Information security keeps getting tougher for every organization out there. ISO 27002 now groups its security controls into just four focused domains with only 93 controls instead of the old 114, making it leaner than ever. Here’s what might surprise you. Most companies still treat these controls as just a checklist. That’s where they trip up. Adopting the latest ISO 27002 is less about ticking boxes and more about building a living, adaptive shield against today’s threats—and the difference can decide who stays safe and who gets left behind.
Table of Contents
- Understanding ISO 27002 And Its Purpose
- Key Security Controls In ISO 27002
- Implementing ISO 27002 In Your Organization
- ISO 27002 Updates And Best Practices For 2025
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understand the Purpose of ISO 27002 | ISO 27002 offers a structured approach to managing information security risks with tailored, actionable controls across four domains: organizational, people, physical, and technological. |
| Phased Implementation Strategy | Adopting a gradual implementation process is essential. Organizations should assess readiness, conduct risk assessments, and prioritize control integration incrementally. |
| Integration of Privacy Principles | The updated standard emphasizes aligning with privacy regulations like GDPR, focusing on data minimization, transparent policies, and robust consent mechanisms. |
| Emphasize Human Factors | Acknowledging human elements in security is vital. Implement personnel screening and security awareness training to mitigate risks associated with human error. |
| Adopt Emerging Best Practices | Organizations should implement continuous threat monitoring, adaptive security architectures, and explore AI-driven analysis to proactively respond to evolving cyber threats. |
Understanding ISO 27002 and Its Purpose
Information security has become a critical concern for organizations navigating complex digital environments. ISO 27002 emerges as a pivotal framework designed to help businesses establish robust information protection strategies.
The Core Purpose of ISO 27002
ISO 27002 represents an internationally recognized standard that provides comprehensive guidance for implementing information security controls. According to research from the International Organization for Standardization, the standard offers organizations a structured approach to managing information security risks effectively. Unlike generic security recommendations, ISO 27002 provides specific, actionable controls that can be tailored to an organization's unique technological and operational landscape.
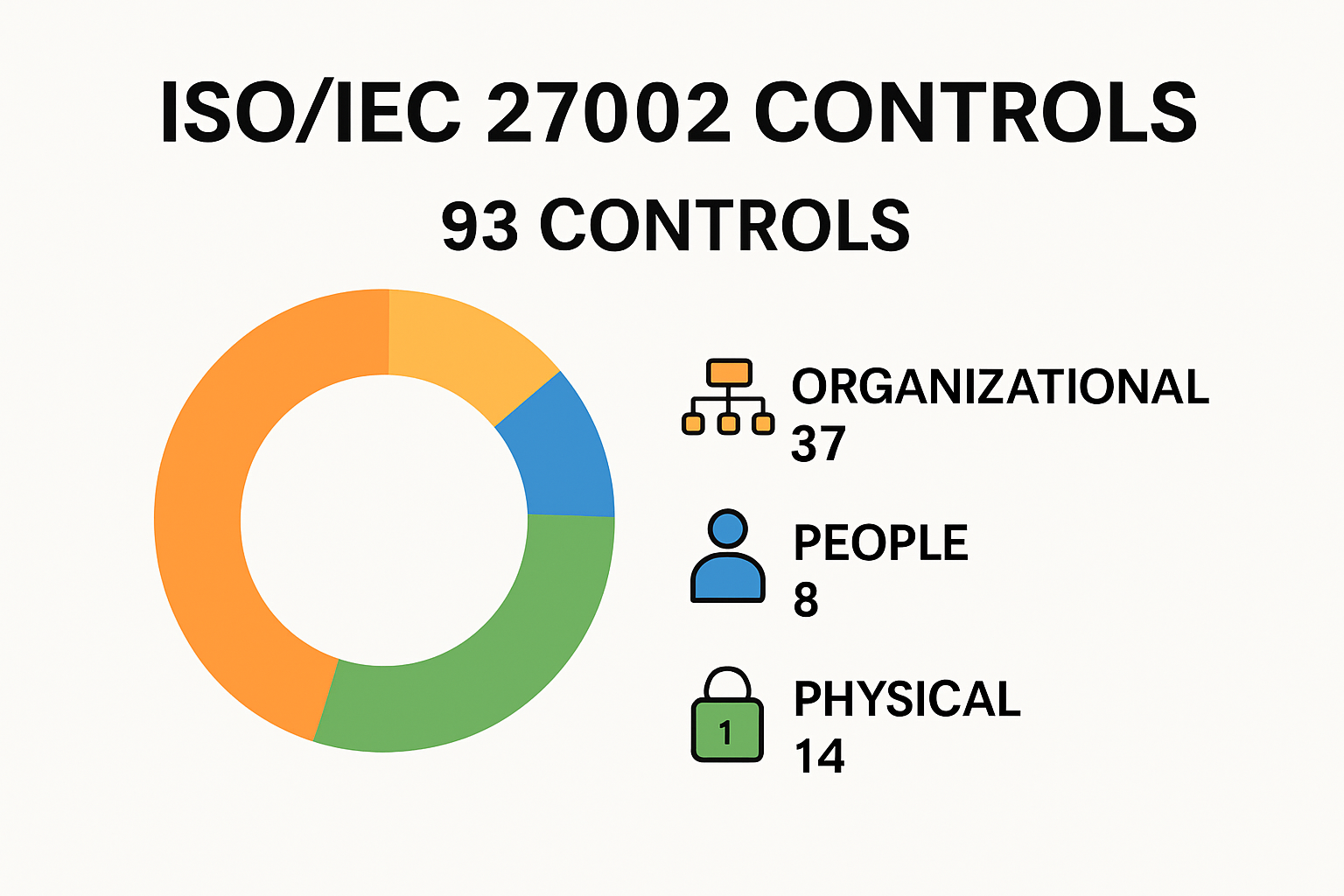
The 2022 revision of the standard significantly transformed its approach, reducing the number of controls from 114 to 93 and categorizing them into four critical domains: organizational, people, physical, and technological. This strategic restructuring reflects the evolving nature of cybersecurity challenges and the need for more targeted, adaptable security frameworks.
Key Domains of Information Security Control
ISO 27002 breaks down information security management into four interconnected domains, each addressing specific aspects of organizational protection:
- Organizational Controls: Focus on establishing comprehensive security policies, risk assessment methodologies, and governance structures
- People Controls: Address human factors in security, including training, awareness programs, and personnel screening
- Physical Controls: Provide guidelines for protecting physical infrastructure, access points, and tangible assets
- Technological Controls: Offer detailed recommendations for digital security, including network protection, system configuration, and data encryption
By providing detailed implementation guidance, ISO 27002 complements ISO 27001, enabling organizations to develop more comprehensive and effective information security management systems. The standard recognizes that security is not a one-size-fits-all solution but requires nuanced, context-specific approaches.
The framework's significance extends beyond theoretical recommendations. It serves as a practical toolkit for security professionals, offering clear, actionable steps to identify vulnerabilities, implement protective measures, and continuously improve an organization's security posture. Whether an organization operates in finance, technology, healthcare, or any other sector, ISO 27002 provides a universal language for understanding and addressing information security challenges.
Organizations adopting ISO 27002 gain more than just a set of guidelines. They receive a strategic framework that helps them anticipate potential threats, develop resilient security infrastructure, and demonstrate a commitment to protecting sensitive information. In an era of increasing cyber risks, this standard represents a critical resource for maintaining trust, compliance, and operational integrity.
To help clarify and compare the four critical domains introduced in ISO 27002, the table below summarizes the main focus and examples for each domain.
| Domain | Primary Focus | Example Controls |
|---|---|---|
| Organizational | Policies, risk management, governance | Security policies, risk assessments |
| People | Human factors & behavior | Personnel screening, training |
| Physical | Protection of physical assets & premises | Access control, visitor management |
| Technological | Digital, network, and IT system security | Encryption, incident response |
Key Security Controls in ISO 27002
Information security demands a strategic and comprehensive approach. ISO 27002 provides organizations with a robust framework of security controls that address the complex challenges of protecting digital assets and sensitive information.
Organizational and Operational Security Controls
According to the International Organization for Standardization, organizational security controls form the foundation of an effective information security management system. These controls focus on establishing clear policies, defining responsibilities, and creating a structured approach to risk management. Key aspects include developing comprehensive security policies, conducting regular risk assessments, and implementing robust governance frameworks.
Project management represents a critical area of organizational security. Research from ISO highlights the importance of integrating security considerations throughout the project lifecycle, ensuring that security is not an afterthought but a fundamental component of organizational strategy. This approach helps prevent potential vulnerabilities from emerging during project development and implementation.
People and Physical Security Domains

Human factors play a crucial role in information security. ISO 27002 emphasizes the significance of people controls that address the human element of cybersecurity. These controls include:
- Personnel Screening: Implementing thorough background checks and verification processes
- Security Awareness Training: Developing comprehensive programs to educate employees about potential security risks
- Access Management: Creating clear protocols for user access and privilege management
Research from the National Institute of Standards and Technology underscores that human error remains one of the most significant security vulnerabilities. Physical security controls complement these efforts by protecting tangible assets and infrastructure. This includes securing physical access points, implementing visitor management systems, and protecting critical infrastructure from unauthorized access.
Technological Security Mechanisms
Technological controls represent the most dynamic aspect of ISO 27002, addressing the rapidly evolving digital threat landscape. These controls encompass a wide range of digital protection strategies, including:
- Network security protection
- Data encryption mechanisms
- System configuration and hardening
- Incident detection and response systems
- Secure software development practices
Cybersecurity experts from SANS Institute emphasize that technological controls must be continuously updated to address emerging threats. The 2022 revision of ISO 27002 reflects this need by providing more flexible and adaptable control mechanisms that can respond to the changing cybersecurity environment.
Implementing these controls requires a holistic approach. Organizations must view security not as a one-time implementation but as an ongoing process of assessment, improvement, and adaptation. By embracing the comprehensive framework provided by ISO 27002, businesses can develop a more resilient and proactive approach to information security, protecting their most valuable digital assets from an increasingly sophisticated threat landscape.
Implementing ISO 27002 in Your Organization
Successful implementation of ISO 27002 requires a strategic and systematic approach that goes beyond simple checklist compliance. Organizations must develop a comprehensive strategy that integrates information security deeply into their operational framework.
Assessing Organizational Readiness
Research from Alencar et al. demonstrates the critical importance of developing an adaptable maturity strategy for information security implementation. Before diving into control implementation, organizations must conduct a thorough assessment of their current security posture. This initial evaluation helps identify existing gaps, strengths, and areas requiring immediate attention.
According to a study by Alkalbani et al., several socio-organizational factors significantly impact successful information security compliance:
- Management Commitment: Ensuring top-level leadership actively supports and drives security initiatives
- Awareness and Training: Developing comprehensive security education programs
- Accountability: Establishing clear responsibilities for security management
- Technology Capability: Assessing and upgrading technological infrastructure
- Process Integration: Embedding security controls into existing organizational workflows
The following table summarizes the key organizational readiness factors and their roles in successful ISO 27002 implementation.
| Factor | Role/Description |
|---|---|
| Management Commitment | Leadership support to drive and sustain security programs |
| Awareness and Training | Educating employees and promoting a security culture |
| Accountability | Clear assignment of responsibilities for security |
| Technology Capability | Ensuring infrastructure can support security requirements |
| Process Integration | Embedding controls into organizational operations |
Phased Implementation Strategy
Implementing ISO 27002 is not an overnight process. Organizations should adopt a phased approach that allows for gradual integration and continuous improvement. Research from academic security studies suggests a maturity model that progresses through distinct stages of security implementation.
Key steps in this phased approach include:
- Conducting a comprehensive initial risk assessment
- Developing a detailed security policy framework
- Prioritizing critical security controls
- Implementing controls in stages
- Continuous monitoring and improvement
Overcoming Implementation Challenges
Organizations often encounter significant challenges when implementing ISO 27002. Cybersecurity experts recommend addressing these challenges through:
- Cultural Transformation: Creating a security-first mindset across the entire organization
- Resource Allocation: Dedicating sufficient budget and personnel to security initiatives
- Continuous Education: Maintaining ongoing training and awareness programs
- Flexible Adaptation: Remaining agile in response to emerging security threats
Successful implementation requires more than technical controls. It demands a holistic approach that combines technological solutions, human factors, and organizational processes. The goal is not merely compliance but creating a robust, adaptive security ecosystem that protects the organization's most valuable assets.
By approaching ISO 27002 implementation as a strategic journey rather than a destination, organizations can develop a dynamic and resilient information security framework. This approach transforms security from a mere compliance requirement into a competitive advantage, building trust with stakeholders and protecting critical business operations.
ISO 27002 Updates and Best Practices for 2025
The information security landscape continues to evolve rapidly, demanding adaptive and forward-thinking approaches. ISO 27002 has responded to these challenges with significant updates that reflect the complex digital environment organizations now navigate.
Key Updates in the 2022 Revision
According to ISACA, the 2022 revision introduced 11 new controls specifically designed to address emerging information security challenges. These updates represent a strategic response to the changing technological and threat landscapes.
The most notable changes include the introduction of controls for:
- Threat Intelligence: Proactive mechanisms for identifying and responding to potential security risks
- Cloud Services Security: Comprehensive guidelines for managing information security in cloud environments
- Business Continuity Readiness: Enhanced ICT preparedness for maintaining operational resilience
Research from cybersecurity experts highlights that the revision streamlined the previous 114 controls into 93, reorganizing them into four critical categories: Organizational, People, Physical, and Technological. This restructuring allows for more targeted and flexible security implementation.
Privacy and Data Protection Integration
The updated standard emphasizes the integration of privacy principles, aligning closely with global regulations like the General Data Protection Regulation (GDPR). This approach recognizes that modern information security goes beyond traditional protection mechanisms, requiring a holistic view of data privacy and organizational accountability.
Key privacy-focused best practices for 2025 include:
- Implementing robust data minimization strategies
- Developing transparent data processing policies
- Creating comprehensive privacy impact assessment frameworks
- Establishing clear consent and data subject rights mechanisms
Emerging Best Practices for 2025
Organizations looking to stay ahead of security challenges should focus on several critical areas:
- Continuous Threat Monitoring: Developing real-time threat intelligence capabilities
- Adaptive Security Architecture: Creating flexible security frameworks that can quickly respond to new threats
- Zero Trust Implementation: Moving beyond traditional perimeter-based security models
- AI-Powered Security Analysis: Leveraging advanced technologies for more sophisticated threat detection
Cybersecurity researchers emphasize that the future of information security lies in proactive, intelligence-driven approaches. The 2025 landscape demands more than static control implementation—it requires a dynamic, responsive security ecosystem that can anticipate and mitigate emerging risks.
The ISO 27002 updates reflect a broader understanding that information security is no longer a technical checkbox but a critical strategic imperative. Organizations must view these guidelines not as rigid requirements, but as a flexible framework for building resilient, adaptive security capabilities that protect their most valuable assets in an increasingly complex digital world.
Frequently Asked Questions
What is ISO 27002?
ISO 27002 is an internationally recognized standard that provides guidelines for implementing information security controls to help organizations manage information security risks effectively.
How has ISO 27002 changed in the 2022 revision?
The 2022 revision of ISO 27002 updated the framework by reducing the number of controls from 114 to 93 and categorizing them into four focused domains: organizational, people, physical, and technological.
Why is a phased implementation strategy important for ISO 27002?
A phased implementation strategy allows organizations to gradually integrate security controls, assess their readiness, and prioritize what needs immediate attention, ensuring a comprehensive and sustainable approach to information security.
How does ISO 27002 address emerging cybersecurity threats?
ISO 27002’s latest revision includes controls focused on threat intelligence, cloud services security, and business continuity readiness, which are designed to help organizations adapt to the evolving cybersecurity landscape.
Transform ISO 27002 Compliance Into Competitive Advantage
Still managing information security controls as just another checklist? Struggling to keep up with evolving ISO 27002 requirements, especially as your teams juggle lengthy security questionnaires and vendor due diligence? You are not alone. Many organizations face the same challenges highlighted in our guide, from reviewing complex controls to demonstrating compliance under pressure. Inefficiencies here slow down sales cycles, threaten trust, and steal valuable time from your core business.

Discover real efficiency with Skypher. Our AI-driven platform automates the entire security questionnaire process and aligns your responses with the latest information security standards, including ISO 27002. No more wasted hours copy-pasting answers or worrying about consistency. Collaborate with your team in real time while reducing delays in proof of concepts and contracts. Ready to show your clients and auditors that your controls are not only compliant but also always up to date? Visit https://skypher.co today and experience how automation and accuracy can put you ahead of the competition.