SOC 2 compliance is becoming a top priority for businesses in 2025. Here’s the surprise. 62 percent of small to medium companies report struggling with SOC 2 due to resource challenges and dedicate around 15 percent of their IT budgets to meet requirements. Most assume compliance is just about ticking boxes for auditors. It’s actually a company-wide shift that can drive trust, sharpen your competitive edge and show customers you take their data seriously.
Table of Contents
- Key Soc 2 Requirements And Their Purpose
- Understanding The 5 Trust Service Criteria
- Steps For Meeting Soc 2 Compliance In 2025
- Common Challenges And Tips For Soc 2 Preparation
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understand the Five Trust Services Criteria | Familiarize yourself with the five criteria: Security, Availability, Confidentiality, Processing Integrity, and Privacy to tailor your approach for compliance. Security is mandatory, while the others are optional based on business needs. |
| Build a Comprehensive Compliance Framework | Create a cross-functional team, conduct gap analyses, and map existing controls against SOC 2 requirements to ensure a holistic compliance strategy. |
| Document Thoroughly and Develop Policies | Maintain detailed security policies, incident response plans, and access controls to support compliance efforts and adaptability to future changes. |
| Implement Continuous Monitoring | Set up robust monitoring systems to provide real-time insights into security postures, facilitating proactive risk management and compliance maintenance. |
| Leverage Technological Advancements | Utilize AI and automated compliance tools to enhance monitoring and risk detection, turning compliance into a strategic advantage rather than a mere requirement. |
Key SOC 2 Requirements and Their Purpose
SOC 2 compliance represents a critical framework for organizations seeking to demonstrate their commitment to data security and customer trust. At its core, SOC 2 provides a comprehensive approach to protecting sensitive information through a structured set of requirements that go beyond basic security protocols.
The Five Trust Services Criteria
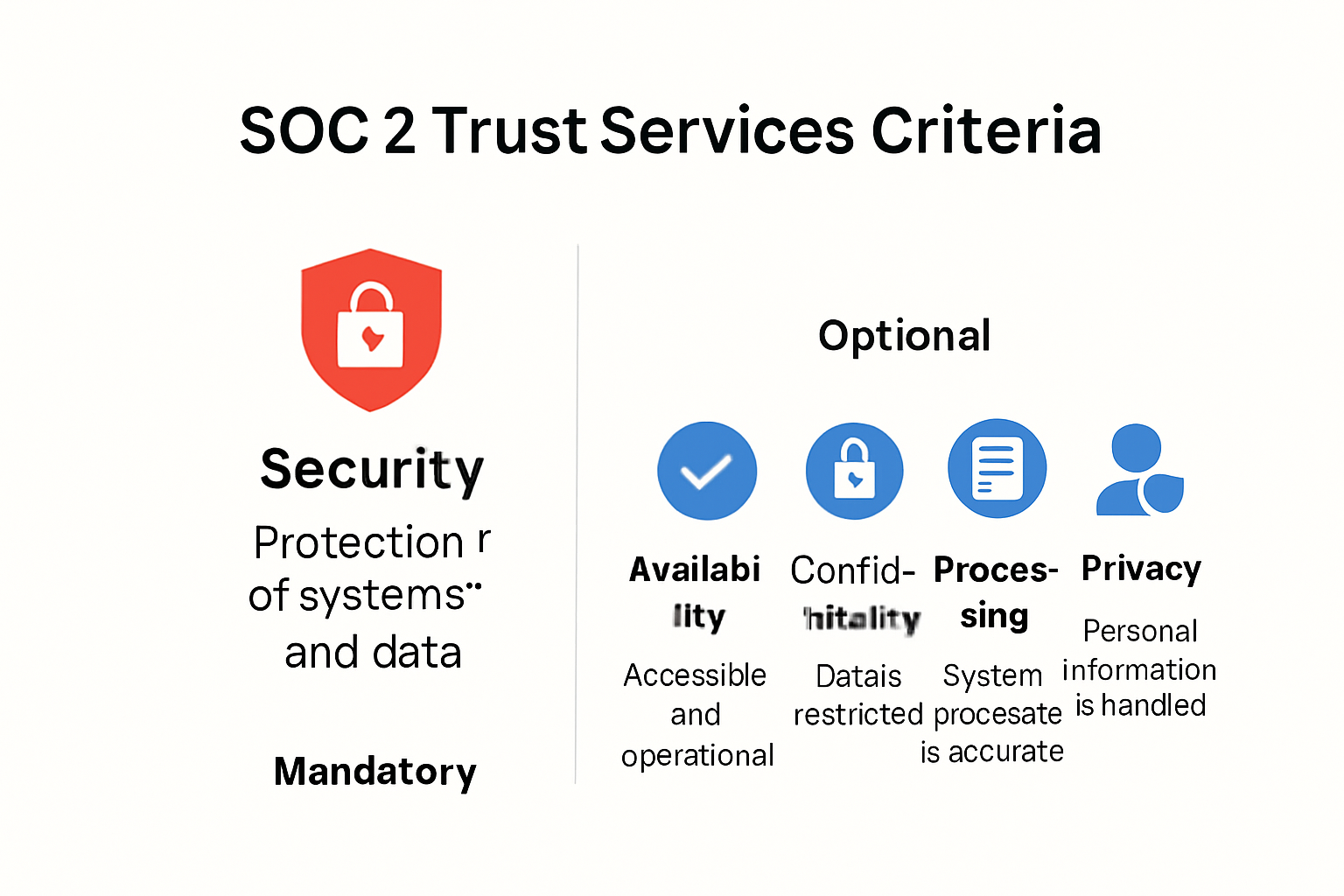
The SOC 2 framework is built around five key Trust Services Criteria, each addressing a specific aspect of organizational data management. According to CertPro, these criteria provide a holistic approach to security and data protection:
- Security: The foundational and mandatory criterion that addresses an organization's ability to protect against unauthorized access and data breaches
- Availability: Ensures systems and data are accessible and operational as agreed
- Confidentiality: Protects sensitive information from unauthorized disclosure
- Processing Integrity: Guarantees that system processing is complete, accurate, and timely
- Privacy: Manages personal information in accordance with established privacy principles
The Security criterion stands out as the only compulsory requirement for SOC 2 audits. Sprinto highlights that this criterion encompasses critical controls including logical and physical access management, system operations, change management, and comprehensive risk mitigation strategies.
Audit and Compliance Process
SOC 2 certification is not a one time achievement but an ongoing commitment to maintaining robust security practices. The American Institute of CPAs (AICPA) developed this voluntary compliance standard to provide organizations with a comprehensive framework for protecting customer data. The audit process involves an independent third party thoroughly examining an organization's controls and systems.
During the audit, organizations must demonstrate they have:
- Clearly defined security policies
- Implemented consistent control mechanisms
- Maintained documented evidence of security practices
- Established ongoing monitoring and improvement processes
Unlike rigid compliance frameworks, SOC 2 offers flexibility. Organizations can tailor their approach based on their specific business needs, selecting which Trust Services Criteria are most relevant to their operations. This adaptability makes SOC 2 particularly valuable for technology companies, cloud service providers, and organizations handling sensitive customer information.
The ultimate purpose of SOC 2 requirements extends beyond mere technical compliance. It represents a commitment to building trust, protecting customer data, and establishing a robust security culture that goes beyond checkbox security. By adhering to these rigorous standards, organizations signal their dedication to maintaining the highest levels of data protection and operational integrity.
For businesses considering SOC 2 certification, understanding these requirements is not just about passing an audit. It is about creating a comprehensive security strategy that protects both the organization and its customers in an increasingly complex digital environment.
Understanding the 5 Trust Service Criteria
The Trust Services Criteria represent a sophisticated framework designed to help organizations establish robust cybersecurity and data protection standards. These criteria provide a comprehensive approach to evaluating an organization's control environment, with each category addressing specific aspects of operational integrity and security.
The Mandatory Foundation: Security Criteria
The Security criteria serve as the cornerstone of SOC 2 compliance. According to Sprinto, this mandatory category includes 33 core requirements that form the baseline for organizational data protection. Unlike other criteria, Security is non-negotiable and must be addressed in every SOC 2 audit.
Key components of the Security criteria include:
- Access Controls: Managing who can access critical systems and data
- Logical Security: Protecting digital infrastructure from unauthorized entry
- Risk Management: Identifying and mitigating potential security vulnerabilities
- System Monitoring: Tracking and analyzing potential security incidents
Optional Complementary Criteria
Linford & Co emphasizes that while Security remains mandatory, the other four criteria are optional and should be selected based on specific business needs. Organizations can strategically choose additional criteria that align with their operational model and customer expectations.
- Availability Criteria: Ensures systems are operational and accessible as agreed
- Processing Integrity: Confirms data processing is accurate, complete, and timely
- Confidentiality: Protects sensitive information from unauthorized disclosure
- Privacy: Manages personal information according to established principles
Implementation and Maturity Strategy
Secureframe notes that many early-stage companies initially focus on the Security criteria, gradually expanding their compliance framework as their business matures. The current version (2017 with 2022 revised points) provides organizations a flexible roadmap for developing comprehensive security practices.
Successful implementation requires a strategic approach:
- Start with the mandatory Security criteria
- Evaluate which additional criteria are most relevant
- Develop specific controls for each selected criterion
- Create documentation demonstrating consistent implementation
- Establish ongoing monitoring and improvement processes
The Trust Services Criteria are not just a compliance checklist but a holistic approach to building organizational trust. By systematically addressing these criteria, businesses demonstrate their commitment to protecting customer data, maintaining operational excellence, and establishing a robust security culture.
For technology companies, cloud service providers, and organizations handling sensitive information, understanding and implementing these criteria is more than a regulatory requirement. It is a strategic investment in building long-term customer confidence and establishing a reputation for reliability and security.
Steps for Meeting SOC 2 Compliance in 2025
As organizations navigate the complex landscape of cybersecurity in 2025, SOC 2 compliance demands a strategic and comprehensive approach. Preparing for successful certification requires more than a checkbox mentality it demands a holistic transformation of security practices and organizational culture.
Building a Robust Compliance Framework
BitSight emphasizes the critical importance of establishing a cross-functional team with clear executive support. This approach ensures that SOC 2 compliance becomes a shared organizational goal rather than a siloed technical exercise.
Key steps in developing a comprehensive compliance framework include:
- Conducting a thorough initial gap analysis
- Mapping existing security controls against SOC 2 requirements
- Identifying potential vulnerabilities and risk areas
- Developing a detailed remediation roadmap
Documentation and Policy Development
Successful SOC 2 compliance hinges on meticulous documentation and well-defined policies. Organizations must create comprehensive security policies that not only meet current requirements but also demonstrate adaptability to emerging technological and regulatory challenges.
Critical documentation elements include:
- Detailed security policies and procedures
- Incident response plans
- Access control protocols
- Risk management frameworks
- Regular security assessment documentation
Continuous Monitoring and Improvement
Compliance is not a one-time achievement but an ongoing process of continuous improvement. Organizations must implement robust monitoring systems that provide real-time insights into their security posture. This approach allows for proactive identification and mitigation of potential risks before they become critical issues.
Strategic monitoring components should address:
- Automated security control tracking
- Regular internal audits
- Continuous risk assessment
- Performance metrics and reporting
- Adaptive security protocol updates
The landscape of SOC 2 compliance in 2025 demands more than technical controls. It requires a holistic approach that integrates security practices into the core of organizational culture. Successful organizations will view compliance not as a regulatory burden but as a strategic opportunity to build trust, enhance operational integrity, and demonstrate commitment to protecting customer data.
For technology companies and service providers, SOC 2 compliance represents a critical differentiator in an increasingly competitive market. By embracing a comprehensive and proactive approach to security, organizations can transform compliance from a checkbox exercise into a powerful strategic advantage that builds customer confidence and drives business success.
Common Challenges and Tips for SOC 2 Preparation
Navigating SOC 2 compliance presents significant hurdles for organizations of all sizes. Understanding these challenges and implementing strategic solutions can transform a complex compliance journey into a manageable and valuable process.
Resource and Complexity Barriers
CG Compliance reveals that 62% of small to medium enterprises struggle with SOC 2 requirements due to resource constraints. Organizations typically dedicate approximately 15% of their IT budget to achieving and maintaining compliance, highlighting the substantial investment required.
Common resource challenges include:
- Limited cybersecurity expertise
- Insufficient budget for comprehensive tools
- Complex documentation requirements
- Lack of dedicated compliance personnel
Strategic Preparation Approaches
According to a McKinsey & Company survey, organizations that adopt best practices can improve compliance efficiency by 50%. Key strategies involve:
- Appointing a dedicated compliance officer
- Investing in robust cybersecurity technologies
- Fostering organization-wide security awareness
- Developing comprehensive documentation processes
- Creating clear, implementable security policies
Technological Advancement in Compliance
OpenMetal highlights the emerging role of artificial intelligence in compliance monitoring. AI technologies are becoming crucial early warning systems that can identify unusual system behaviors and potential security risks before they escalate.
Emerging technological solutions for SOC 2 preparation include:
- AI-powered risk detection systems
- Automated compliance monitoring tools
- Real-time threat prevention platforms
- Continuous security assessment technologies
Successful SOC 2 preparation requires a holistic approach that transcends traditional compliance checklists. Organizations must view compliance as a strategic opportunity to enhance their security posture, build customer trust, and demonstrate organizational maturity.
The most effective SOC 2 preparation strategies integrate technical solutions with cultural transformations. This means creating an environment where security is not just a technical requirement but a fundamental organizational value. By fostering a proactive security mindset, investing in continuous learning, and leveraging advanced technological tools, businesses can navigate the complex SOC 2 landscape with confidence.
Ultimately, SOC 2 compliance is about more than meeting a set of technical requirements. It is about building a robust, transparent, and trustworthy operational framework that protects both the organization and its stakeholders in an increasingly complex digital ecosystem.
Frequently Asked Questions
What are the key SOC 2 requirements for businesses in 2025?
SOC 2 requirements are built around five Trust Services Criteria: Security, Availability, Confidentiality, Processing Integrity, and Privacy. Security is the only mandatory criterion, while the others are optional based on business needs.
Why is SOC 2 compliance important for small to medium businesses?
SOC 2 compliance is essential for small to medium businesses as it demonstrates a commitment to data security and builds customer trust. It can enhance competitive advantage and provide a framework for protecting sensitive information.
How can organizations prepare for SOC 2 compliance effectively?
Organizations can prepare for SOC 2 compliance by building a robust compliance framework, developing detailed documentation of security policies, and establishing continuous monitoring and improvement processes to address potential risks.
What challenges do businesses face when achieving SOC 2 compliance?
Many businesses encounter challenges such as resource constraints, complexity of documentation, and limited cybersecurity expertise. Approximately 62% of small to medium enterprises struggle with SOC 2 compliance due to these resource barriers.
Turn SOC 2 Stress Into Trust and Speed With Skypher
Are you feeling overwhelmed by the resource hurdles of SOC 2 compliance? Many organizations lose valuable time and money managing endless security questionnaires and documentation. You read in the article how managing policies and monitoring controls is only half the battle. The real challenge is keeping your team in sync while efficiently handling security reviews and proving compliance to clients.

With Skypher, you can leave the spreadsheets behind. Our AI-driven Questionnaire Automation Tool drastically reduces the effort of answering hundreds of security reviews, helping your team maintain accurate documentation and accelerate sales cycles. Get started now to meet compliance demands faster, build client trust, and free up resources for what matters most. Visit Skypher today and discover how easy trust and compliance can become.
