Every company that handles sensitive data worries about proving its trustworthiness. Demand for SOC 2 compliance is at an all time high with over 85 percent of SaaS vendors now asked for SOC 2 reports during sales conversations. Most expect a template to make the process quick and simple. Here's the shocker. Templates alone will not get you compliant or impress your clients. They need to be dynamic and constantly updated if you want a SOC 2 report that truly builds trust in 2025.
Table of Contents
- What Is A Soc 2 Report Template?
- Key Sections Included In A Soc 2 Template
- How To Customize A Soc 2 Report Template For Your Business
- Download Free Soc 2 Report Template (2025 Version)
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 Report Template Framework | A SOC 2 report template is essential for organizations to demonstrate compliance with security standards and includes elements like auditor reports, management assertions, and control tests. |
| Dynamic Document Requirement | Templates must be regularly updated to reflect changes in technology, security threats, and organizational processes to maintain their effectiveness. |
| Customization is Key | Organizations should customize SOC 2 templates by aligning them with their unique security requirements, seeking resources for tailored control mechanisms, and creating comprehensive reporting strategies. |
| Multi-Source Resource Approach | Accessing a high-quality SOC 2 report template often requires a combination of resources rather than relying on a single template, emphasizing the importance of careful adaptation to specific needs. |
| Continuous Improvement Focus | Treating the SOC 2 report template as an ongoing strategic initiative rather than a static compliance task can enhance an organization's security posture and foster client trust. |
What Is a SOC 2 Report Template?
A SOC 2 report template serves as a critical framework for organizations demonstrating their commitment to robust security and compliance standards. This comprehensive document provides a structured approach for evaluating and communicating an organization's control mechanisms across key trust service criteria.
Understanding the SOC 2 Report Basics
At its core, a SOC 2 report template is a standardized documentation format designed to systematically assess an organization's information security practices. AICPA defines this template as a critical tool for validating an organization's security controls and protocols. The template typically covers five primary trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
The primary purpose of a SOC 2 report template extends beyond mere documentation. It provides a transparent mechanism for organizations to demonstrate their commitment to protecting client data and maintaining rigorous operational standards. Businesses across technology, finance, healthcare, and other data sensitive industries rely on these templates to showcase their internal control effectiveness.Key Components of a SOC 2 Report Template
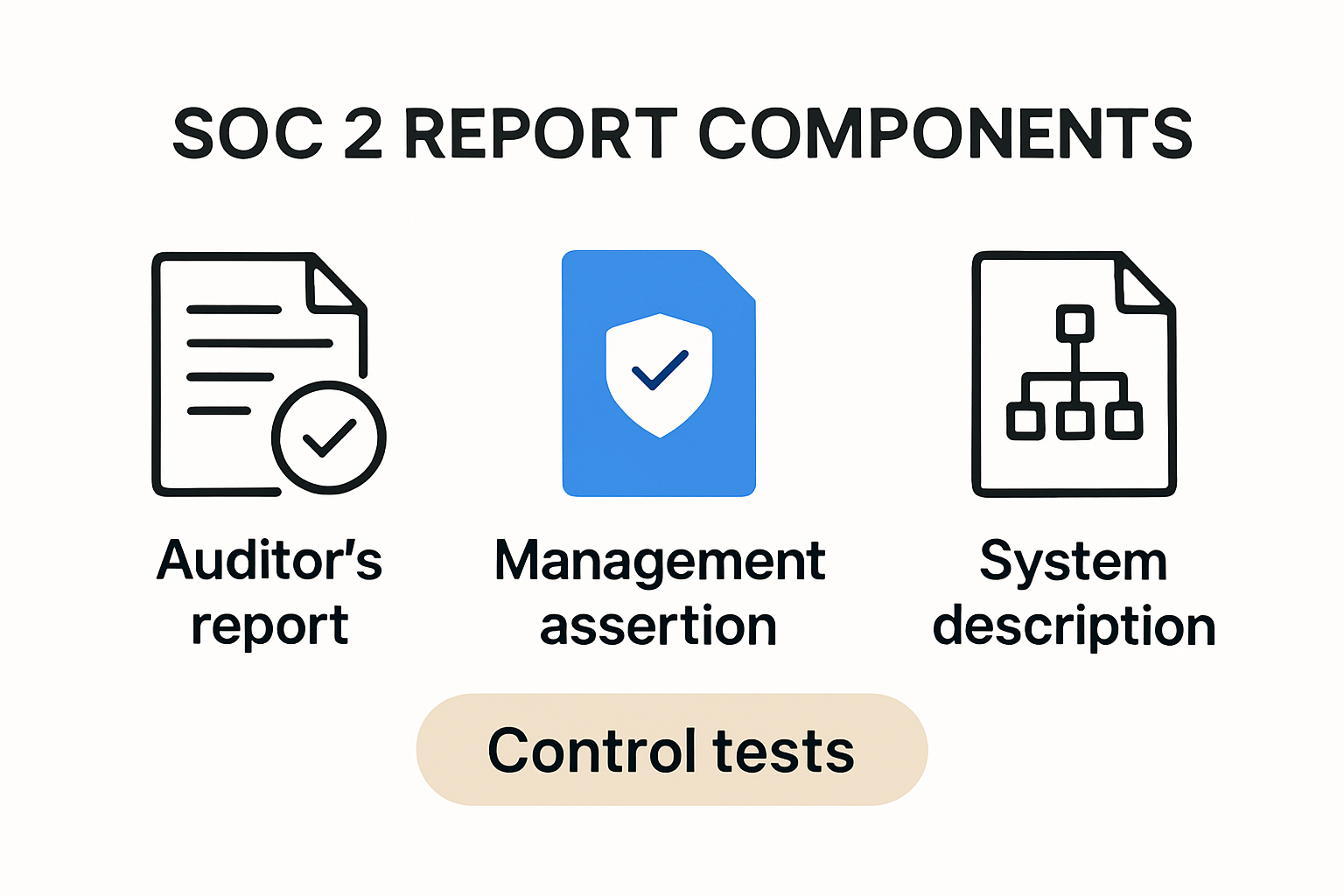
A comprehensive SOC 2 report template includes several critical sections that collectively provide a holistic view of an organization's control environment. According to Princeton University's Office of Audit and Compliance, these typically include:
- Auditor's Report: An independent assessment of the organization's control mechanisms
- Management Assertion: A statement from organizational leadership about the effectiveness of internal controls
- System Description: A detailed overview of the organization's infrastructure, processes, and control objectives
- Detailed Control Tests: Specific evaluations of how implemented controls meet defined security standards
The template's structured approach enables potential clients, partners, and stakeholders to quickly understand an organization's security posture. By providing a standardized format, SOC 2 report templates facilitate transparent communication about an organization's risk management and security practices.
Organizations seeking to create a robust SOC 2 report must pay meticulous attention to each template section. The documentation must be precise, comprehensive, and reflective of actual operational practices. Inaccurate or incomplete reports can undermine an organization's credibility and potentially expose critical security vulnerabilities.
Moreover, SOC 2 report templates are not static documents. They require regular updates to reflect changing technological landscapes, emerging security threats, and evolving organizational processes. Successful organizations treat these templates as dynamic tools for continuous improvement in their security and compliance strategies.
By leveraging a well-designed SOC 2 report template, organizations can effectively communicate their commitment to maintaining high standards of data protection and operational excellence. These documents serve as powerful testimonials of an organization's dedication to securing sensitive information and building trust with clients and stakeholders.
To help clarify the major sections that comprise a SOC 2 report template, the table below summarizes each core component and its primary purpose.
| Section | Description | Purpose |
|---|---|---|
| Auditor's Report | Independent assessment of controls | Provides objective evaluation |
| Management Assertion | Statement from leadership on control effectiveness | Declares management commitment |
| System Description | Overview of infrastructure, processes, and control objectives | Describes the system and its environment |
| Detailed Control Tests | Evaluation of how controls meet security standards | Demonstrates operational effectiveness |
Key Sections Included in a SOC 2 Template
A SOC 2 report template represents a structured blueprint for demonstrating an organization's commitment to security and operational excellence. Understanding the precise sections within this critical document helps organizations craft comprehensive and transparent compliance documentation.
Management's Assertion and Auditor's Perspective
The management's assertion serves as the foundational component of a SOC 2 report. According to Hyperproof, this section represents a formal statement from organizational leadership confirming the design and operational effectiveness of their control mechanisms. This declaration provides immediate insight into management's understanding and commitment to robust security practices.
Companying the management's assertion is the independent auditor's report. SANS Institute highlights that this section offers an objective evaluation of the organization's controls. The auditor provides a professional opinion on the effectiveness of implemented security measures, detailing the audit's scope, methodology, and any identified exceptions or areas requiring improvement.
Comprehensive System Description
The system description represents a critical narrative component of the SOC 2 report template. Cloud Security Alliance emphasizes that this section must provide a holistic overview of the organization's technological infrastructure, operational processes, and control environment. Key elements typically include:
- Infrastructure Overview: Detailed mapping of technological systems and networks
- Service Description: Comprehensive explanation of services and their associated security mechanisms
- Control Objectives: Explicit statement of security goals and implementation strategies
- Incident Management: Documentation of potential security events and response protocols
This section transforms abstract security concepts into a tangible, comprehensible narrative that stakeholders can easily understand. It serves as a transparent window into an organization's security architecture, demonstrating commitment to comprehensive risk management.
Detailed Control Testing and Evaluation
The control testing section represents the most technically rigorous component of a SOC 2 report template. AICPA recommends a meticulous approach to documenting the specific tests performed and their results across five critical trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
Organizations must provide granular evidence of control effectiveness, including:
- Test Descriptions: Specific methodologies used to evaluate control mechanisms
- Test Results: Detailed documentation of control performance
- Exception Reporting: Transparent disclosure of any identified control weaknesses
This section transforms theoretical security frameworks into practical, measurable outcomes. By providing concrete evidence of control effectiveness, organizations build trust with clients, partners, and regulatory bodies.
A well-constructed SOC 2 report template goes beyond mere compliance documentation. It represents a strategic communication tool that demonstrates an organization's commitment to maintaining the highest standards of security, operational integrity, and client trust. Each section works collaboratively to create a comprehensive narrative of technological governance and risk management.
How to Customize a SOC 2 Report Template for Your Business
Customizing a SOC 2 report template requires strategic planning and a deep understanding of your organization's unique security landscape. The process involves transforming a standard template into a precise reflection of your specific operational controls and security mechanisms.
Identifying Your Organizational Security Scope
Customization begins with a comprehensive assessment of your organization's specific security requirements. Princeton University's Office of Audit and Compliance recommends conducting an in-depth internal review to map out your technological infrastructure, data handling processes, and potential risk areas. This initial evaluation helps determine which trust service criteria are most relevant to your business.
The five primary trust service criteria - security, availability, processing integrity, confidentiality, and privacy - provide a framework. However, not every organization will require equal emphasis on each criterion. Technology companies might prioritize security and processing integrity, while healthcare organizations may focus more on confidentiality and privacy protections.
The following table compares the five Trust Service Criteria, including their focus area and example industry emphasis, as discussed in this section.
| Trust Service Criterion | Focus Area | Example Industry Emphasis |
|---|---|---|
| Security | Protecting against threats | Technology, SaaS |
| Availability | System uptime/reliability | Cloud Services |
| Processing Integrity | Processing accuracy | Technology, Finance |
| Confidentiality | Limiting data disclosure | Healthcare, Legal |
| Privacy | Data collection and use | Healthcare, Consumer Services |
Developing Tailored Control Mechanisms
ITSM Documentation suggests utilizing comprehensive implementation toolkits to create customized control documentation. These resources offer 28 adaptable templates that can be modified to reflect your specific operational environment. Key areas for customization include:
- Infrastructure Documentation: Detailed mapping of your technological systems
- Risk Assessment Protocols: Specific procedures for identifying and mitigating potential security threats
- Incident Response Framework: Tailored strategies for managing and reporting security events
- Compliance Verification Processes: Custom mechanisms for ongoing control effectiveness monitoring
Implementing Comprehensive Reporting Strategies
Cado Security emphasizes the importance of creating a reporting structure that goes beyond standard compliance documentation. An effective customized SOC 2 report should include:
- Executive Summary: A high-level overview of your security posture
- Incident Performance Metrics: Quantitative assessment of security event management
- Threat Landscape Analysis: Detailed examination of potential security risks
- Remediation Action Plans: Specific strategies for addressing identified vulnerabilities
The customization process is not a one-time event but an ongoing strategic initiative. Organizations must continuously refine their SOC 2 report template to reflect technological changes, emerging security threats, and evolving business processes.
Successful customization requires collaboration across multiple departments. Security teams, IT professionals, legal experts, and senior management must work together to create a comprehensive and accurate representation of the organization's control environment.
By treating the SOC 2 report template as a dynamic document rather than a static compliance checkbox, organizations can transform it into a powerful tool for demonstrating their commitment to robust security practices. The goal is not just to pass an audit but to build genuine trust with clients, partners, and stakeholders through transparent and comprehensive security reporting.
Download Free SOC 2 Report Template (2025 Version)
Navigating the complex landscape of SOC 2 compliance requires access to high-quality, up-to-date documentation templates. While numerous resources exist, finding a comprehensive and reliable free SOC 2 report template demands careful consideration and strategic research.
Understanding Template Availability and Limitations
AICPA notes that while complete free templates are rare, organizations can leverage multiple resources to construct their SOC 2 documentation. The key is understanding that no single template fits every organizational need. Compliance professionals must carefully adapt available resources to their specific operational context.
Most professional organizations recommend a multi-source approach to developing SOC 2 documentation. Princeton University's Office of Audit and Compliance provides review templates and guidelines that can serve as foundational resources for organizations seeking to develop their compliance documentation.
Navigating Free and Low-Cost Template Resources
While completely free templates are uncommon, several strategies can help organizations access cost-effective SOC 2 documentation resources:
- Professional Association Resources: AICPA offers guidance documents and framework outlines
- Open-Source Compliance Toolkits: Some cybersecurity organizations provide partial template frameworks
- Academic Institution Resources: University compliance offices occasionally share template structures
- Vendor Sample Templates: Some compliance software providers offer limited free template versions
Caution is paramount when downloading templates. Organizations must ensure that any downloaded resource meets their specific compliance requirements and undergoes thorough legal and security review before implementation.
Critical Considerations for Template Selection
Selecting an appropriate SOC 2 report template requires careful evaluation. Cloud Security Alliance recommends considering the following factors:
- Alignment with Trust Service Criteria: Ensure the template covers security, availability, processing integrity, confidentiality, and privacy
- Customization Potential: Look for templates that can be easily modified to reflect your specific organizational structure
- Compliance Currency: Verify the template meets the latest 2025 regulatory standards
- Comprehensive Coverage: Select resources that provide detailed guidance across multiple compliance dimensions
Professional organizations strongly advise against using a template verbatim. Each SOC 2 report must be uniquely tailored to an organization's specific operational environment, technological infrastructure, and risk management strategies.
The most effective approach involves combining multiple resources, consulting with compliance experts, and developing a template that precisely reflects your organization's unique security ecosystem. While free resources provide valuable starting points, successful SOC 2 compliance requires a nuanced, comprehensive approach that goes beyond simple template downloading.
Organizations committed to robust security practices should view the SOC 2 report template as a dynamic tool for continuous improvement. The most valuable templates are those that can be continuously refined to address emerging technological challenges and evolving security landscapes.
Frequently Asked Questions
What is a SOC 2 report template?
A SOC 2 report template is a standardized document that helps organizations showcase their security controls and compliance with established standards, focusing on trust service criteria like security, availability, and confidentiality.
Why is customization important for a SOC 2 report template?
Customization is crucial because it ensures that the SOC 2 report accurately reflects an organization's unique security practices, risk areas, and operational processes, enhancing its credibility and effectiveness.
How can organizations download a free SOC 2 report template for 2025?
Organizations can find free SOC 2 report templates by accessing resources from professional associations like the AICPA, academic institutions, or cybersecurity organizations. It's essential to ensure these templates align with specific compliance needs.
What are the key components included in a SOC 2 report template?
Key components of a SOC 2 report template include the auditor's report, management's assertion, a comprehensive system description, and detailed control testing and evaluation. These sections provide a holistic view of the organization's control environment.
Ready to Move Beyond Static SOC 2 Templates?
If you're struggling to keep your SOC 2 report template accurate and up to date, you're not alone. Many organizations spend countless hours rewriting documents or toggling between security controls and questionnaire responses. Manual effort and static templates often lead to delays, missed details, and lost client trust. There is a better way to demonstrate your commitment to security and efficiency.

Make compliance effortless and reliable by upgrading your process with Skypher. Our AI-driven questionnaire automation tool transforms how you handle security reviews, connects seamlessly with over 40 third-party platforms, and supports real-time team collaboration. Let your team focus on higher-value work instead of endlessly updating templates. Discover how you can save time, eliminate bottlenecks, and impress clients today. Visit our platform to get started now.
