Every organization faces digital threats that evolve faster than most people realize, which makes IT security policies much more than just paperwork. Now here’s something surprising. Gartner reports organizations that regularly review their IT security policies are 50 percent less likely to suffer major security breaches. You might expect these policies are simply rigid technical manuals, but the real twist is they work best when treated as living documents people actually understand, backed by real training and a focus on long-term security culture.
Table of Contents
- What Are IT Security Policies?
- Types Of IT Security Policies Explained
- Creating Effective IT Security Policies
- Implementing And Enforcing IT Security Policies
Quick Summary
| Takeaway | Explanation |
|---|---|
| Develop Tailored IT Security Policies | Organizations must create IT security policies that are customized to their specific needs, risk profiles, and technological environments to effectively mitigate cybersecurity risks. |
| Focus on the CIA Triad | Effective policies should be built around the principles of Confidentiality, Integrity, and Availability to safeguard sensitive information and establish security guidelines. |
| Engage in Continuous Policy Review | IT security policies should be viewed as living documents that require regular updates and adjustments to adapt to evolving technologies and emerging threats. |
| Implement Training and Cultural Change | Successful policy enforcement hinges on comprehensive employee training and fostering a culture of security awareness throughout the organization. |
| Utilize Technological Tools for Enforcement | Robust technological infrastructure, including access control systems and monitoring tools, is crucial for ensuring compliance with security policies and detecting violations. |
What are IT Security Policies?
IT security policies represent a critical framework that organizations use to protect their digital assets, establish clear guidelines for technology use, and mitigate potential cybersecurity risks. These comprehensive documents serve as a roadmap for managing and safeguarding an organization's information technology infrastructure and sensitive data.
Definition and Core Purpose
At its core, an IT security policy is a formal set of rules and guidelines that define how an organization manages and protects its information assets. According to the National Institute of Standards and Technology, these policies outline acceptable and unacceptable uses of technology resources while establishing protocols to prevent unauthorized access, modification, or destruction of critical information.
The primary objectives of IT security policies include:
- Protecting Sensitive Information: Establishing clear boundaries for data handling and access
- Reducing Cybersecurity Risks: Creating standardized procedures to minimize potential security breaches
- Ensuring Regulatory Compliance: Aligning organizational practices with industry and legal requirements
Key Components Of Effective IT Security Policies
Comprehensive IT security policies are built around the fundamental CIA triad: Confidentiality, Integrity, and Availability. This framework ensures that organizational data remains private, authentic, and accessible only to authorized personnel. Cybersecurity experts recommend developing policies that address multiple critical areas:
- User Access Management
- Data Protection Protocols
- Network Security Guidelines
- Incident Response Procedures
- Technology Usage Standards
A well-constructed IT security policy goes beyond simple technical restrictions. It creates a culture of security awareness, educating employees about potential risks and their responsibilities in protecting organizational assets. By clearly defining expectations, consequences, and best practices, these policies transform security from a technical requirement into a shared organizational commitment.
Organizations must recognize that IT security policies are not static documents. As technological landscapes evolve and new threats emerge, these policies require regular review and updates. Research from Gartner suggests that successful organizations treat their security policies as living documents, continuously adapting to changing technological and threat environments.
Moreover, effective IT security policies are not one-size-fits-all solutions. They must be tailored to an organization's specific needs, industry regulations, technological infrastructure, and risk profile. This customization ensures that security measures are both comprehensive and practical, addressing unique organizational challenges while maintaining operational efficiency.
Types of IT Security Policies Explained
IT security policies are not monolithic but instead comprise multiple layers and types designed to address different aspects of organizational technology management and protection. Understanding these various policy types helps organizations create a comprehensive and robust security strategy that addresses potential vulnerabilities from multiple perspectives.
Organizational Levels of Security Policies
The National Institute of Standards and Technology identifies three primary categories of IT security policies that organizations typically implement:
-
Organizational (Master) Information Security Policy: This overarching policy establishes the fundamental security principles, high-level goals, and strategic approach to information protection. It serves as the foundational document that guides all subsequent security efforts and sets the tone for the organization's security culture.
-
Issue-Specific Security Policies: These policies target specific technological or operational concerns such as acceptable use, password management, email communication, and remote work guidelines. They provide detailed instructions on handling particular security challenges and define acceptable behaviors for employees.
-
System-Specific Security Policies: Tailored to individual technology systems or platforms, these policies address unique security requirements for specific hardware, software, or network infrastructure. They ensure that each technological component receives targeted protection aligned with its particular vulnerabilities and operational context.
Functional Categories of IT Security Policies
Beyond organizational levels, IT security policies can be categorized by their functional focus. Cybersecurity experts recommend developing policies across several critical domains:
- Access Control Policies: Define user authentication, authorization levels, and permissions for accessing organizational resources
- Data Protection Policies: Establish guidelines for handling, storing, and transmitting sensitive information
- Network Security Policies: Outline protocols for protecting network infrastructure, managing firewalls, and preventing unauthorized access
- Incident Response Policies: Create structured procedures for detecting, reporting, and responding to security breaches
- Compliance and Regulatory Policies: Ensure alignment with industry standards and legal requirements

Strategic Policy Framework Considerations
Research from Gartner suggests that effective IT security policies require a holistic approach that goes beyond simple rule-setting. Organizations must develop policies that are dynamic, adaptable, and integrated across different technological and operational domains.
The HITRUST Common Security Framework provides an excellent example of a comprehensive policy approach. This framework encompasses multiple control categories and offers a structured methodology for developing interconnected security policies that address various organizational needs.
Successful policy development involves continuous assessment, regular updates, and alignment with emerging technological trends and potential security threats. Organizations must view their IT security policies as living documents that evolve alongside their technological infrastructure and threat landscape.
Ultimately, the goal of diverse IT security policies is not just to restrict or control but to create a proactive, informed approach to managing technological risks. By understanding and implementing different types of policies, organizations can build a resilient, adaptive security strategy that protects their most valuable digital assets.
Creating Effective IT Security Policies
Developing robust IT security policies requires a strategic, comprehensive approach that goes beyond simple document creation. These policies serve as critical blueprints for protecting an organization's digital infrastructure and must be carefully crafted to address complex technological challenges and organizational needs.
Key Foundational Elements
Cybersecurity experts recommend a structured methodology for creating effective IT security policies. The process begins with a thorough understanding of the organization's technological ecosystem, potential vulnerabilities, and specific risk profile.
Critical steps in policy development include:
- Comprehensive Risk Assessment: Identify and evaluate potential security threats and vulnerabilities
- Stakeholder Engagement: Collaborate with departments across the organization to understand unique technological requirements
- Clear Objective Definition: Establish specific, measurable security goals aligned with organizational strategy
According to NIST guidelines, successful policy creation requires a holistic approach that considers technical, operational, and human factors. Policies must be designed not just as restrictive documents but as practical guides that enable secure technological operations.
Structural Components And Best Practices
Effective IT security policies should include several key components to ensure comprehensive coverage and clarity. Information Security experts recommend the following essential elements:
- Purpose and Scope: Clearly define the policy's objectives and organizational boundaries
- Roles and Responsibilities: Outline specific responsibilities for different organizational roles
- Detailed Guidelines: Provide specific, actionable instructions for technology use and security protocols
- Compliance Mechanisms: Establish clear consequences for policy violations
- Regular Review and Update Procedures: Create a framework for continuous policy refinement
Language is crucial in policy development. Policies must be written in clear, accessible terms that employees across different technological skill levels can understand. Research from Gartner emphasizes the importance of creating policies that are both technically precise and comprehensible to non-technical staff.
Implementation And Enforcement Strategies
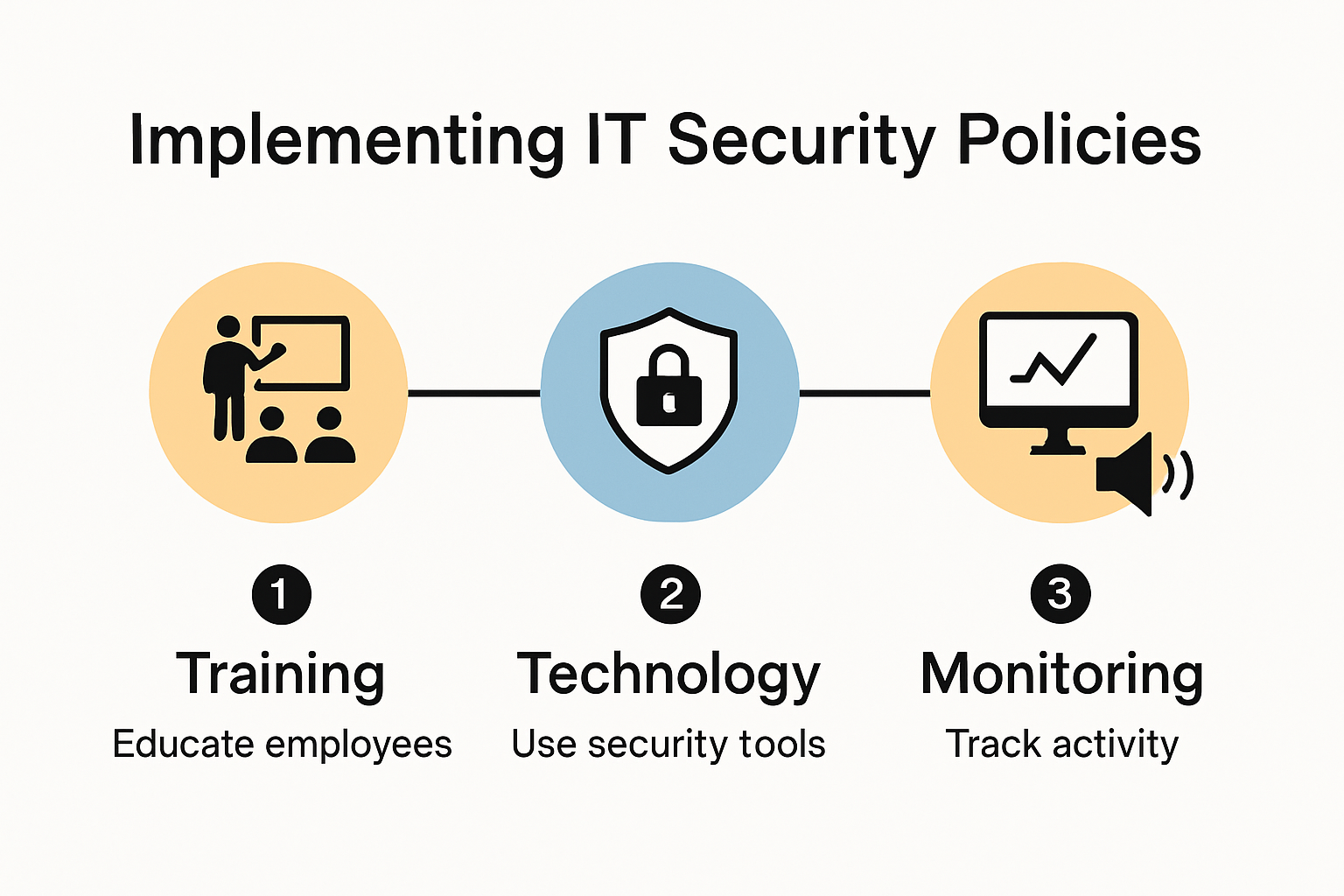 Creating a policy is only the first step. Successful implementation requires a multifaceted approach that combines technological tools, employee training, and organizational culture transformation.
Creating a policy is only the first step. Successful implementation requires a multifaceted approach that combines technological tools, employee training, and organizational culture transformation.
Cybersecurity research highlights several critical implementation strategies:
- Develop comprehensive training programs that explain policy rationales
- Implement technological controls that support policy guidelines
- Create transparent reporting and accountability mechanisms
- Foster a security-conscious organizational culture
Executive leadership plays a pivotal role in policy effectiveness. Security experts stress that top-down support is essential for creating a genuine commitment to security practices. When leadership demonstrates a genuine understanding and commitment to security policies, employees are more likely to take these guidelines seriously.
Ultimately, IT security policies are living documents that must evolve with technological landscapes and emerging threats. Organizations must view policy creation as an ongoing process of assessment, refinement, and adaptation. By approaching security policies as dynamic, collaborative tools rather than static documents, organizations can build more resilient and effective technological defense strategies.
Implementing And Enforcing IT Security Policies
Implementing and enforcing IT security policies represents a critical challenge for organizations seeking to protect their digital assets. Successful implementation goes far beyond simply documenting rules and requires a comprehensive, strategic approach that integrates technological tools, human behavior, and organizational culture.
Technological Infrastructure And Control Mechanisms
Cybersecurity experts from CISA emphasize the importance of creating robust technological infrastructure that supports policy enforcement. This involves deploying sophisticated tools and systems that can automatically monitor, detect, and respond to potential security violations.
Key technological enforcement mechanisms include:
- Access Control Systems: Implement multi-factor authentication and role-based access controls
- Network Monitoring Tools: Deploy real-time intrusion detection and prevention systems
- Automated Compliance Tracking: Use software that continuously checks for policy adherence
- Encryption Technologies: Protect sensitive data across various technological platforms
Employee Training And Cultural Integration
Research from the Sans Institute reveals that human factors are often the most significant vulnerability in security implementations. Effective policy enforcement requires a comprehensive approach to employee education and cultural transformation.Successful training programs should focus on:
- Awareness Development: Help employees understand the rationale behind security policies
- Practical Skills Training: Provide concrete examples of policy implementation
- Continuous Learning: Create ongoing educational opportunities about emerging threats
- Simulated Scenarios: Use realistic cybersecurity exercises to test employee responses
Monitoring, Evaluation, And Continuous Improvement
Gartner research highlights the importance of treating security policy implementation as a dynamic, evolving process. Organizations must develop comprehensive monitoring and evaluation mechanisms that allow for continuous refinement of their security approach.
Key strategies for effective monitoring include:
- Regular security audits and vulnerability assessments
- Incident response and forensic analysis
- Periodic policy review and update processes
- Benchmarking against industry best practices
The National Institute of Standards and Technology recommends a risk-based approach to policy enforcement. This means creating flexible frameworks that can adapt to changing technological landscapes and emerging threat environments.
Consequence management is another crucial aspect of policy enforcement. Organizations must establish clear, consistent disciplinary procedures for policy violations while maintaining a supportive environment that encourages reporting and learning from potential security incidents.
Technology alone cannot guarantee security. The most effective implementations combine sophisticated technical controls with a strong organizational culture of security awareness. This holistic approach transforms security from a compliance requirement into a shared organizational value.
Ultimately, successful IT security policy implementation requires commitment from every level of the organization. From executive leadership to front-line employees, everyone plays a critical role in creating and maintaining a robust security ecosystem that can adapt to increasingly complex technological challenges.
Frequently Asked Questions
What is an IT security policy?
An IT security policy is a formal set of rules and guidelines that dictate how an organization protects its information assets. It outlines acceptable and unacceptable technology usage to prevent unauthorized access and security breaches.
Why are IT security policies important?
IT security policies are crucial because they establish clear guidelines for managing cybersecurity risks, protect sensitive information, and ensure compliance with legal and regulatory obligations. Organizations with regularly reviewed policies are significantly less likely to suffer major breaches.
What are the key components of effective IT security policies?
Effective IT security policies should include guidelines on user access management, data protection protocols, network security measures, incident response procedures, and technology usage standards. They should also emphasize the principles of Confidentiality, Integrity, and Availability (CIA triad).
How often should IT security policies be reviewed?
IT security policies should be viewed as living documents and should be reviewed regularly to adapt to evolving technologies and emerging threats. Continuous assessment and updates ensure that policies remain relevant and effective against potential cybersecurity risks.
Elevate Your IT Security Policies with Skypher's Automation!
Navigating the complexities of IT security policies can be overwhelming—especially when polices require regular updates to adapt to evolving technologies and emerging threats. Organizations often face the challenge of managing countless security questionnaires, which not only consume time but also divert critical resources from actual security measures.
Imagine streamlining this tedious process! With Skypher's AI Questionnaire Automation Tool, you can enhance your organization's cybersecurity posture while improving operational productivity. Our platform simplifies the completion of security reviews with advanced features like real-time collaboration, customizable Trust Centers, and seamless integration with over 40 third-party risk management platforms. By treating your security policies as living documents alongside our technology, you’re setting the stage for a proactive security culture.
!
Are you ready to transform how your organization handles security questionnaires? Start today with Skypher to experience increased efficiency, accuracy, and collaboration in your IT security processes. Visit us at https://skypher.co and revolutionize your approach to cybersecurity now!
