Managing recurring security questionnaires from clients can quickly overwhelm even the most organized American or European compliance teams. For companies serving customers in strict regulatory environments, SOC 2 auditors act as independent validators of your security and data protection controls. Understanding what these auditors evaluate and how they conduct their assessments will help CISOs and compliance managers prioritize resources, minimize back-and-forth, and present a credible compliance posture to stakeholders.
Table of Contents
- Defining SOC 2 Auditors And Their Role
- Types Of SOC 2 Audits And Key Differences
- Core Responsibilities Of SOC 2 Auditors
- SOC 2 Audit Process For SaaS Companies
- Common Risks, Costs, And Practical Challenges
Key Takeaways
| Point | Details |
|---|---|
| Understanding SOC 2 Auditors | SOC 2 auditors validate cybersecurity practices of organizations, focusing on five Trust Services Criteria to assess security and operational integrity. |
| Types of SOC 2 Audits | Organizations can choose between SOC 2 Type 1 and Type 2 audits, with Type 1 offering a snapshot of controls and Type 2 demonstrating ongoing effectiveness over time. |
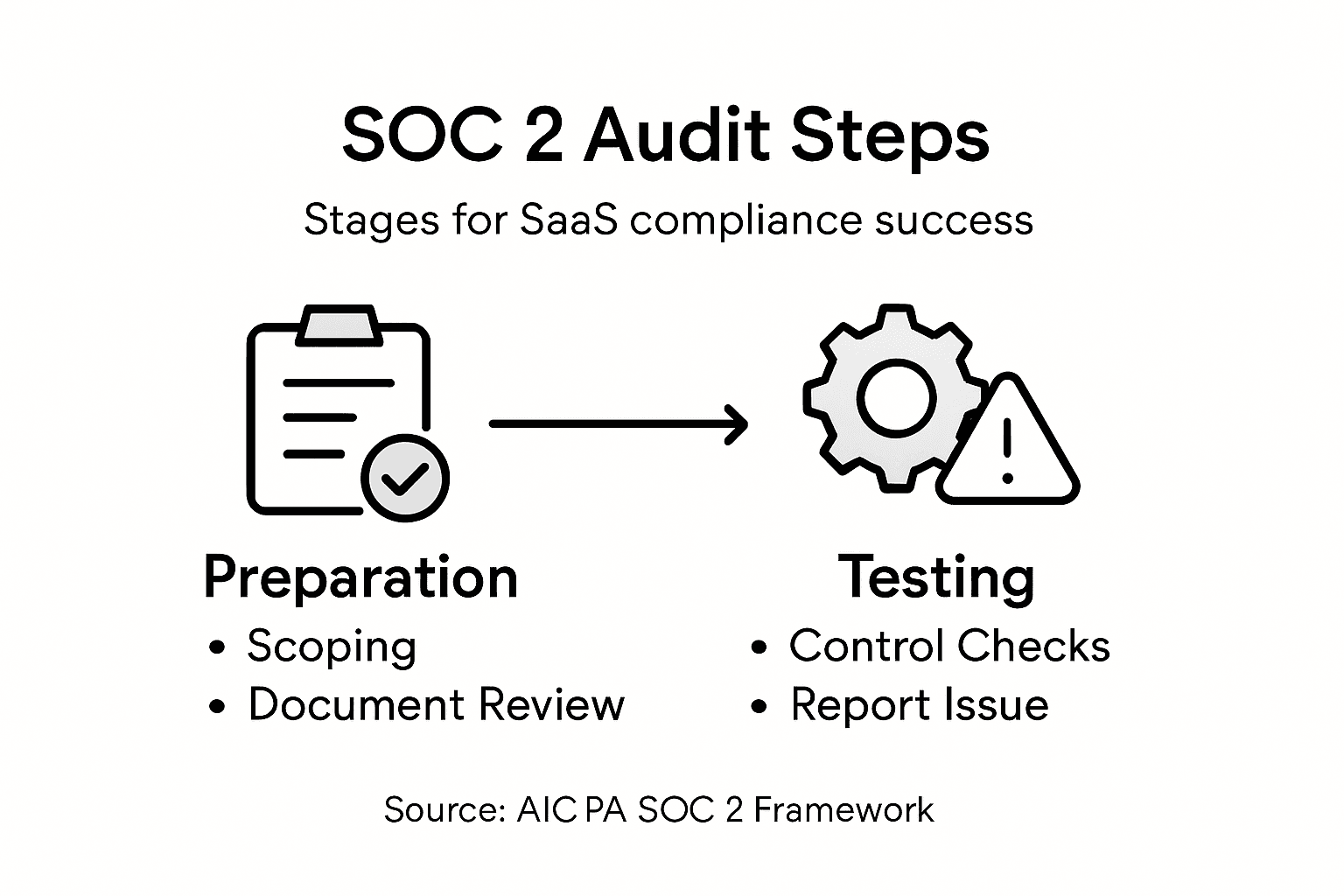
| Critical Audit Steps | The SOC 2 audit process includes stages like planning, control documentation review, testing, and reporting to ensure comprehensive evaluation. |
| Financial and Compliance Challenges | Preparing for SOC 2 compliance involves navigating risks, financial implications, and operational challenges, necessitating strategic planning and resource allocation. |
Defining SOC 2 Auditors and Their Role
SOC 2 auditors play a critical role in validating the cybersecurity practices of service organizations, particularly within technology and cloud service sectors. These specialized professionals, typically Certified Public Accountants (CPAs), conduct comprehensive evaluations of an organization's internal controls and security mechanisms.
The primary function of SOC 2 auditors involves assessing organizational controls based on five key Trust Services Criteria established by the American Institute of Certified Public Accountants (AICPA). These critical assessment areas include:
- Security: Protecting systems against unauthorized access
- Availability: Ensuring systems are operational and accessible
- Processing Integrity: Confirming system processing is complete, accurate, and timely
- Confidentiality: Safeguarding sensitive information
- Privacy: Managing personal data collection and usage
SOC 2 auditors employ a rigorous methodology to examine an organization's control environment. They review documentation, interview key personnel, and perform detailed testing to validate the effectiveness of implemented security measures. These independent assessments provide crucial insights into an organization's risk management and cybersecurity practices.

Here's a summary of the five Trust Services Criteria and their business impact:
| Criterion | Focus Area | Business Impact |
|---|---|---|
| Security | Protection from threats | Reduces risk of data breaches |
| Availability | System uptime | Ensures reliable client access |
| Processing Integrity | Accurate operations | Promotes trust in service output |
| Confidentiality | Safeguarding sensitive data | Prevents data leaks |
| Privacy | Personal data handling | Builds client confidence |
The audit process typically involves multiple stages:
- Initial scoping and planning
- Comprehensive control documentation review
- Detailed testing of control effectiveness
- Reporting and recommendations
Pro tip: Select SOC 2 auditors with demonstrated expertise in your specific industry and proven experience with cloud service security frameworks.
Types of SOC 2 Audits and Key Differences
Security professionals and technology leaders must understand the nuanced differences between SOC 2 audit types to effectively manage their organization's compliance strategy. SOC 2 reporting frameworks offer two primary assessment approaches: Type 1 and Type 2 audits, each serving distinct organizational needs and providing unique insights into cybersecurity controls.
The key characteristics of SOC 2 audit types include:
-
SOC 2 Type 1 Reports:
- Assess control design at a specific point in time
- Provide snapshot evaluation of security mechanisms
- Validate the suitability of established control frameworks
- Typically shorter and less comprehensive
-
SOC 2 Type 2 Reports:
- Evaluate both control design and operational effectiveness
- Cover an extended period (usually 6-12 months)
- Offer more detailed insights into sustained security practices
- Demonstrate consistent implementation of security controls
Organizations select audit types based on their specific compliance requirements, industry standards, and stakeholder expectations. Type 1 audits serve as an initial assessment, while Type 2 audits provide a more robust, time-tested validation of an organization's security posture.
Below is a comparison of SOC 2 Type 1 and Type 2 audits for decision-making:
| Aspect | Type 1 | Type 2 |
|---|---|---|
| Coverage period | Single point in time | 6-12 months continuous review |
| Control assessment | Design only | Design and effectiveness |
| Organizational benefit | Early readiness proof | Demonstrates ongoing security |
| Stakeholder value | Basic due diligence | Stronger assurance |
The audit process involves comprehensive examination across five critical Trust Services Criteria:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Companies can choose which criteria to include based on their unique operational landscape and risk management strategy.
Pro tip: Engage SOC 2 auditors who specialize in your specific industry vertical to ensure the most relevant and comprehensive assessment of your security controls.
Core Responsibilities of SOC 2 Auditors
SOC 2 auditors play a critical role in validating the cybersecurity and operational integrity of technology organizations. Independent audit professionals must conduct comprehensive assessments that go far beyond surface-level compliance checks, providing stakeholders with deep insights into an organization's security controls.
The core responsibilities of SOC 2 auditors encompass several key areas:
-
Evidence Collection:
- Gather comprehensive documentation
- Interview key organizational personnel
- Perform detailed control testing
- Validate security mechanism effectiveness
-
Compliance Verification:
- Assess controls against Trust Services Criteria
- Evaluate design and operational effectiveness
- Identify potential security vulnerabilities
- Provide objective recommendations
Auditors follow a structured approach to ensure thorough and reliable assessments. Their methodology involves multiple stages of rigorous examination, including:
- Initial planning and scoping
- Detailed documentation review
- Comprehensive control testing
- Risk assessment and gap analysis
- Report preparation and findings validation
Professional skepticism remains a cornerstone of the SOC 2 audit process. Certified Public Accountants (CPAs) with specialized cybersecurity expertise must maintain independence and objectivity throughout their investigation, ensuring that their assessment provides genuine value to organizations seeking to strengthen their security posture.
Pro tip: Select SOC 2 auditors with demonstrable experience in your specific industry vertical to ensure the most nuanced and relevant security assessment.
SOC 2 Audit Process for SaaS Companies
SaaS organizations must navigate a complex landscape of cybersecurity compliance, with the SOC 2 audit serving as a critical validation of their security infrastructure. Comprehensive audit processes help technology companies demonstrate their commitment to robust security practices and build trust with potential clients and stakeholders.
The SOC 2 audit journey for SaaS companies typically involves several strategic stages:
-
Preliminary Assessment:
- Conduct internal gap analysis
- Identify control weaknesses
- Map existing processes to Trust Services Criteria
- Develop remediation strategies
-
Preparation Phase:
- Refine security policies
- Implement technical controls
- Document organizational procedures
- Prepare comprehensive evidence collection
The audit process follows a structured approach that demands meticulous attention to detail and systematic documentation. SaaS companies must demonstrate controls across critical domains:
- Data management practices
- Access control mechanisms
- Vendor risk management
- Incident response protocols
- Continuous monitoring systems
Successful SOC 2 audits require organizations to prove not just the existence of controls, but their consistent and effective implementation over an extended period. This means maintaining rigorous documentation, conducting regular internal assessments, and continuously improving security frameworks.
Pro tip: Engage a dedicated internal compliance team months before the audit to ensure seamless preparation and minimize potential control gaps.
Common Risks, Costs, and Practical Challenges
SaaS organizations preparing for SOC 2 compliance must carefully navigate a complex landscape of potential risks and financial investments. SOC 2 compliance challenges encompass multiple dimensions that require strategic planning and significant organizational resources.
The primary risks and challenges can be categorized into several critical areas:
-
Compliance Risks:
- Insufficient control design
- Gaps in operational effectiveness
- Incomplete documentation
- Misalignment with evolving criteria
-
Financial Considerations:
- External auditor fees
- Internal resource allocation
- Remediation and technology investment
- Ongoing monitoring expenses
Organizations typically encounter substantial practical challenges throughout the SOC 2 audit process, including:
- Maintaining continuous compliance
- Balancing audit requirements with business operations
- Keeping pace with technological changes
- Managing complex documentation requirements
- Ensuring consistent staff training and awareness
The financial implications of SOC 2 compliance can be significant, with total costs ranging from $30,000 to $100,000 depending on organizational complexity, existing infrastructure, and the depth of required improvements. These expenses include not just direct audit fees, but also substantial internal investments in process refinement, technology upgrades, and ongoing monitoring systems.
Pro tip: Develop a dedicated compliance budget and timeline at least six months before your planned SOC 2 audit to mitigate unexpected financial and operational disruptions.
Simplify SOC 2 Compliance with Skypher's AI-Powered Automation
Navigating the demands of SOC 2 audits requires precise control documentation and seamless collaboration between teams. If managing security questionnaires and maintaining consistent evidence across the five Trust Services Criteria feels overwhelming, you are not alone. Skypher offers a powerful SaaS platform designed to automate and accelerate your security review process, ensuring your organization stays audit-ready and strengthens cybersecurity posture without the stress.

Experience the difference with Skypher’s AI Questionnaire Automation Tool that handles complex formats and integrates with over 40 third-party risk management platforms including ServiceNow and Slack for real-time collaboration. Whether your organization is preparing for a Type 1 or Type 2 SOC 2 audit, Skypher helps reduce the time and resources spent on compliance by answering hundreds of security questions in minutes and providing a customizable Trust Center to enhance client trust. Don’t wait until audit deadlines approach — start streamlining your SOC 2 readiness today by visiting Skypher’s platform. Learn how our AI-driven solutions can transform your compliance journey and empower your teams to focus on what matters most.
Frequently Asked Questions
What is the role of SOC 2 auditors?
SOC 2 auditors validate the cybersecurity practices of service organizations by assessing their internal controls and security mechanisms against the Trust Services Criteria.
What are the differences between SOC 2 Type 1 and Type 2 audits?
SOC 2 Type 1 audits assess control design at a single point in time, while Type 2 audits evaluate both control design and operational effectiveness over a period, typically ranging from 6 to 12 months.
What are the key stages involved in the SOC 2 audit process?
The SOC 2 audit process typically involves initial scoping and planning, control documentation review, control effectiveness testing, and reporting with recommendations.
What are common challenges SaaS companies face during SOC 2 compliance?
Common challenges include maintaining continuous compliance, balancing audit requirements with business operations, keeping up with technological changes, and managing complex documentation requirements.