Security leaders know the challenge of shaping a resilient framework that aligns with global best practices and ever-changing regulations. When operations span across continents and sensitive data grows in scale, effective standards become more than an expectation—they are a necessity. The ISO/IEC 27000 family stands out as a trusted blueprint for systematic risk management and proactive security governance, offering CISOs and compliance managers a proven path to safeguarding critical assets and driving operational consistency.
Table of Contents
- Defining ISO Information Security Standards
- Major ISO Information Security Frameworks
- Key Requirements and Certification Process
- Roles and Responsibilities in Compliance
- Common Pitfalls and Risk Management
Key Takeaways
| Point | Details |
|---|---|
| Risk-Based Approach | Implementing ISO/IEC 27000 standards helps organizations develop a proactive framework that anticipates and mitigates security risks. |
| Certification Process | Achieving ISO/IEC 27001 certification requires comprehensive documentation and a thorough risk assessment to validate an organization's security management capabilities. |
| Role Clarity | Defining roles and responsibilities at various organizational levels is crucial for effective compliance and security management. |
| Continuous Improvement | Organizations must adopt a culture of security awareness and regular training to address potential vulnerabilities and ensure resilience against digital threats. |
Defining ISO Information Security Standards
Information security standards represent a critical framework for organizations seeking to protect their digital assets and manage technological risks. The ISO/IEC 27000 family provides a comprehensive international approach to establishing robust information security management systems (ISMS), offering organizations a systematic method for identifying, assessing, and mitigating security vulnerabilities.
At its core, the ISO standards focus on creating a structured methodology for managing information security risks. International security management standards define precise requirements for implementing comprehensive security controls across technological, human, and procedural domains. These standards are not merely theoretical guidelines but practical blueprints that enable businesses to develop resilient security infrastructures that can adapt to evolving digital threats.
The primary goal of these standards is establishing a risk-based approach to information security. Organizations can systematically evaluate potential vulnerabilities, implement appropriate safeguards, and continuously monitor their security posture. By following ISO guidelines, companies create a proactive framework that goes beyond reactive security measures, focusing instead on anticipating and preventing potential breaches before they occur.
Pro tip: When implementing ISO information security standards, start by conducting a comprehensive risk assessment that identifies your organization's unique vulnerabilities and prioritizes security investments accordingly.
Major ISO Information Security Frameworks
The ISO/IEC 27000 series provides a comprehensive suite of international standards designed to address the complex landscape of information security management. At the forefront of these frameworks is ISO/IEC 27001, which serves as the foundational standard for establishing robust information security management systems (ISMS) across diverse organizational environments.
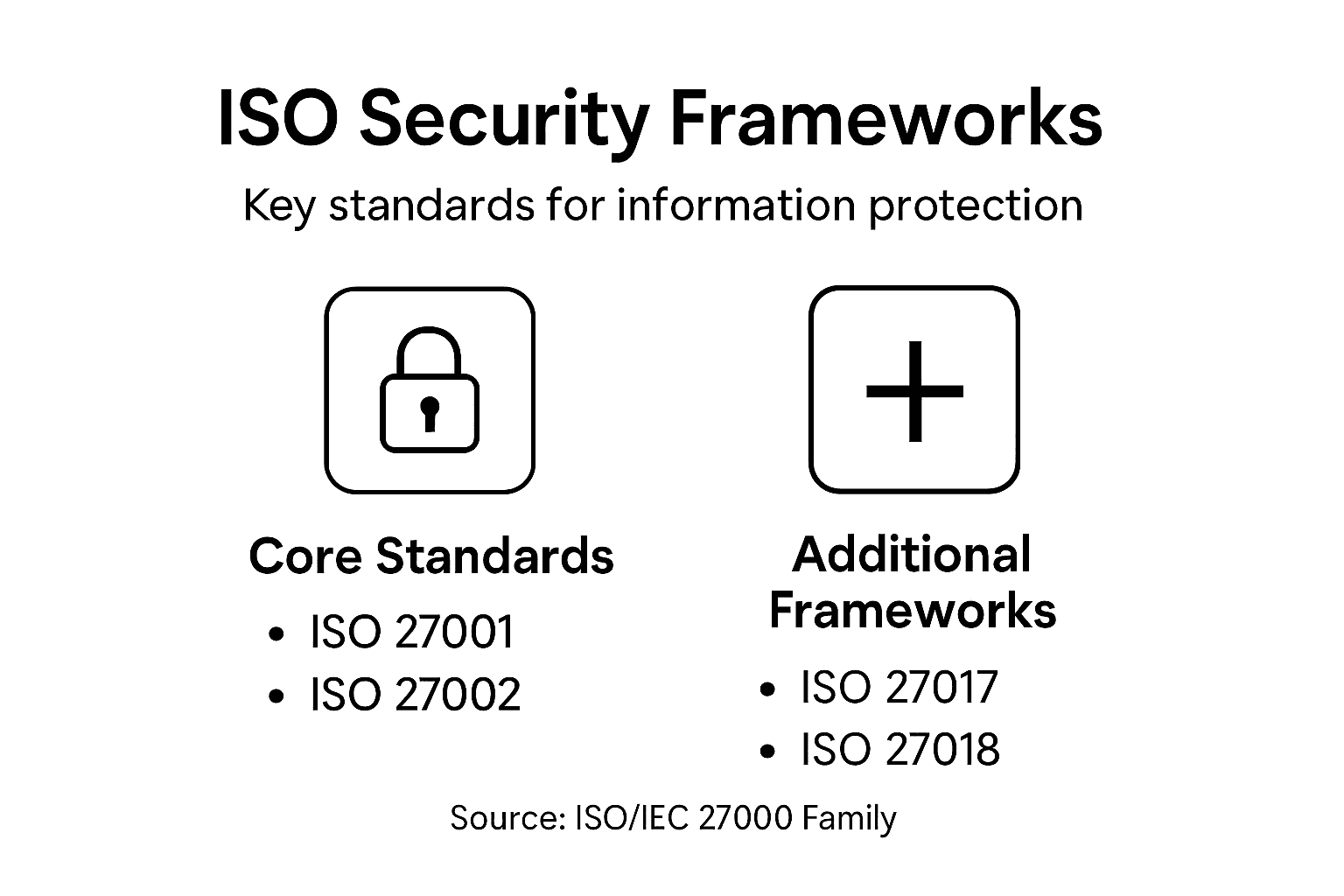
Within the series, multiple key frameworks play critical roles in creating holistic security strategies. International security management standards define a structured approach that enables organizations to systematically identify, assess, and mitigate information security risks. The primary frameworks include ISO/IEC 27001 (ISMS requirements), ISO/IEC 27002 (security controls guidance), ISO/IEC 27005 (risk management), and ISO/IEC 27017 (cloud security), each addressing specific aspects of comprehensive security governance.
Each framework serves a distinct purpose in the information security ecosystem. ISO/IEC 27001 establishes the overarching requirements for an ISMS, providing a model for creating, implementing, maintaining, and continually improving security management processes. ISO/IEC 27002 complements this by offering detailed security control guidelines, helping organizations implement practical safeguards across technological, operational, and administrative domains. Other specialized standards like ISO/IEC 27017 focus on emerging technological challenges, such as cloud security, reflecting the evolving nature of digital risk management.
The following table summarizes key ISO/IEC 27000 series frameworks and their specific focus areas:
| Framework | Main Purpose | Typical Use Case |
|---|---|---|
| ISO/IEC 27001 | Sets ISMS requirements | Establishing security programs |
| ISO/IEC 27002 | Provides control implementation guidance | Selecting and applying controls |
| ISO/IEC 27005 | Focuses on risk management methodologies | Risk assessment and mitigation |
| ISO/IEC 27017 | Addresses cloud security best practices | Securing cloud environments |
Pro tip: When implementing ISO security frameworks, conduct a thorough gap analysis to understand your current security posture and prioritize standard implementation based on your organization's specific risk profile and technological infrastructure.
Key Requirements and Certification Process
The ISO/IEC 27001 certification process represents a rigorous and systematic approach to validating an organization's information security management capabilities. Information security certification requirements demand comprehensive documentation, risk assessment, and implementation of robust security controls that demonstrate an organization's commitment to protecting critical digital assets.

The certification journey encompasses several critical stages. Organizations must first conduct a thorough risk assessment, identifying potential vulnerabilities across their technological infrastructure, data management processes, and organizational workflows. This initial evaluation forms the foundation for developing a tailored Information Security Management System (ISMS) that addresses specific organizational risks. The process requires creating detailed documentation including security policies, risk treatment plans, and comprehensive control implementation strategies that align with ISO 27001 framework guidelines.
The external certification audit represents the culmination of an organization's preparation and commitment to information security. An accredited, independent auditing body will meticulously examine the organization's ISMS, evaluating the effectiveness of implemented controls, reviewing documentation, and assessing the overall security governance framework. Successful certification requires demonstrating not just the existence of security measures, but also proving their consistent application and continuous improvement mechanisms. Organizations must be prepared to showcase how their security strategies adapt to evolving technological landscapes and emerging threat environments.
Pro tip: Maintain a living documentation system that tracks all security control implementations, updates, and improvements to streamline future certification and recertification processes.
Roles and Responsibilities in Compliance
Information security compliance demands a structured approach to defining organizational roles and responsibilities. Information security governance requires strategic involvement from multiple layers of organizational leadership, ensuring a comprehensive and integrated approach to managing digital risks and protecting critical assets.
The organizational hierarchy of information security compliance typically involves three primary tiers of responsibility. At the executive level, top management and the governing body are responsible for establishing overarching security policies, allocating resources, and ensuring that security objectives align with broader business strategies. The Information Security Manager serves as a critical operational role, translating high-level directives into actionable implementation plans, managing risk assessments, and coordinating the development and maintenance of the Information Security Management System (ISMS).
Beyond leadership roles, every employee plays a crucial part in maintaining organizational security. This includes understanding and adhering to established security policies, participating in regular training and awareness programs, and actively reporting potential security incidents or vulnerabilities. Individual accountability becomes a cornerstone of effective security governance, transforming compliance from a top-down mandate into a collaborative, organization-wide commitment. Successful implementation requires clear communication, ongoing education, and a culture that prioritizes security as a shared responsibility across all organizational levels.
Here's a comparison of organizational roles and their core responsibilities in ISO information security compliance:
| Organizational Level | Primary Responsibility | Key Actions Performed |
|---|---|---|
| Executives | Set policy and allocate resources | Approve strategy, fund initiatives |
| Information Security Manager | Develop and manage ISMS | Lead assessments, coordinate controls |
| All Employees | Daily compliance and vigilance | Follow policies, report incidents |
Pro tip: Create a comprehensive role matrix that clearly defines security responsibilities, reporting structures, and accountability for each organizational level to ensure transparent and effective information security management.
Common Pitfalls and Risk Management
Navigating the complex landscape of information security requires a sophisticated understanding of potential vulnerabilities and strategic risk mitigation. Information security risk management demands a proactive approach that anticipates and addresses potential systemic weaknesses before they can compromise organizational integrity.
Organizations frequently encounter several critical pitfalls that can undermine their information security efforts. These include inadequate risk identification processes, insufficient stakeholder engagement, and misalignment between security controls and business objectives. Many companies struggle with developing comprehensive risk assessment frameworks that capture the nuanced and dynamic nature of modern technological threats. Incomplete documentation, sporadic employee training, and a reactive rather than proactive security mindset can create significant gaps in an organization's defensive strategies.
Effective risk management requires a holistic and continuous approach that integrates technical controls, human factors, and organizational processes. Successful organizations develop robust risk assessment methodologies that include regular vulnerability scanning, threat modeling, and adaptive security protocols. This involves creating a culture of security awareness, implementing comprehensive training programs, and establishing clear communication channels for reporting and addressing potential security incidents. The goal is not just compliance, but building a resilient security ecosystem that can anticipate, respond to, and mitigate emerging digital risks.
Pro tip: Implement a quarterly risk assessment review process that involves cross-functional teams and leverages both automated scanning tools and human expertise to identify and prioritize potential security vulnerabilities.
Streamline ISO Compliance with Skypher’s Automated Security Questionnaire Solutions
Navigating the complexities of ISO information security standards requires meticulous documentation, thorough risk assessments, and effective collaboration across all organizational roles. Challenges like maintaining up-to-date security controls and demonstrating consistent compliance during audits can slow down your journey to certification and risk management. Skypher’s AI Questionnaire Automation Tool directly addresses these pain points by accelerating responses to security questionnaires, enhancing accuracy, and providing seamless integration with over 40 third-party risk management platforms.

Take control of your information security compliance today by leveraging Skypher’s platform to reduce time spent on security reviews and improve stakeholder collaboration. With features like real-time integration with Slack and ServiceNow, multilingual support, and a customizable Trust Center, Skypher empowers medium to large organizations in tech and finance to build trust while efficiently managing their ISO 27001 certification requirements. Visit Skypher.co and discover how easy it is to automate your compliance workflows and strengthen your security posture now.
Frequently Asked Questions
What are ISO information security standards?
ISO information security standards are a set of international guidelines, specifically the ISO/IEC 27000 family, that provide frameworks for establishing and managing information security management systems (ISMS) to protect digital assets and manage technological risks.
How does ISO/IEC 27001 certification benefit organizations?
ISO/IEC 27001 certification helps organizations validate their information security management capabilities, ensuring they have comprehensive documentation, robust security controls, and a risk-based approach to managing their information security efforts, which builds trust with stakeholders.
What is the purpose of the ISO/IEC 27002 framework?
The ISO/IEC 27002 framework offers detailed guidance on security controls that organizations can implement to protect their information assets. It complements ISO/IEC 27001 by providing practical measures for establishing effective security practices across various domains.
Why is risk assessment important in ISO compliance?
Risk assessment is crucial in ISO compliance as it allows organizations to identify and evaluate potential vulnerabilities within their technological infrastructure. It forms the foundation for developing a tailored Information Security Management System (ISMS) that addresses specific risks and implements appropriate controls.