SOC reports set the gold standard for proving your company's trustworthiness, but many decision makers get tangled up over which one their business actually needs. Surprisingly, nearly 70 percent of organizations confuse the purpose and audience of SOC 1, SOC 2, and SOC 3 reports. Instead of guessing, the smart move is to look at how these reports have totally different scopes, with each serving a unique compliance and communication goal you might not expect.
Table of Contents
- What Are Soc 1, Soc 2, And Soc 3 Reports?
- Main Differences Between Soc 1, Soc 2, And Soc 3
- Choosing The Right Soc Report For Your Business
- Latest Soc Compliance Trends For 2025
Quick Summary
| Takeaway | Explanation |
|---|---|
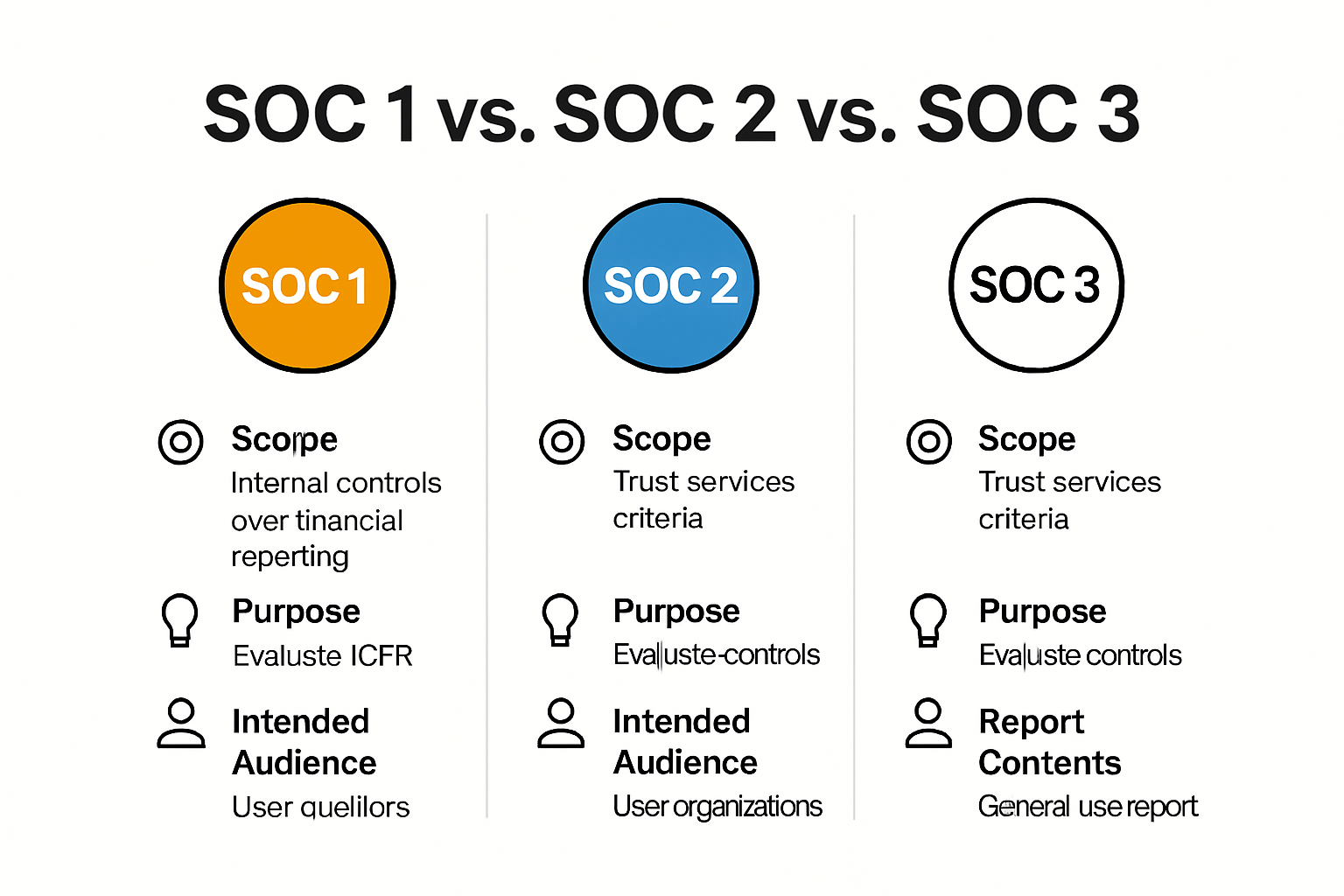
| Understand the Different SOC Reports | SOC 1 focuses on financial reporting controls, SOC 2 assesses security and privacy across five key criteria, and SOC 3 provides public-facing assurance without technical details. |
| Choose the Right SOC Report for Your Business | Select SOC 1 for financial services, SOC 2 for technology and cloud services to meet compliance and communication needs effectively. |
| Stay Updated on SOC Compliance Trends | In 2025, organizations should integrate AI for compliance automation and use blockchain for enhanced verification of SOC reports to maintain operational efficiency and trust. |
What Are SOC 1, SOC 2, and SOC 3 Reports?
Service Organization Control (SOC) reports represent critical compliance and security documentation that organizations use to demonstrate their commitment to data protection and operational integrity. These reports provide comprehensive insights into an organization's internal controls, security practices, and risk management strategies.
Understanding the SOC Report Framework
SOC reports are standardized assessment frameworks developed by the American Institute of Certified Public Accountants (AICPA) to help organizations validate their operational controls and security mechanisms. Each type of SOC report serves a unique purpose and targets different aspects of organizational performance and risk management.
SOC 1 Reports: Financial Reporting Controls
SOC 1 reports specifically focus on internal controls related to financial reporting. According to the Journal of Accountancy, these reports evaluate the effectiveness of controls that impact an organization's financial statements. Service organizations that process financial transactions or manage financial data typically require SOC 1 reports to demonstrate the reliability and accuracy of their financial control environments.
SOC 2 Reports: Security and Privacy Assurance
Research from AICPA reveals that SOC 2 reports assess an organization's controls across five key Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. These reports provide a comprehensive evaluation of an organization's ability to protect customer data and maintain robust information security practices. Unlike SOC 1 reports, SOC 2 reports are broader in scope and address critical technological and operational controls.
Differentiating SOC Report Types

SOC 3 Reports: Public-Facing Assurance
SOC 3 reports offer a more generalized and publicly accessible summary of an organization's security controls. Cybersecurity experts from ISACA explain that these reports provide high-level assurance without disclosing specific technical details. Organizations can freely distribute SOC 3 reports to demonstrate their commitment to security and build trust with potential clients and stakeholders.
The distinctions between SOC 1, SOC 2, and SOC 3 reports enable organizations to communicate their control environments effectively. While SOC 1 focuses on financial reporting, SOC 2 addresses broader security and privacy concerns, and SOC 3 offers a public-friendly overview of an organization's control mechanisms.
Companies across various industries leverage these reports to validate their operational excellence, build customer confidence, and demonstrate compliance with rigorous security standards. By understanding the nuanced differences between SOC reports, organizations can strategically select the most appropriate assessment framework to showcase their commitment to robust risk management and data protection practices.
To help you quickly compare the main features, audience, and focus of each report type, the following table summarizes the key differences between SOC 1, SOC 2, and SOC 3 reports:
| SOC Report Type | Main Focus | Intended Audience | Key Characteristics |
|---|---|---|---|
| SOC 1 | Financial reporting controls | Clients and auditors | Evaluates internal controls affecting financial statements; includes Type I (design) and Type II (operational effectiveness) |
| SOC 2 | Security, privacy, availability, processing integrity, confidentiality | Management, clients, regulators | Assesses controls across 5 Trust Services Criteria; detailed and technical; may be Type I or II |
| SOC 3 | Public trust and general information security | General public | Publicly distributable; high-level summary; no technical/confidential details |
Main Differences Between SOC 1, SOC 2, and SOC 3
While SOC 1, SOC 2, and SOC 3 reports are all part of the Service Organization Control framework, they serve distinct purposes and target different organizational needs. Understanding their unique characteristics helps organizations select the most appropriate report for their specific compliance and communication requirements.
Scope and Purpose of Each SOC Report
SOC 1 Report Characteristics
According to the AICPA, SOC 1 reports exclusively focus on financial reporting controls. These reports are critical for service organizations that directly impact their clients' financial statements. The primary objective is to provide assurance about the design and effectiveness of internal controls related to financial processing and reporting mechanisms.
Financial institutions, payroll processors, and investment management firms frequently utilize SOC 1 reports to demonstrate the reliability of their financial control environments. Research from Deloitte indicates that SOC 1 reports are typically divided into two types: Type I, which assesses control design at a specific point in time, and Type II, which evaluates the operational effectiveness of controls over a defined period.
SOC 2 Report Comprehensive Security Assessment
SOC 2 reports represent a more holistic approach to organizational control evaluation. Cybersecurity experts from ISACA explain that these reports assess controls across five critical Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Unlike SOC 1 reports, SOC 2 reports provide a broader perspective on an organization's technological and operational security practices.
Distribution and Accessibility
Report Visibility and Intended Audience
The key differentiator among SOC reports lies in their distribution and intended audience. SOC 1 and SOC 2 reports are typically restricted documents, shared only with specific stakeholders, clients, and internal management. In contrast, cybersecurity compliance experts note that SOC 3 reports are designed for public distribution, offering a generalized overview of an organization's security controls without revealing sensitive technical details.
SOC 3 reports serve as a marketing and trust-building tool, allowing organizations to demonstrate their commitment to robust security practices without compromising confidential information. These reports provide a high-level assurance that can be freely shared with potential clients, partners, and the general public.
The strategic selection of SOC reports depends on an organization's specific compliance needs, industry requirements, and communication objectives. By understanding the nuanced differences between SOC 1, SOC 2, and SOC 3 reports, organizations can effectively communicate their control environments, build trust with stakeholders, and demonstrate their commitment to operational excellence and security standards.
Choosing the Right SOC Report for Your Business
Selecting the appropriate SOC report is a strategic decision that requires careful consideration of your organization's industry, operational requirements, and stakeholder expectations. Understanding the nuanced differences between SOC 1, SOC 2, and SOC 3 reports helps businesses make informed choices about their compliance and communication strategies.
Industry-Specific Considerations
Financial Services and Accounting Sectors
Research from Deloitte indicates that organizations in financial services should prioritize SOC 1 reports. These reports are critical for companies processing financial transactions, managing payroll, or providing investment services. Banks, accounting firms, and financial technology companies typically require SOC 1 reports to demonstrate the reliability of their financial control mechanisms.
Technology and Cloud Service Providers
Cloud service providers, software companies, and technology platforms should focus on SOC 2 reports. According to AICPA experts, SOC 2 reports are essential for organizations handling sensitive customer data. These reports evaluate security controls across five key criteria: security, availability, processing integrity, confidentiality, and privacy. Technology companies can use SOC 2 reports to showcase their commitment to robust data protection practices.
The following table organizes recommended SOC report types by industry to help guide your selection:
| Industry Sector | Recommended SOC Report | Primary Focus |
|---|---|---|
| Financial Services, Accounting | SOC 1 | Internal controls over financial reporting |
| Payroll Processing, Investment Mgmt | SOC 1 | Reliability and accuracy of financial transaction processing |
| Technology, Cloud Service Providers | SOC 2 | Security, privacy, availability, processing integrity, confidentiality |
| Software / SaaS Platforms | SOC 2 | Data protection and robust information security practices |
| General Marketing/Public Trust | SOC 3 | Publicly sharing high-level security overview |
Strategic Report Selection
Evaluating Organizational Needs
Choosing the right SOC report involves assessing several critical factors. Cybersecurity compliance experts from ComplianceForge recommend considering the following key elements:
- Stakeholder Requirements: Identify the specific compliance needs of your clients, partners, and regulatory bodies
- Data Sensitivity: Determine the level of control and transparency required for your organization's data management
- Industry Regulations: Understand the specific compliance standards relevant to your business sector
Marketing and Trust Building
SOC 3 reports serve a unique purpose for organizations looking to publicly demonstrate their security commitment. ISACA security professionals suggest these reports are ideal for:
- Public Communication: Sharing a high-level overview of security practices
- Marketing Purposes: Building trust with potential clients and partners
- General Audience Engagement: Providing a non-technical summary of security controls
The decision between SOC 1, SOC 2, and SOC 3 reports is not mutually exclusive. Many organizations benefit from obtaining multiple report types to address different stakeholder needs and demonstrate comprehensive control environments. By carefully evaluating your specific operational requirements, industry standards, and communication objectives, you can develop a strategic approach to SOC reporting that enhances your organization's credibility and transparency.
Consult with certified cybersecurity and compliance professionals to develop a tailored SOC reporting strategy that aligns with your business goals and provides meaningful assurance to your stakeholders.
Latest SOC Compliance Trends for 2025
As cybersecurity landscapes evolve rapidly, SOC compliance is undergoing significant transformations in 2025. Organizations are increasingly adopting innovative approaches to meet complex security and regulatory requirements while maintaining operational efficiency and trust.
Technological Integration in Compliance
Artificial Intelligence and Automated Compliance
Research from MIT Technology Review indicates that artificial intelligence is revolutionizing SOC compliance processes. Advanced AI algorithms now enable organizations to automatically detect control gaps, predict potential security vulnerabilities, and streamline compliance documentation. Cybersecurity experts from Gartner predict that AI-driven compliance tools will reduce manual audit preparation time by up to 60% in 2025.
Blockchain for Enhanced Verification
Blockchain technology is emerging as a game-changing solution for SOC report verification. According to IEEE Security & Privacy, blockchain provides immutable audit trails, ensuring the integrity and transparency of compliance documentation. This technology enables real-time verification of control implementations, creating a more dynamic and trustworthy compliance ecosystem.
Evolving Compliance Frameworks
Integrated Control Management
Cisco's Common Control Framework (CCF) v4.0 represents a significant advancement in standardized compliance. By mapping controls across multiple global frameworks like ISO 27001, SOC 2, NIST, and FedRAMP, organizations can develop more cohesive and efficient compliance strategies. This approach reduces redundancy and provides a scalable model for managing complex regulatory requirements.
Emerging Trust Services Criteria
The AICPA is expanding Trust Services Criteria to address emerging technological challenges. Research from ISACA highlights new focus areas including:
- AI Governance Controls: Frameworks for responsible AI development and deployment
- Cloud-Native Security Protocols: Enhanced criteria for distributed and multi-cloud environments
- Privacy-Enhancing Technologies: Robust mechanisms for data protection and consent management
These evolving trends demonstrate that SOC compliance is becoming more proactive, technology-driven, and holistic. Organizations must continuously adapt their compliance strategies to leverage emerging technologies, maintain stakeholder trust, and effectively mitigate evolving cybersecurity risks.
Successful compliance in 2025 requires a forward-thinking approach that integrates advanced technologies, anticipates regulatory changes, and prioritizes comprehensive risk management. By embracing these innovative trends, organizations can transform compliance from a mandatory requirement into a strategic business advantage.
Frequently Asked Questions
What is the difference between SOC 1, SOC 2, and SOC 3 reports?
SOC 1 focuses on internal controls over financial reporting, while SOC 2 evaluates security and privacy across five Trust Services Criteria. SOC 3 provides a public-facing summary of an organization’s security controls without technical details.
When should my organization choose a SOC 1 report?
A SOC 1 report is recommended for organizations that handle financial transactions or manage financial data, such as financial services, payroll processors, and accounting firms.
Who should be the audience for SOC 2 reports?
SOC 2 reports target management, clients, and regulators, providing detailed assessments of an organization’s controls related to security, availability, processing integrity, confidentiality, and privacy.
Can SOC 3 reports be shared publicly?
Yes, SOC 3 reports are designed for public distribution, allowing organizations to demonstrate their commitment to security with a high-level overview that can be easily shared with potential clients and stakeholders.
Ready to Simplify Your SOC Reporting and Questionnaire Process?
If navigating SOC 1, SOC 2, or SOC 3 requirements feels overwhelming, you are not alone. Many organizations feel pressured to demonstrate compliance, yet get bogged down by time-consuming security questionnaires and slow team coordination. Manual processes can lead to errors, delayed contracts, and missed business opportunities, especially when fast answers are critical for winning trust with clients and regulators.

With Skypher, you can automate your security review process and respond to security questionnaires in a fraction of the time. Our AI Questionnaire Automation Tool speeds up your compliance workflow, integrates with more than 40 leading platforms, and helps you build a dynamic Trust Center tailored for SOC reporting needs.
Take the first step toward faster compliance and stronger client confidence. Visit Skypher now to see how your team can eliminate bottlenecks and gain a decisive edge in the evolving world of SOC requirements.
