Phishing attacks still account for 40% of incidents in 2025, revealing a persistent challenge despite growing cybersecurity investments. Security awareness programs have evolved from checkbox compliance exercises into strategic initiatives that measurably reduce human cyber risk. This guide shows you how to build a tailored security awareness program that improves employee behaviors, streamlines compliance processes, and protects your organization from evolving threats.
Table of Contents
- Introduction To Security Awareness Programs
- Prerequisites And Preparation Before Launching Your Program
- Step 1: Program Assessment And Planning
- Step 2: Team Building And Role Definition
- Step 3: Role-Based Training Development
- Step 4: Multi-Channel Awareness Delivery
- Step 5: Tool Integration For Efficiency
- Common Mistakes And Troubleshooting
- Measuring Success And Continuous Improvement
- Expected Results And Timelines
- Enhance Your Security Awareness With Skypher Automation
- Frequently Asked Questions
Key Takeaways
| Point | Details |
|---|---|
| Risk Reduction | Security awareness programs reduce human cyber risk by up to 35% within a year when properly implemented. |
| Role-Based Training | Tailored training by employee role improves engagement and behavior adoption by 25%. |
| Leadership Impact | Programs with dedicated teams and executive support see 40% higher success rates. |
| Multi-Channel Delivery | Using varied training methods boosts retention and policy compliance by 30%. |
| Automation Integration | AI-driven questionnaire tools accelerate compliance workflows and reduce manual errors. |
Introduction to Security Awareness Programs
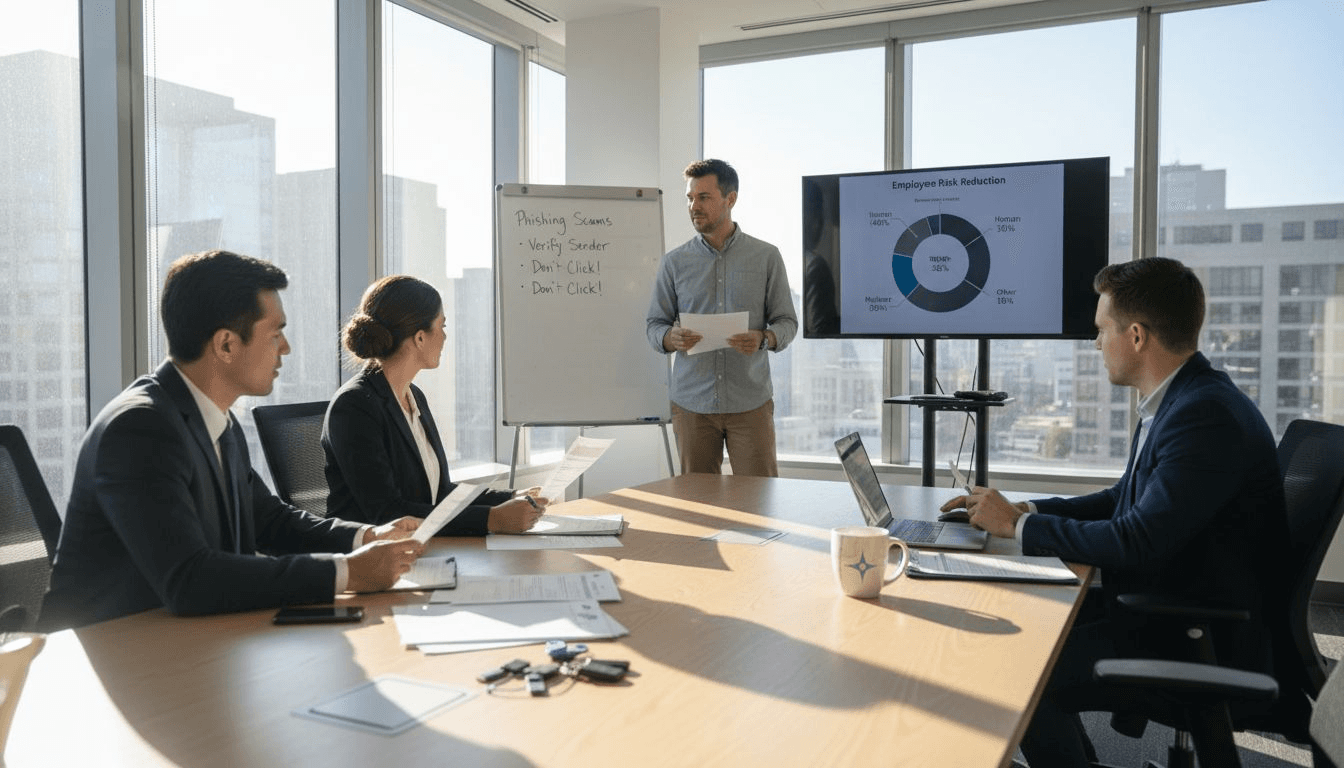
Human factors remain the primary vulnerability in organizational cybersecurity. Your employees face sophisticated social engineering attacks daily, from phishing emails to business email compromise schemes. Embedding a strong security culture through ongoing awareness programs reduces these human-related cyber risks significantly.
Effective security awareness programs align with organizational culture rather than imposing generic training. You need continuous program evolution to address emerging cyber threats targeting your specific industry. Finance and tech sectors face unique risks requiring specialized approaches.
Consider these foundational elements:
- Programs must be ongoing initiatives, not annual compliance checkboxes
- Content should address real threats your employees encounter
- Training must align with your organizational risk profile and regulatory requirements
- Measurement systems track behavioral changes, not just completion rates
Pro Tip: Start by identifying the top three threats your industry faces. Finance organizations might prioritize wire fraud and account takeover, while tech companies focus on intellectual property theft and supply chain attacks.
Prerequisites and Preparation Before Launching Your Program
You cannot build an effective security awareness program without proper groundwork. Executive sponsorship provides sustained leadership support and resource allocation necessary for long-term success. Assembling a dedicated security awareness team with defined roles enhances program implementation success rates by 40%.
Secure these critical elements before launch:
- Executive sponsor who champions the program and maintains visibility
- Cross-functional team including IT security, compliance, HR, and communications
- Budget allocation covering tools, content development, and staff time
- Assessment of current program maturity using established frameworks
Your risk assessment should identify vulnerabilities specific to your organization. Tech companies with remote workforces face different threats than finance firms with hybrid models. Understanding your threat landscape shapes program priorities and security coding training needs.
Form your team with clear role definitions. Your program owner oversees governance and reporting. Security specialists develop technical content. Communications experts ensure messages resonate. HR coordinates delivery logistics. Each role contributes unique expertise to essential security training development.
Pro Tip: Schedule monthly meetings with your executive sponsor to review metrics and maintain engagement. This regular touchpoint ensures leadership stays invested throughout the program lifecycle.
Step 1: Program Assessment and Planning
Assessment establishes your starting point and guides improvement priorities. Using a maturity model to assess current state and plan incremental improvements leads to higher success and leadership buy-in. The Security Awareness Maturity Model® provides a structured framework for evaluation.
Follow these planning steps:
- Evaluate your current program across key dimensions like content quality, delivery methods, and metrics
- Define specific, measurable objectives aligned with organizational risk reduction goals
- Set realistic timelines for achieving maturity milestones
- Establish reporting mechanisms that maintain leadership engagement
Your objectives should include quantifiable targets. Reduce phishing simulation click rates by 50% within six months. Achieve 95% training completion within mandated timeframes. Decrease security incident reports by 30% year over year.
| Maturity Level | Characteristics | Timeline |
|---|---|---|
| Non-Existent | No formal program, ad-hoc training only | Starting point |
| Compliance Focused | Annual required training, minimal metrics | 3-6 months |
| Promoting Awareness | Regular communications, basic simulations | 6-12 months |
| Long-Term Culture Change | Integrated behaviors, advanced metrics | 12-18 months |
| Metrics Framework | Data-driven decisions, continuous improvement | 18+ months |
Develop reporting dashboards tracking key performance indicators. Share monthly updates with leadership highlighting progress toward objectives. This visibility maintains support and demonstrates program value.
Integrate your planning with broader compliance initiatives. Security questionnaire automation can streamline vendor assessments while reinforcing awareness program messages. Connect awareness efforts to operational efficiency gains leadership values.
Pro Tip: Create a one-page roadmap showing quarterly milestones and quick wins. Leadership responds better to visual timelines than detailed project plans. Update this roadmap quarterly as you achieve objectives and identify new priorities.
Step 2: Team Building and Role Definition
Program governance requires clear ownership and distributed responsibilities. Assign a single program owner who maintains oversight and accountability. This person coordinates cross-functional efforts and reports progress to leadership.
Dedicated security awareness teams with clear roles increase program success by 40%. Your team structure should reflect organizational needs and available resources. Smaller organizations might combine roles while larger enterprises require specialized positions.
Define these core responsibilities:
- Program owner manages strategy, budgets, and executive reporting
- Content developers create training materials tailored to your organization
- Technical specialists implement tools and measure effectiveness
- Communications experts craft messages that resonate with employees
IT teams focus on technical controls and incident response integration. Finance teams ensure compliance with regulations like SOC 2 and PCI DSS. Compliance teams align awareness efforts with audit requirements and role-based training development.
Establish communication channels between teams. Weekly stand-ups keep everyone aligned. Shared project management tools track deliverables. Regular coordination prevents duplicate efforts and ensures consistent messaging across the organization.
Your team needs authority to implement changes and access to necessary resources. Without executive backing, teams struggle to gain employee participation or secure budget for tools and content.
Step 3: Role-Based Training Development
Generic training fails because employees face different threats based on their roles. Tailored training content by employee role improves behavior adoption by 25%. IT staff need technical security training while finance teams require fraud detection skills.
Develop distinct modules addressing role-specific risks:
- IT and security teams receive advanced technical training on secure coding, infrastructure hardening, and incident response
- Finance teams learn wire fraud prevention, account verification procedures, and financial data protection
- Executives receive targeted training on business email compromise and high-value target attacks
- All employees complete foundational training covering phishing, password security, and data handling
Prioritize training topics using recent attack data. If your industry sees increased business email compromise attempts, make email authentication a top priority. Ransomware surges require backup and recovery awareness.

Incorporate real scenarios employees encounter daily. Use actual phishing emails your organization received, sanitized for training purposes. Walk through incident response procedures with hands-on exercises. This practical approach increases engagement and retention compared to abstract concepts.
Update content continuously to reflect evolving threats. Quarterly content reviews ensure training remains relevant. New attack techniques require new awareness modules. Role-based security training evolves with your threat landscape.
Step 4: Multi-Channel Awareness Delivery
Single-channel training creates fatigue and reduces effectiveness. Use of multiple delivery methods leads to 30% increase in retention and security policy compliance. You need varied formats addressing different learning styles and attention spans.
Deploy these delivery channels:
- Phishing simulations testing real-world response and identifying high-risk users
- Digital training modules providing flexible, self-paced learning
- Physical materials like posters and desk reminders reinforcing key messages
- Contests and challenges gamifying security behaviors and creating friendly competition
Interactive learning deepens retention better than passive content consumption. Scenario-based exercises require employees to make decisions and see consequences. Branching scenarios adapt based on choices, providing personalized learning paths.
Schedule training at regular intervals without overwhelming employees. Monthly phishing simulations maintain vigilance. Quarterly training modules cover new topics. Weekly security tips in company newsletters keep awareness top of mind.
Vary communication formats to prevent fatigue. Video content one month, interactive quizzes the next, then team challenges. This variety maintains engagement throughout the year. Automation tips for awareness programs can streamline content delivery.
Pro Tip: Launch phishing simulations on different days and times each month. Attackers do not follow predictable schedules, and neither should your tests. This unpredictability keeps employees alert rather than gaming the system.
Step 5: Tool Integration for Efficiency
Technology amplifies program impact while reducing manual effort. AI-powered automation transforms time-consuming security questionnaire processes into streamlined workflows. Integration with collaboration platforms ensures awareness messages reach employees where they already work.
Implement these technology integrations:
- AI-powered questionnaire automation reducing manual response efforts by 80% or more
- Collaboration platform integrations with Slack and Microsoft Teams for seamless communication
- API connections to third-party risk management systems enabling automated workflows
- Document management integrations with Confluence, Notion, and SharePoint centralizing security content
| Approach | Time Required | Error Rate | Scalability |
|---|---|---|---|
| Manual Questionnaire Response | 40-60 hours per questionnaire | 15-20% inconsistencies | Limited by staff capacity |
| Automated Questionnaire Response | 1-2 hours per questionnaire | Under 5% with AI validation | Handles 200+ questions in minutes |
Your security awareness program generates frequent questionnaire requests from customers and partners. Manual responses consume valuable time while introducing inconsistencies. Automation benefits for questionnaires include faster turnaround, higher accuracy, and freed capacity for strategic work.
Integrate awareness program content into your knowledge base. AI systems reference this content when generating questionnaire responses, ensuring consistency between training and external communications. This integration reinforces key messages while improving security questionnaire response automation.
Common Mistakes and Troubleshooting
Programs fail when organizations treat awareness as a one-time event rather than ongoing commitment. Over 60% of failed programs have outdated training content leading to reduced effectiveness. You must continuously update materials to address emerging threats.
Avoid these common pitfalls:
- Treating annual compliance training as sufficient security awareness
- Using generic content that does not address your specific risk profile
- Failing to update training as threats evolve
- Neglecting metrics and behavioral measurement
- Losing leadership engagement after initial program launch
55% of unsuccessful programs lacked sustained leadership engagement. Your executive sponsor must remain visible throughout the program lifecycle. Regular metric reporting and success stories maintain this engagement.
Employee training fatigue emerges when programs rely on single delivery methods. Combat this by varying formats, keeping sessions short, and making content relevant to daily work. Tips to avoid program fatigue include gamification and peer-led initiatives.
Programs stagnate when teams stop measuring and iterating. Your awareness program requires the same continuous improvement approach you apply to other business processes.
Troubleshoot low engagement by surveying employees about content relevance and delivery preferences. Adjust based on feedback rather than assuming you know what works.
Measuring Success and Continuous Improvement
Measurement transforms awareness from a cost center into a quantifiable risk reduction investment. Tracking phishing click rates and training completion rates improves human risk scores by 35% within a year. You need metrics demonstrating program effectiveness to leadership and guiding improvement priorities.
Track these key performance indicators:
- Phishing simulation click rates and reporting rates showing behavioral changes
- Training completion percentages indicating program reach and compliance
- Human risk scores combining multiple behavioral metrics into single indicators
- Security incident rates attributed to human error revealing real-world impact
- Time to complete security questionnaires measuring operational efficiency gains
Your human risk score combines phishing susceptibility, training compliance, policy violations, and incident involvement. This composite metric provides leadership with a single number tracking program effectiveness over time.
Report metrics monthly to maintain leadership visibility. Quarterly business reviews dive deeper into trends and improvement opportunities. Annual reports demonstrate cumulative impact and justify continued investment.
Iterate based on data rather than assumptions. If phishing simulations reveal high click rates in specific departments, deploy targeted training there. Low completion rates signal delivery method problems requiring adjustment. Use metrics to drive effective questionnaire responses and continuous program enhancement.
Expected Results and Timelines
Realistic expectations prevent disappointment and maintain leadership support. Mature programs typically reach measurable outcomes in 12-18 months with up to 40% reduction in human-related security incidents. You cannot transform security culture overnight.

Anticipate these typical milestones:
| Timeline | Expected Outcomes | Key Metrics |
|---|---|---|
| 3 Months | Baseline established, initial training deployed | 85% completion rate, baseline phishing click rate |
| 6 Months | Behavior changes emerging, metrics trending positive | 20% reduction in click rates, improved reporting |
| 12 Months | Culture shift visible, incident rates declining | 35% click rate reduction, 25% fewer incidents |
| 18 Months | Mature program operating, sustained improvements | Continued metric improvements, program self-sustaining |
Your phishing click rates should decline steadily as employees recognize and report threats. Initial simulations might see 30-40% click rates. After six months of consistent training, expect rates below 15%. Mature programs achieve single-digit click rates.
Automation tools deliver immediate efficiency gains. Security questionnaire response times drop from days to hours. Your team redirects saved time toward strategic security initiatives rather than repetitive questionnaire completion.
Sustained success requires ongoing leadership engagement and continuous program evolution. Programs plateau when teams stop innovating or leadership attention wanes. Maintain momentum through regular communication, fresh content, and demonstrated business value.
Enhance Your Security Awareness with Skypher Automation
Building an effective security awareness program requires balancing employee education with operational efficiency. Skypher's AI-powered questionnaire automation integrates seamlessly with your awareness initiatives, reducing manual questionnaire efforts by over 80% while maintaining accuracy and consistency.

Our platform connects with Slack, Microsoft Teams, and over 40 third-party risk management systems, enabling real-time collaboration and streamlined compliance workflows. Your security team spends less time on repetitive questionnaire responses and more time strengthening your awareness program. AI-driven content management ensures questionnaire answers align with your training materials, reinforcing consistent security messages. Explore best practices for questionnaire automation to enhance your program efficiency.
Frequently Asked Questions
What are the key metrics to evaluate a security awareness program?
Track phishing simulation click rates to measure threat recognition improvements. Monitor training completion percentages ensuring program reach across your organization. Calculate human risk scores combining multiple behavioral indicators into actionable metrics. Measure security incident rates attributed to human error showing real-world impact.
How can I maintain employee engagement and prevent training fatigue?
Use multi-channel delivery methods including simulations, contests, videos, and interactive exercises. Vary content formats monthly to maintain novelty and interest. Keep training sessions short, focused, and relevant to daily work activities. Regular content updates reflecting current threats prevent staleness.
What role does leadership play in security awareness success?
Leadership engagement drives resource allocation, cultural support, and employee participation. Executive sponsors maintain program visibility and champion security initiatives organization-wide. Regular metric reporting keeps leadership invested in program success and improvement priorities.
How long does it take to see measurable improvements from a security awareness program?
Typically 12 to 18 months to reach program maturity with measurable risk reductions of 30-40%. Initial behavior changes emerge within 3-6 months of consistent training. Sustained executive sponsorship and continuous program evolution accelerate progress toward maturity milestones.