Choosing between SOC 1 and SOC 2 reports often triggers debate in boardrooms across the United States, Canada, and Europe as tech firms work to safeguard both financial statements and sensitive client data. Understanding the difference matters because each framework carries unique implications for risk management and compliance. This overview untangles the key distinctions, helping security teams focus on the SOC report that aligns with their organization’s core business needs and stakeholder expectations.
Table of Contents
- Defining SOC 1 and SOC 2 Reports
- Primary Purposes and Key Audiences
- SOC 1 Versus SOC 2 Criteria and Controls
- Impact on Compliance and Risk Management
- Choosing the Right SOC Report for Your Needs
Key Takeaways
| Point | Details |
|---|---|
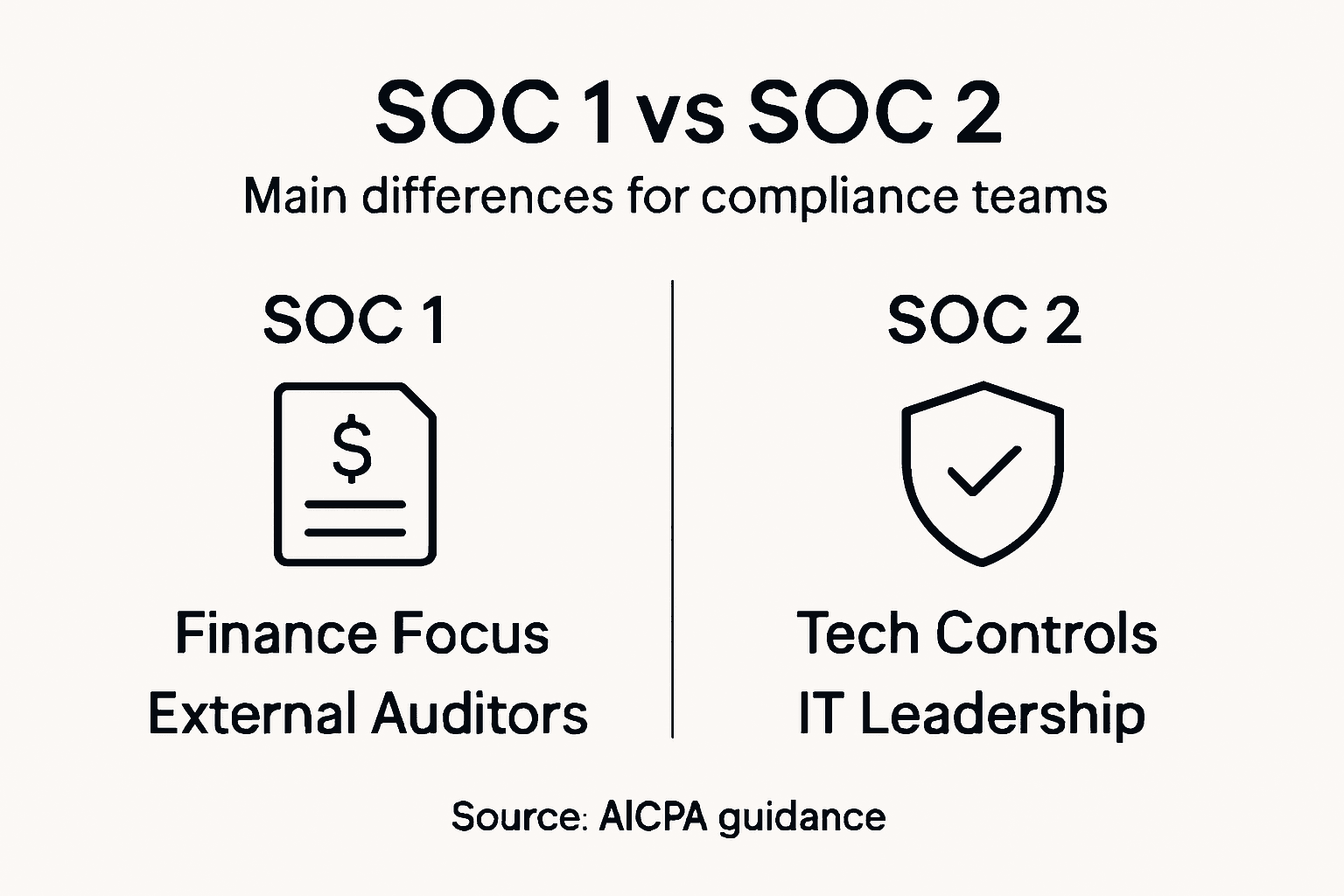
| Understanding SOC Reports | SOC 1 reports focus on financial reporting controls, while SOC 2 reports emphasize cybersecurity and data protection controls. |
| Target Audiences | SOC 1 is primarily for auditors and finance teams, whereas SOC 2 is intended for IT and security professionals. |
| Selection Criteria | Choosing between SOC 1 and SOC 2 depends on specific organizational compliance needs and risk management strategies. |
| Impact on Compliance | Both report types offer comprehensive assurances and enhance trust with clients and regulatory bodies by validating internal controls. |
Defining SOC 1 and SOC 2 Reports
Service Organization Control (SOC) reports are comprehensive assessments developed by the American Institute of Certified Public Accountants (AICPA) to evaluate an organization's internal controls and security practices. These reports provide critical insights for businesses seeking to understand and validate their operational and financial risk management strategies.
SOC reports come in different variations, with SOC 1 and SOC 2 being the most prominent. SOC reports help evaluate internal controls at service providers, each serving distinct purposes:
- SOC 1 Reports: Focus specifically on controls relevant to financial reporting
- SOC 2 Reports: Emphasize cybersecurity and technology controls
- Type I Reports: Assess control design at a specific point in time
- Type II Reports: Evaluate control effectiveness over an extended period
The key distinction between SOC 1 and SOC 2 reports lies in their primary objectives. SOC 1 reports are primarily designed for auditors and focus on financial statement-related controls within service organizations. They provide assurance about the design and implementation of internal financial reporting mechanisms.
In contrast, SOC 2 reports concentrate on cybersecurity and data management practices. These reports evaluate an organization's controls across five critical trust service criteria:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Pro-Tip: When selecting between SOC 1 and SOC 2 reports, carefully assess your organization's specific compliance and risk management needs to determine the most appropriate assessment framework.
Here's how SOC 1 and SOC 2 reports differ across core business dimensions:
| Dimension | SOC 1 Report | SOC 2 Report |
|---|---|---|
| Primary Focus | Financial reporting controls | Cybersecurity and privacy controls |
| Main Users | Auditors, finance teams | Security officers, IT professionals |
| Compliance Alignment | Financial auditing standards | Trust Services Criteria |
| Typical Recipients | Financial stakeholders | Clients with data security concerns |
| Key Outcome | Financial statement reliability | Client confidence in data protection |
Primary Purposes and Key Audiences
Security compliance reports like SOC 1 and SOC 2 serve critical roles for different stakeholders in the business ecosystem. These assessments are designed to provide targeted insights and assurances to specific audiences with unique risk management and regulatory compliance needs.
SOC 1 reports are primarily targeted at the following key audiences:
- Financial auditors conducting external financial statement reviews
- Accounting firms verifying service organization controls
- Corporate finance teams assessing vendor financial reporting risks
- Executive leadership monitoring internal financial control effectiveness
SOC 2 reports, by contrast, cater to a broader range of technology and security-focused stakeholders:
- Chief Information Security Officers (CISOs)
- IT governance and compliance professionals
- Cybersecurity risk management teams
- Third-party vendor risk assessment specialists
- Potential clients evaluating service provider security credentials
Each report type addresses specific organizational concerns. SOC reports help evaluate internal controls by providing granular insights into an organization's operational frameworks. SOC 1 reports concentrate on financial reporting mechanisms, offering detailed assessments of control environments that impact financial statement reliability.

Meanwhile, SOC 2 reports focus on technological infrastructure, data protection strategies, and cybersecurity protocols. These reports provide comprehensive evaluations of an organization's ability to safeguard sensitive information and maintain robust security standards across multiple critical domains.
Pro-Tip: Carefully analyze your organization's specific compliance requirements and stakeholder expectations before selecting between SOC 1 and SOC 2 reporting frameworks to ensure maximum value and relevance.
SOC 1 Versus SOC 2 Criteria and Controls
SOC 1 and SOC 2 reports differ fundamentally in their approach to evaluating organizational controls, each targeting specific aspects of operational risk management. SOC audits assess critical organizational controls through distinct methodological frameworks that address unique business requirements.
SOC 1 Control Criteria are characterized by the following key attributes:
- Focused exclusively on financial reporting controls
- Conducted under SSAE 18 standards
- Designed to evaluate internal financial process risks
- Primarily used by accounting and financial audit professionals
- Concentrate on controls impacting financial statement accuracy
SOC 2 Control Criteria encompass a broader range of technological and operational domains:
- Comprehensive evaluation of cybersecurity practices
- Based on five Trust Services Criteria
- Flexible framework addressing multiple operational dimensions
- Mandatory security control assessments
- Optional criteria for additional operational domains
The five Trust Services Criteria for SOC 2 reports include:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Unlike SOC 1 reports, which narrowly focus on financial reporting mechanisms, SOC 2 reports provide a holistic assessment of an organization's technological infrastructure and data protection strategies. These reports offer comprehensive insights into an organization's ability to maintain robust security standards and protect sensitive information across multiple critical domains.
Pro-Tip: Carefully evaluate your organization's specific compliance requirements and select the SOC report type that most comprehensively addresses your operational and security risk management needs.
Impact on Compliance and Risk Management
Compliance and risk management strategies are fundamentally transformed by the distinct approaches of SOC 1 and SOC 2 reports. Compliance addresses critical organizational risks through targeted assessment frameworks that provide comprehensive insights into an organization's operational control effectiveness.
SOC 1 Reports Impact on Risk Management:
- Mitigate financial reporting risks
- Provide assurance to external auditors
- Support accurate financial statement preparation
- Validate internal financial control mechanisms
- Reduce potential errors in financial processes
SOC 2 Reports Impact on Risk Management:
- Address comprehensive cybersecurity vulnerabilities
- Validate data protection strategies
- Demonstrate operational reliability to enterprise clients
- Provide evidence of security control effectiveness
- Support contract negotiations with financial institutions
The implications of these reports extend far beyond simple compliance checkboxes. SOC 1 reports primarily serve financial stakeholders by ensuring the integrity of financial reporting mechanisms, while SOC 2 reports offer a broader shield against technological and operational risks.
Enterprise organizations increasingly rely on these reports as critical risk management tools. They provide independent, third-party validation of an organization's control environments, helping to build trust with clients, partners, and regulatory bodies by demonstrating a proactive approach to managing potential vulnerabilities.
Pro-Tip: Develop a comprehensive compliance strategy that integrates both SOC 1 and SOC 2 report insights to create a holistic risk management approach.
Choosing the Right SOC Report for Your Needs
Selecting the appropriate SOC report is a critical strategic decision that requires careful evaluation of organizational objectives, stakeholder requirements, and operational complexities. SOC report selection depends on specific service characteristics and requires a nuanced understanding of your company's risk management landscape.
Scenarios Requiring SOC 1 Reports:
- Financial services organizations
- Accounting and payroll service providers
- Companies directly impacting client financial statements
- Organizations with complex financial reporting mechanisms
- Businesses serving financial institutions
Scenarios Requiring SOC 2 Reports:
- Cloud service providers
- Technology and software companies
- Data hosting and storage organizations
- Cybersecurity service providers
- Companies handling sensitive customer information
The decision-making process involves evaluating several critical factors:
- Nature of your primary business services
- Types of data you manage
- Client and regulatory compliance requirements
- Specific industry standards
- Stakeholder expectations
In many instances, organizations might find value in pursuing both SOC 1 and SOC 2 reports to provide comprehensive assurance across financial and technological domains. This approach demonstrates a holistic commitment to robust internal controls and builds significant trust with clients, partners, and regulatory bodies.
The following table summarizes when each SOC report type is typically needed in different industries:
| Industry Example | SOC 1 Needed | SOC 2 Needed |
|---|---|---|
| Payroll Providers | Essential for client audits | Optional unless handling sensitive data |
| Cloud Services | Rarely required | Critically important for contracts |
| Banks & Lenders | Frequently required | Increasingly requested by partners |
| SaaS Startups | Sometimes needed for investors | Usually expected for client trust |
Pro-Tip: Conduct a thorough internal assessment of your organization's risk profile and compliance needs before determining which SOC report type best aligns with your strategic objectives.
Simplify SOC 1 and SOC 2 Compliance with Smart Automation
Understanding the nuances between SOC 1 and SOC 2 reports is essential for effective risk management and regulatory compliance. Both reports demand thorough security questionnaires and detailed responses that can strain your team and delay business processes. Managing these complex requirements manually can increase the risk of errors and slow down your response times.
Skypher offers a powerful solution to these challenges. Our AI Questionnaire Automation Tool accelerates and simplifies the response process for SOC-related security assessments, helping you answer hundreds of questions accurately in minutes. With seamless API Integrations with Third-Party Risk Management Platforms, real-time collaboration features, and a Custom Trust Center, your teams stay aligned and your compliance efforts become a competitive advantage.

Take control of your SOC compliance today. Visit Skypher to experience how automated questionnaire workflows can reduce your compliance burden and boost client confidence with fast, precise security reviews. Start streamlining your path to SOC 1 and SOC 2 certification now.
Frequently Asked Questions
What are the main differences between SOC 1 and SOC 2 reports?
SOC 1 reports focus on financial reporting controls, while SOC 2 reports emphasize cybersecurity and technology controls. SOC 1 is designed for auditors and finance teams, whereas SOC 2 targets security officers and IT professionals.
Who are the primary users of SOC 1 and SOC 2 reports?
SOC 1 reports are primarily used by financial auditors and corporate finance teams, while SOC 2 reports cater to Chief Information Security Officers (CISOs), IT governance professionals, and potential clients evaluating a service provider's security credentials.
What are the key trust service criteria evaluated in SOC 2 reports?
SOC 2 reports evaluate five key trust service criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. These criteria ensure a comprehensive assessment of an organization's cybersecurity practices and data management strategies.
When should an organization choose a SOC 1 report over a SOC 2 report?
Organizations should choose a SOC 1 report when they are involved in financial services, accounting, payroll, or any business that impacts client financial statements. A SOC 2 report is more suitable for technology companies, cloud service providers, and organizations handling sensitive customer information.