B2B software companies face higher stakes than ever when it comes to keeping customer data safe. A single security breach can cost businesses an average of $4.45 million. Most assume installing firewalls or antivirus software is enough protection. The real advantage lies in building a security and compliance center that not only defends but actually turns security into a business asset.
Table of Contents
- Key Features Of Security And Compliance Center
- Benefits For B2B Software Companies
- Implementing Effective Security And Compliance Strategies
- Best Practices For CISO And GRC Teams
Quick Summary
| Takeaway | Explanation |
|---|---|
| Implement Multi-Factor Authentication | Enhances security by requiring additional verification steps beyond just passwords. |
| Focus on Real-Time Threat Detection | Utilizing AI and machine learning helps identify and respond to abnormal activities swiftly. |
| Regular Compliance Audits Are Essential | Performing audits ensures adherence to regulatory standards and identifies gaps in security practices. |
| Cultivate a Security-Conscious Culture | Training employees to recognize threats fosters a proactive security environment throughout the organization. |
| Position CISO at Board Level | Direct reporting to the board enables unbiased risk assessments and aligns security with business objectives. |
Key Features of Security and Compliance Center
A robust security and compliance center goes beyond basic protection mechanisms. It serves as a comprehensive framework that empowers organizations to manage, monitor, and mitigate potential security risks effectively. The core features of an advanced security and compliance center are designed to provide holistic protection across multiple dimensions of organizational security.
Below is a summary table outlining the core features of a Security and Compliance Center and their key functions, helping organizations understand where each feature fits into an effective security ecosystem.
| Feature | Key Functions |
|---|---|
| Identity & Access Management | User authentication, role-based access, single sign-on |
| Threat Detection & Response | Continuous monitoring, automated alerts, activity logging |
| Compliance & Reporting | Regulatory tracking, audit trail documentation, report generation |
Identity and Access Management
Identity and access management represents the foundational pillar of any security infrastructure. Learn more about advanced access controls helps organizations establish precise user permissions and authentication protocols. According to Google's Security Whitepaper, implementing multi-factor authentication and the principle of least privilege are critical strategies. This approach ensures that users have access only to resources necessary for their specific roles, dramatically reducing potential security vulnerabilities.
Key components of identity management include:
- User Authentication: Implementing robust verification processes
- Role-Based Access Control: Restricting system access based on organizational roles
- Single Sign-On (SSO): Streamlining user access across multiple platforms
Threat Detection and Response
Advanced security centers must provide real-time threat monitoring and rapid response capabilities. The UK Government Security Group emphasizes the importance of proactive threat management. Modern security platforms utilize artificial intelligence and machine learning algorithms to detect anomalous activities, potential data breaches, and unauthorized access attempts.
Effective threat detection strategies involve:
- Continuous Monitoring: 24/7 surveillance of network activities
- Automated Alerts: Instant notifications for suspicious behaviors
- Comprehensive Logging: Detailed records of all system interactions
Compliance and Reporting
Compliance is not merely a checkbox but a critical organizational requirement. A sophisticated security and compliance center generates comprehensive reports that demonstrate adherence to industry standards and regulatory frameworks. These reports provide transparency, facilitate audits, and help organizations maintain their security certifications.
Reporting features typically include:
- Regulatory Compliance Tracking: Monitoring alignment with industry standards
- Customizable Report Generation: Tailored insights for different stakeholders
- Audit Trail Documentation: Detailed logs for forensic analysis
By integrating these key features, organizations can create a resilient security ecosystem that protects critical assets, maintains regulatory compliance, and builds trust with stakeholders. The goal is not just prevention but creating an adaptive, intelligent security infrastructure that evolves with emerging technological challenges.
Benefits for B2B Software Companies
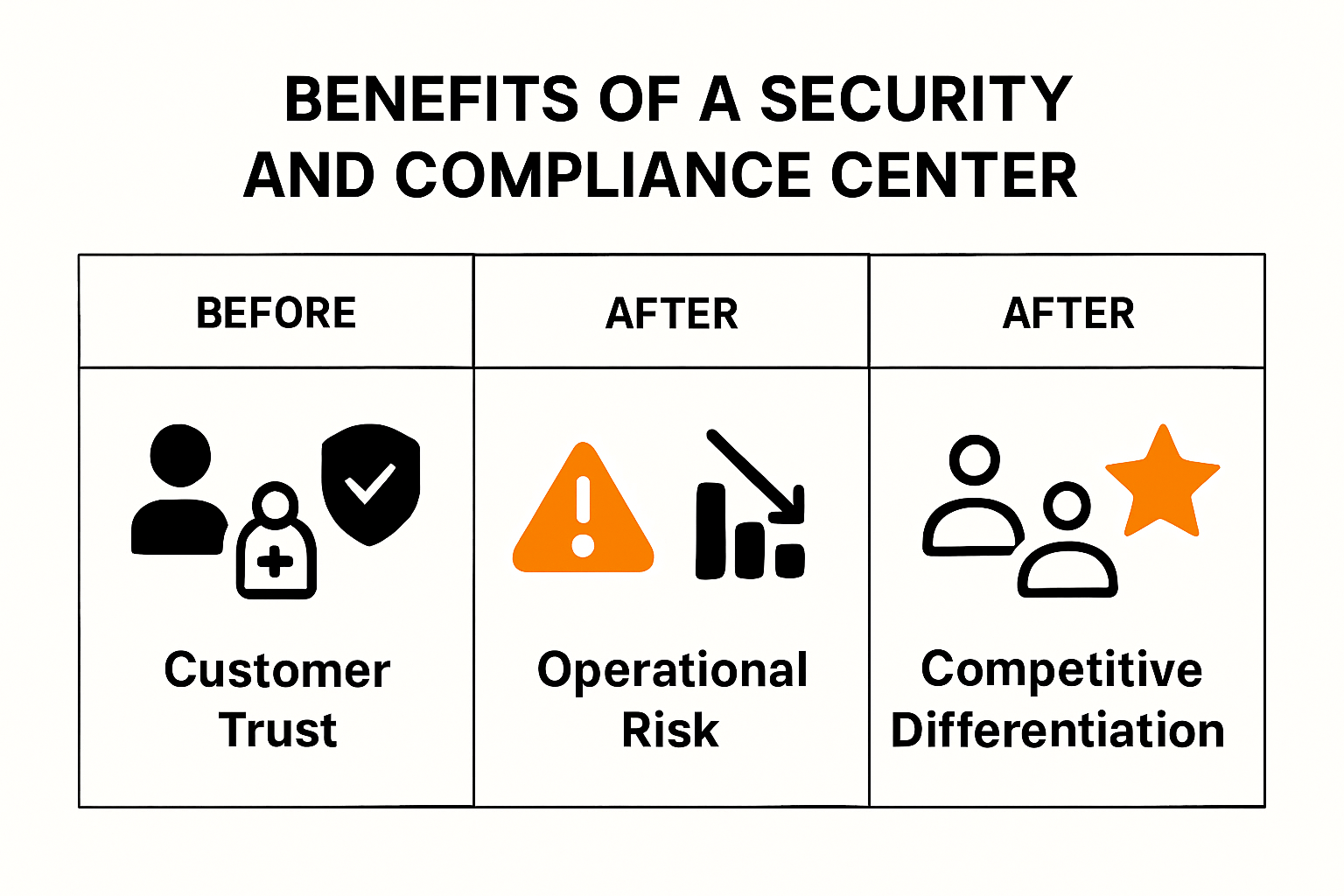
B2B software companies operate in a complex digital ecosystem where security and compliance are not just optional features but critical business imperatives. A comprehensive security and compliance center offers transformative advantages that extend far beyond basic risk mitigation.
The table below summarizes the main benefits that a Security and Compliance Center delivers for B2B software companies, highlighting both protective and strategic advantages.
| Benefit | Description |
|---|---|
| Enhanced Customer Trust & Credibility | Builds reputation through strong security practices |
| Operational Risk Reduction | Minimizes financial and reputational damages |
| Competitive Differentiation | Positions company as a secure and trustworthy partner |
Enhanced Customer Trust and Credibility
In the competitive B2B software marketplace, trust is the ultimate currency. Explore our enterprise security solutions demonstrate how robust security frameworks can significantly elevate a company's reputation. According to the Small Business Administration, conducting thorough cybersecurity risk assessments helps businesses identify vulnerabilities and create actionable protection strategies.
Customer trust is built through demonstrable security practices:
- Transparent Security Protocols: Clear communication about protection mechanisms
- Continuous Compliance Verification: Regular audits and certifications
- Proactive Risk Management: Demonstrating commitment to data protection
Operational Risk Reduction
A strategic security and compliance center provides comprehensive risk management capabilities that directly impact business continuity. The Indiana Cybersecurity Department highlights that automated compliance processes can significantly reduce potential financial and reputational damages associated with security breaches.
Key risk reduction strategies include:
- Automated Vulnerability Detection: Identifying potential security weaknesses
- Incident Response Planning: Developing rapid mitigation protocols
- Comprehensive Data Protection: Securing critical business information
Competitive Differentiation
In an era where data breaches can devastate business relationships, a robust security framework becomes a powerful market differentiator. Federal Trade Commission guidelines emphasize implementing fundamental cybersecurity measures such as software updates, secure file management, and multi-factor authentication.
Competitive advantages emerge through:
- Advanced Security Certifications: Demonstrating superior protection standards
- Regulatory Compliance: Meeting and exceeding industry requirements
- Client Confidence: Providing assurance through comprehensive security mechanisms
By investing in a sophisticated security and compliance center, B2B software companies transform potential vulnerabilities into strategic strengths. This approach not only protects organizational assets but also positions the company as a trustworthy, forward-thinking technology partner in an increasingly complex digital landscape.
Implementing Effective Security and Compliance Strategies
Implementing robust security and compliance strategies requires a comprehensive, proactive approach that goes beyond traditional defensive mechanisms. Organizations must develop a multifaceted framework that addresses technological, operational, and human factors to create a resilient security ecosystem.
Strategic Framework Development
Building an effective security strategy starts with comprehensive risk assessment and strategic planning. Understand security questionnaire challenges provides insights into the complex landscape of organizational security. According to research published in ArXiv, integrating advanced technologies like blockchain can enhance transparency and traceability in vendor risk management, creating an immutable record of security assessments.
Key components of strategic framework development include:

- Comprehensive Risk Mapping: Identifying potential vulnerabilities across systems
- Vendor Risk Assessment: Evaluating third-party security protocols
- Continuous Monitoring: Implementing real-time threat detection mechanisms
Technology and Infrastructure Security
Modern security strategies must prioritize robust technological infrastructure that can adapt to evolving cyber threats. Forbes Tech Council emphasizes the critical importance of architectural choices, recommending single-tenant hosting environments to minimize shared security risks.
Critical technological security strategies involve:
- Secure Architecture Design: Implementing isolated, dedicated infrastructure
- Access Control Mechanisms: Granular permission management
- Encryption Protocols: Protecting data at rest and in transit
Cultural and Human Factor Integration
Technology alone cannot guarantee complete security. Organizations must cultivate a comprehensive security culture that empowers employees to become active participants in the protection ecosystem. This involves continuous training, awareness programs, and creating an environment where security consciousness is ingrained in daily operations.
Human-centric security approaches include:
- Regular Security Training: Educating teams about emerging threats
- Incident Response Preparedness: Developing clear communication protocols
- Security Awareness Programs: Creating a proactive security mindset
By integrating technological sophistication with strategic planning and human awareness, organizations can create a holistic security and compliance approach. This multidimensional strategy transforms security from a reactive function to a proactive, adaptive system that continuously evolves to meet emerging challenges in the digital landscape.
Best Practices for CISO and GRC Teams
Chief Information Security Officers (CISOs) and Governance, Risk, and Compliance (GRC) teams play a critical role in developing and maintaining an organization's security strategy. Their responsibilities extend far beyond traditional security management, requiring a holistic approach that integrates technological expertise with strategic business understanding.
Strategic Organizational Positioning
Learn more about security questionnaire strategies highlights the complex landscape CISOs navigate. According to research from Berkeley Management Review, the structural positioning of the CISO is crucial. The recommendation is clear: CISOs should report directly to the Board, ensuring objective threat assessment and preventing potential conflicts of interest that might arise from reporting to technical executives like CIOs or CTOs.
Key strategic positioning considerations include:
- Independent Reporting Lines: Direct communication with board leadership
- Objective Risk Assessment: Unbiased security evaluation
- Strategic Alignment: Connecting security initiatives with business objectives
Governance and Compliance Framework
EC Council's Cybersecurity Exchange emphasizes the importance of developing comprehensive cybersecurity governance. This involves creating clear roles, establishing robust policies, and ensuring that security objectives are tightly aligned with overall business goals.
Critical governance elements include:
- Policy Development: Creating clear, actionable security guidelines
- Role Definition: Establishing precise responsibilities
- Continuous Compliance Monitoring: Regular assessment and adaptation
Board Communication and Resource Alignment
TechTarget's Security Planning Guide underscores the critical need for CISOs to effectively communicate cybersecurity metrics and potential risks to the board. This communication is essential for securing necessary resources and maintaining organizational support for security initiatives.
Effective communication strategies include:
- Metrics-Driven Reporting: Presenting quantifiable security insights
- Risk Translation: Converting technical challenges into business language
- Strategic Resource Justification: Demonstrating the business value of security investments
Successful CISO and GRC teams recognize that security is not just a technical challenge but a strategic business imperative. By positioning themselves strategically, developing robust governance frameworks, and communicating effectively, they transform security from a cost center to a value-generating organizational function. The most effective teams view security as an enabler of business innovation and growth, rather than a mere defensive mechanism.
Frequently Asked Questions
What are the key features of a Security and Compliance Center?
A Security and Compliance Center typically includes features such as Identity and Access Management, Threat Detection and Response, and Compliance and Reporting, which help organizations manage and mitigate security risks effectively.
How can a Security and Compliance Center enhance customer trust?
By implementing robust security practices and maintaining continuous compliance verification, organizations can build a strong reputation, reassuring customers that their data is protected and that they prioritize cybersecurity.
What benefits does a strategic security framework provide for B2B software companies?
A strategic security framework enhances customer trust, reduces operational risks, and provides competitive differentiation, all of which contribute to a company's long-term success in the B2B marketplace.
Why is real-time threat detection important in security management?
Real-time threat detection is crucial because it allows organizations to swiftly identify and respond to potentially harmful activities, thereby preventing data breaches and minimizing the impact of security incidents.
Transform Security Compliance Into a Competitive Edge
Security teams in B2B software are under constant pressure to streamline assessments and build customer trust. If your organization is tired of time-consuming security questionnaires and struggles with proving compliance quickly, you are not alone. The stakes are high—your security and compliance program needs to be both airtight and efficient. Skypher helps you overcome the exact challenges explored in our guide, including automating compliance workflows and enabling fast, accurate responses to security reviews.

Ready to prove your security posture and win deals faster? Discover how the AI Questionnaire Automation Tool from Skypher reduces turnaround time, improves audit readiness, and helps you showcase your custom Trust Center for maximum client confidence. Visit https://skypher.co and start turning complex compliance processes into a strategic asset for your team today.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- The Case for Security Questionnaire Automation
- The ever growing number of security questionnaires and what you and your company can do to face it
- Features
- Steps to comply CCPA compliance by Bista Solutions
- Document Version Control for Businesses in 2025: Best Practices and Adobe Solutions - Mapsoft
