PCI compliance attestation is climbing to the top of every B2B company's priority list for 2025. Businesses processing card payments now face over 64% of organizations struggling with documentation and encryption updates, exposing major risks. Most assume passing the annual checkbox is enough, but the real punchline is this. In 2025, PCI will demand continuous vigilance where compliance means not just ticking boxes but building security resilience that sets you apart from the crowd.
Table of Contents
- Understanding PCI Compliance Attestation Requirements
- Steps To Achieve Attestation For B2B Software
- Key Benefits For Sales, Risk, And Compliance Leaders
- Common Challenges And Expert Tips For 2025
Quick Summary
| Takeaway | Explanation |
|---|---|
| Achieve PCI Compliance Early | Begin the compliance attestation process to identify gaps in your security infrastructure promptly. |
| Implement Strong Security Controls | Utilize firewalls, data encryption, and access management to protect payment card information. |
| Conduct Regular Security Assessments | Continuous monitoring and annual recertification are vital for maintaining compliance and addressing vulnerabilities. |
| Focus on Training and Awareness | Provide immersive and scenario-based training to enhance incident response capabilities among team members. |
| Leverage Compliance for Competitive Advantage | Use compliance attestation to build trust and differentiate your company in the marketplace with potential clients. |
Understanding PCI Compliance Attestation Requirements
PCI compliance attestation represents a critical security framework for B2B companies handling payment card data. At its core, this process involves demonstrating an organization's adherence to the Payment Card Industry Data Security Standard (PCI DSS), a comprehensive set of security requirements designed to protect sensitive financial information.
The Fundamental Components of PCI Compliance
PCI compliance attestation is not just a checkbox exercise but a robust validation of an organization's security infrastructure. The PCI Security Standards Council defines a multilayered approach that requires businesses to implement stringent data protection mechanisms. Companies must establish comprehensive security controls that encompass network architecture, data encryption, access management, and continuous monitoring.
According to Stanford University's IT security guidelines, organizations processing payment card information must develop a holistic strategy that addresses several key domains. These include:
- Network Security: Implementing robust firewall configurations and network segmentation
- Data Protection: Encrypting cardholder data during transmission and storage
- Vulnerability Management: Regularly updating and patching systems to address potential security weaknesses
- Access Control: Establishing strict user authentication and authorization protocols
To help clarify the core elements of PCI compliance, the following table summarizes the key security domains and their primary focus areas essential for B2B companies.
| PCI Compliance Component | Primary Focus |
|---|---|
| Network Security | Firewall configuration, network segmentation |
| Data Protection | Cardholder data encryption during transit/storage |
| Vulnerability Management | System patching and addressing security weaknesses |
| Access Control | User authentication, authorization protocols |
Attestation and Validation Processes
The PCI compliance attestation process involves a detailed examination of an organization's security practices. Companies must complete a self-assessment questionnaire (SAQ) or undergo an external audit conducted by a Qualified Security Assessor (QSA), depending on their transaction volume and specific payment processing environment.
Amazon Web Services highlights that cloud service providers are increasingly expanding their compliance offerings to help businesses more effectively meet these rigorous standards. This evolution reflects the growing complexity of maintaining secure payment ecosystems in an increasingly digital business environment.
The attestation process requires organizations to demonstrate not just technical controls but also organizational commitment to maintaining a robust security posture. This means developing comprehensive policies, conducting regular staff training, and maintaining detailed documentation of security practices and incident response procedures.
For B2B companies, achieving and maintaining PCI compliance is not merely a regulatory requirement but a critical trust signal for potential clients and partners. It demonstrates a proactive approach to data protection and signals an organization's commitment to maintaining the highest standards of security and professionalism in handling sensitive financial information.
Steps to Achieve Attestation for B2B Software
Achieving PCI compliance attestation requires a strategic and systematic approach for B2B software companies. The process demands meticulous planning, comprehensive security implementation, and ongoing commitment to maintaining rigorous data protection standards.
Initial Assessment and Gap Analysis
The first critical step in achieving PCI compliance attestation involves conducting a thorough initial assessment of your current security infrastructure. The PCI Security Standards Council recommends a comprehensive gap analysis that identifies potential vulnerabilities and areas requiring immediate attention.
Key components of this initial assessment include:
- Infrastructure Review: Mapping out all systems that handle payment card data
- Security Control Evaluation: Analyzing existing security mechanisms
- Compliance Documentation: Gathering and organizing current security policies and procedures
Companies must create a detailed inventory of all payment card data touch points, understanding exactly how cardholder information flows through their systems. This involves documenting every system, network, and application that interacts with sensitive financial data.
Implementing Comprehensive Security Measures
Wikipedia's overview of PCI DSS highlights the multifaceted nature of compliance requirements. B2B software companies must implement a robust set of security controls that address various critical areas:
- Build and maintain a secure network infrastructure
- Protect cardholder data through advanced encryption techniques
- Develop strong access control mechanisms
- Implement continuous monitoring and vulnerability management systems
- Create and maintain comprehensive security policies
This stage requires significant technical expertise. Companies often need to redesign network architectures, implement advanced encryption protocols, and establish stringent access management systems. The goal is not just to meet minimum requirements but to create a truly resilient security environment.
Validation and Ongoing Compliance
The final step involves formal validation of your security measures. This typically requires completing a Self-Assessment Questionnaire (SAQ) or undergoing an external audit by a Qualified Security Assessor (QSA). B2B software companies must prepare extensive documentation demonstrating their compliance with PCI DSS requirements.
Ongoing compliance is equally critical. This means:
- Regular security assessments
- Continuous monitoring of systems
- Annual recertification processes
- Immediate response to any identified vulnerabilities
Successful PCI compliance attestation is not a one-time achievement but a continuous journey of security improvement. B2B software companies must develop a culture of security that goes beyond checklist compliance, treating data protection as a fundamental business priority.
The process demands significant investment in time, resources, and technical expertise. However, the benefits extend far beyond mere regulatory compliance. Companies that successfully navigate this process demonstrate their commitment to protecting client data, ultimately building trust and competitive advantage in an increasingly security-conscious market.
For organizations preparing for PCI compliance attestation in 2025, this step-by-step table outlines the essential phases, main activities, and goals of the process as discussed above.
| Step | Main Activities | Goal |
|---|---|---|
| Initial Assessment & Gap Analysis | Assess security, map data, review policies | Identify vulnerabilities/gaps |
| Implement Security Measures | Secure network, encrypt data, define access controls | Establish robust protections |
| Validation & Ongoing Compliance | SAQ/audit, monitor systems, recertify, fix vulnerabilities | Ensure & maintain compliance status |
Key Benefits for Sales, Risk, and Compliance Leaders
PCI compliance attestation delivers substantial strategic advantages for B2B organizations, extending far beyond basic regulatory requirements. Leaders across sales, risk management, and compliance departments can leverage this process to transform their organizational security posture and business opportunities.
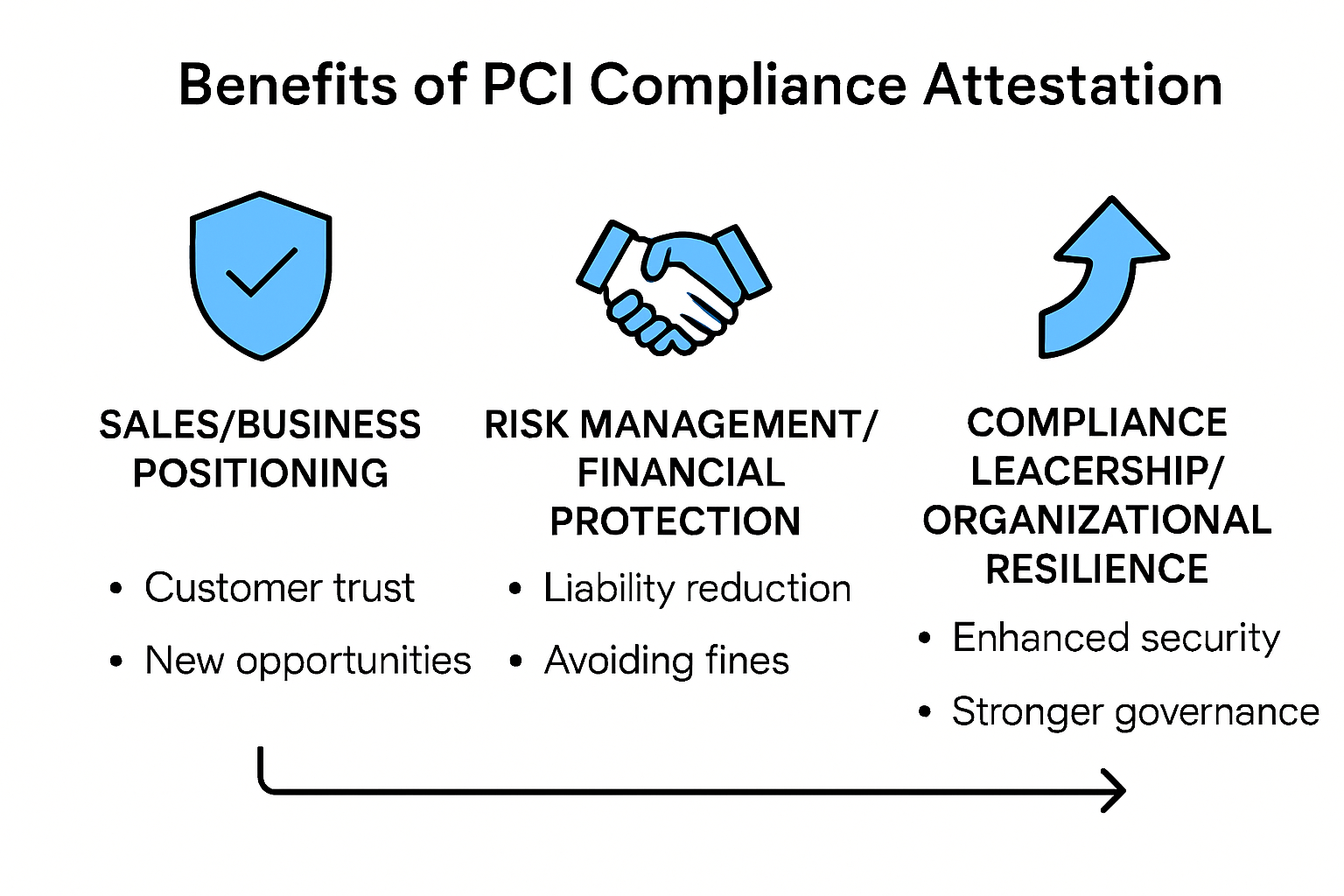
Strategic Business Positioning
Investopedia highlights that PCI compliance significantly enhances brand reputation and client trust. For sales leaders, this translates into a powerful competitive differentiator. Companies demonstrating robust security practices can more effectively attract enterprise clients who prioritize data protection.
Key business positioning benefits include:
- Competitive Advantage: Establishing credibility in security-conscious markets
- Client Confidence: Signaling commitment to data protection
- Risk Mitigation: Reducing potential security-related business obstacles
Sales teams can strategically use PCI compliance as a trust-building mechanism. When engaging with potential clients, the ability to showcase comprehensive security protocols becomes a significant selling point. Learn more about strategic security communication.
Risk Management and Financial Protection
SafetyCulture's research underscores that PCI compliance is crucial for protecting organizations against substantial financial and legal risks. Risk management professionals gain multiple protective advantages through a comprehensive compliance strategy.
Risk mitigation benefits encompass:
- Preventing potential data breach expenses
- Avoiding significant regulatory penalties
- Establishing clear security governance frameworks
- Reducing potential litigation risks
By proactively addressing security vulnerabilities, organizations can potentially save millions in potential breach-related costs. ZenGRC emphasizes that comprehensive compliance strategies improve operational efficiency while protecting critical business assets.
Compliance Leadership and Organizational Resilience
Compliance leaders play a pivotal role in transforming PCI attestation from a mandatory requirement into a strategic organizational capability. The process demands more than technical implementation it requires developing a robust security culture that permeates every business function.
Key compliance leadership strategies include:
- Developing comprehensive security training programs
- Creating cross-functional security awareness
- Establishing continuous improvement mechanisms
- Building adaptive security frameworks
Successful PCI compliance attestation represents more than a checkbox exercise. It demonstrates an organization's commitment to maintaining the highest standards of data protection, ultimately building trust with clients, partners, and stakeholders.
For modern B2B companies, PCI compliance is not just about meeting regulatory requirements. It is a strategic approach to building organizational resilience, protecting sensitive information, and creating a competitive advantage in an increasingly complex digital business environment.
Common Challenges and Expert Tips for 2025
As B2B companies approach the 2025 PCI compliance landscape, organizations face increasingly complex security challenges that demand sophisticated and adaptive strategies. Understanding these hurdles and implementing expert-recommended solutions will be critical for maintaining robust data protection frameworks.
Documentation and Encryption Complexity
Protegrity's research reveals that 64% of organizations struggle with documentation and encryption updates, highlighting a significant preparedness gap for the upcoming compliance requirements. Companies must develop systematic approaches to manage these intricate technical requirements.
Key documentation and encryption challenges include:

- Comprehensive Record Keeping: Maintaining detailed and current security documentation
- Encryption Standards: Implementing advanced encryption protocols
- Technical Complexity: Navigating evolving security technologies
- Continuous Update Management: Keeping pace with rapid technological changes
Experts recommend establishing dedicated compliance teams that can continuously monitor and update security documentation. This approach ensures organizations remain agile and responsive to emerging regulatory requirements. Learn more about strategic security documentation.
Multi-Factor Authentication and Risk Management
Tevora's PCI Compliance Checklist emphasizes the critical importance of risk-based flexibility and expanded multi-factor authentication requirements. Organizations must develop more sophisticated access control mechanisms that go beyond traditional password-based security.
Recommended strategies for enhanced authentication include:
- Implementing adaptive multi-factor authentication
- Creating context-aware access controls
- Developing granular user permission frameworks
- Integrating advanced behavioral analysis techniques
By adopting a proactive approach to authentication, companies can significantly reduce unauthorized access risks and demonstrate robust security governance.
Training and Incident Response Preparedness
SISA highlights simulation-based training as a cutting-edge methodology for PCI compliance in 2025. Organizations must move beyond traditional compliance training to immersive, scenario-driven learning experiences that prepare teams to handle complex security incidents.
Key training focus areas include:
- Realistic cybersecurity simulation scenarios
- Incident response strategy development
- Cross-functional security awareness programs
- Continuous learning and skill updates
Effective training transforms compliance from a theoretical exercise into a practical, organization-wide capability. By creating a culture of security awareness, companies can turn potential vulnerabilities into strategic strengths.
The 2025 PCI compliance landscape demands more than technical adherence. It requires a holistic approach that integrates advanced technology, comprehensive documentation, sophisticated training, and a proactive security mindset. B2B companies that view compliance as a strategic opportunity rather than a regulatory burden will be best positioned to protect their assets and build trust with clients and partners.
Frequently Asked Questions
What is PCI compliance attestation?
PCI compliance attestation is the process by which organizations demonstrate adherence to the Payment Card Industry Data Security Standard (PCI DSS), which establishes security requirements for businesses that handle payment card data.
Why is PCI compliance important for B2B companies in 2025?
In 2025, PCI compliance is crucial for B2B companies as it ensures robust protection of sensitive financial information, helps build trust with clients, and mitigates risks associated with data breaches and regulatory penalties.
What steps should B2B companies take to achieve PCI compliance attestation?
B2B companies should conduct an initial assessment and gap analysis of their security infrastructure, implement comprehensive security measures, and engage in ongoing compliance validation through regular security assessments and audits.
What are the benefits of achieving PCI compliance attestation for B2B businesses?
Achieving PCI compliance attestation offers several benefits, including enhanced brand reputation, increased client confidence, improved risk management, and a competitive advantage in the marketplace.
Turn PCI Compliance Complexity Into Competitive Strength
Are you overwhelmed by the constant pressure to document, update, and validate your PCI security controls? The article highlights how preparing for PCI compliance attestation in 2025 requires more than annual checklists. B2B teams often struggle with documentation overload, time-consuming security questionnaires, and the need for airtight responses to client RFPs or audits. Gaps in collaboration, proof accuracy, and timely updates can hold back both your compliance and sales cycles.

Stop letting manual processes and outdated documentation put your business at risk. Meet the new standard for secure, efficient review with Skypher's AI-driven Questionnaire Automation Tool, built for organizations needing real-time collaboration, advanced integrations, and swift, accurate answers to any security questionnaire. Your next compliance review does not have to be a roadblock. Transform tedious, stressful attestation work into a strategic advantage. Visit https://skypher.co today and see how you can reduce delays, boost client trust, and handle PCI requirements with confidence.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- The ever growing number of security questionnaires and what you and your company can do to face it
- Increasing company efficiency: boosting collaboration with widespread adoption
- The Case for Security Questionnaire Automation
- Steps to comply CCPA compliance by Bista Solutions
- Data Privacy Best Practices for Small Businesses in 2025 - Loft Legal
