Security teams at American tech firms spend up to 40 percent of their time manually handling questionnaires. This task drains resources and often delays critical risk assessments, leaving CISOs and compliance managers searching for better options. With growing pressure to protect sensitive data and work across large departments, finding smarter methods to automate these workflows means your team can respond faster and cut costly errors. Discover actionable steps for transforming how your organization tackles security questionnaires.
Table of Contents
- Step 1: Assess Current Security Questionnaire Workflows
- Step 2: Configure Core AI-Driven Automation Tools
- Step 3: Integrate With Collaboration And Risk Management Platforms
- Step 4: Calibrate Response Templates And Data Models
- Step 5: Test Security Build Accuracy And Completion
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Assess Current Workflows | Evaluate your existing security questionnaire processes to identify inefficiencies and opportunities for improvement. |
| 2. Implement AI Automation | Choose an AI platform that streamlines responses, reduces manual input, and enhances accuracy in assessments. |
| 3. Integrate Seamlessly | Ensure your automation tools connect with collaboration and risk management systems for improved data management and visibility. |
| 4. Customize Data Models | Tailor response templates and data models to accurately reflect your organization's risk landscape and compliance needs. |
| 5. Conduct Thorough Testing | Validate the AI system's accuracy and reliability through comprehensive testing protocols and feedback from security professionals. |
Step 1: Assess current security questionnaire workflows
Assessing your organization's current security questionnaire workflows is a critical first step in streamlining your response processes. This initial evaluation will help you identify inefficiencies, bottlenecks, and opportunities for significant improvement in how your team manages complex security assessments.
Start by conducting a comprehensive internal audit of your existing questionnaire management approach. Gather documentation from previous security reviews and interview team members who regularly handle these workflows. Verify the implementation of security controls by examining current processes, tracking response times, and identifying areas where manual interventions create delays. Pay special attention to how information is collected, validated, and documented across different departments. Map out the current workflow step by step, noting where handoffs occur, who is responsible for each stage, and how long each stage typically takes.
Analyze the patterns in your current security questionnaire processes. Look for repetitive tasks that could potentially be automated, communication gaps between teams, and instances where critical information gets trapped in email chains or disparate systems. Review the complexity and frequency of questionnaires your organization receives, tracking metrics like average completion time, error rates, and the number of stakeholders involved in each response.
Pro tip: Create a visual workflow diagram that captures every step of your current security questionnaire process to help your team easily identify optimization opportunities.
Here's a summary of typical challenges and optimization opportunities in current security questionnaire workflows:
| Workflow Challenge | Impact on Operations | Potential Optimization |
|---|---|---|
| Manual data collection | Slow response times | Automate information entry |
| Cross-team communication | Delays and miscommunication | Use centralized platforms |
| Email chain bottlenecks | Lost context and confusion | Implement unified dashboards |
| High error rates | Rework and compliance risk | Standardize response templates |
Step 2: Configure core AI-driven automation tools
Configuring core AI-driven automation tools represents a transformative approach to streamlining your security questionnaire response processes. This step focuses on implementing intelligent technologies that can dramatically reduce manual effort and enhance the accuracy of your security assessments.
Begin by selecting an AI-powered platform that offers robust integration capabilities. Implement web security testing protocols that allow for comprehensive vulnerability detection and automated scanning. Look for tools that can parse complex questionnaire formats, extract key information, and generate precise responses based on your organization's specific security infrastructure. Ensure the chosen solution supports advanced features like natural language processing, machine learning model training, and seamless integration with your existing risk management systems.

Carefully configure the AI automation tool by mapping your organization's unique security policies, compliance requirements, and past questionnaire response patterns. Set up custom response templates, define confidence thresholds for AI generated answers, and establish clear workflows for human review and validation. Pay close attention to configuring access controls, ensuring that sensitive information remains protected throughout the automated process. Test the system thoroughly with sample questionnaires to validate its accuracy and refine its performance iteratively.
Pro tip: Create a staged rollout strategy for your AI automation tools, starting with low complexity questionnaires to build confidence and fine tune the system before handling more intricate security assessments.
This table contrasts traditional questionnaire processes with an AI-automated approach:
| Aspect | Traditional Method | AI-Driven Automation |
|---|---|---|
| Response speed | Days to weeks | Minutes to hours |
| Error frequency | High | Significantly reduced |
| Manual workload | Extensive | Minimizes manual effort |
| Compliance tracking | Inconsistent | Consistent and auditable |
Step 3: Integrate with collaboration and risk management platforms
Successfully integrating security questionnaire automation tools with collaboration and risk management platforms transforms how your organization approaches vendor risk assessments. This critical step ensures seamless communication, centralized data management, and enhanced visibility across your security ecosystem.
Implement standardized information gathering protocols that enable smooth data exchange between your automation tools and existing risk management systems. Prioritize platforms that offer robust API connections, allowing real time synchronization of security questionnaire data, risk profiles, and assessment results. Identify key integration points such as document sharing repositories, communication channels, and centralized dashboards where stakeholders can access and collaborate on security assessments.
Carefully configure your integration settings to maintain granular access controls and ensure sensitive information remains protected. Map out specific workflows that define how questionnaire responses will be routed, reviewed, and archived across different platforms. Test each integration thoroughly to validate data accuracy, validate authentication mechanisms, and confirm that information flows seamlessly between your AI automation tools and existing risk management infrastructure. Pay special attention to creating automated notifications and escalation paths that keep relevant team members informed about questionnaire progress and potential security risks.
Pro tip: Create a detailed integration mapping document that outlines every connection point, authentication method, and data flow between your security questionnaire automation platform and collaboration tools.
Step 4: Calibrate response templates and data models
Calibrating response templates and data models is a critical process that transforms your security questionnaire automation from generic to precisely tailored for your organization's unique risk landscape. This step involves fine tuning your AI systems to generate accurate, contextually relevant responses that reflect your specific security posture and compliance requirements.
Develop comprehensive risk assessment frameworks that allow your automation tools to understand and respond to nuanced security questions with unprecedented precision. Begin by analyzing historical questionnaire responses, identifying patterns in your organization's risk management approach, and creating machine learning training datasets that capture the subtleties of your security protocols. Map out detailed response templates that can dynamically adjust based on question context, organizational structure, and specific compliance standards relevant to your industry.
Iteratively refine your data models by conducting systematic reviews of AI generated responses. Establish a feedback loop where security professionals can validate, modify, and enhance template outputs, gradually improving the system's accuracy and reliability. Implement version control mechanisms that track changes to response templates, allowing you to maintain an audit trail of how your questionnaire automation evolves over time. Pay special attention to creating flexible templates that can accommodate diverse questionnaire formats while maintaining consistent, high quality responses across different vendor assessment frameworks.
Pro tip: Create a quarterly calibration ritual where your security and AI teams collaboratively review and update response templates to ensure they remain aligned with your organization's changing risk landscape.
Step 5: Test security build accuracy and completion
Testing security build accuracy and completion represents the critical validation phase where you confirm your questionnaire automation system performs precisely as intended. This comprehensive assessment ensures that your AI powered solution delivers consistent, reliable, and comprehensive security responses across diverse scenarios.
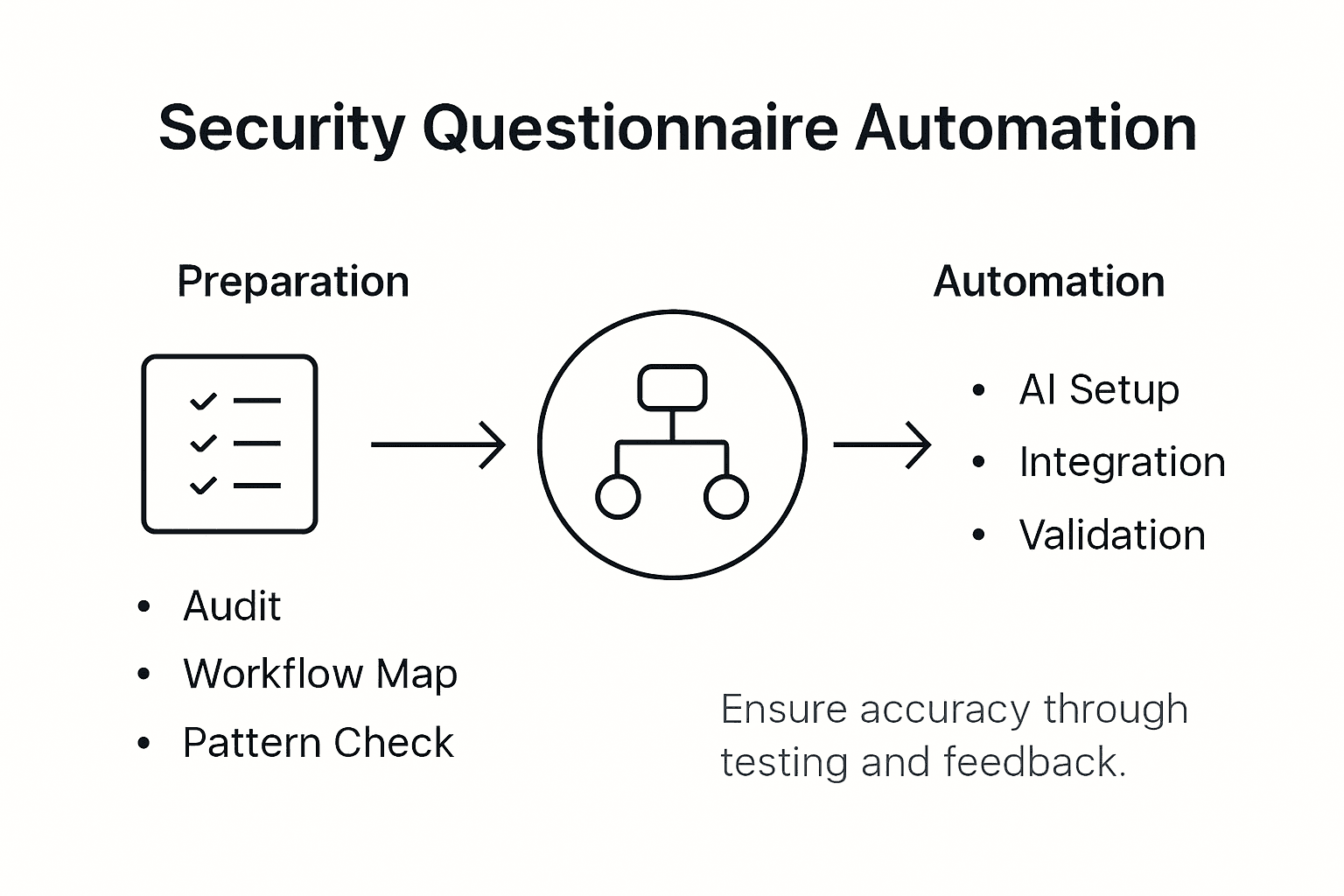
Implement systematic security control assessment procedures that methodically evaluate every aspect of your automation platform. Develop a rigorous testing framework that includes multiple verification stages: synthetic questionnaire testing, edge case scenario analysis, cross validation with manual expert reviews, and performance benchmarking. Design test scenarios that simulate complex security questionnaires from different industries, challenging your system to generate accurate, nuanced responses under varied conditions. Focus on evaluating the AI models contextual understanding, response consistency, and ability to adapt to subtle variations in question formatting and content.
Execute comprehensive validation protocols that go beyond surface level testing. Create a structured feedback mechanism where security professionals can continuously review and score AI generated responses, providing granular insights into system performance. Implement quantitative metrics that track response accuracy, completeness, compliance alignment, and contextual relevance. Pay special attention to identifying potential blind spots or recurring patterns of uncertainty in your automation system, using these insights to continuously refine your machine learning models and response templates.
Pro tip: Establish a dedicated testing environment that allows you to simulate real world security questionnaire scenarios without risking production data integrity.
Transform Your Security Questionnaire Process with Skypher
The challenge of streamlining and automating complex security questionnaire workflows, as outlined in the Security Build Guide for Streamlined Questionnaire Automation, is a critical concern for many organizations. Common pain points like slow response times, manual data collection, communication delays, and the need for precise AI-driven automation are all addressed by Skypher's advanced SaaS platform. By leveraging Skypher's AI Questionnaire Automation Tool, your team can reduce hours or days of work to minutes with industry-leading accuracy and reliability.
Skypher supports over 30 API integrations with popular risk management platforms such as ServiceNow and OneTrust while enabling seamless collaboration through Slack and Microsoft Teams. The platform’s custom Trust Center and real-time integration features provide a centralized, secure environment for managing sensitive responses, helping you avoid email bottlenecks and manual errors. Designed specifically for medium to large organizations in tech and finance sectors, Skypher empowers you to accelerate proof of concepts and contract negotiations by delivering trusted, efficient security reviews.
Experience the impact of tailored AI-powered automation that transforms your questionnaire responses with precision and speed.

Explore how you can elevate your security questionnaire workflows today by visiting Skypher's landing page. Discover the full potential of AI-driven automation tools, real-time collaboration, and seamless integrations at Skypher. Take the first step toward conquering your security assessment challenges now.
Frequently Asked Questions
How can I assess my current security questionnaire workflows?
Start by conducting a thorough internal audit of your existing processes. Gather documentation and interview team members to identify inefficiencies and areas for improvement, such as response times and manual interventions.
What are the steps to configure AI-driven automation tools for security questionnaires?
Begin by selecting an AI platform that integrates well with your current systems. Map your organization's security policies and compliance requirements, and test the system with sample questionnaires to ensure accuracy and effectiveness of automation.
How do I integrate security questionnaire automation tools with collaboration platforms?
Implement standardized information-gathering protocols that enable data exchange with your risk management systems. Focus on setting up API connections for real-time updates and maintaining access controls to protect sensitive information.
What should I consider when calibrating response templates and data models?
Analyze historical responses to create tailored response templates that reflect your unique security landscape. Establish a feedback loop for continuous improvement and track changes with version control to adapt to evolving security requirements.
How can I test the accuracy and completion of my security build automation?
Create a rigorous testing framework that includes synthetic tests and expert reviews to evaluate your automation's performance. Continuously collect feedback and track metrics to ensure responses are accurate and compliant, refining your models as needed.