Choosing the right security standard can shape your organization’s compliance future. For CISOs and compliance managers in tech and finance, clear distinctions between ISO 27001 certification and SOC 2 drive both regulatory alignment and client trust. Each framework brings unique requirements, global recognition, and sector relevance, making the decision critical for operational resilience and market positioning. This guide cuts through complexity so you can take informed steps toward stronger, more transparent security compliance.
Table of Contents
- Defining ISO27001 And SOC 2 Standards
- Core Requirements And Compliance Processes
- Audit Scope, Reporting, And Certification Differences
- Practical Impacts For Tech And Finance Firms
- Selecting The Best Fit For Your Organization
Key Takeaways
| Point | Details |
|---|---|
| ISO 27001 provides a comprehensive management system | It focuses on a systematic risk management approach encompassing people, processes, and technology. |
| SOC 2 emphasizes trust service criteria | It specifically targets security, availability, processing integrity, confidentiality, and privacy for service organizations. |
| Both standards can create a stronger security posture | Organizations often pursue both certifications to enhance their credibility and commitment to information security. |
| Strategic alignment is critical when choosing a standard | Assess factors like geographic scope, industry regulations, and resource capabilities to select the appropriate framework. |
Defining ISO27001 and SOC 2 Standards
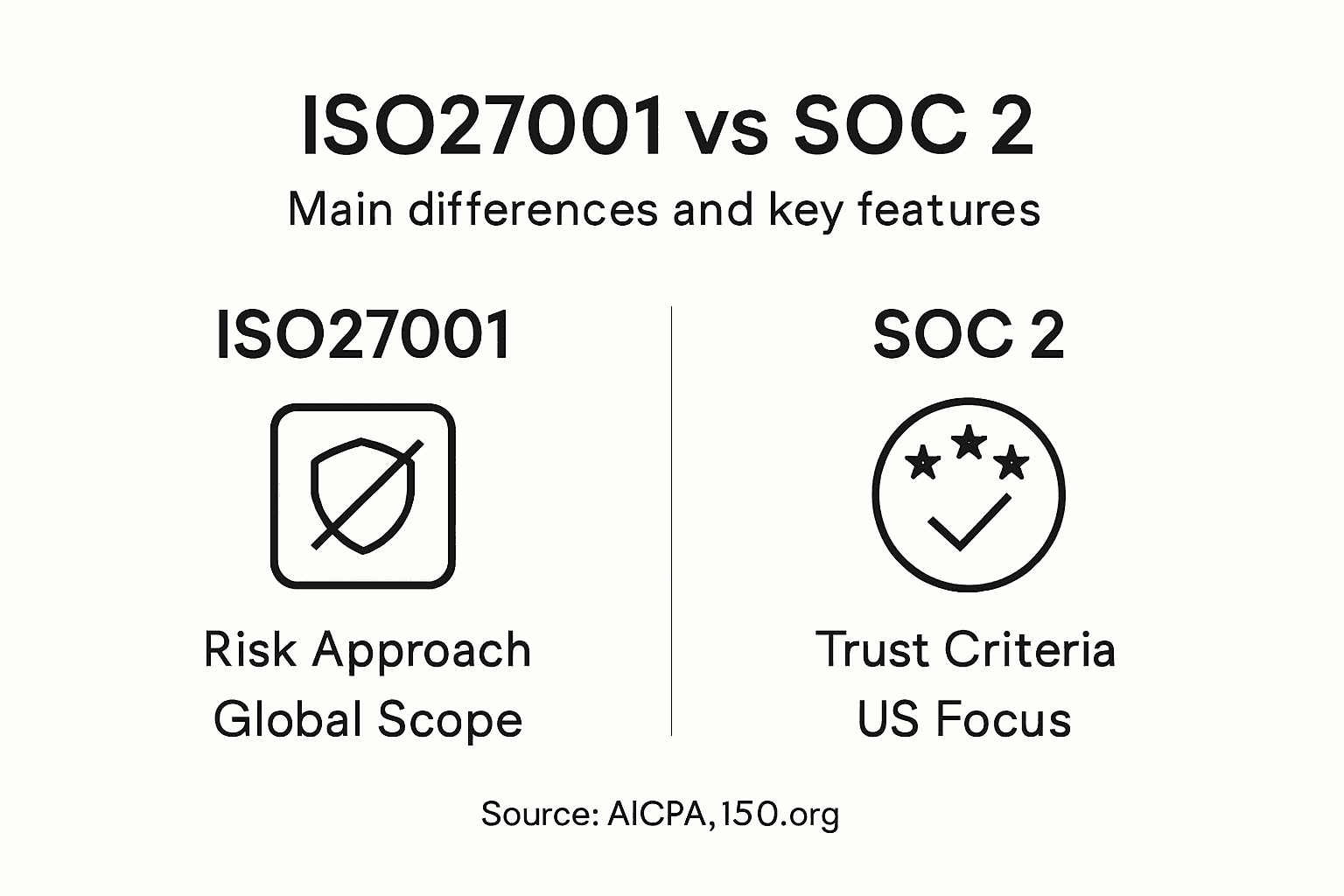
Organizations seeking robust cybersecurity frameworks frequently encounter two prominent international standards: ISO 27001 and SOC 2. While both aim to enhance information security, they differ significantly in origin, scope, and implementation approach.
The ISO 27001 standard, developed by the International Organization for Standardization, provides a comprehensive systematic approach to managing sensitive company information. ISO 27001 consulting guide reveals this framework encompasses a holistic risk management process covering people, processes, and technology. Organizations implementing this standard must:
- Conduct thorough information security risk assessments
- Develop systematic control mechanisms
- Establish continuous improvement protocols
- Implement organization-wide security policies
- Create documentation demonstrating compliance
SOC 2, alternatively, represents an American Institute of Certified Public Accountants (AICPA) framework specifically designed for service organizations. Unlike ISO 27001's broader approach, SOC 2 focuses more narrowly on five key trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
The primary distinction lies in their fundamental purpose and implementation. ISO 27001 offers a more proactive, systematic management system, while SOC 2 provides a reactive, attestation-based evaluation of an organization's existing security controls. Companies often pursue both standards to demonstrate comprehensive security commitment.
Here's a concise comparison of ISO 27001 and SOC 2 across core dimensions:
| Aspect | ISO 27001 | SOC 2 |
|---|---|---|
| Geographic Scope | Global recognition | Primarily North America |
| Certification Type | Formal three-year certification | Attestation report; no formal certificate |
| Audit Focus | Management system and processes | Control objectives and operations |
| Industry Adoption | Finance, tech, healthcare | Technology, SaaS, service organizations |
SOC 2 and ISO 27001 are complementary frameworks that help organizations build robust, trustworthy information security practices.
Pro tip: Consult with cybersecurity professionals to determine which standard best aligns with your organization's specific security requirements and industry regulations.
Core Requirements and Compliance Processes
Navigating the compliance landscape for ISO 27001 and SOC 2 requires understanding their distinct yet complementary requirements. SOC 2 compliance path demonstrates the intricate steps organizations must undertake to achieve these critical security certifications.
For ISO 27001, the core compliance process involves a systematic, comprehensive approach:
- Conduct a thorough information security risk assessment
- Develop an Information Security Management System (ISMS)
- Implement robust security controls and policies
- Perform regular internal audits
- Undergo mandatory external certification audits
- Maintain continuous improvement and monitoring
SOC 2 compliance follows a more targeted methodology centered on five trust service criteria. Organizations must demonstrate:
- Security controls protecting against unauthorized access
- System availability and operational reliability
- Processing integrity of data management
- Confidentiality protection mechanisms
- Privacy management of personal information
The key difference lies in their audit approaches. ISO 27001 requires a comprehensive management system certification, while SOC 2 focuses on specific control objectives and provides an attestation report detailing an organization's security practices.
Successful compliance is not a one-time event, but a continuous journey of security enhancement and risk management.
Both standards demand rigorous documentation, periodic assessments, and a commitment to maintaining high security standards. Companies often find that pursuing both certifications creates a more robust, comprehensive security framework.

Pro tip: Develop a cross-functional team with expertise in cybersecurity, legal compliance, and technical implementation to streamline your certification process.
Audit Scope, Reporting, and Certification Differences
The audit processes for ISO 27001 and SOC 2 represent fundamentally different approaches to information security validation. SOC 1 and SOC 2 compliance path illuminates the nuanced differences organizations must understand when pursuing these critical certifications.
For ISO 27001 audits, the scope encompasses a comprehensive evaluation of an organization's entire Information Security Management System (ISMS). Key audit characteristics include:
- Holistic assessment of security governance
- Evaluation of risk management frameworks
- Systematic review of control implementation
- Documentation completeness and consistency
- Verification of continuous improvement processes
- Assessment of organizational security culture
SOC 2 audit reporting differs significantly, focusing on specific trust service criteria with a more granular approach:
- Type I reports assess design of security controls at a specific point in time
- Type II reports evaluate operational effectiveness over a defined period
- Requires detailed evidence of control implementation
- Provides attestation from independent auditors
- Focuses on specific operational security mechanisms
The certification processes also vary dramatically. ISO 27001 certification requires a comprehensive three-year cycle with annual surveillance audits, while SOC 2 generates a report without a formal certification mechanism. This fundamental difference means organizations approach each standard with distinct strategic objectives.
Successful security compliance demands understanding the nuanced differences between audit methodologies and reporting requirements.
Ultimately, while both standards aim to enhance organizational security, they offer different levels of assurance and demonstrate security commitment through unique evaluation approaches.
Pro tip: Engage auditors who specialize in both frameworks to develop a comprehensive, complementary approach to your security compliance strategy.
Practical Impacts for Tech and Finance Firms
Tech and finance organizations face unique challenges in implementing cybersecurity standards, with ISO 27001 and SOC 2 offering critical frameworks for risk management. Cyber risks in financial services underscores the vital importance of robust information security protocols.
For financial institutions, the practical implications of these standards are profound:
- Enhanced credibility with clients and regulators
- Standardized risk assessment methodologies
- Comprehensive protection of sensitive financial data
- Improved incident response capabilities
- Reduced potential for costly security breaches
- Demonstrable commitment to data protection
Technology companies experience equally significant benefits from these compliance frameworks:
- Streamlined security infrastructure development
- Improved vendor and client trust
- Systematic approach to identifying vulnerabilities
- Competitive advantage in security-conscious markets
- Structured framework for continuous security improvement
The standards provide more than just compliance checkboxes. They represent comprehensive approaches to building resilient, trustworthy technological ecosystems that can withstand increasingly sophisticated cyber threats.
Successful implementation transforms compliance from a bureaucratic exercise into a strategic business advantage.
Both ISO 27001 and SOC 2 enable organizations to move beyond reactive security measures, creating proactive, intelligence-driven security strategies that protect critical assets and maintain stakeholder confidence.
Summary of business impacts for finance and technology firms adopting these standards:
| Sector | Key Impact | Strategic Advantage |
|---|---|---|
| Finance | Strong regulatory standing | Greater client trust and retention |
| Technology | Improved security posture | Competitive edge in contracts |
Pro tip: Integrate compliance frameworks into your broader strategic planning, viewing them as opportunities for organizational improvement rather than mere regulatory requirements.
Selecting the Best Fit for Your Organization
Choosing between ISO 27001 and SOC 2 requires careful strategic analysis tailored to your organization's unique requirements. Security framework selection reveals critical considerations that extend beyond simple compliance checkboxes.
Organizations should evaluate the standards based on several key factors:
- Geographic operational scope
- Industry-specific regulatory requirements
- Current security infrastructure maturity
- Client and stakeholder expectations
- Resource allocation capabilities
- Long-term strategic objectives
Decision matrix for selecting the appropriate framework:
-
Choose ISO 27001 if you:
- Operate internationally
- Require a comprehensive risk management system
- Need global security recognition
- Work in highly regulated industries
-
Select SOC 2 if you:
- Primarily serve North American markets
- Need rapid client trust demonstration
- Focus on operational security specifics
- Operate in service-based technology sectors
Many sophisticated organizations recognize that these frameworks are not mutually exclusive. A hybrid approach can provide comprehensive security coverage, addressing both strategic risk management and operational security requirements.
Successful framework selection transforms compliance from a burden into a strategic competitive advantage.
The optimal choice depends on understanding your organization's unique risk landscape, operational context, and strategic growth objectives. Careful, nuanced evaluation will guide you toward the most appropriate security standard.
Pro tip: Consult with cybersecurity professionals who can perform a detailed assessment of your specific organizational needs before committing to a compliance framework.
Streamline Your ISO 27001 and SOC 2 Compliance with Skypher
Navigating the complexities of ISO 27001 and SOC 2 compliance requires more than understanding standards. The challenges of managing extensive security questionnaires, coordinating cross-functional teams, and maintaining rigorous documentation can slow down your cybersecurity progress and delay critical audits. Skypher’s AI Questionnaire Automation Tool offers a powerful solution designed specifically for tech and finance organizations looking to accelerate these processes while increasing accuracy.
Experience how Skypher transforms compliance with features like:
- AI-driven automation to answer hundreds of security questions in under a minute
- Seamless integrations with over 40 third-party risk management platforms including ServiceNow and OneTrust
- Real-time collaboration tools that unify your teams and streamline communication
- A customizable Trust Center that centralizes your compliance evidence and content

Don’t let manual questionnaire responses or fragmented processes hold back your security certification journey. Visit Skypher today and discover how to reduce overhead, improve team efficiency, and confidently demonstrate your commitment to cybersecurity. Explore our AI Questionnaire Automation Tool and learn why medium to large organizations trust Skypher to power their compliance strategy.
Frequently Asked Questions
What is the main difference between ISO 27001 and SOC 2?
ISO 27001 offers a comprehensive systematic approach to managing sensitive information, focusing on an organization's Information Security Management System (ISMS). SOC 2, on the other hand, is more narrowly focused on specific trust service criteria related to service organizations' operational security controls.
Which standard should I pursue first, ISO 27001 or SOC 2?
The choice depends on your organization's specific needs. If you require a comprehensive risk management system and global recognition, ISO 27001 may be ideal. If you need to rapidly demonstrate trust to clients in service-based technology sectors, consider SOC 2 first.
How do the audit processes differ between ISO 27001 and SOC 2?
ISO 27001 audits involve a thorough assessment of the entire Information Security Management System, including governance and risk management frameworks. SOC 2 audits are more specific and evaluate operational effectiveness over time based on trust service criteria, resulting in a detailed attestation report.
Can organizations pursue both ISO 27001 and SOC 2 certifications?
Yes, many organizations pursue both standards. Implementing both can create a more robust security framework, helping to address both strategic risk management and operational security requirements.