Compliance is more complex than ever for American CISOs tasked with protecting both health and payment card data. With over 90 percent of large organizations processing sensitive records subject to HIPAA and PCI DSS standards, missing a single requirement can trigger costly audits or legal fallout. This article clarifies key differences in regulatory frameworks and explores practical automation strategies that help American tech firms avoid common pitfalls while streamlining security questionnaire responses.
Table of Contents
- Defining PCI And HIPAA Compliance Standards
- Key Differences And Overlapping Requirements
- Essential 2026 Updates For PCI And HIPAA
- Common Compliance Pitfalls And How To Avoid Them
- Automation Strategies For Streamlined Compliance
Key Takeaways
| Point | Details |
|---|---|
| Understanding HIPAA and PCI DSS | HIPAA focuses on healthcare data protection, while PCI DSS is concerned with securing payment card transactions. Both require robust security protocols to safeguard sensitive information. |
| 2026 Regulatory Updates | Significant updates to both HIPAA and PCI DSS are expected in 2026, emphasizing stricter cybersecurity measures and specialized data protections. Organizations must prepare proactively. |
| Common Compliance Risks | Organizations often encounter pitfalls in vendor management and data handling, highlighting the need for comprehensive training and rigorous security assessments. |
| Leveraging Automation | Implementing automated solutions can streamline compliance efforts for HIPAA and PCI DSS, allowing for continuous monitoring and reducing manual errors. |
Defining PCI and HIPAA Compliance Standards
In the complex world of data protection, HIPAA and PCI DSS represent two critical regulatory frameworks designed to safeguard sensitive information across healthcare and financial sectors. These standards establish mandatory security protocols that organizations must implement to protect patient health records and payment card data from unauthorized access or breaches.
The Health Insurance Portability and Accountability Act (HIPAA) is a federal law that establishes federal standards for health information protection. It primarily applies to healthcare providers, health plans, and healthcare clearinghouses, mandating strict guidelines for handling electronic protected health information (ePHI). The law encompasses three key rules: the Privacy Rule, the Security Rule, and the Breach Notification Rule, each addressing different aspects of patient data protection.
Conversely, the Payment Card Industry Data Security Standard (PCI DSS) is a private contractual standard focused on securing payment card transactions. Unlike HIPAA, which is government-mandated, PCI DSS is a set of security requirements established by major credit card companies to prevent cardholder data breaches. Organizations processing, storing, or transmitting payment card information must comply with these technical and operational standards to minimize financial fraud risks.
Pro tip: Conduct annual comprehensive audits of your compliance frameworks, ensuring that your security controls meet both HIPAA and PCI DSS requirements across all digital and physical touchpoints.
Key Differences and Overlapping Requirements
While HIPAA and PCI DSS are both designed to protect sensitive information, they differ significantly in scope, application, and regulatory frameworks. Compliance requirements vary across these standards, creating unique challenges for organizations navigating both regulatory environments.
The primary distinction lies in their focus and enforcement mechanisms. HIPAA is a federal law exclusively governing healthcare information privacy in the United States, mandating comprehensive protections for patient data across administrative, physical, and technical domains. Its scope encompasses healthcare providers, health plans, and medical clearinghouses, with strict penalties for non-compliance. In contrast, PCI DSS is a global, privately established standard primarily focused on payment card security, applicable to any organization processing credit card transactions, regardless of industry or geographic location.
The following table compares the primary focus and enforcement of HIPAA and PCI DSS:
| Standard | Primary Sector | Enforcement Type | Key Protected Data |
|---|---|---|---|
| HIPAA | Healthcare providers | Federal law | Patient health records (ePHI) |
| PCI DSS | All organizations | Private contract | Payment cardholder data |
Despite their differences, both frameworks share critical security objectives. They require organizations to implement robust access controls, encrypt sensitive data, conduct regular risk assessments, and maintain comprehensive documentation of security practices. Both standards demand multi-layered security approaches that protect against unauthorized data access, breaches, and potential financial or reputational damages. Organizations operating in healthcare or financial sectors must often simultaneously comply with both standards, necessitating a sophisticated, integrated approach to data protection.
Pro tip: Develop a unified compliance strategy that addresses both HIPAA and PCI DSS requirements simultaneously, leveraging overlapping security controls to streamline your compliance efforts and reduce implementation complexity.
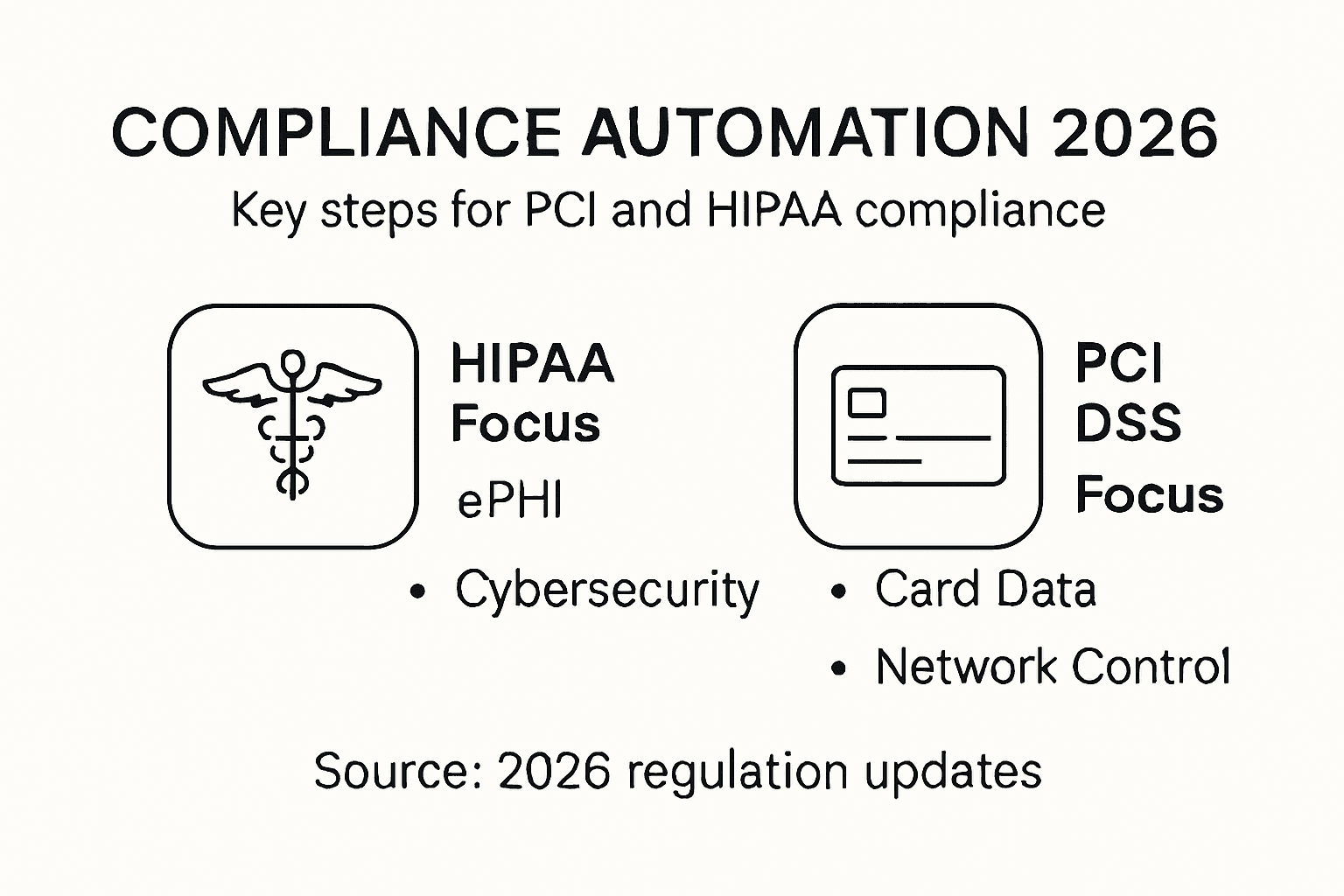
Essential 2026 Updates for PCI and HIPAA
The healthcare and financial sectors are preparing for significant regulatory changes in 2026, with substantial HIPAA security rule modifications poised to reshape compliance landscapes. The Department of Health and Human Services (HHS) is implementing comprehensive cybersecurity updates that will demand unprecedented levels of organizational preparedness and technological sophistication.
For HIPAA, the most critical updates center on prescriptive cybersecurity requirements. Organizations will now be mandated to implement multi-factor authentication, encrypt data both at rest and in transit, conduct regular penetration testing, and perform continuous risk assessments. These changes represent a fundamental shift from previous risk-based approaches to more stringent, defined security protocols. Notably, the updates will introduce enhanced protections for sensitive health information, particularly surrounding reproductive health and substance use disorder data, reflecting evolving privacy considerations.
PCI DSS is also expected to evolve, with anticipated updates focusing on emerging technological threats and more robust payment card security mechanisms. While specific 2026 PCI DSS modifications are still being finalized, organizations can expect increased emphasis on advanced encryption technologies, more sophisticated access controls, and enhanced monitoring systems. The convergence of these regulatory updates underscores the growing complexity of data protection in an increasingly interconnected digital ecosystem.
Here's a summary of the major 2026 updates for HIPAA and PCI DSS:
| Update Area | HIPAA (2026) | PCI DSS (2026) | Business Impact |
|---|---|---|---|
| Authentication | Mandatory multi-factor authentication | Enhanced access controls | Stronger user verification |
| Encryption | Data at rest and in transit required | Advanced encryption technologies | Improved data confidentiality |
| Risk Assessment | Continuous monitoring | Increased monitoring systems | Ongoing threat identification |
| Specialized Protections | Focus on reproductive health and substance use data | Broadened threat coverage | Higher compliance complexity |
Pro tip: Proactively conduct a comprehensive gap analysis against the 2026 HIPAA and PCI DSS requirements, identifying potential compliance vulnerabilities at least six months before official implementation.
Common Compliance Pitfalls and How to Avoid Them
Navigating the complex landscape of HIPAA and PCI DSS compliance requires a proactive approach to identifying and mitigating potential vulnerabilities. Common HIPAA compliance pitfalls reveal critical areas where organizations frequently stumble, creating significant legal and financial risks.
One of the most prevalent compliance challenges involves vendor management and data handling. Organizations often fail to establish comprehensive Business Associate Agreements (BAAs), neglect proper encryption practices, and overlook critical breach reporting timelines. Staff-related errors compound these risks, with common mistakes including misaddressed emails, shared login credentials, and inadequate access controls. These seemingly minor oversights can result in substantial penalties and compromise sensitive electronic protected health information (ePHI).
Preventing compliance violations demands a multifaceted strategy. Robust workforce training programs, rigorous vendor management protocols, and continuous security assessments are essential. Organizations must implement systematic risk analysis processes, regularly update security policies, and develop clear, enforceable guidelines for handling sensitive data. This includes creating detailed incident response plans, conducting periodic security audits, and maintaining comprehensive documentation that demonstrates ongoing compliance efforts.
Pro tip: Implement a quarterly compliance review process that includes automated vulnerability scanning, staff training updates, and comprehensive documentation audits to proactively identify and address potential compliance gaps.
Automation Strategies for Streamlined Compliance
In the rapidly evolving landscape of regulatory compliance, organizations must leverage advanced technological solutions to streamline GRC audit processes effectively. Automation has emerged as a critical strategy for managing the complex requirements of HIPAA and PCI DSS compliance, enabling businesses to reduce manual errors, improve efficiency, and maintain continuous regulatory alignment.
The core of effective compliance automation lies in implementing intelligent systems that can continuously monitor, assess, and document regulatory requirements. Advanced AI-powered platforms can automatically track changes in compliance standards, flag potential vulnerabilities, and generate comprehensive reports that demonstrate ongoing adherence. These technologies enable real-time risk assessment, allowing organizations to proactively identify and address potential compliance gaps before they escalate into significant issues.
Successful compliance automation requires a holistic approach that integrates multiple technological components. This includes implementing robust security information and event management (SIEM) systems, automated documentation tools, continuous monitoring platforms, and intelligent risk assessment algorithms. Organizations should focus on creating interconnected systems that can seamlessly collect, analyze, and report compliance-related data across different regulatory frameworks, reducing the administrative burden and minimizing the potential for human error.
Pro tip: Develop a centralized compliance automation dashboard that integrates multiple regulatory standards, providing a comprehensive view of your organization's compliance status and enabling rapid response to potential vulnerabilities.
Simplify PCI and HIPAA Compliance with Skypher's AI-Powered Automation
The challenges of meeting complex 2026 HIPAA and PCI DSS requirements demand more than manual checklists and fragmented processes. As this article highlights, staying ahead means implementing continuous monitoring, enforcing multi-factor authentication, and conducting comprehensive risk assessments — tasks that can quickly overwhelm traditional compliance teams. Skypher offers an AI Questionnaire Automation Tool specifically designed to help medium to large organizations in tech and finance streamline their security questionnaire responses. This minimizes costly mistakes, reduces response times dramatically, and ensures higher accuracy across evolving regulatory frameworks.

Unlock efficiency and gain a competitive edge by automating your compliance workflows with Skypher. Benefit from real-time collaboration, seamless integrations with over 40 third-party risk management platforms, and a customizable Trust Center to centralize your compliance efforts. Don’t wait until the new regulations take effect. Visit Skypher now to transform how your team handles PCI and HIPAA compliance for 2026 and beyond. Learn more about our AI Questionnaire Automation Tool and how our platform drives faster, more reliable security reviews.
Frequently Asked Questions
What are the key differences between HIPAA and PCI DSS compliance?
HIPAA focuses on protecting electronic protected health information (ePHI) in the healthcare sector, whereas PCI DSS is designed to secure payment card data across all industries. HIPAA is a federal law, while PCI DSS is a private standard established by credit card companies.
What are the essential updates to HIPAA and PCI DSS compliance expected in 2026?
In 2026, HIPAA will introduce mandatory multi-factor authentication, data encryption, continuous risk assessments, and enhanced protections for sensitive health data. PCI DSS is expected to focus on advanced encryption technologies and improved access controls.
How can organizations avoid common compliance pitfalls for HIPAA and PCI DSS?
Organizations can avoid compliance pitfalls by establishing robust vendor management practices, implementing comprehensive staff training, and developing clear incident response plans. Regular security assessments and a quarterly compliance review process can help identify vulnerabilities.
What role does automation play in achieving compliance with HIPAA and PCI DSS?
Automation helps organizations streamline compliance processes by continuously monitoring regulatory requirements, tracking changes, and generating reports. Utilizing intelligent systems for risk assessment and documentation can reduce manual errors and enhance overall compliance efficiency.