Online threats are getting more cunning every year. A study found that using multi-factor authentication keeps accounts secure an astonishing 99.99 percent of the time. Sounds unbeatable, right? Not so fast. Most people still think a strong password alone is enough, so they leave doors wide open to hackers. Here’s why even the basics might not protect you in 2025—and what you really need to know to stay safe.
Table of Contents
- Understanding Safe Cyber Practices Today
- How To Protect Your Devices And Accounts
- Top Safe Cyber Habits For Families And Kids
- Responding To Cyber Threats Quickly And Safely
Quick Summary
| Takeaway | Explanation |
|---|---|
| Embrace Zero Trust Architecture | Adopt a proactive security framework that requires continuous verification of every digital interaction, regardless of its origin, to mitigate modern cyber threats. |
| Implement Multi-Factor Authentication (MFA) | Utilize MFA, including biometric verification and hardware security keys, to dramatically reduce the risk of unauthorized access to online accounts. |
| Cultivate Digital Awareness in Families | Encourage open communication about online experiences among family members and teach children to recognize and avoid potential online threats. |
| Prepare an Incident Response Plan | Develop a structured incident response plan with designated roles and immediate action protocols to efficiently address potential cyber threats when they arise. |
| Focus on Continuous Education and Updates | Keep abreast of the latest cybersecurity developments and ensure regular training and software updates to maintain robust protection against cyber threats. |
 |
Understanding Safe Cyber Practices Today
In the rapidly evolving digital ecosystem, safe cyber practices have become more critical than ever. Cybersecurity is no longer a specialized technical concern but a fundamental requirement for individuals and organizations across all sectors.The Changing Landscape of Cybersecurity
The digital threat environment continues to transform at an unprecedented pace. Cybercriminals are becoming increasingly sophisticated, developing advanced techniques that target vulnerabilities in complex technological systems. According to the U.S. Department of Labor, conducting annual risk assessments is crucial for identifying and prioritizing information system risks.
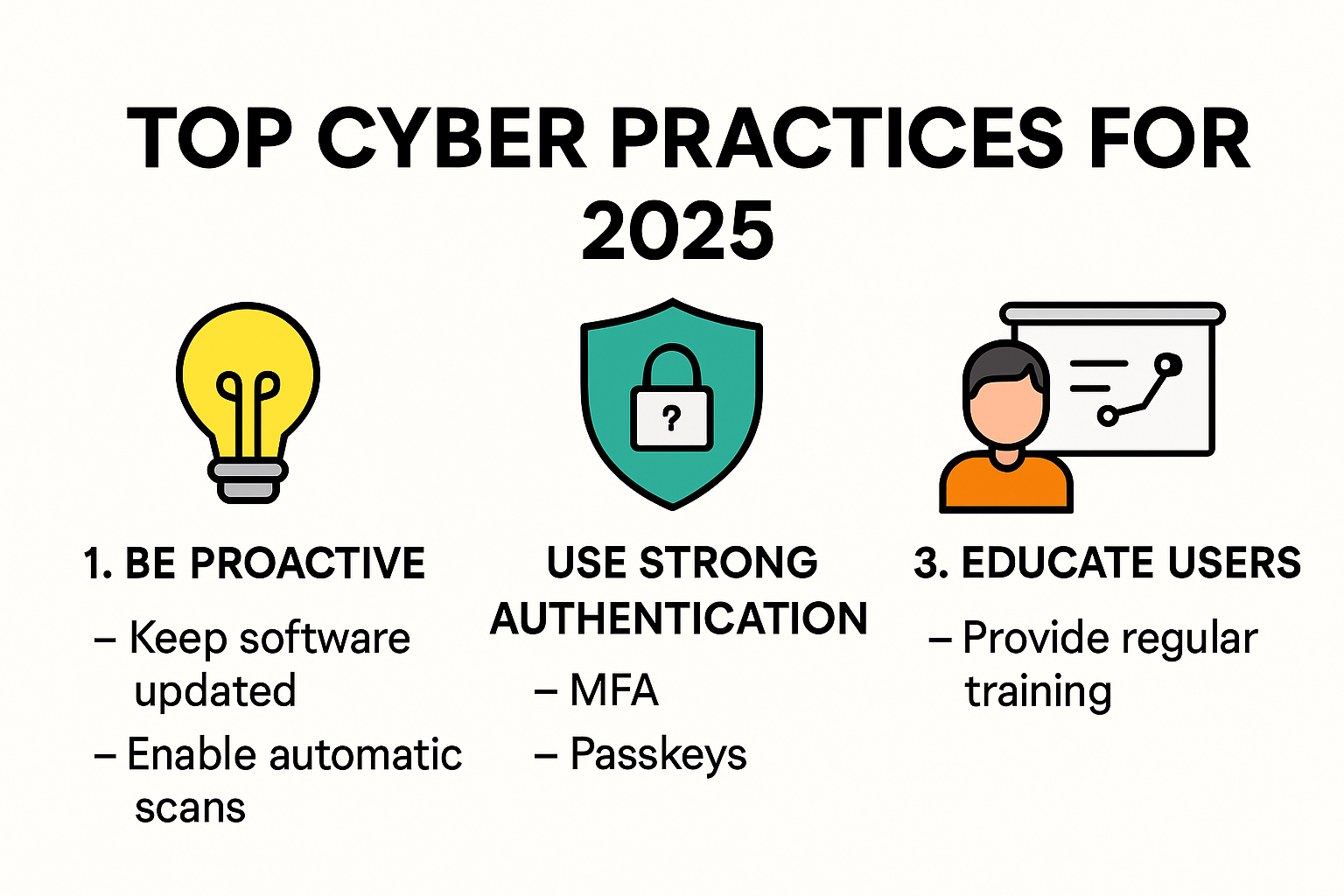
Modern safe cyber strategies require a holistic approach that goes beyond traditional perimeter defense. Organizations must now adopt proactive and adaptive security frameworks that can respond dynamically to emerging threats. Zero Trust architecture has emerged as a leading paradigm, requiring continuous verification of every digital interaction regardless of its origin.
Building a Culture of Cybersecurity Awareness
Effective cyber safety is not just about technological solutions but also about human behavior. The National Institute of Standards and Technology (NIST) emphasizes the importance of integrating cybersecurity education across various learning environments to build a skilled and aware workforce.
Key components of a robust cyber awareness culture include:
- Continuous Training: Regular educational programs that keep staff updated on the latest threat vectors and defensive strategies.
- Simulated Threat Exercises: Practical workshops that help employees recognize and respond to potential cyber risks.
- Personal Accountability: Encouraging individual responsibility for maintaining digital security protocols.
Implementing Comprehensive Protection Strategies
Protecting digital assets requires a multi layered approach. Organizations must implement comprehensive strategies that blend technological solutions with human expertise. EDUCAUSE Review recommends implementing network micro segmentation to isolate critical resources and minimize potential breach impacts.
Effective safe cyber practices in 2025 will likely include:
- Advanced AI driven threat detection systems
- Robust encryption protocols for data at rest and in transit
- Real time monitoring and automated incident response mechanisms
By understanding and implementing these comprehensive safe cyber practices, individuals and organizations can significantly reduce their digital risk exposure and create more resilient technological ecosystems.
How to Protect Your Devices and Accounts
In an era of increasing digital complexity, protecting personal devices and online accounts has become paramount. Cybersecurity is no longer optional but a critical necessity for maintaining digital safety and personal information integrity.
Strengthening Account Security
Account protection begins with robust authentication mechanisms. Research from Harvard Privacy and Security Studies reveals that implementing strong security protocols can dramatically reduce unauthorized access risks. Multi-Factor Authentication (MFA) stands out as a powerful defense strategy.
According to a comprehensive study published in arXiv, accounts utilizing MFA experienced an astounding 99.99% security rate during the research period. This means adding an extra verification layer significantly minimizes the potential for unauthorized account access.
Key MFA implementation strategies include:
- Biometric Verification: Using fingerprint or facial recognition
- Hardware Security Keys: Physical devices that provide an additional authentication step
- Time Based One Time Passwords: Dynamic codes generated for specific login attempts

Device Protection Fundamentals
Modern devices require comprehensive protection strategies that go beyond traditional antivirus software. Regular software updates play a crucial role in maintaining device security. Harvard Privacy Researchers emphasize that software updates often include critical security patches addressing known system vulnerabilities.
Effective device protection involves:
- Automated Update Settings: Ensuring your operating system and applications receive timely security patches
- Comprehensive Endpoint Protection: Installing robust security software that monitors potential threats
- Network Security Configuration: Utilizing secure and encrypted network connections
Advanced Security Techniques
Beyond basic protections, advanced users can implement sophisticated security measures. This includes utilizing virtual private networks (VPNs), encrypting sensitive data, and maintaining strict privacy settings across digital platforms.
Consider implementing these advanced techniques:
- Utilize end to end encryption for communication platforms
- Regularly audit connected devices and remove unnecessary access permissions
- Create complex and unique passwords for different accounts
- Use password management tools to generate and store secure credentials
Protecting your digital ecosystem requires continuous attention and proactive strategies. By understanding and implementing these comprehensive device and account protection methods, you can significantly reduce your vulnerability to cyber threats and maintain robust digital security.
Here is a table summarizing different Multi-Factor Authentication (MFA) methods and their key features to help you choose the most suitable option for strengthening account security:
| MFA Method | Description | Example Platforms | Key Security Benefit |
|---|---|---|---|
| Biometric Verification | Uses fingerprint or facial recognition | Smartphones, Laptops | High; personal and unique |
| Hardware Security Key | Physical device for extra authentication | Google, Microsoft, GitHub | Very high; hard to replicate |
| Time-Based One-Time Password | Dynamic codes generated per login attempt | Banking apps, Email | High; changes each use |
Top Safe Cyber Habits for Families and Kids
In the digital age, teaching safe cyber practices to children has become as essential as teaching road safety. Families play a crucial role in developing strong digital literacy and protective behaviors that safeguard children from online risks.
Creating a Culture of Digital Awareness
Open communication forms the foundation of digital safety for families. The Department of Homeland Security emphasizes the importance of establishing trust and dialogue about online experiences. Parents should create an environment where children feel comfortable discussing their digital interactions without fear of judgment.
Key strategies for building digital awareness include:
- Regular family discussions about online experiences
- Sharing age appropriate digital safety stories
- Demonstrating positive online behavior
- Listening without overreacting to potential digital challenges
Implementing Robust Security Practices
Security is not just about technology but about developing smart digital habits. Australian Cyber Security Centre recommends implementing strong authentication methods and teaching children about digital protection.
Critical security practices for families involve:
- Strong Password Management: Teaching children how to create complex passwords
- Multi Factor Authentication: Enabling additional verification layers on accounts
- Privacy Settings: Regularly reviewing and updating social media and device privacy configurations
Recognizing and Avoiding Online Threats
Educating children about potential digital dangers is crucial for their online safety. Walden University Cybersecurity Research highlights the importance of teaching children to recognize and avoid online threats.
Essential threat recognition skills include:
- Identifying suspicious messages and emails
- Understanding the risks of sharing personal information
- Recognizing potential online predatory behaviors
- Learning about digital footprints and long term consequences of online actions
By consistently implementing these safe cyber habits, families can create a supportive digital environment that protects children while allowing them to explore and learn in the online world. The goal is not to instill fear but to empower children with knowledge and critical thinking skills that will serve them throughout their digital lives.
Responding to Cyber Threats Quickly and Safely
In the complex digital landscape, understanding how to respond to cyber threats efficiently can mean the difference between minor disruption and catastrophic damage. Rapid and strategic response becomes critical when facing potential security breaches.
Developing a Comprehensive Incident Response Plan
Preparing for potential cyber incidents requires a structured approach. The National Institute of Standards and Technology (NIST) emphasizes the importance of creating a detailed incident response plan that clearly defines organizational protocols.
Key components of an effective incident response strategy include:
- Clear Role Assignment: Designate specific team members with defined responsibilities during a cyber incident
- Immediate Action Protocols: Establish step by step procedures for containment and mitigation
- Communication Channels: Create predefined communication pathways for rapid information sharing
- Forensic Documentation: Implement processes for preserving evidence and conducting post incident analysis
Below is a table outlining the main components of an incident response plan and their purposes to help you understand the structured process of dealing with cyber threats effectively:
| Component | Purpose |
|---|---|
| Clear Role Assignment | Defines who does what during an incident |
| Immediate Action Protocols | Outlines steps for containment and mitigation |
| Communication Channels | Enables fast and organized information flow |
| Forensic Documentation | Preserves evidence for analysis and learning |
Implementing Immediate Threat Mitigation Techniques
When a potential cyber threat is detected, speed and precision are paramount. The Small Business Administration recommends implementing multi-layered security strategies to minimize potential damage.
Critical immediate response techniques include:
- Isolation of Affected Systems: Disconnect compromised devices from networks to prevent further spread
- Password Reset Procedures: Immediately change credentials for potentially compromised accounts
- Data Backup Verification: Ensure recent backups are intact and accessible
- External Reporting: Notify relevant authorities and cybersecurity agencies about the incident
Systematic Recovery and Future Prevention
Recovery from a cyber incident involves more than just restoring systems. George Washington University IT Security highlights the importance of learning from each incident to strengthen future defenses.
Post incident recovery strategies should focus on:
- Conducting comprehensive system audits
- Identifying and patching specific vulnerabilities
- Updating security protocols based on incident insights
- Providing additional training for team members
Responding to cyber threats is not about perfection but about resilience. By developing robust response mechanisms, organizations can transform potential security disasters into manageable challenges. The goal is to create an adaptive system that learns and improves with each encountered threat.
Remember that effective cyber threat response is an ongoing process requiring continuous education, technological adaptation, and a proactive mindset. Stay informed, stay prepared, and prioritize your digital safety.
Frequently Asked Questions
What is multi-factor authentication (MFA) and why is it important for online security in 2025?
Multi-factor authentication (MFA) is a security process that requires users to provide two or more verification factors to gain access to an account. It is important for online security in 2025 because it dramatically reduces the risk of unauthorized access, with studies showing a 99.99% security rate for MFA-enabled accounts.
How can families educate children about safe online practices?
Families can educate children about safe online practices by encouraging open communication about their digital experiences, sharing age-appropriate safety stories, and teaching them to recognize online threats such as suspicious messages and the risks associated with sharing personal information.
What are some key components of an effective incident response plan for cyber threats?
Key components of an effective incident response plan include clear role assignments, immediate action protocols for containment and mitigation, established communication channels for information sharing, and forensic documentation to preserve evidence for post-incident analysis.
How can individuals protect their devices against cyber threats in 2025?
Individuals can protect their devices by keeping software updated, utilizing comprehensive endpoint protection, employing virtual private networks (VPNs), using strong passwords, and enabling multi-factor authentication on their accounts.
Move Beyond Basic Cyber Hygiene with Skypher’s AI Security Automation
You already know that strong passwords and multi-factor authentication are critical, but what’s your strategy for managing the rising complexity of security reviews and compliance checks? The article highlighted how evolving threats in 2025 demand both top-tier account protection and agile incident response. If your team feels overwhelmed by ever-growing security questionnaires or spends hours manually answering client requests, you are not alone. In fact, bottlenecks in security reviews often slow down sales and raise stress for your risk and compliance teams, even as the need for accuracy and real-time collaboration grows.

Meet Skypher, the all-in-one AI-driven Questionnaire Automation Tool built for organizations with serious cybersecurity goals. Lighten the load on your team with a platform that streamlines repetitive tasks, integrates directly with your existing risk management solutions, and boosts trust during sales and vendor assessments. Ready to transform your security questionnaire process and respond to client demands quickly? Explore our AI-powered features or book a personalized demo right at Skypher.co. Start saving time and strengthening your security posture today.
