Choosing between ISO 27001 and SOC 2 is not as straightforward as it seems. Each year, global spending on information security certification exceeds $150 billion, yet many companies struggle to pick the right standard for their goals. Most people assume these two frameworks work the same way. Here’s the surprise: ISO 27001 is a rigorous international certification with 93 controls built in, while SOC 2 is a flexible attestation tailored to your needs. That means your decision could completely change how your clients, partners, and regulators view your business.
Table of Contents
- Understanding ISO 27001 And SOC 2 Standards
- Key Differences Between ISO 27001 And SOC 2
- Selecting The Right Standard For Your Organization
- Certification Process, Costs, And Compliance Tips
Quick Summary
| Takeaway | Explanation |
|---|---|
| ISO 27001 requires a comprehensive approach | Organizations need to implement a full Information Security Management System (ISMS) covering people, processes, and technology to achieve certification, which includes 93 predefined controls. |
| SOC 2 offers flexibility in attestation | Organizations can customize their security assessments based on five Trust Services Criteria, with reports providing insights over specific periods rather than a rigid certification structure. |
| Consider industry requirements when choosing a standard | Organizations operating globally may benefit more from ISO 27001, while those in North America, especially tech companies, may find SOC 2 more relevant. |
| Understand financial commitments for certification | ISO 27001 typically costs between $10,000 to $50,000, whereas SOC 2 audits range from $10,000 to $60,000, reflecting different scopes and requirements for compliance. |
| Continuous improvement is key to both standards | Organizations should view certification as an ongoing commitment that necessitates regular assessments, updates to security practices, and adaptation to emerging threats. |
Understanding ISO 27001 and SOC 2 Standards
Information security standards play a critical role in protecting organizational data and building trust with stakeholders. Two prominent frameworks that enterprises rely on are ISO 27001 and SOC 2, each offering unique approaches to managing and demonstrating information security practices.
The Foundations of ISO 27001
ISO 27001 represents an internationally recognized standard for Information Security Management Systems (ISMS). Developed by the International Organization for Standardization, this framework provides a systematic approach to managing sensitive information. Organizations seeking ISO 27001 certification must implement a comprehensive set of controls and demonstrate a structured process for identifying, managing, and mitigating information security risks.
The standard encompasses 93 defined controls across various domains, requiring organizations to develop a holistic security strategy. According to SCRUT, the certification is valid for three years, with annual surveillance audits ensuring continued compliance and ongoing improvement. This approach emphasizes a continuous improvement model that adapts to evolving security challenges.
SOC 2: A Flexible Attestation Framework
Unlike ISO 27001, SOC 2 is an attestation report developed by the American Institute of Certified Public Accountants (AICPA). It focuses on evaluating an organization's security controls against five key Trust Services Criteria: Security, Availability, Confidentiality, Processing Integrity, and Privacy. As ComplyJet explains, SOC 2 offers more flexibility, allowing organizations to demonstrate their current security practices without a rigid certification process.
SOC 2 reports come in two primary types: Type 1, which provides a snapshot of an organization's controls at a specific point in time, and Type 2, which evaluates controls over a period of 3-12 months. This approach provides potential clients and partners with a detailed understanding of an organization's security practices and commitments.
Key Differences and Considerations
While both ISO 27001 and SOC 2 address information security, they differ significantly in scope and approach. IDENFY highlights that ISO 27001 offers a globally recognized certification, while SOC 2 provides a more flexible attestation report. ISO 27001 requires a more structured implementation of controls, making it ideal for organizations seeking a comprehensive, standardized approach to information security.
The choice between ISO 27001 and SOC 2 depends on various factors, including industry requirements, geographic location, and specific organizational needs. Some organizations opt to pursue both standards to demonstrate a robust and comprehensive approach to information security. Understanding the nuanced differences helps businesses make informed decisions about their security strategy and compliance efforts.
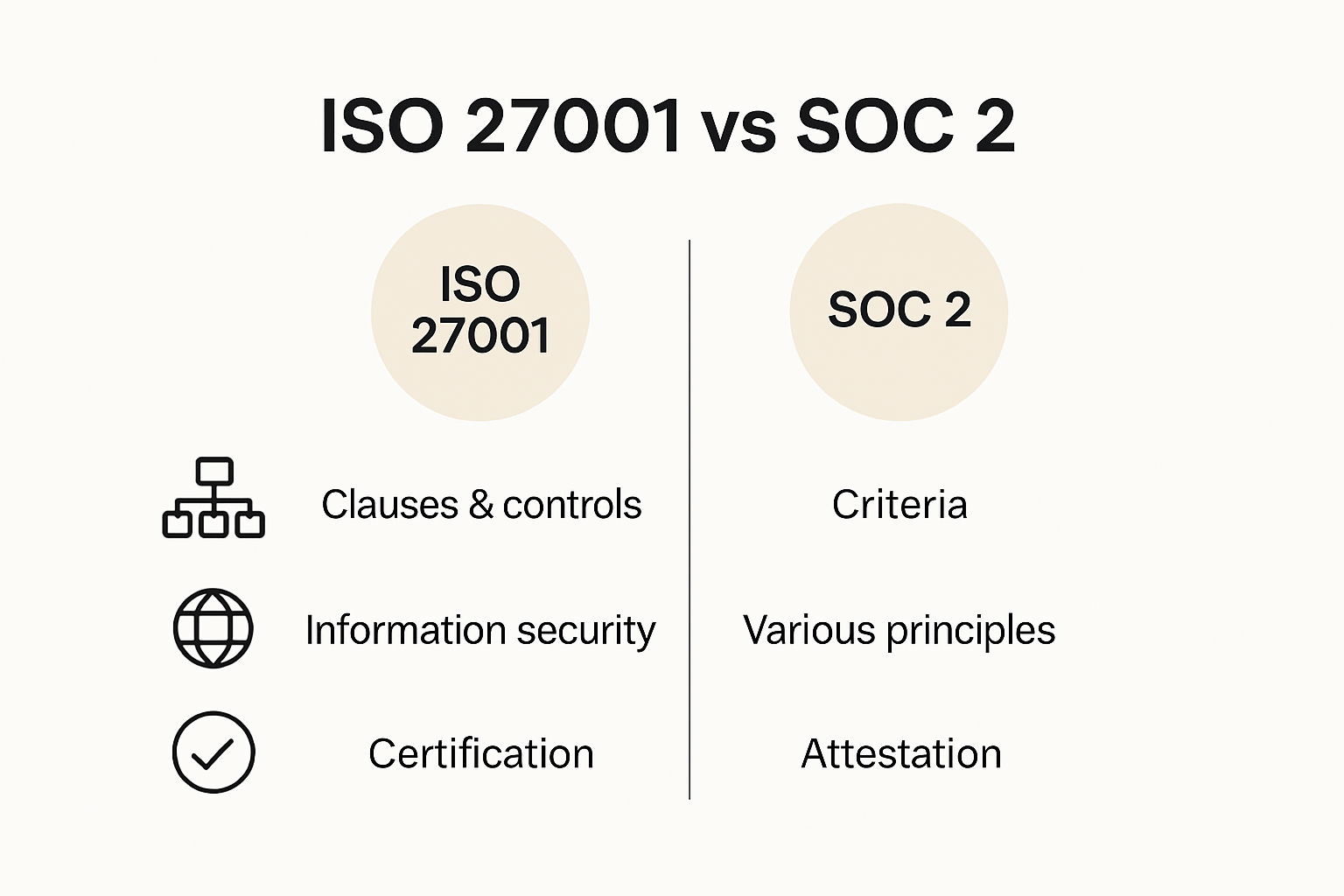
Key Differences Between ISO 27001 and SOC 2
Navigating the complex world of information security standards requires a deep understanding of their unique characteristics. ISO 27001 and SOC 2 might seem similar at first glance, but they differ significantly in their approach, scope, and implementation.
Structural and Certification Approaches
The most fundamental difference lies in their structural framework and certification process. According to PECB, ISO 27001 is a comprehensive standard that provides a structured approach to managing information security across an entire organization. Organizations pursuing ISO 27001 must implement a complete Information Security Management System (ISMS) that covers people, processes, and technological infrastructure.
In contrast, SOC 2 offers a more flexible attestation framework. Cybercrest Compliance highlights that SOC 2 focuses on demonstrating specific security controls that align with Trust Services Criteria. This approach allows organizations to tailor their security practices more dynamically, making it particularly appealing for technology and cloud service providers.
Control Framework and Scope
The control mechanisms between these two standards showcase stark differences. ISO 27001 provides a rigorous set of 93 predefined controls in its Annex A, creating a comprehensive and standardized approach to information security. As ComplyJet explains, these controls cover a wide range of security aspects, requiring organizations to implement a systematic and documented approach to managing information security risks.
SOC 2, by comparison, offers a more adaptable framework based on five Trust Services Criteria: Security, Availability, Confidentiality, Processing Integrity, and Privacy. Organizations can select which criteria are most relevant to their operations, allowing for a more customized approach to demonstrating security capabilities. This flexibility makes SOC 2 particularly attractive for organizations with unique security requirements or those operating in specialized industries.

Validation and Reporting Mechanisms
The validation and reporting processes represent another critical difference between these standards. ISO 27001 results in a formal certification valid for three years, with mandatory annual surveillance audits to ensure continued compliance. This approach emphasizes long-term, consistent security management and continuous improvement.
SOC 2 provides two types of reports: Type 1, which offers a snapshot of an organization's controls at a specific point, and Type 2, which evaluates controls over a 3-12 month period. These reports are typically renewed annually, providing stakeholders with a current view of an organization's security practices. While not a formal certification, SOC 2 reports serve as a crucial tool for demonstrating security commitments to clients, partners, and regulators.
Ultimately, the choice between ISO 27001 and SOC 2 depends on an organization's specific needs, industry requirements, and strategic objectives. Many forward-thinking organizations choose to implement both standards, creating a comprehensive and robust approach to information security that addresses multiple stakeholder expectations and regulatory requirements.
Selecting the Right Standard for Your Organization
Choosing between ISO 27001 and SOC 2 requires careful consideration of your organization's specific needs, industry requirements, and strategic objectives. Understanding the nuanced differences can help you make an informed decision that best supports your information security strategy.
Industry and Market Considerations
Your industry and target market play a crucial role in determining the most appropriate standard. According to StrongDM, global organizations typically benefit more from ISO 27001, as it provides a universally recognized certification that demonstrates a comprehensive approach to information security management. The standard's international recognition makes it particularly valuable for businesses operating across multiple countries or seeking to establish credibility in international markets.
In contrast, IDENFY highlights that SOC 2 is especially prevalent in North American markets, particularly for technology companies and SaaS providers. If your primary client base is concentrated in the United States or you operate primarily in the tech sector, SOC 2 might offer a more targeted and flexible approach to demonstrating your security capabilities.
Organizational Maturity and Resources
The selection process also depends on your organization's security maturity and available resources. ISO 27001 requires a more comprehensive and structured implementation of an Information Security Management System (ISMS). This approach demands significant initial investment in developing systematic security processes, documenting controls, and establishing a continuous improvement framework.
SOC 2 offers a more adaptable path, allowing organizations to demonstrate their current security practices without the same level of structural overhaul. This makes it an attractive option for smaller organizations or those with limited resources. However, the flexibility comes with the need for ongoing assessment and potential frequent adjustments to meet changing security requirements.
Strategic Approach and Comprehensive Coverage
Many forward-thinking organizations are choosing a dual approach. StrongDM suggests that pursuing both ISO 27001 and SOC 2 can provide comprehensive security coverage. This strategy allows organizations to establish a robust ISMS through ISO 27001 while maintaining the flexibility to conduct detailed security assessments through SOC 2 reports.
The decision isn't always about choosing one standard over another. Instead, consider how these frameworks can complement each other in your overall security strategy. Some organizations start with SOC 2 to gain immediate insights into their security controls and then progress to ISO 27001 for a more structured, long-term approach to information security management.
Ultimately, the right choice depends on your specific organizational goals, client expectations, and industry requirements. Consult with security professionals, review your current security posture, and consider the long-term benefits of each standard. Remember that information security is not a one-time achievement but an ongoing commitment to protecting your organization's most valuable assets.
Certification Process, Costs, and Compliance Tips
Navigating the certification landscape for ISO 27001 and SOC 2 requires strategic planning, financial investment, and a comprehensive understanding of the compliance journey. Each standard presents unique challenges and opportunities for organizations seeking to demonstrate their commitment to information security.
Certification Timelines and Preparation
Secureframe reveals significant differences in certification timelines between ISO 27001 and SOC 2. ISO 27001 certification typically demands a more extended preparation period, spanning six to twelve months. This comprehensive process involves developing a robust Information Security Management System (ISMS), conducting thorough risk assessments, and creating extensive documentation that covers organizational security practices.
SOC 2 offers a comparatively shorter path. Type 1 audits can be completed in just a few months, providing a snapshot of an organization's security controls. Type 2 audits require three to twelve months of control observation, offering a more in-depth evaluation of security practices over time. This flexibility makes SOC 2 attractive for organizations seeking a more adaptable compliance approach.
Financial Investments and Cost Considerations
The financial commitment for certification varies significantly between these standards. According to Secureframe, ISO 27001 certification costs typically range from $10,000 to $50,000, reflecting the comprehensive nature of the audit process. This investment covers extensive documentation, initial and surveillance audits, and the implementation of a comprehensive security management system.
SOC 2 audits present a slightly different financial landscape. Type 1 audits average between $10,000 and $20,000, while Type 2 audits can range from $30,000 to $60,000. The cost variation depends on the complexity of an organization's security controls and the specific Trust Services Criteria being evaluated. While potentially less expensive than ISO 27001, SOC 2 still requires significant financial and organizational commitment.
Compliance Strategy and Best Practices
Successful compliance requires a strategic approach tailored to each standard's unique requirements. Secureframe recommends that organizations pursuing ISO 27001 focus on developing comprehensive policies, conducting rigorous risk assessments, and establishing a continuous improvement framework for their ISMS. This approach demands a holistic view of information security that extends beyond mere technical controls.
For SOC 2, the emphasis lies in selecting relevant Trust Services Criteria and maintaining meticulous control documentation. Organizations must prepare detailed evidence demonstrating the effectiveness of their security controls. This requires ongoing documentation, regular internal assessments, and a commitment to maintaining high security standards.
Whether choosing ISO 27001, SOC 2, or pursuing both, organizations must view certification as more than a one-time achievement. It represents an ongoing commitment to information security, requiring continuous improvement, adaptation to emerging threats, and a proactive approach to risk management. Success demands not just financial investment but also organizational culture that prioritizes security as a fundamental business strategy.
Frequently Asked Questions
What is the main difference between ISO 27001 and SOC 2?
ISO 27001 is an international certification that requires organizations to implement a comprehensive Information Security Management System (ISMS) with 93 predefined controls, while SOC 2 is a flexible attestation that evaluates an organization's security controls against five Trust Services Criteria.
Which standard should my organization choose, ISO 27001 or SOC 2?
The choice depends on several factors such as your industry, geographic location, and specific needs. ISO 27001 is beneficial for global organizations, while SOC 2 is particularly relevant for technology companies in North America. Some organizations opt for both to cover diverse security requirements.
How much does it cost to obtain ISO 27001 certification compared to SOC 2?
ISO 27001 certification typically costs between $10,000 to $50,000 depending on the organization's complexity and needs. In contrast, SOC 2 audits can range from $10,000 for Type 1 to $60,000 for Type 2 reports, reflecting their different scopes and requirements.
How long does the certification process take for ISO 27001 and SOC 2?
ISO 27001 certification generally requires a longer preparation period of six to twelve months to develop an ISMS. In contrast, SOC 2 Type 1 audits can be completed in a few months, while Type 2 audits involve a 3-12 month evaluation period.
Ready to Conquer Security Questionnaire Overload After Your ISO 27001 or SOC 2 Journey?
Choosing between ISO 27001 and SOC 2 is just the beginning. Now, you face the reality of proving your controls again and again through endless security questionnaires and third-party risk assessments. If you have ever lost valuable sales time or felt the stress from repetitive, manual answers to security reviews, Skypher can help your team stay focused and compliant.

See how Skypher uses AI-driven automation to simplify the complexities revealed in your security certification process, whether for ISO 27001 or SOC 2. Our platform integrates with 40+ TPRM tools and gives you a customizable Trust Center so you answer once and impress every stakeholder. Visit our homepage and experience how Skypher turns compliance pain into operational efficiency. Get started now and never lose momentum to manual questionnaires again.