaire Automation Tool lets you tackle complex assessments faster and more accurately, ensuring your documentation matches the latest ISO 27001 standards. Cut response times, boost your team's productivity, and show clients and auditors you are always one step ahead of new requirements. Get started at Skypher today before the 2025 deadline catches up.
