Every security leader knows the pressure of proving control effectiveness to clients and regulators without draining valuable resources. For CISOs and compliance officers at organizations handling sensitive financial and technology data, producing a reliable SOC 2 report is no longer optional. Automating the review and creation of independent audit of organizational controls delivers both speed and accuracy, freeing teams to focus on strategic security priorities while maintaining global trust and compliance.
Table of Contents
- What Is A SOC 2 Sample Report?
- Types Of SOC 2 Reports And Their Differences
- Core Sections Of A SOC 2 Sample Report
- Understanding Trust Services Criteria In SOC 2
- Roles And Responsibilities In SOC 2 Compliance
- Risks, Common Mistakes, And Report Alternatives
Key Takeaways
| Point | Details |
|---|---|
| Importance of SOC 2 Reports | SOC 2 reports provide critical insights into an organization's security controls and capabilities, essential for technology companies and cloud service providers. |
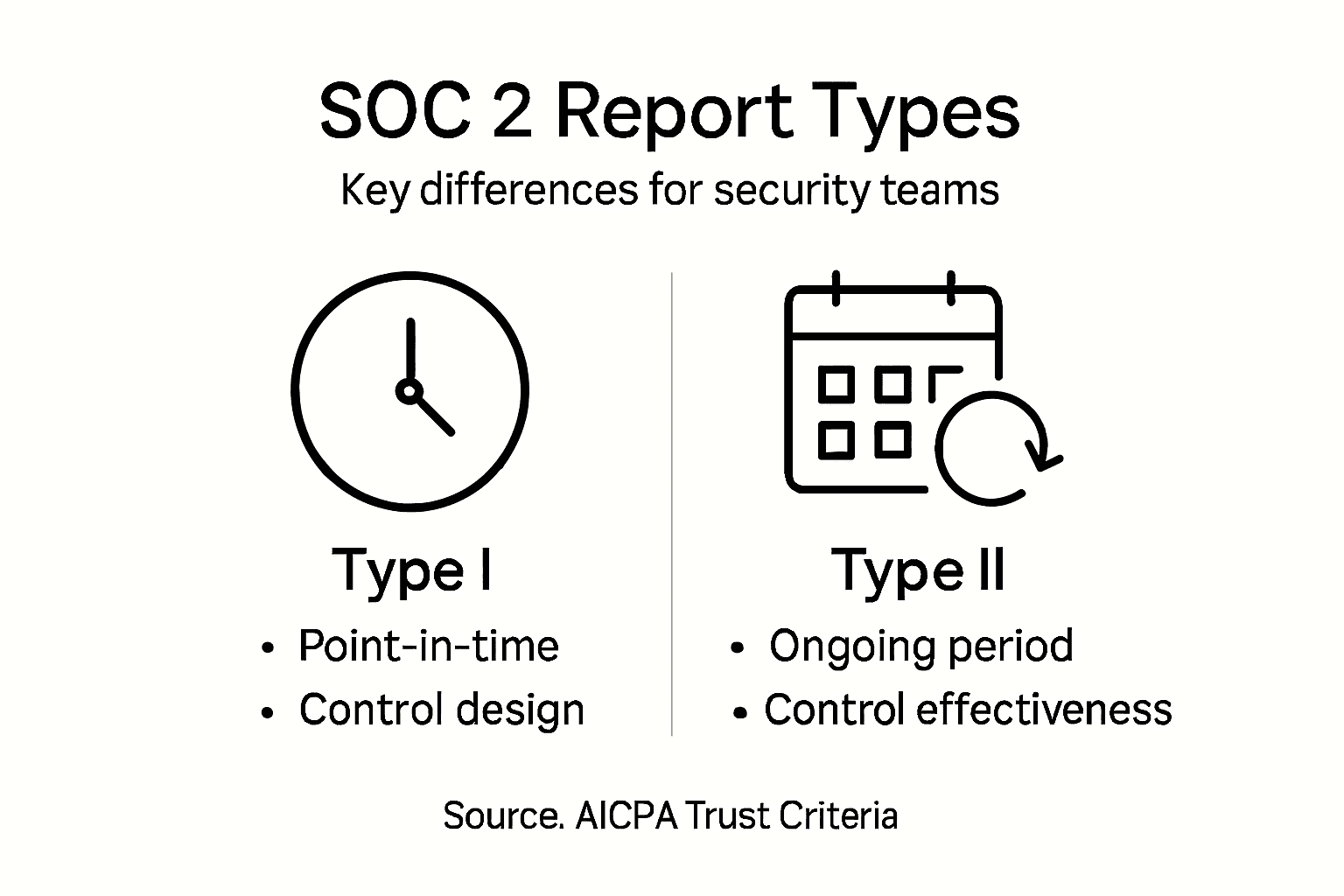
| Types of SOC 2 Reports | Understand the differences between Type I and Type II reports; Type I evaluates design while Type II assesses ongoing effectiveness over time. |
| Key Components | The core sections of a SOC 2 report include the Independent Auditor's Opinion, Management's Assertion, and System Description, offering transparency and accountability. |
| Common Compliance Risks | Organizations face risks such as inadequate preparation and misinterpretation of audit scope, which can hinder effective SOC 2 compliance efforts. |
What Is a SOC 2 Sample Report?
A SOC 2 sample report represents an independent auditor's comprehensive assessment of an organization's security controls and operational practices. Specifically designed for technology companies and cloud service providers, these reports provide critical insights into how organizations protect customer data and maintain rigorous security standards.
The report is fundamentally an independent audit of organizational controls that verifies the suitability of an organization's security infrastructure. Unlike generic compliance documents, a SOC 2 report offers a detailed examination of five key trust service criteria:
- Security: Protecting against unauthorized system access
- Availability: Ensuring systems are operational and accessible
- Processing Integrity: Confirming data processing accuracy and completeness
- Confidentiality: Restricting data access to authorized parties
- Privacy: Managing personal information collection and usage
The structure of a SOC 2 sample report typically includes multiple critical sections that provide comprehensive transparency. These sections generally encompass:
- An independent auditor's opinion
- Management's formal assertion about control effectiveness
- Detailed description of the organizational system and controls
- Specific control objectives and testing results
Organizations obtain these reports to demonstrate their commitment to robust cybersecurity practices, essentially providing third-party validation of their security posture. For potential clients and partners, a SOC 2 report serves as a competitive advantage by offering transparent evidence of their security capabilities.
Pro tip: When reviewing a SOC 2 sample report, pay close attention to the auditor's opinion and any identified control gaps, as these sections reveal the most meaningful insights about an organization's actual security practices.
Types of SOC 2 Reports and Their Differences
SOC 2 reports are complex security assessment documents with distinct variations that serve different organizational needs. Understanding these types is crucial for security professionals seeking comprehensive insights into an organization's control frameworks and security practices.
According to industry standards, there are two primary SOC 2 report types to consider: Type I and Type II. Each serves a unique purpose in validating an organization's security controls:
Type I Report Characteristics:
- Evaluates the design of security controls at a specific point in time
- Provides a snapshot of an organization's control framework
- Less comprehensive than Type II reports
- Typically covers a shorter assessment period
Type II Report Characteristics:
- Assesses both design and operational effectiveness of controls
- Examines control implementation over an extended period (usually 6-12 months)
- Offers more in-depth analysis of control performance
- Provides greater confidence in an organization's security practices
Beyond the primary SOC 2 report types, organizations might also encounter SOC 1 and SOC 3 reports. SOC 1 focuses primarily on financial reporting controls, while SOC 3 offers a more generalized public report with limited technical details.
Here's a side-by-side look at different SOC report types and alternatives for fast decision-making:
| Report Type/Framework | Main Focus | Level of Detail | Intended Audience |
|---|---|---|---|
| SOC 2 Type I | Control design at a point in time | Summary of controls, snapshot audit | Prospects, internal teams |
| SOC 2 Type II | Control design and operating effectiveness over time | Detailed control testing, audit trail | Clients, auditors, regulators |
| SOC 1 | Internal control over financial reporting | Focused on financial processes | Financial auditors, clients' finance |
| SOC 3 | General security overview | Public, limited detail | General public, marketing use |
| ISO 27001 | Information security management system | Process and policy audit, certification | Global partners, large enterprises |
| FedRAMP | U.S. government cloud security | Rigorous, technical, ongoing assessments | Federal agencies, cloud vendors |
The selection between Type I and Type II reports depends on an organization's specific compliance requirements, audit objectives, and the depth of security validation needed. Type I reports are often used for initial assessments, whereas Type II reports provide more comprehensive and credible evidence of sustained security effectiveness.
Pro tip: When selecting between SOC 2 report types, consider your stakeholders' expectations and the level of assurance they require about your security controls.
Core Sections of a SOC 2 Sample Report
SOC 2 sample reports are complex documents that provide comprehensive insights into an organization's security controls and practices. These reports are meticulously structured to offer transparency and detailed evaluation of an organization's information security management.

According to industry experts, a typical SOC 2 report contains several critical sections for comprehensive assessment. The core components include:
Key Report Sections:
- Independent Auditor's Opinion
- Management's Assertion
- System Description
- Detailed Control Evaluation
- Supplemental Information
The Independent Auditor's Opinion is perhaps the most crucial section. This component provides a professional assessment of the organization's control design and operational effectiveness. Auditors can issue two primary types of opinions:
-
Unqualified Opinion (Clean Report)
- Indicates comprehensive and effective controls
- Suggests high level of security compliance
-
Qualified Opinion
- Highlights specific control weaknesses or limitations
- Requires immediate attention and remediation
The System Description section offers a comprehensive narrative explaining the organization's system, its boundaries, and the specific security controls implemented. This section provides critical context for understanding the scope of the assessment and the organization's security infrastructure.
A SOC 2 report is more than a document—it's a strategic tool that demonstrates an organization's commitment to robust security practices.
Management's Assertion represents the organization's formal statement about the accuracy and completeness of the system description and control implementation. This section provides direct accountability and transparency from the organization's leadership.
Pro tip: When reviewing a SOC 2 report, pay special attention to the auditor's opinion and any qualified statements, as these reveal the most critical insights about potential security vulnerabilities.
Understanding Trust Services Criteria in SOC 2
Trust Services Criteria represent a comprehensive framework that establishes critical standards for evaluating an organization's security controls and information management practices. These criteria, developed by the American Institute of Certified Public Accountants (AICPA), provide a structured approach to assessing an organization's commitment to protecting sensitive information.
The SOC 2 framework encompasses five distinct trust services criteria that organizations can leverage to demonstrate their security capabilities:
Five Core Trust Services Criteria:
- Security: Protecting systems against unauthorized access
- Availability: Ensuring systems are operational and accessible
- Processing Integrity: Maintaining accurate and complete data processing
- Confidentiality: Restricting data access to authorized parties
- Privacy: Managing personal information collection and usage
Mandatory vs. Optional Criteria:
- Security is the only mandatory criterion for all SOC 2 assessments
- Organizations can select additional criteria based on their specific service commitments
- Each criterion requires demonstrating both design and operational effectiveness of controls
Trust Services Criteria provide organizations with a flexible framework to address unique security challenges while maintaining consistent evaluation standards.
The selection of applicable criteria depends on an organization's specific risk profile, service offerings, and customer expectations. For instance, a cloud storage provider might emphasize security, availability, and confidentiality, while a healthcare technology company might prioritize privacy and security controls.
Pro tip: When preparing for a SOC 2 audit, conduct a thorough internal assessment of your controls against each Trust Services Criterion to identify potential gaps before the official evaluation.
Roles and Responsibilities in SOC 2 Compliance
SOC 2 compliance is a collaborative effort that requires strategic coordination across multiple organizational roles and responsibilities. Successfully navigating this complex process demands clear accountability and a comprehensive understanding of each stakeholder's critical functions.
According to industry experts, SOC 2 compliance involves strategic collaboration among several key organizational roles:
Primary Stakeholder Roles:
- Executive Leadership: Sets overall compliance strategy and governance
- Security Teams: Implement and maintain security controls
- IT Department: Design and monitor technical infrastructure
- Compliance Officers: Manage documentation and audit preparation
- External Auditors: Provide independent assessment
Key Responsibilities by Role:
-
Executive Leadership
- Establish compliance culture
- Approve security policies
- Allocate resources for compliance initiatives
-
Security Teams
- Design and implement control mechanisms
- Conduct continuous monitoring
- Manage access controls
- Respond to security incidents
-
Compliance Officers
- Develop comprehensive documentation
- Track control effectiveness
- Coordinate internal and external audit processes
- Manage risk assessment activities
Effective SOC 2 compliance requires a synchronized approach where each role understands and executes its responsibilities with precision and commitment.
Successful SOC 2 compliance is not a one-time event but an ongoing process that demands continuous collaboration, communication, and commitment from all organizational levels. Each role plays a crucial part in maintaining the integrity of the organization's security controls and demonstrating trustworthiness to stakeholders.
This summary table highlights the unique contributions of key stakeholder roles in SOC 2 compliance:
| Stakeholder Role | Unique Contribution | Impact on SOC 2 Success |
|---|---|---|
| Executive Leadership | Sets compliance tone and priorities | Drives resource allocation and accountability |
| Security Teams | Implements technical safeguards | Maintains operational security |
| IT Department | Builds and manages secure systems | Ensures infrastructure reliability |
| Compliance Officers | Oversees documentation and audit prep | Provides audit readiness and transparency |
| External Auditors | Evaluates control effectiveness | Validates and certifies compliance |
Pro tip: Implement regular cross-departmental meetings to ensure alignment and transparency in SOC 2 compliance efforts, creating a unified approach to security management.
Risks, Common Mistakes, and Report Alternatives
SOC 2 compliance involves navigating a complex landscape of potential risks and challenges that can significantly impact an organization's security posture. Understanding these potential pitfalls is crucial for developing a robust and effective compliance strategy.
Organizations frequently encounter several critical risks during SOC 2 compliance that can undermine their security efforts:
Common SOC 2 Compliance Risks:
- Inadequate preparation and planning
- Misunderstanding audit scope
- Insufficient control implementation
- Lack of continuous monitoring
- Overlooking third-party vendor risks
Typical Compliance Mistakes:
-
Documentation Gaps
- Incomplete security policy documentation
- Inconsistent control evidence
- Lack of detailed process descriptions
-
Narrow Compliance Focus
- Treating SOC 2 as a one-time event
- Focusing solely on passing the audit
- Neglecting ongoing security improvements
-
Incomplete Risk Assessment
- Ignoring subservice providers
- Failing to address all trust criteria
- Underestimating potential security vulnerabilities
Successful SOC 2 compliance is about creating a sustainable security culture, not just passing an audit.
Alternative Compliance Frameworks:
- ISO 27001: International standard for information security management
- FedRAMP: Cloud security authorization for government systems
- Cybersecurity Insurance Assessments: Risk management alternative
- Industry-Specific Security Frameworks: Tailored compliance options
Pro tip: Develop a comprehensive, ongoing compliance strategy that views SOC 2 as a continuous improvement process rather than a one-time checkbox exercise.
Simplify SOC 2 Compliance with AI-Powered Automation
Navigating the complexities of SOC 2 reports and trust services criteria requires precision and efficiency. If your security team struggles with the time-consuming process of preparing documentation, coordinating control evidence, or responding to extensive security questionnaires, Skypher offers a tailored solution. Our AI Questionnaire Automation Tool dramatically accelerates the review process, reducing hours of manual work to minutes while ensuring accuracy aligned with SOC 2 standards.

Empower your team to manage SOC 2 compliance effortlessly by leveraging real-time collaboration, seamless integration with over 40 third-party risk management platforms, and a customizable Trust Center that centralizes your security documentation. Act now to transform your compliance workflow and gain the competitive advantage your clients demand. Discover how at Skypher and explore our AI Questionnaire Automation Tool to see why leading tech and finance organizations trust us to boost efficiency and fortify their security posture.
Frequently Asked Questions
What is a SOC 2 sample report?
A SOC 2 sample report is an independent auditor's assessment of an organization's security controls and operational practices, focusing on how it protects customer data and maintains security standards.
What are the key components of a SOC 2 report?
A typical SOC 2 report includes an independent auditor's opinion, management's assertion on control effectiveness, a description of the organizational system, and detailed control evaluation results.
What are the differences between SOC 2 Type I and Type II reports?
SOC 2 Type I reports assess the design of security controls at a specific point in time, while Type II reports evaluate the effectiveness of those controls over an extended period, usually 6-12 months.
Why are Trust Services Criteria important in a SOC 2 report?
Trust Services Criteria provide critical standards for assessing an organization's security controls and practices. They ensure companies address security, availability, processing integrity, confidentiality, and privacy, demonstrating their commitment to protecting sensitive information.
