Third party risks in B2B software companies are growing faster than ever and putting operational integrity on the line. Hard to believe, but over 60 percent of organizations have experienced disruptions linked to third party vendors in the last year alone. Most teams think tightening up their own cybersecurity is enough, but ignoring the web of external dependencies can turn a minor oversight into a business-wide nightmare.
Table of Contents
- Understanding Third Party Risks In B2B Contexts
- Steps To Build A Third Party Risk Management Program
- Tools And Best Practices For Ongoing Risk Monitoring
- Collaborating Across Teams For Effective Risk Management
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understand third party risks comprehensively | Recognize that third party risks can disrupt operations and data security across many dimensions. |
| Establish a risk management governance framework | Create a dedicated committee overseeing the development and implementation of risk assessment strategies. |
| Conduct thorough vendor assessments | Implement a detailed evaluation process covering background checks, compliance, and financial stability. |
| Prioritize continuous risk monitoring | Develop adaptive systems for real-time updates and ongoing risk evaluations to manage emerging threats. |
| Encourage cross-department collaboration | Foster teamwork and communication across various departments for a unified approach to manage risks effectively. |
Understanding Third Party Risks in B2B Contexts
Third party risks represent a critical challenge for B2B software companies navigating complex technology ecosystems. These risks emerge from dependencies on external vendors, partners, and service providers that can potentially compromise an organization's security, operational integrity, and strategic objectives.
The Anatomy of Third Party Risk Landscapes
In modern B2B software environments, third party risks are multifaceted and increasingly sophisticated. Research from NIST Special Publication reveals that organizations face intricate challenges when managing external technological relationships. These risks are not merely theoretical concerns but tangible threats that can disrupt business operations, compromise sensitive data, and erode stakeholder trust.
Typically, third party risks manifest through several critical dimensions:
To help clarify the different dimensions of third party risks facing B2B software companies, the following table summarizes the main risk types described and their potential impacts:
| Risk Dimension | Description | Potential Impact |
|---|---|---|
| Data Security Vulnerabilities | External partners may introduce breach points in networks | Data loss, security breaches |
| Compliance Inconsistencies | Misaligned regulatory standards with vendors | Fines, legal liabilities |
| Operational Dependency Risks | Reliance on third party services as single points of failure | Service disruption, lost revenue |
- Data Security Vulnerabilities: External partners may introduce potential breach points in organizational networks
- Compliance Inconsistencies: Misaligned regulatory standards between organizations can create significant operational risks
- Operational Dependency Risks: Reliance on third party services can create potential single points of failure
Strategic Risk Assessment Frameworks
According to research from the National Institutes of Health, effective third party risk management requires comprehensive assessment strategies. Organizations must develop robust frameworks that systematically evaluate potential vendor risks before establishing technological partnerships.
Successful risk assessment involves multiple critical evaluation dimensions:
- Comprehensive vendor background checks
- Detailed security infrastructure analysis
- Ongoing performance and compliance monitoring
- Clear contractual risk allocation mechanisms
The complexity of managing third party risks demands a proactive, holistic approach. B2B software companies cannot afford reactive risk management strategies. Instead, they must implement dynamic, intelligent systems that continuously assess and mitigate potential vulnerabilities across their entire technological ecosystem.
Understanding and managing third party risks is not about eliminating all potential threats but creating resilient, adaptive risk management protocols that protect organizational interests while maintaining operational flexibility. By developing sophisticated risk assessment methodologies, B2B software companies can transform potential vulnerabilities into strategic opportunities for enhanced security and technological collaboration.
Steps to Build a Third Party Risk Management Program
Building a robust third party risk management program requires strategic planning, comprehensive assessment, and continuous monitoring. For B2B software companies, this process demands a systematic approach that addresses the complex interconnections between organizational security and external vendor relationships.
Establishing Foundational Risk Management Infrastructure
According to TechTarget, developing an effective third party risk management program begins with establishing a dedicated governance framework. This involves creating a cross-functional risk management committee responsible for defining, implementing, and overseeing risk assessment strategies.
Key components of this foundational infrastructure include:
- Clear Governance Structures: Defining roles, responsibilities, and accountability mechanisms
- Comprehensive Policy Development: Creating detailed guidelines for vendor risk assessment
- Risk Categorization Protocols: Developing systematic methods for classifying vendor risks
Comprehensive Vendor Assessment and Validation
Research from Moss Adams highlights the critical importance of rigorous vendor assessment processes. Organizations must implement a multi-dimensional evaluation approach that goes beyond surface-level compliance checks.
Effective vendor assessment strategies should encompass:
- Detailed background investigations
- Security infrastructure analysis
- Compliance verification
- Financial stability assessment
- Performance historical review

Continuous Monitoring and Adaptive Risk Management
IANS Research emphasizes that third party risk management is not a one-time activity but an ongoing process. Organizations must develop adaptive mechanisms that allow for continuous monitoring and rapid response to emerging risks.
Key elements of continuous monitoring include:
- Regular risk reassessments
- Real-time threat intelligence tracking
- Dynamic risk scoring mechanisms
- Automated compliance validation tools
Successful third party risk management requires a holistic, proactive approach. By implementing comprehensive assessment frameworks, maintaining rigorous governance structures, and developing adaptive monitoring systems, B2B software companies can effectively mitigate potential vulnerabilities while maintaining strategic technological partnerships.
Tools and Best Practices for Ongoing Risk Monitoring
Ongoing risk monitoring represents a critical defense mechanism for B2B software companies seeking to maintain robust third party risk management strategies. The dynamic nature of technological ecosystems demands sophisticated, adaptive approaches that can anticipate and mitigate potential vulnerabilities in real time.
Advanced Risk Monitoring Technologies
According to a 2024 blockchain research study, emerging technologies are revolutionizing how organizations track and assess third party risks. Innovative frameworks now integrate smart contract technologies and real-time monitoring systems that provide unprecedented transparency and immediate risk detection.
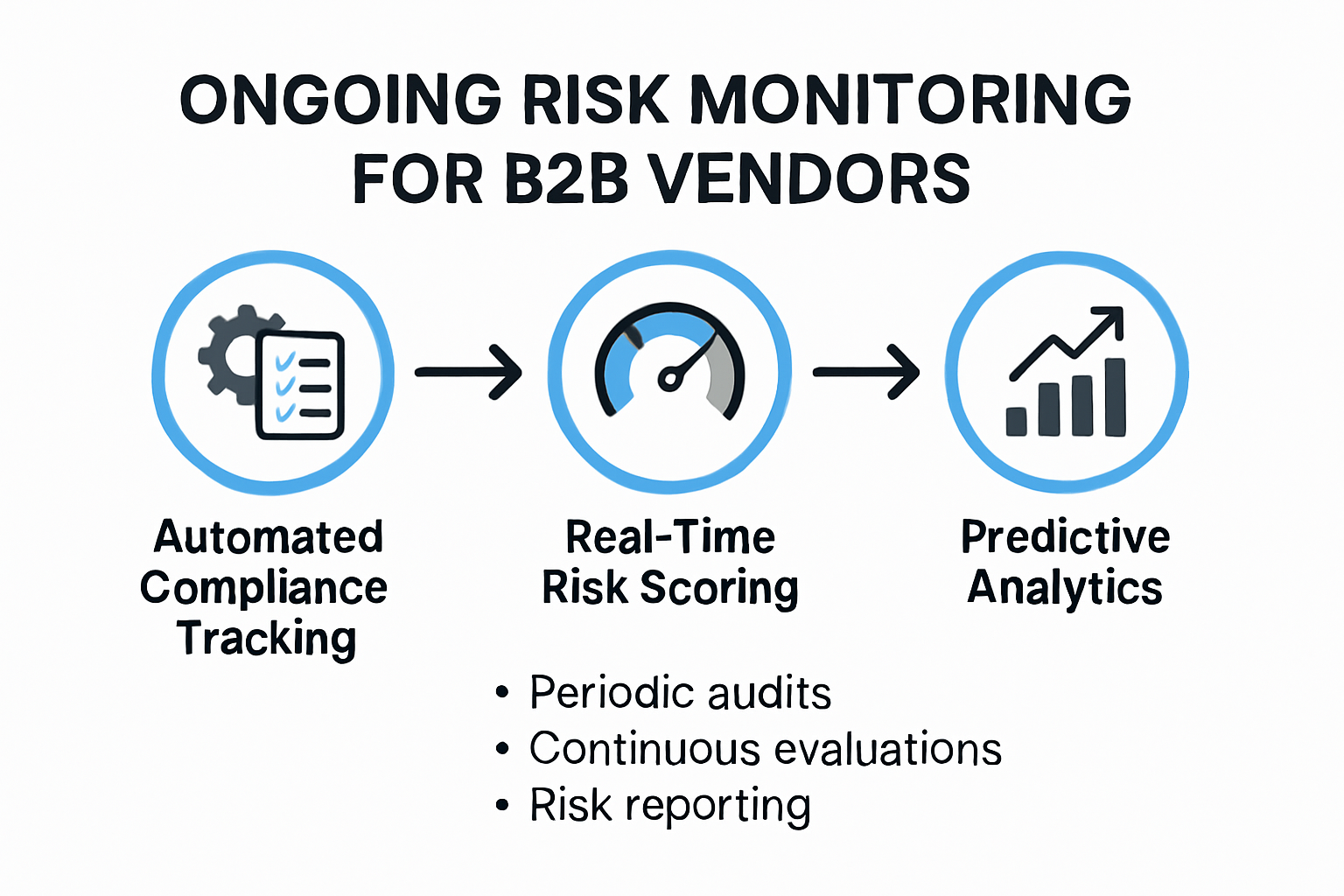
Key technological capabilities for effective risk monitoring include:
- Automated Compliance Tracking: Systems that continuously validate vendor adherence to security standards
- Real-Time Risk Scoring: Dynamic algorithms that assess and update vendor risk profiles instantly
- Predictive Analytics: Machine learning models that forecast potential risk scenarios
Comprehensive Vendor Assessment Frameworks
Research from Cherry Bekaert emphasizes the importance of establishing comprehensive vendor assessment protocols. Organizations must develop structured approaches that go beyond periodic reviews and create continuous, proactive monitoring mechanisms.
Effective assessment frameworks should include:
- Periodic security audits
- Continuous information requests
- Detailed performance evaluations
- Regular compliance verification processes
Strategic Monitoring and Reporting Mechanisms
Successful risk monitoring requires more than technological tools. Organizations must develop strategic reporting mechanisms that transform raw data into actionable insights. This involves creating clear communication channels, establishing escalation protocols, and ensuring cross-functional visibility into potential risks.
To enhance your understanding of security questionnaire management, learn more about navigating complex assessment processes.
Critical elements of strategic monitoring include:
- Transparent reporting dashboards
- Clear risk threshold definitions
- Rapid incident response protocols
- Regular executive-level risk reviews
By implementing sophisticated monitoring technologies, developing comprehensive assessment frameworks, and creating strategic reporting mechanisms, B2B software companies can transform third party risk management from a reactive defense into a proactive strategic advantage. The goal is not just to identify risks but to create an adaptive ecosystem that continuously evolves and improves organizational resilience.
Collaborating Across Teams for Effective Risk Management
Effective third party risk management transcends traditional departmental boundaries, requiring a holistic, integrated approach that leverages collective organizational expertise. Successful collaboration becomes the cornerstone of robust risk mitigation strategies in modern B2B software environments.
Breaking Down Organizational Silos
According to the World Economic Forum, third party risk management cannot be confined to isolated IT or security teams. Instead, it demands a comprehensive, cross-functional strategy where multiple departments actively participate in identifying, assessing, and mitigating potential risks.
Key strategies for breaking down organizational silos include:
- Collaborative Risk Assessment Workshops: Regular meetings that bring together representatives from different departments
- Shared Risk Management Dashboards: Transparent platforms enabling real-time information sharing
- Integrated Communication Protocols: Establishing clear channels for risk communication across teams
Defining Clear Roles and Responsibilities
Research from the Enterprise Risk Management Initiative emphasizes the importance of formally defining roles and responsibilities in third party risk management. Each team must understand its specific contribution to the overall risk management ecosystem.
Essential collaborative responsibilities include:
The following table organizes the essential responsibilities of different teams involved in third party risk management, giving a clear overview of who leads each critical function:
| Team | Core Responsibility |
|---|---|
| Legal | Contractual risk assessment |
| IT Security | Technical vulnerability evaluation |
| Finance | Vendor financial stability analysis |
| Procurement | Vendor selection and screening |
| Compliance | Regulatory standard verification |
- Legal team: Contractual risk assessment
- IT security: Technical vulnerability evaluation
- Finance: Vendor financial stability analysis
- Procurement: Vendor selection and initial screening
- Compliance: Regulatory standard verification
Implementing Integrated Risk Communication Frameworks
Successful cross-team collaboration requires more than periodic meetings. Organizations must develop sophisticated communication frameworks that enable seamless information exchange and collective decision-making.
Discover how to streamline your security assessment processes to enhance interdepartmental collaboration and risk management efficiency.
Critical elements of an integrated risk communication framework include:
- Standardized risk reporting templates
- Automated escalation mechanisms
- Regular cross-functional risk review sessions
- Continuous learning and improvement protocols
By fostering a culture of collaboration, transparency, and shared responsibility, B2B software companies can transform third party risk management from a potential organizational challenge into a strategic competitive advantage. The goal is to create an adaptive, responsive ecosystem where risk management becomes a collective organizational capability rather than a siloed function.
Frequently Asked Questions
What are third party risks in B2B software companies?
Third party risks refer to potential threats that arise from dependencies on external vendors, partners, and service providers that can impact security, operational integrity, or strategic objectives.
How can B2B software companies assess third party risks?
Companies can assess third party risks through comprehensive vendor background checks, security infrastructure analysis, ongoing compliance monitoring, and clear risk allocation in contracts.
What are the key components of a third party risk management program?
A robust third party risk management program should include establishing a risk management governance framework, conducting thorough vendor assessments, and implementing continuous monitoring and adaptive risk management strategies.
Why is continuous monitoring essential in third party risk management?
Continuous monitoring is critical as it allows organizations to rapidly detect and respond to emerging risks, ensuring ongoing compliance and security in a constantly changing technological landscape.
Tired of Third Party Risk Slowing Your B2B Growth?
Managing third party risk can feel overwhelming when every vendor questionnaire, security audit, and compliance review slows down your operations and puts sensitive deals on hold. As highlighted in this article, gaps in your third party risk management not only expose you to data breaches and compliance penalties. They also directly threaten your sales cycles and customer trust. If your teams are still tackling tedious questionnaires and chasing manual responses, you are at risk of missing critical warnings and losing valuable time.

Take control today by switching to technology that automates your third party reviews and accelerates risk communications. Discover how Skypher can help your growth-focused teams handle security questionnaires seamlessly, collaborate in real time, and keep vendor assessments moving with AI-powered speed. Get started now to prevent vulnerabilities from holding you back. Visit Skypher's homepage or learn more about security questionnaire automation and set your business on the path to stronger, faster risk management.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- The ever growing number of security questionnaires and what you and your company can do to face it
- The Case for Security Questionnaire Automation
- Increasing company efficiency: boosting collaboration with widespread adoption
- Contract Review for Small Business: Essential Guide 2025 - Loft Legal
- 5 Ways to Secure Your Small Business and Prevent Data Breach-Bista
