Every organization wants to feel protected, which is why security surveys have become a top priority in 2025. Here is a shocker though. Researchers cracked passwords for 16 percent of user accounts in just 90 minutes, and 4.75 percent used the word 'password' as their password. Everyone talks about software updates and firewalls, but it turns out the biggest threats often hide in plain sight, from everyday habits to overlooked compliance gaps.
Table of Contents
- What Are Security Surveys And Why They Matter
- Key Steps In Conducting Effective Security Surveys
- Common Risks Identified By Security Surveys
- Best Practices And Tools For Security Surveys In 2025
Quick Summary
| Takeaway | Explanation |
|---|---|
| Security surveys are essential for risk management. | They provide organizations with a comprehensive assessment of vulnerabilities, ensuring proactive measures against potential threats. |
| Follow a structured process for effective surveys. | Preparation, data collection, and strategic reporting are crucial steps that yield actionable insights for enhancing security frameworks. |
| Address technological, human, and regulatory risks. | Identify and mitigate vulnerabilities in digital systems, employee behaviors, and compliance protocols for a holistic risk management approach. |
| Utilize advanced tools for better assessments. | Leverage AI and machine learning technologies to enhance the accuracy and efficiency of security surveys in an evolving landscape. |
| View security surveys as ongoing processes. | Continuous assessment and improvement are vital in adapting to emerging threats and maintaining a robust security posture. |
What Are Security Surveys and Why They Matter
Security surveys represent a critical proactive approach for organizations to assess and strengthen their overall security infrastructure. These comprehensive evaluations systematically examine an organization's security protocols, potential vulnerabilities, and risk management strategies across multiple dimensions.
Understanding the Core Purpose of Security Surveys
At their fundamental level, security surveys are structured diagnostic tools designed to provide a holistic view of an organization's security posture. Our guide on security questionnaires reveals that these assessments go far beyond simple checklists. They are sophisticated diagnostic instruments that help organizations identify potential weaknesses before they can be exploited by malicious actors.
The Centers for Disease Control and Prevention emphasizes that security surveys are not just optional exercises but essential components of comprehensive risk management. These evaluations enable organizations to systematically analyze their current security measures, revealing potential gaps that might otherwise remain undetected.
Key Components and Scope of Security Surveys
Security surveys typically encompass multiple critical areas of organizational protection. These include physical security infrastructure, digital network protection, employee access protocols, data management practices, and incident response capabilities. Organizations conduct these surveys to gain a 360-degree understanding of their security ecosystem.
The process involves detailed assessments that might include:
- Infrastructure Analysis: Evaluating physical and digital security systems
- Risk Assessment: Identifying potential vulnerabilities and threat vectors
- Compliance Verification: Ensuring alignment with industry-specific security standards
By conducting thorough security surveys, organizations can develop targeted strategies to mitigate risks, enhance protective measures, and create more resilient security frameworks. These surveys are not just about identifying problems but about constructing proactive, adaptive security approaches that can evolve with emerging technological challenges.
Moreover, security surveys serve multiple strategic purposes. They provide leadership with clear, actionable insights into an organization's security readiness, enable informed decision-making, and demonstrate a commitment to comprehensive risk management. In an era of increasingly sophisticated cyber threats, these surveys are no longer optional but essential survival tools for modern enterprises.
Key Steps in Conducting Effective Security Surveys
Conducting a comprehensive security survey requires a strategic and methodical approach that goes beyond simple checklist completion. Organizations must implement a structured process that ensures thorough examination and meaningful insights into their security infrastructure.
Preparation and Initial Assessment
Before launching a security survey, organizations need to establish clear objectives and scope. Learn more about navigating security questionnaire challenges to understand the foundational groundwork required. This initial phase involves defining specific goals, identifying key stakeholders, and determining the breadth of the assessment.
The preparation stage typically includes:
- Stakeholder Identification: Engaging representatives from IT, security, legal, and operational departments
- Resource Allocation: Determining necessary personnel, tools, and budget for the survey
- Scope Definition: Outlining specific areas of examination including digital systems, physical infrastructure, and operational protocols
Comprehensive Data Collection and Analysis
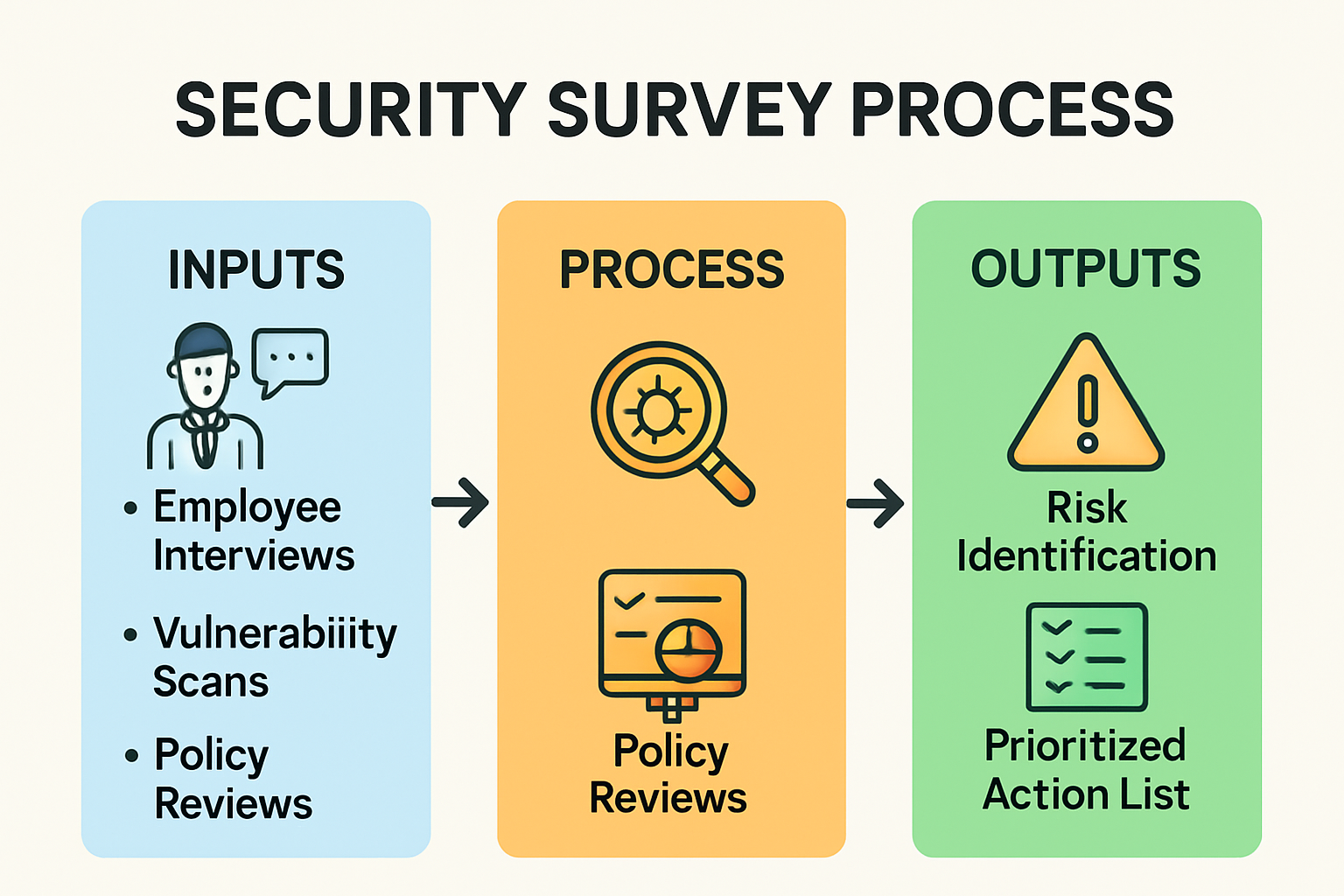 Data collection represents the most critical phase of security surveys. Organizations must employ multiple methodologies to gather comprehensive information. This includes technical assessments, document reviews, interviews with key personnel, and systematic vulnerability scanning.
Data collection represents the most critical phase of security surveys. Organizations must employ multiple methodologies to gather comprehensive information. This includes technical assessments, document reviews, interviews with key personnel, and systematic vulnerability scanning.
Effective data collection strategies involve:
- Utilizing advanced scanning tools to identify network vulnerabilities
- Conducting in-depth interviews with security personnel
- Reviewing existing security documentation and incident reports
- Performing simulated security scenarios to test response mechanisms
Advanced organizations increasingly leverage AI-powered tools to enhance the precision and depth of their security survey processes. These technologies can rapidly analyze complex datasets, identifying potential risks that might escape traditional manual review methods.
Reporting and Strategic Implementation
The final stage of a security survey focuses on transforming collected data into actionable strategic recommendations. This phase requires creating detailed reports that not only highlight vulnerabilities but also provide clear, prioritized remediation strategies.
Key reporting components should include:
- Comprehensive vulnerability mapping
- Risk prioritization based on potential impact
- Specific, implementable recommendations
- Timeline for addressing critical security gaps
Successful security surveys are not one-time events but part of an ongoing, dynamic risk management strategy. Organizations must view these assessments as continuous improvement processes, regularly updating their approaches to match evolving technological landscapes and emerging threat vectors.
By following these structured steps, organizations can transform security surveys from routine compliance exercises into powerful strategic tools that genuinely enhance their overall security posture and organizational resilience.
Below is a table summarizing the key steps involved in conducting an effective security survey, including the primary tasks and objectives at each phase.
| Step | Primary Tasks | Main Objective |
|---|---|---|
| Preparation & Initial Assessment | Stakeholder identification, resource allocation, scope definition | Establish clear goals & survey boundaries |
| Data Collection & Analysis | Technical assessments, interviews, document reviews, vulnerability scanning, scenario simulation | Gather & analyze comprehensive security data |
| Reporting & Strategic Implementation | Vulnerability mapping, risk prioritization, recommendations, timeline creation | Provide actionable insights & prioritize remediation |
Common Risks Identified by Security Surveys
Security surveys consistently unveil a complex landscape of organizational vulnerabilities that can compromise an entity's overall security infrastructure. Understanding these common risks is crucial for developing targeted mitigation strategies and preventing potential breaches.
Technological Vulnerabilities and Digital Exposure
Our guide on security questionnaire challenges highlights the evolving nature of technological risks. Digital systems represent a significant area of vulnerability for most organizations. According to EDUCAUSE research, the top technological risks include phishing, social engineering, and inadequate end-user awareness.
Key technological vulnerabilities frequently discovered during security surveys involve:
- Outdated Software: Unpatched systems that remain exposed to known security exploits
- Weak Authentication Mechanisms: Insufficient password protocols and lack of multifactor authentication
- Network Configuration Weaknesses: Improperly secured network entry points
Human Factor and Organizational Cultural Risks
A systematic review of cybersecurity risks emphasizes that human behavior represents a critical vulnerability often overlooked in traditional security assessments. Organizations frequently discover significant risks stemming from employee behaviors and organizational culture.
Human-related security risks typically include:
- Limited security awareness among staff
- Inadequate training on cybersecurity best practices
- Poor password management and credential handling
- Insufficient understanding of potential social engineering tactics
The U.S. Department of the Interior's Office of Inspector General revealed startling insights into human-related security weaknesses. In their investigation, they found that 4.75 percent of active user account passwords were based on the word 'password'. Within just 90 minutes of testing, researchers cracked passwords for 16 percent of user accounts.
To illustrate the statistics about password vulnerabilities and human factor risks identified by recent security surveys, see the table below.
| Statistic | Value | Source |
|---|---|---|
| Accounts with 'password' as password | 4.75% | DOI Office of Inspector General |
| User accounts cracked in 90 minutes | 16% | DOI Office of Inspector General |
| Common causes of human-factor breaches | Weak passwords, limited awareness, poor training | Article Summary/EDUCAUSE/MDPI evidence |
Compliance and Regulatory Exposure
Security surveys frequently uncover significant compliance and regulatory risks that can have substantial legal and financial implications. These risks extend beyond technological vulnerabilities and touch on broader organizational governance.
Common compliance-related risks include:
- Incomplete or outdated security documentation
- Failure to meet industry-specific regulatory requirements
- Inadequate data protection and privacy protocols
- Insufficient incident response and reporting mechanisms
The complexity of these risks underscores the importance of comprehensive security surveys. Organizations must adopt a holistic approach that addresses technological, human, and regulatory dimensions of security. By systematically identifying and addressing these risks, entities can build more resilient and adaptive security frameworks that protect against evolving threats.
Best Practices and Tools for Security Surveys in 2025
As cybersecurity landscapes continue to evolve, organizations must adopt sophisticated approaches to conducting security surveys. The year 2025 demands innovative strategies and cutting-edge tools that can provide comprehensive, actionable insights into an organization's security posture.
Strategic Frameworks and Methodological Approaches
Learn how to navigate complex security questionnaires to understand the foundational principles of modern security survey design. The Cloud Security Alliance highlights the critical need for integrated, holistic approaches that go beyond traditional checklist-based assessments.
Key strategic best practices for 2025 include:
- Comprehensive Risk Integration: Combining technological, human, and regulatory risk assessments
- Continuous Assessment Models: Moving from point-in-time surveys to ongoing, dynamic evaluation processes
- Cross-Functional Collaboration: Ensuring involvement from IT, security, legal, and operational teams
The AssessITS research introduces advanced methodological guidelines that draw from multiple international standards, including NIST 800-30 Rev 1, COBIT 5, and ISO 31000. This approach provides a systematic method for identifying, analyzing, and mitigating IT risks with unprecedented precision.
Advanced Tools and Technology Solutions
Technology has transformed security survey methodologies. Organizations now have access to sophisticated tools that leverage artificial intelligence, machine learning, and comprehensive data analysis techniques. These tools enable more nuanced, real-time security assessments that can quickly identify and prioritize potential vulnerabilities.
Emerging tools in 2025 typically feature:
- AI-Powered Risk Assessment: Automated systems that can predict and analyze potential security risks
- Integrated Security Culture Platforms: Tools that assess both technological and human-factor security risks
- Real-Time Vulnerability Mapping: Dynamic systems that provide continuous security insights
The UK's National Protective Security Authority offers an innovative Security Culture Tool that exemplifies the next generation of survey technologies. This free, online platform provides interactive workshops and comprehensive workforce surveys that analyze security culture from multiple perspectives.
Implementation and Continuous Improvement
 Successful security surveys in 2025 are characterized by their ability to adapt and evolve. Organizations must view these assessments as dynamic processes rather than static compliance exercises. This means developing flexible frameworks that can quickly respond to emerging threats and technological changes.
Successful security surveys in 2025 are characterized by their ability to adapt and evolve. Organizations must view these assessments as dynamic processes rather than static compliance exercises. This means developing flexible frameworks that can quickly respond to emerging threats and technological changes.
Key implementation strategies include:
- Regular technology and methodology updates
- Comprehensive staff training and awareness programs
- Flexible, scalable assessment frameworks
- Integration of qualitative and quantitative assessment methods
By embracing these advanced approaches, organizations can transform security surveys from routine compliance tasks into strategic tools for comprehensive risk management. The most successful entities will be those that view security not as a destination, but as a continuous journey of improvement and adaptation.
Frequently Asked Questions
What is a security survey?
A security survey is a comprehensive assessment tool used by organizations to evaluate their security protocols, identify vulnerabilities, and enhance their risk management strategies.
Why are security surveys important?
Security surveys help organizations proactively identify and mitigate risks, ensuring stronger security measures are implemented and protecting against potential threats.
What are the key components of a security survey?
Key components of a security survey include infrastructure analysis, risk assessment, and compliance verification, providing a holistic view of an organization's security posture.
How often should organizations conduct security surveys?
Organizations should treat security surveys as ongoing processes, regularly updating their assessments to adapt to emerging threats and technological changes.
Turn Security Surveys Into a Competitive Advantage
Are security surveys overwhelming your team or delaying your deals? The article highlights how rising compliance demands, human errors, and slow response times are leaving organizations exposed. With data showing that 16 percent of user accounts can be cracked in minutes, you cannot afford to overlook gaps in security assessments or let manual questionnaire work slow you down.

Imagine managing your next security survey with confidence and speed. Skypher automates security questionnaire responses, integrates with over 40 risk platforms, and gives your team real-time collaboration tools. Reduce bottlenecks, boost accuracy, and build trust with every assessment. Take control of your security reviews and streamline your compliance process now. Visit Skypher's main site to see how our AI-powered platform turns a security challenge into your organization’s strength.
Recommended
- The ever growing number of security questionnaires and what you and your company can do to face it
- The different formats & mistakes made when writing or answering security questionnaires
- Guides - Saasy - Webflow HTML Website Template
- Blog - Skypher
- GDPR Compliant Testing in 2025: No Cookies, No Problems
- Data Privacy Best Practices for Small Businesses in 2025 - Loft Legal
