SOC 2 auditors are the gatekeepers for trust in data privacy and security. Most people expect a simple checklist, but a real SOC 2 audit is a deep dive that can take six to twelve months of preparation for a proper review. The surprise is not just in the length or complexity. The real twist is that the most important factor is not technical skill alone. Organizations who find an auditor that matches their company culture and communication style see radically better outcomes and smoother audits. That one decision can determine the difference between audit failure and a security program that wins client trust.
Table of Contents
- Understanding The Role Of A SOC 2 Auditor
- How To Choose The Right SOC 2 Auditor
- SOC 2 Audit Process: Steps And Expectations
- Tips For Working Effectively With Your SOC 2 Auditor
Quick Summary
| Takeaway | Explanation |
|---|---|
| Selecting the Right SOC 2 Auditor is Critical | Choose an auditor who not only has the necessary technical expertise and certifications but also aligns with your organization's culture and communication style for a more effective partnership. |
| Thorough Preparation is Essential for Success | Begin preparing for the SOC 2 audit 6-12 months in advance by documenting security policies, assessing internal controls, and conducting gap analyses to identify and address weaknesses. |
| The Audit Process Involves In-Depth Evaluation | The SOC 2 audit goes beyond compliance checks; expect detailed examinations of security practices through stakeholder interviews, documentation reviews, and technical testing to assess true security effectiveness. |
| Transparency Builds Trust with Auditors | Maintain open communication throughout the audit process by being upfront about your security infrastructure and any vulnerabilities, fostering a collaborative relationship with auditors. |
| View Audit Findings as Opportunities for Growth | Utilize auditor recommendations for ongoing improvement, treating the SOC 2 audit not as a one-time requirement but as a continuous process to enhance security posture and control mechanisms. |
Understanding the Role of a SOC 2 Auditor
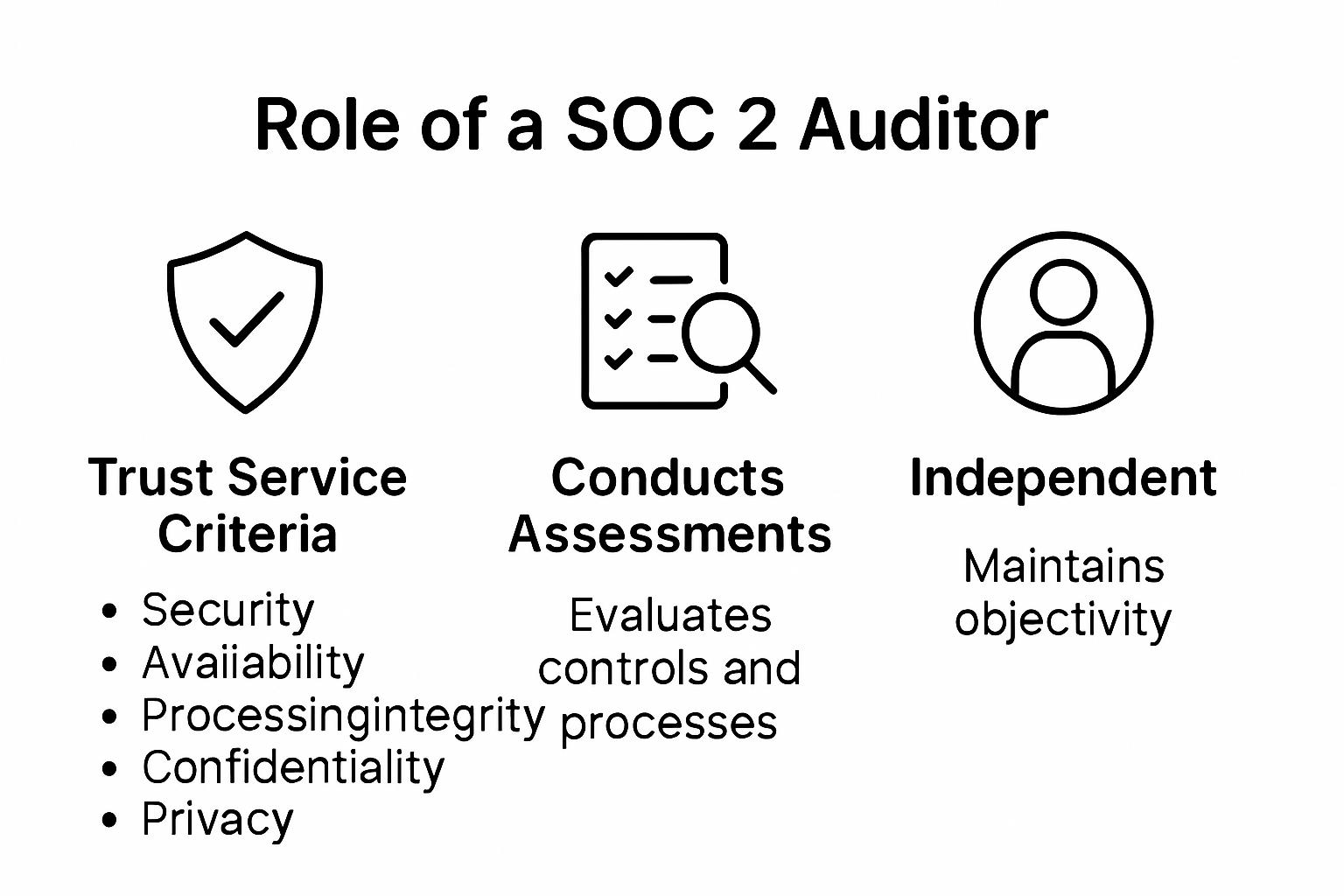
A SOC 2 auditor plays a critical role in helping organizations validate their cybersecurity and data protection practices. These specialized professionals conduct comprehensive assessments that go far beyond simple compliance checks. They serve as independent investigators who systematically evaluate an organization's internal controls and security protocols.
The Core Responsibilities of SOC 2 Auditors
SOC 2 auditors are certified professionals tasked with performing detailed examinations of an organization's information security management systems. According to the American Institute of Certified Public Accountants (AICPA), these auditors focus on five core Trust Service Criteria: security, availability, processing integrity, confidentiality, and privacy.
Their primary responsibilities include:
- Comprehensive Control Review: Meticulously examining an organization's security controls and operational processes
- Risk Assessment: Identifying potential vulnerabilities and weaknesses in existing security frameworks
- Evidence Collection: Gathering and analyzing documentation that demonstrates effective security practices
The audit process requires auditors to take a forensic approach. They do not merely check boxes but conduct in-depth investigations that reveal the actual effectiveness of an organization's security infrastructure. Research from cloud security experts indicates that these professionals must maintain an independent and objective perspective throughout their evaluation.
Technical Expertise and Evaluation Techniques
Successful SOC 2 auditors possess a unique blend of technical knowledge and analytical skills. They must understand complex information security frameworks, network architectures, and regulatory requirements. According to Neumetric's cybersecurity research, auditors typically employ multiple evaluation techniques:
- Reviewing security policies and procedural documentation
- Conducting interviews with key organizational stakeholders
- Performing technical testing of access controls
- Validating authentication and authorization mechanisms
- Assessing data protection and encryption strategies
The auditor's report becomes a critical document that provides stakeholders with an independent assessment of the organization's security posture. This report does not simply state whether an organization passes or fails but provides nuanced insights into its security practices.
Moreover, SOC 2 auditors must stay current with evolving cybersecurity threats and technological advancements. They continuously update their knowledge to ensure their evaluation methodologies remain relevant and comprehensive. Their work requires a perfect balance between technical expertise and rigorous investigative skills.
By providing an objective, third-party perspective, SOC 2 auditors help organizations build trust with clients, partners, and regulatory bodies. Their detailed assessments go beyond compliance checkboxes and offer meaningful insights into an organization's commitment to protecting sensitive information.
How to Choose the Right SOC 2 Auditor
Selecting the appropriate SOC 2 auditor represents a critical decision that can significantly impact your organization's security assessment and compliance strategy. The right auditor goes beyond mere technical verification and becomes a strategic partner in understanding and improving your security infrastructure.
Evaluating Professional Credentials and Expertise
The foundation of choosing an effective SOC 2 auditor lies in thoroughly assessing their professional qualifications. According to Wolf & Co, organizations should prioritize auditors with specific industry experience and deep technical understanding.
Key credentials to examine include:
- AICPA Certification: Verify the auditor is a licensed Certified Public Accountant (CPA) authorized by the American Institute of Certified Public Accountants
- Relevant Industry Experience: Seek auditors with proven track records in your specific sector
- Technical Specialization: Look for professionals with advanced cybersecurity and information systems credentials
Compass IT Consulting recommends conducting comprehensive background checks that extend beyond formal certifications. This includes reviewing past audit reports, understanding their methodology, and evaluating their depth of technical knowledge.
Assessing Auditor Compatibility and Approach
Beyond technical qualifications, organizations must evaluate the auditor's communication style and collaborative approach. An effective SOC 2 auditor should function as a partner rather than a purely transactional service provider.
Critical factors to consider include:
- Communication transparency
- Willingness to provide detailed explanations
- Ability to translate complex technical findings into actionable insights
- Demonstrated commitment to understanding your unique organizational context
ERM Protect emphasizes the importance of conducting preliminary discussions to assess cultural and professional alignment. These initial conversations can reveal crucial insights about the auditor's problem-solving approach and communication effectiveness.
Additionally, organizations should request and thoroughly review references from previous clients. Pay special attention to feedback regarding the auditor's:
- Thoroughness of investigation
- Professionalism during the audit process
- Quality and clarity of final reporting
- Ability to provide constructive recommendations
The ideal SOC 2 auditor combines technical expertise with strategic insight. They should not merely identify compliance gaps but help your organization develop a robust, proactive approach to information security.
Financial considerations are important but should not be the sole determining factor. While cost matters, selecting an auditor based primarily on price can compromise the quality and depth of your security assessment. Invest in an auditor who demonstrates comprehensive understanding and a commitment to helping your organization strengthen its security posture.
Ultimately, choosing the right SOC 2 auditor is about finding a trusted advisor who can provide objective, thorough, and meaningful insights into your organization's security controls and practices.
To help summarize the most important factors when evaluating a SOC 2 auditor, the following table organizes the technical and compatibility attributes you should compare:
| Evaluation Factor | What to Look For | Why It Matters |
|---|---|---|
| AICPA Certification | Registered CPA authorized by AICPA | Ensures credibility and compliance |
| Relevant Industry Experience | Track record in your specific sector | Sector expertise improves audit effectiveness |
| Technical Specialization | Advanced cybersecurity/info systems credentials | Deepens technical assessment quality |
| Communication Transparency | Clear, open, and timely communicator | Promotes smoother collaboration and understanding |
| Constructive Recommendations | Ability to provide actionable, practical advice | Drives ongoing security improvements |
| Professionalism & Partnering | Demonstrated commitment to your context and unique challenges | Fosters a positive, collaborative relationship |
SOC 2 Audit Process: Steps and Expectations

The SOC 2 audit process is a comprehensive evaluation that requires meticulous preparation, strategic planning, and a deep understanding of an organization's security controls. Unlike standard compliance checks, this process demands a holistic approach to demonstrating an organization's commitment to protecting sensitive information.
Preparing for the SOC 2 Audit
AICPA guidelines emphasize that successful SOC 2 audits begin long before the actual assessment. Organizations must first define their audit scope and identify which of the five Trust Service Criteria they will be evaluated against: security, availability, processing integrity, confidentiality, and privacy.
Key preparatory steps include:
- Comprehensive Documentation: Creating detailed security policies and procedures
- Internal Control Assessment: Conducting a thorough review of existing security mechanisms
- Gap Analysis: Identifying and addressing potential weaknesses in current security infrastructure
Compliance experts at Secure Controls Framework recommend organizations start their preparation at least 6-12 months before the actual audit. This timeline allows for meaningful implementation and refinement of security controls.
The Audit Execution Phase
During the formal audit, SOC 2 auditors conduct an in-depth examination of an organization's security practices. According to CyberSecurity Insights, this phase typically involves multiple critical activities:
- Conducting extensive interviews with key stakeholders
- Reviewing technical documentation and security logs
- Performing technical testing of security controls
- Examining access management procedures
- Validating data protection and encryption mechanisms
Auditors use a combination of documentation review, technical testing, and stakeholder interviews to develop a comprehensive understanding of an organization's security posture. They look beyond surface-level compliance to assess the actual effectiveness and implementation of security controls.
Post-Audit Considerations and Reporting
The conclusion of the audit results in a detailed report that provides insights into the organization's security practices. Information Systems Audit and Control Association (ISACA) notes that this report is not a simple pass or fail document but a nuanced assessment of an organization's security controls.
Key components of the final report include:
- Detailed description of tested controls
- Auditor's opinion on the effectiveness of these controls
- Recommendations for improving security infrastructure
- Identification of potential vulnerabilities
Organizations receive a type II SOC 2 report, which covers a specified time period and demonstrates the ongoing effectiveness of security controls. This report becomes a critical document for building trust with clients, partners, and stakeholders.
Successful navigation of the SOC 2 audit process requires more than technical compliance. It demands a strategic approach to security that views protection as an ongoing, dynamic process rather than a static checklist. Organizations that embrace this mindset transform the audit from a compliance exercise into a meaningful opportunity for security enhancement.
The following table breaks down the SOC 2 audit process steps and the main actions required at each stage, to clarify what organizations can expect from start to finish:
| Audit Stage | Key Actions | Purpose/Outcome |
|---|---|---|
| Preparation | Document policies, assess controls, conduct gap analysis | Build foundation and identify improvements |
| Audit Scope Definition | Select Trust Service Criteria (e.g., security, availability) | Tailor assessment to company and client needs |
| Pre-Audit Remediation | Close identified gaps, implement necessary controls | Address weaknesses before formal audit begins |
| Audit Execution | Interviews, doc reviews, technical testing, log analysis | Evaluate effectiveness of controls |
| Reporting | Auditor issues findings, recommendations, and opinions | Obtain a detailed SOC 2 report for stakeholders |
| Post-Audit Review | Internal review of findings, create action plan | Strengthen ongoing security and compliance efforts |
Tips for Working Effectively With Your SOC 2 Auditor
Navigating a SOC 2 audit requires more than technical preparedness. The relationship between an organization and its SOC 2 auditor can significantly impact the audit's effectiveness, efficiency, and ultimate value. Successful collaboration demands strategic communication, proactive preparation, and a collaborative mindset.
Preparation and Transparency
DevOps Oasis emphasizes the critical importance of early and comprehensive stakeholder engagement. Organizations must create a cross-functional team that includes representatives from IT, legal, compliance, and executive leadership. This approach ensures a holistic understanding of the audit process and reduces potential friction during the assessment.
Key preparation strategies include:
- Clear Communication Channels: Establish dedicated points of contact for the auditor
- Comprehensive Documentation: Organize all relevant security policies and procedures
- Proactive Risk Identification: Conduct internal assessments before the formal audit
Transparency is the cornerstone of an effective audit relationship. OneTrust recommends that organizations be upfront about their current security infrastructure, potential vulnerabilities, and ongoing improvement efforts. This honesty helps auditors understand the context of your security controls and approach the assessment more collaboratively.
Managing the Audit Interaction
Effective interaction with a SOC 2 auditor requires a strategic approach that balances professionalism with openness. Trust Cloud Community suggests several critical practices for smooth audit interactions:
- Respond promptly to auditor requests
- Provide clear, concise documentation
- Assign knowledgeable team members to support the audit process
- Maintain a cooperative and professional demeanor
Organizations should view the auditor as a partner rather than an adversary. This means being prepared to discuss challenges openly, demonstrate continuous improvement efforts, and show a genuine commitment to security excellence.
Leveraging Audit Insights
The most successful organizations transform the SOC 2 audit from a compliance exercise into a strategic opportunity for improvement. Rather than viewing the audit as a one-time event, treat it as an ongoing process of security enhancement.
Consider the auditor's findings as valuable insights that can:
- Identify potential security gaps
- Highlight areas for process improvement
- Provide an objective assessment of your security infrastructure
- Offer recommendations for strengthening control mechanisms
After the audit, schedule a comprehensive review of the findings with key stakeholders. Develop a detailed action plan that addresses the auditor's recommendations and establishes a timeline for implementing improvements.
Remember that SOC 2 compliance is not a destination but a continuous journey. The most effective organizations cultivate a culture of ongoing security improvement, viewing each audit as an opportunity to refine and strengthen their security posture.
Ultimately, working effectively with a SOC 2 auditor requires a combination of technical preparedness, strategic communication, and a commitment to continuous improvement. By approaching the audit as a collaborative process, organizations can transform a potentially stressful experience into a valuable opportunity for growth and security enhancement.
Frequently Asked Questions
What is the role of a SOC 2 auditor?
SOC 2 auditors evaluate an organization’s information security management systems, focusing on five core Trust Service Criteria: security, availability, processing integrity, confidentiality, and privacy. They conduct assessments that go beyond compliance checks to provide objective insights into security practices.
How do I choose the right SOC 2 auditor for my organization?
When selecting a SOC 2 auditor, assess their professional credentials, relevant industry experience, and technical expertise. Additionally, evaluate their communication style and compatibility with your organization's culture to ensure effective collaboration throughout the audit process.
How long does a SOC 2 audit typically take?
A SOC 2 audit can take anywhere from six to twelve months of preparation before the actual review. The audit process itself involves detailed examinations, stakeholder interviews, and documentation review, making thorough preparation essential for success.
What should organizations do after receiving their SOC 2 audit report?
After receiving a SOC 2 audit report, organizations should review the findings and recommendations with key stakeholders, using them as insights for ongoing improvement. This should include developing an action plan to address any identified vulnerabilities and enhance security controls.
Transform the SOC 2 Audit Challenge Into a Win for Your Team
Preparing for a SOC 2 audit can feel overwhelming. You need detailed documentation, clear communication with your auditor, and flawless control evidence ready to go. Many companies struggle with last-minute information gathering and coordinating between departments. The truth is, success hinges not just on technical controls but on how quickly and accurately you can respond to those deep-dive security questions auditors ask, especially when they require evidence across different teams.

Imagine if you could cut your audit prep time, improve response accuracy, and boost trust with both your auditors and customers. Skypher automates security questionnaire workflows, organizes evidence across your organization, and allows real-time collaboration—all so your next SOC 2 audit is smoother and faster. Ready to eliminate bottlenecks and ace your audit? Discover how Skypher’s AI-driven platform accelerates your SOC 2 journey and empowers your team to work smarter, not harder.
