B2B software decisions can shape the future of your entire company. Some RFP processes fail to uncover a vendor’s true strengths or weaknesses and end up costing big. But companies that use strategic RFP questions see up to 50 percent higher satisfaction with their chosen software partners. Most decision-makers just ask standard questions and hope for the best. The smartest ones use targeted, probing questions to spot red flags before it is too late.
Table of Contents
- Essential Rfp Questions For B2b Software
- Security And Compliance Rfp Questions For Ciso Teams
- Evaluating Vendor Responses: Best Practices
- Customizing Rfp Questions For Your Business Needs
Quick Summary
| Takeaway | Explanation |
|---|---|
| Craft RFP Questions Strategically | Develop RFP questions that assess vendors’ core capabilities and alignment with business goals to enhance decision-making. |
| Prioritize Security and Compliance | Ask detailed questions about data protection and regulatory compliance to ensure vendor security practices meet necessary standards. |
| Assess Implementation and Support | Evaluate the vendor's implementation strategy and support services to ensure smooth integration and ongoing assistance. |
| Create a Structured Evaluation Framework | Implement a standardized scoring system and involve diverse stakeholders to objectively analyze vendor responses. |
| Customize RFP to Fit Your Needs | Tailor questions based on unique organizational goals and existing infrastructure to gauge vendor fit more accurately. |
Essential RFP Questions for B2B Software
Navigating the complex world of B2B software procurement requires strategic questioning that goes beyond surface-level evaluations. Crafting a comprehensive Request for Proposal (RFP) demands precision, depth, and a thorough understanding of your organization's specific requirements.
Strategic Foundational Questions
The initial phase of RFP development centers on establishing a robust framework for vendor assessment. Comprehensive vendor evaluation begins with fundamental inquiries that reveal a vendor's core capabilities and alignment with your business objectives.
Key strategic questions should address:
-
Company Background: Investigate the vendor's history, financial stability, and market positioning. Request detailed information about their organizational structure, years in business, and client portfolio. Research from IT procurement experts suggests that understanding a vendor's long-term viability is crucial for sustainable partnerships.
-
Technical Capabilities: Probe deeply into the software's technical specifications, integration potential, and scalability. Ask specific questions about API capabilities, compatibility with existing systems, and future product roadmaps.
Security and Compliance Interrogation
In the current digital ecosystem, security questions are non-negotiable. B2B software procurement must prioritize robust security frameworks and comprehensive compliance mechanisms. Our guide on security questionnaire automation provides additional insights into this critical evaluation process.
Critical security-related RFP questions should encompass:
- Detailed inquiries about data protection protocols
- Compliance with industry-specific regulatory standards
- Incident response and breach notification procedures
- Third-party security certifications and audit histories
Implementation and Support Assessment
Beyond technical specifications, understanding a vendor's implementation strategy and ongoing support model is paramount. Questions in this domain should reveal the vendor's commitment to client success and their ability to provide seamless technological integration.
Key implementation and support questions include:
- Comprehensive implementation timeline and methodology
- Training and onboarding support mechanisms
- Ongoing technical support structure
- Service level agreements (SLAs) and performance guarantees
By systematically addressing these critical areas, organizations can transform the RFP process from a mundane procurement exercise into a strategic decision-making tool. The goal is not merely to select a software solution but to forge a partnership that drives technological innovation and business growth.
Remember, an exceptional RFP is an investment in your organization's future technological ecosystem. Each question should be crafted with precision, designed to extract meaningful insights that extend far beyond standard vendor responses.
Security and Compliance RFP Questions for CISO Teams
In the rapidly evolving digital security landscape, Chief Information Security Officers (CISOs) must approach vendor selection with unprecedented rigor. The Request for Proposal (RFP) process represents a critical checkpoint for evaluating potential software partners and their commitment to robust security practices.
Fundamental Security Standards and Certifications
The cornerstone of any comprehensive security assessment involves thoroughly examining a vendor's compliance with recognized industry standards. How security questionnaires impact organizational risk highlights the importance of meticulous vendor evaluation.
Research from Promet Source indicates that CISOs should prioritize questions that reveal a vendor's adherence to critical security frameworks such as:
- NIST Compliance: Detailed evidence of alignment with NIST cybersecurity framework guidelines
- ISO 27001 Certification: Proof of international information security management standards implementation
- SOC 2 Type II Reports: Comprehensive third-party audit documentation demonstrating security control effectiveness
To clarify and compare these fundamental security standards and certifications, the table below organizes their key characteristics and purposes:
| Standard/Certification | Purpose | What to Request from Vendor |
|---|---|---|
| NIST Compliance | Aligns security controls with U.S. federal guidelines | Evidence of NIST framework alignment |
| ISO 27001 Certification | Validates international security management standards | ISO 27001 certificate/documentation |
| SOC 2 Type II Report | Verifies operational effectiveness of security controls | Recent SOC 2 Type II audit report |
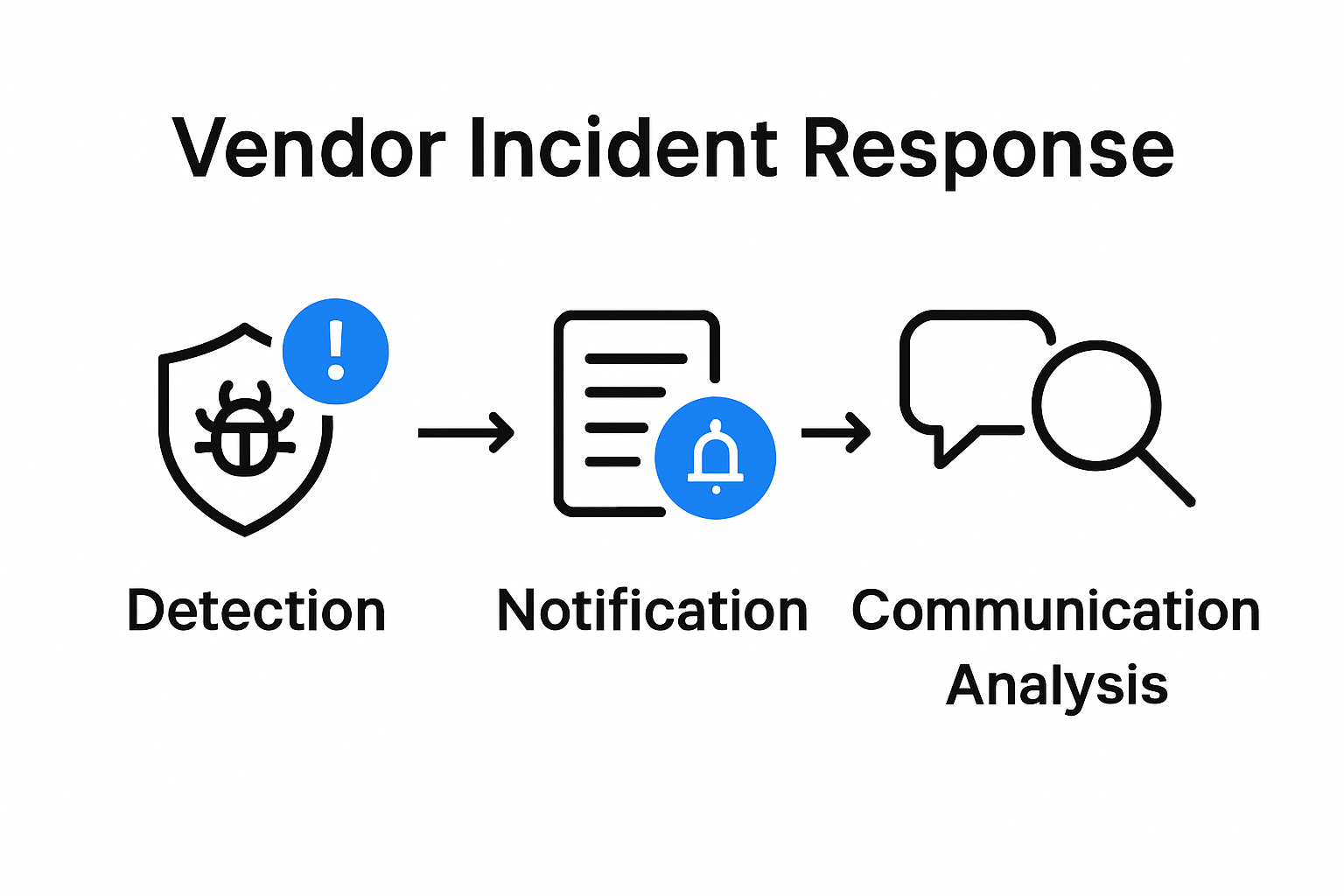
Incident Response and Breach Management
Beyond initial certifications, understanding a vendor's incident response capabilities is paramount. FRS Software emphasizes the critical nature of having a well-documented Cyber Security Incident Response Manual (CSIRM).
Key questions in this domain should probe:
- Specific procedures for detecting and containing potential security breaches
- Communication protocols during security incidents
- Root cause analysis methodologies
- Transparent reporting mechanisms for potential vulnerabilities
Business Continuity and Disaster Recovery
Research from Torii underscores the importance of comprehensive business continuity planning. CISOs must demand detailed insights into a vendor's disaster recovery strategies.
Critical areas of investigation include:
- Documented Business Continuity Plan (BCP) with regular testing protocols
- Defined Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO)
- Infrastructure redundancy mechanisms
- Data backup and restoration procedures
- Third-party dependency management in continuity strategies
The following table summarizes the essential components to look for in a vendor's business continuity and disaster recovery plan:
| Component | Description |
|---|---|
| Business Continuity Plan (BCP) | Detailed, regularly tested recovery procedures |
| Recovery Time Objective (RTO) | Target time to restore services after disruption |
| Recovery Point Objective (RPO) | Maximum allowable data loss in an incident |
| Infrastructure Redundancy | Backup systems and failover capabilities |
| Data Backup & Restoration | Regular backup schedules and restoration process |
| Third-party Dependency Management | Strategies for critical supplier continuity |
Effective security and compliance RFP questions transform vendor selection from a transactional process to a strategic risk management exercise. By systematically addressing these critical domains, CISO teams can establish robust partnerships that prioritize organizational security and resilience.
Remember, the goal extends beyond mere compliance. Each question should be a precision instrument designed to reveal a vendor's genuine commitment to protecting your most valuable digital assets.
Evaluating Vendor Responses: Best Practices
Transforming raw vendor responses into actionable insights requires a systematic and strategic approach. The evaluation process goes far beyond simple compliance checking and demands a nuanced, multifaceted methodology that uncovers the true potential of potential software partners.
Establishing a Robust Evaluation Framework
Research from TechTarget highlights the critical importance of creating a structured evaluation process. Organizations must develop a comprehensive assessment strategy that involves multiple stakeholders and leverages objective evaluation criteria.
Key components of an effective evaluation framework include:
- Standardized Scoring Mechanisms: Create a consistent scoring system that allows for objective comparison across different vendor responses
- Cross-Functional Review Teams: Engage stakeholders from IT, security, operations, and business units to provide holistic insights
- Response Templates: Develop standardized templates that enable systematic and comparable vendor response analysis
Detailed Response Analysis Techniques
Research from George Mason University suggests a methodical approach to dissecting vendor responses. Our comprehensive guide on security questionnaire formats provides additional context for navigating complex response evaluations.
Critical analysis techniques should encompass:
- Eliminating non-compliant proposals immediately
- Creating a detailed response matrix for side-by-side comparisons
- Conducting thorough life cycle cost analyses
- Verifying claims through independent references and additional due diligence
Advanced Evaluation Strategies
Beyond traditional assessment methods, forward-thinking organizations must adopt more sophisticated evaluation approaches. This involves looking beyond surface-level responses to understand the deeper strategic alignment and potential long-term partnership capabilities.
Advanced evaluation strategies include:
- Capability Mapping: Align vendor capabilities with specific organizational requirements and future growth objectives
- Risk Assessment: Conduct comprehensive risk evaluations that extend beyond immediate technical capabilities
- Innovation Potential: Evaluate vendors not just on current offerings but their demonstrated ability to adapt and innovate
Successful vendor response evaluation is an art form that blends rigorous analytical techniques with strategic vision. It requires a delicate balance between technical scrutiny and understanding the broader potential of a potential partnership.
Remember that the goal is not simply to select a vendor but to identify a strategic technology partner who can grow and evolve alongside your organization. Each response should be viewed as a window into the vendor's potential to become a true collaborative force in your digital transformation journey.
Customizing RFP Questions for Your Business Needs
Customizing Request for Proposal (RFP) questions is not a one-size-fits-all exercise but a strategic process that demands precision, insight, and a deep understanding of your organization's unique technological ecosystem. Research from the W6H Pattern methodology emphasizes the importance of structuring interrogative questions to extract maximum value and specificity.
Defining Organizational Requirements
Acquisition.gov guidelines underscore the critical nature of clear requirement communication. Organizations must develop a comprehensive framework that goes beyond generic inquiries to reveal vendor capabilities that align precisely with business objectives.
Key considerations for defining requirements include:
- Technological Landscape: Map existing technological infrastructure
- Strategic Objectives: Align software selection with long-term business goals
- Performance Metrics: Establish clear, measurable expectations
Structuring Targeted Interrogation Strategies
Our comprehensive guide on security questionnaire challenges highlights the nuanced approach required for effective questioning. Drawing from the W6H methodology, organizations should craft questions that systematically explore:
- What: Specific functional requirements
- Where: Deployment and integration contexts
- When: Implementation timelines and future scalability
- Who: Vendor team capabilities and support structures
- Why: Underlying rationale for proposed solutions
- How: Technical implementation and integration methodologies
- Which: Specific features and differentiators
Advanced Customization Techniques
Technology standards research reveals that effective RFP customization extends beyond simple question formulation. Organizations must develop a holistic approach that:
- Creates flexible yet precise evaluation frameworks
- Encourages vendor innovation
- Allows for comparative analysis across potential solutions
- Maintains regulatory compliance
- Provides sufficient context for comprehensive responses
Successful RFP customization transforms the procurement process from a transactional interaction into a strategic dialogue. Each question becomes an instrument of discovery, designed to uncover not just technical capabilities but potential partnership synergies.
Remember that the most effective RFP questions are those that reveal a vendor's ability to understand and adapt to your specific organizational context. They should challenge vendors to demonstrate not just technical proficiency but a genuine commitment to solving your unique business challenges.
Frequently Asked Questions
What are strategic RFP questions for B2B software?
Strategic RFP questions for B2B software focus on assessing a vendor's core capabilities, security measures, implementation strategies, and support services to ensure alignment with business objectives.
How can I assess a vendor's security and compliance effectively?
To assess a vendor's security and compliance, ask specific questions about data protection protocols, industry regulations they comply with, incident response procedures, and their certifications like ISO 27001 and SOC 2 Type II.
What implementation and support aspects should be evaluated in an RFP?
Key areas to evaluate include the vendor’s implementation timeline, training and onboarding support, ongoing technical assistance, and service level agreements (SLAs) to ensure a smooth integration process.
How can I customize RFP questions for my organization?
Customizing RFP questions involves defining your organization's unique requirements, structuring targeted questions based on technology and strategic goals, and encouraging vendors to demonstrate their ability to address specific challenges.
Turn RFP Challenges Into Strategic Wins With Skypher
Does your team spend too much time digging through complex RFP questions and struggling to complete security questionnaires on tight deadlines? As outlined in "RFP Questions 2025: Critical Insights for B2B Software," the stakes are high. Missing a key compliance or security detail can mean losing trust and delaying critical deals. You need a way to navigate security and compliance questions with confidence while also speeding up your entire procurement cycle.

Discover how Skypher transforms the security questionnaire process into a smooth workflow. Our AI-powered Questionnaire Automation Tool is built for organizations like yours that demand accuracy, real-time team collaboration, and easy integration with your vendor risk systems. Do not let another RFP slow down your growth or put your next deal in jeopardy. Start your journey towards stress-free questionnaires and higher RFP success rates by visiting Skypher now.
Recommended
- The ever growing number of security questionnaires and what you and your company can do to face it
- The Case for Security Questionnaire Automation
- The different formats & mistakes made when writing or answering security questionnaires
- 3 Ways to Speed Up Your Response to Security Questionnaires with Skypher
- Instant Quoting Software for manufacturing
