Most American companies know that failing a compliance audit can cost millions and erode hard-earned trust. In a digital age where data privacy and financial transparency are under scrutiny, understanding the difference between SOC 1 and SOC 2 is no longer optional. This guide breaks down the unique roles of these two attestation reports and reveals why choosing the right framework can protect both your reputation and your bottom line.
Table of Contents
- SOC 1 And SOC 2 Explained Clearly
- Key Differences Between SOC 1 And SOC 2
- Essential Reporting Elements And Frameworks
- Compliance Requirements And Audit Process
- Risks, Liabilities, And Common Pitfalls
Key Takeaways
| Point | Details |
|---|---|
| Purpose of SOC Reports | SOC 1 focuses on financial reporting controls, while SOC 2 assesses security and operational controls. |
| Audience Distinction | SOC 1 is primarily for auditors and financial institutions, whereas SOC 2 targets tech firms and cloud providers. |
| Reporting Types | SOC Type I evaluates control design at a specific time, and SOC Type II examines effectiveness over 6-12 months. |
| Compliance Strategy | Developing a proactive documentation and compliance strategy enhances control monitoring and minimizes audit issues. |
SOC 1 and SOC 2 Explained Clearly
Service Organization Control (SOC) reports are critical frameworks used by companies to validate their internal control systems and demonstrate trust to potential clients and stakeholders. SOC 1 and SOC 2 are two distinct types of attestation reports that serve different purposes in assessing organizational controls and security practices.
SOC 1 reports specifically focus on financial reporting controls, evaluating controls that might impact a service organization's client financial statements. These reports are typically used by accounting firms, financial service providers, and organizations whose services directly influence their clients' financial reporting processes. Designed under the American Institute of Certified Public Accountants (AICPA) guidelines, SOC 1 reports help ensure that a service organization maintains robust internal controls.
In contrast, SOC 2 reports assess controls related to security, availability, processing integrity, confidentiality, and privacy. These reports are particularly crucial for technology companies, cloud service providers, and organizations handling sensitive customer data. SOC 2 helps verify that a company has implemented appropriate security protocols and maintains high standards of data protection. Unlike SOC 1, which centers on financial mechanisms, SOC 2 provides a comprehensive evaluation of an organization's operational and security practices.
Pro Tip: Strategic Compliance Approach: When preparing for SOC audits, develop a comprehensive documentation system that tracks your control implementations and can easily demonstrate your compliance across multiple Trust Services Criteria.
Key Differences Between SOC 1 and SOC 2
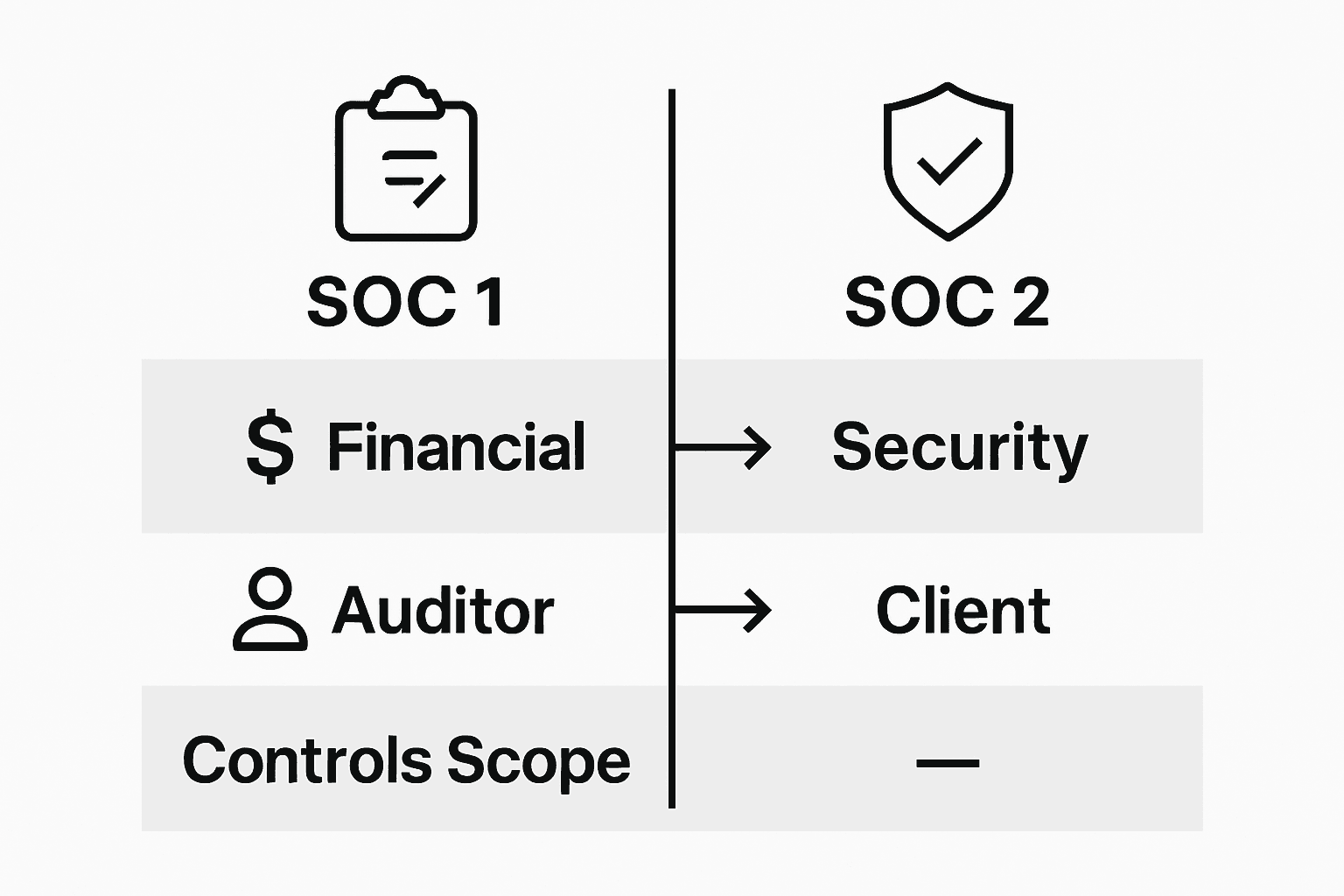
While both SOC 1 and SOC 2 reports are critical compliance frameworks, they serve distinctly different purposes in organizational control assessment. The primary audience and focus of these reports fundamentally differ in their scope and intent.
SOC 1 Reports are specifically tailored for financial reporting controls, primarily targeting external auditors who need to understand how a service organization's internal controls might impact financial statements. These reports are deeply rooted in the Sarbanes-Oxley Act requirements and are crucial for accounting firms, financial service providers, and organizations whose services directly influence client financial reporting processes.
SOC 2 Reports, by contrast, provide a comprehensive assessment of an organization's operational controls related to security, availability, processing integrity, confidentiality, and privacy. These reports are designed to address the growing need for rigorous data protection and operational due diligence. Unlike SOC 1, SOC 2 reports are typically sought by technology companies, cloud service providers, and organizations handling sensitive customer data, with a primary focus on demonstrating robust security practices and data protection mechanisms.
The key distinctions extend beyond their focus: SOC 1 is narrowly centered on financial reporting controls, while SOC 2 offers a broader evaluation of an organization's overall security and operational practices. This means companies in different industries will prioritize different SOC reports based on their specific compliance and risk management needs.
Here's a side-by-side look at the distinct features and impacts of SOC 1 and SOC 2:
| Aspect | SOC 1 | SOC 2 |
|---|---|---|
| Primary Focus | Financial reporting controls | Security and operational controls |
| Typical Audience | Auditors, financial institutions | Tech firms, cloud providers |
| Regulatory Driver | Sarbanes-Oxley Act | Trust Services Criteria |
| Most Common Use Case | Client financial statement audits | Data protection, privacy reviews |
Pro Tip: Strategic Compliance Selection: Carefully assess your organization's primary risk areas and regulatory requirements to determine whether SOC 1, SOC 2, or potentially both types of reports will provide the most comprehensive assurance for your stakeholders.
Essential Reporting Elements and Frameworks
SOC Reports represent critical frameworks for organizational control assessment, with each type following specific structural guidelines designed to provide comprehensive insights into an organization's operational and security practices. These reports are meticulously structured to offer detailed evaluations of control environments.
Specifically for SOC 2 reports, the framework is built around five core Trust Services Criteria (TSC), which serve as the foundational elements for comprehensive security assessments. The Trust Services Criteria include security, availability, processing integrity, confidentiality, and privacy, with security being the mandatory criterion. Organizations have the flexibility to select additional criteria based on their specific service offerings and industry requirements.
The reporting process involves a detailed examination of an organization's control mechanisms, with auditors providing an independent opinion on the effectiveness of these controls. This systematic approach ensures that stakeholders receive a transparent and comprehensive view of an organization's risk management and security practices. The reports typically include a description of the organization's systems, the auditor's tests of controls, and a detailed evaluation of how well those controls meet the specified criteria.
Each SOC report type follows a distinct methodology, with SOC 1 focusing on financial reporting controls and SOC 2 providing a broader assessment of operational and security controls. The choice between these reports depends on an organization's specific compliance needs, industry regulations, and the expectations of its stakeholders.
Pro Tip: Strategic Reporting Preparation: Develop a comprehensive documentation strategy that proactively tracks your organizational controls, ensuring you can seamlessly demonstrate compliance across multiple Trust Services Criteria when audit time arrives.
Compliance Requirements and Audit Process
SOC Compliance is a rigorous framework that requires organizations to demonstrate their commitment to robust internal controls and security practices. The audit process involves comprehensive evaluations of an organization's control mechanisms across different regulatory landscapes.

The SOC audit process is strategically designed with two primary report types: SOC 1 and SOC 2. SOC 1 reports are primarily driven by Sarbanes-Oxley Act requirements, focusing on financial reporting controls for publicly traded companies. In contrast, SOC 2 reports address broader operational controls, particularly in data protection and privacy domains. These audits meticulously assess an organization's controls against specific Trust Services Criteria, evaluating both design and operational effectiveness.
Two distinct assessment approaches characterize SOC reporting: Type I and Type II reports. Type I reports evaluate the design of control systems at a specific point in time, providing a snapshot of an organization's control framework. Type II reports offer a more comprehensive analysis, examining the operational effectiveness of these controls over an extended period, typically six to twelve months. This approach allows stakeholders to gain deeper insights into an organization's consistent performance and risk management capabilities.
Below are the main differences between SOC Type I and Type II reports:
| Report Type | What It Examines | Timeframe Covered | Business Value |
|---|---|---|---|
| SOC Type I | Design of controls | Single point in time | Quick assurance, entry-level |
| SOC Type II | Design + effectiveness | 6-12 months | Ongoing assurance, higher trust |
For organizations navigating complex regulatory environments, SOC audits serve as critical validation mechanisms. They demonstrate compliance with industry standards, validate internal control effectiveness, and provide transparency to clients, investors, and regulatory bodies. The specific compliance requirements vary depending on the industry, with healthcare organizations often needing to address HIPAA regulations, while financial services might focus on Sarbanes-Oxley or GDPR compliance requirements.
Pro Tip: Strategic Audit Preparation: Develop a proactive documentation strategy that continuously monitors and updates your control mechanisms, ensuring you can seamlessly demonstrate compliance and minimize potential audit friction.
Risks, Liabilities, and Common Pitfalls
SOC Compliance represents a critical strategic endeavor where organizations must navigate complex regulatory landscapes and potential operational risks. Failing to obtain the appropriate SOC report can trigger significant legal and reputational consequences, making comprehensive understanding essential for leadership teams.
Compliance Risks emerge from multiple dimensions, with the most critical challenges stemming from inadequate documentation and insufficient control monitoring. Organizations frequently encounter audit findings related to incomplete Trust Services Criteria assessments, which can substantially impact client relationships and organizational credibility. These risks are particularly pronounced in technology and financial service sectors, where data protection and financial reporting controls are stringently evaluated.
The potential liabilities extend beyond immediate audit outcomes. Organizations might face substantial financial penalties, contractual breaches, and erosion of stakeholder trust if they cannot demonstrate robust control mechanisms. Specific risks include losing critical business contracts, experiencing regulatory sanctions, and potentially facing legal actions from clients or regulatory bodies who discover control vulnerabilities.
Some common pitfalls organizations encounter include inconsistent documentation practices, inadequate risk assessment frameworks, and failure to continuously update control mechanisms. Technology firms, cloud service providers, and financial institutions must invest significant effort in maintaining comprehensive, current documentation that reflects their evolving operational landscape. The most successful organizations treat SOC compliance as a continuous improvement process rather than a periodic checkbox exercise.
Pro Tip: Proactive Risk Management: Develop a dynamic compliance strategy that treats SOC reporting as an ongoing organizational capability, not just an annual audit requirement, by implementing continuous monitoring and iterative control refinement.
Simplify Your SOC Compliance with Skypher's AI-Driven Solutions
Navigating SOC 1 and SOC 2 audits demands thorough documentation, continuous control monitoring, and swift responses to complex security questionnaires. These challenges often slow down compliance efforts and risk audit delays or costly mistakes. Skypher offers a powerful answer to these pain points with its AI Questionnaire Automation Tool. Designed specifically for tech and finance organizations, Skypher accelerates your security review process by automating lengthy questionnaires and integrating seamlessly with over 40 third-party risk management platforms.

Don’t let SOC compliance become a bottleneck. Empower your teams with advanced features like real-time collaboration, customizable Trust Centers, and multilingual support that ensure accuracy and speed in every submission. Ready to transform your security assurance process and build stronger client trust? Discover how Skypher can streamline your SOC audits today by visiting our platform and elevating your compliance strategy with technology designed for your toughest regulatory hurdles.
Frequently Asked Questions
What is the primary difference between SOC 1 and SOC 2 reports?
SOC 1 reports focus on financial reporting controls, while SOC 2 reports assess controls related to security, availability, processing integrity, confidentiality, and privacy, making them suitable for different types of organizations.
Who typically uses SOC 1 and SOC 2 reports?
SOC 1 reports are mainly used by auditors and financial institutions, while SOC 2 reports are sought after by technology firms, cloud service providers, and organizations handling sensitive customer data.
What are the Trust Services Criteria for SOC 2 reports?
The Trust Services Criteria for SOC 2 include security, availability, processing integrity, confidentiality, and privacy, with security being the mandatory criterion for evaluation.
What are the risks of not obtaining a SOC report?
Failing to obtain a SOC report can lead to significant legal and reputational consequences, including financial penalties, loss of client trust, and potential regulatory sanctions.
Recommended
- Complete Guide to SOC Type II Reports
- Understanding SOC II Type 1: What You Need to Know
- Understanding SOC 2 AICPA: Your Guide to Compliance
- Understanding SOC 1 Compliance: Key Concepts Explained
- Complete Guide to Ecommerce Security Basics – Shopify Experts: Grow Your eCommerce Revenue
- SOC 2 compliance checklist: 10 essential controls - Heights Consulting Group